The digital security landscape is currently witnessing a troubling evolution in social engineering tactics, where the very mechanisms designed to keep users secure are being subverted to facilitate fraud. A recent, highly effective phishing campaign has come to light that leverages Apple’s own automated notification systems to bypass traditional email defenses. By turning legitimate account security alerts into vessels for malicious lures, attackers are successfully masquerading as trusted entities, effectively neutralizing the efficacy of standard spam filters and user skepticism.
The Anatomy of an Authorized Deception
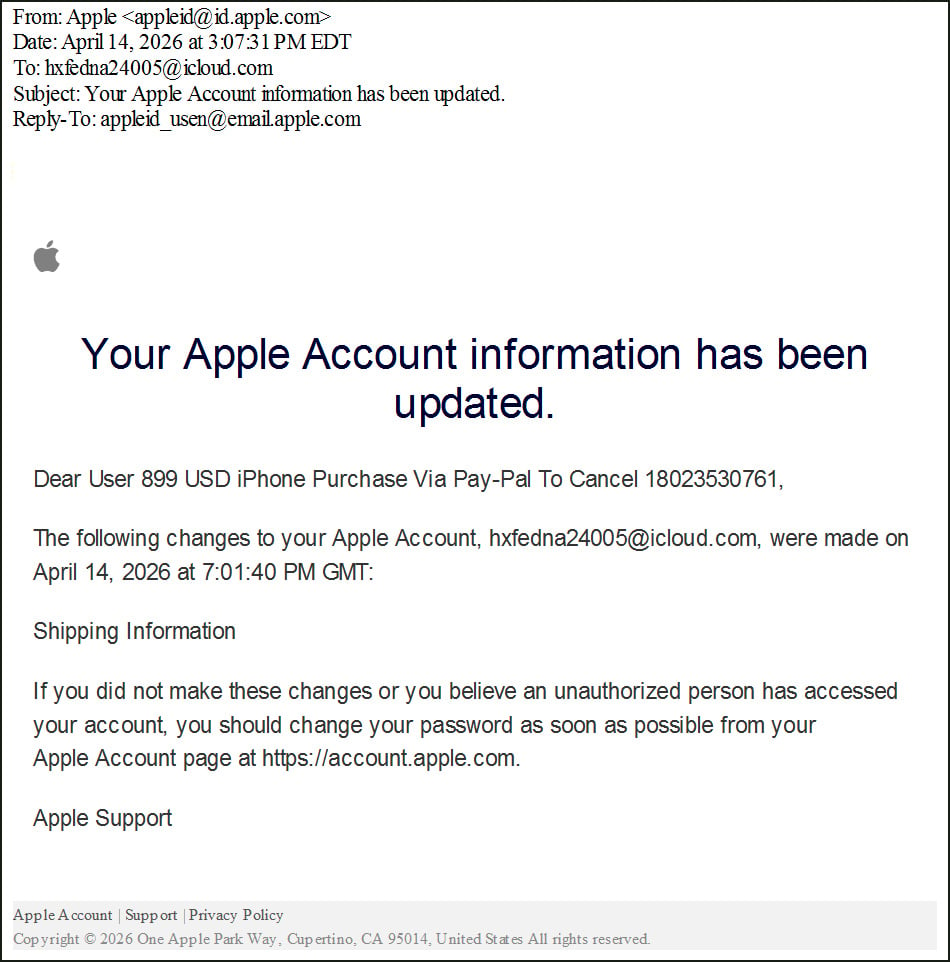
At the heart of this campaign is a sophisticated "callback phishing" methodology. Unlike traditional phishing, which directs users to a malicious link or a spoofed login page, this approach relies on psychological manipulation, urging the recipient to contact a fake support hotline. The brilliance of the attack—if one can call it that—lies in its delivery. Because the email originates directly from Apple’s verified infrastructure, it passes all major email authentication protocols, including Sender Policy Framework (SPF), DomainKeys Identified Mail (DKIM), and Domain-based Message Authentication, Reporting, and Conformance (DMARC).
For the recipient, the visual cues of legitimacy are overwhelming. The message arrives from an official Apple domain, typically [email protected]. It contains accurate header metadata and is routed through Apple’s own outbound relays. To a security gateway, the message is indistinguishable from a genuine account security alert, as it is, in a technical sense, a genuine notification generated by Apple’s servers.

The Mechanism of Abuse
The attack cycle begins with the adversary registering a new Apple account. Once inside the ecosystem, the attacker manipulates the profile settings to embed their fraudulent narrative. Since the primary fields of an Apple ID—such as the first and last name—are reflected in subsequent security notifications, the attacker strategically splits their phishing script across these fields.
When the attacker subsequently modifies their "Shipping Information," the Apple system automatically triggers an update notification. This automated email serves as the delivery vehicle, pulling the data from the attacker’s profile and presenting it as part of a formal security warning. The resulting email informs the user of an unauthorized transaction—often citing an $899 iPhone purchase via a third-party service like PayPal—and provides a toll-free number for the user to "cancel" the transaction. By the time the email reaches the victim, it is formatted exactly like a legitimate security alert, complete with the user’s associated email address, creating a sense of urgency that is difficult to ignore.
Industry Implications and the Erosion of Trust
This incident highlights a significant structural vulnerability in how major technology platforms handle user-defined data within automated messaging. When a platform allows user-supplied inputs to be reflected in system-generated communications without robust sanitization, it inadvertently provides a sandbox for malicious actors to conduct "living-off-the-land" attacks.
The implications for the cybersecurity industry are profound. For years, security training has relied on teaching users to "check the sender" and "verify the domain." This campaign renders that advice obsolete. If an email originates from an authenticated, trusted server, the traditional heuristic indicators of phishing are silenced. This forces a paradigm shift in how security awareness programs must be constructed. Users can no longer rely on technical metadata to judge the veracity of a message; they must instead be educated on the behavioral patterns of the service providers themselves. For instance, reputable companies rarely, if ever, include support numbers in automated account change notifications, nor do they solicit sensitive financial or remote-access cooperation over the phone.

Expert Analysis: The Rise of Callback Phishing
Callback phishing represents a dangerous maturation of social engineering. By shifting the point of compromise from a browser-based exploit to a voice-based interaction, attackers can bypass endpoint detection and response (EDR) systems that would otherwise catch malicious scripts or phishing URLs.
When a victim calls the provided number, they are greeted by a "customer support representative" who is, in reality, a member of a coordinated fraud syndicate. These operators are highly trained in psychological manipulation. They often employ "fear-based" tactics, suggesting that the victim’s identity has been stolen or their bank account is currently being drained. Once the victim is in a state of heightened anxiety, the operator may coerce them into installing remote management software—such as AnyDesk or TeamViewer—under the guise of "securing the device." Once the attacker has remote access, the transition from a simple phishing lure to full-scale financial theft is trivial. The attacker can then view the victim’s screen, manipulate their banking applications, and deploy further malware to establish persistence.
Future Trends and the "Verified" Threat Vector
The reliance on trusted infrastructure to deliver malicious content is a trend that is likely to accelerate. As email providers become better at identifying and blocking traditional malicious domains, attackers will increasingly turn to platforms that maintain high domain reputation scores. Whether it is abusing cloud-based document hosting, calendar invitation services, or, as in this case, automated notification systems, the goal is to occupy the "trusted path" of communication.
This phenomenon also challenges the concept of "identity-as-a-service." If the platform’s own identity management system is being used to propagate scams, the platform itself is inadvertently complicit in the attack chain. We are likely to see a shift toward more restrictive input validation on account profile pages, where service providers will need to strip or sanitize any content that resembles a URL, phone number, or call-to-action before reflecting that data in automated alerts.
Furthermore, the rise of AI-driven social engineering is likely to make these attacks even more dangerous. Currently, the phishing scripts in these Apple-based attacks are somewhat generic. However, as LLMs (Large Language Models) become integrated into fraud operations, we can expect to see highly personalized, context-aware phishing messages that use a victim’s actual purchase history or regional dialect to increase the likelihood of a successful callback.
Countermeasures and Defense Strategies
For organizations and individual users, the defense against this type of attack must be multi-layered. First, organizations should implement stringent policies regarding the use of remote access software, explicitly prohibiting the installation of such tools based on instructions from unsolicited support calls. Second, the adoption of robust identity verification procedures for support interactions is essential. A legitimate company will not ask a user to share their screen or provide multi-factor authentication (MFA) codes over the phone.
At the platform level, tech giants must prioritize the "sanitization of reflection." Any data that a user can input into their account profile should be subjected to rigorous pattern matching to prevent the insertion of phone numbers, links, or phrases that mimic system warnings. Furthermore, security teams should implement "anomaly detection" on account changes. If a user suddenly updates their shipping information to contain text that mirrors a support message, the system should flag this behavior and prevent the subsequent notification from being sent until a human or a more advanced heuristic engine can verify the content.
Conclusion
The exploitation of Apple’s notification infrastructure is a sobering reminder that the security of a system is only as strong as its most overlooked feature. As threat actors continue to innovate, they will inevitably look for the path of least resistance—and often, that path lies through the very systems we trust the most. The incident serves as a critical call to action for both the developers of digital infrastructure and the end-users who inhabit it. Trust must be treated as a verifiable commodity, not an inherent assumption, and security, in an age of automated deception, requires constant vigilance against the very messages we once considered the hallmark of a secure account. As we move forward, the focus must shift from merely securing the perimeter to securing the integrity of the communication channels that define our digital lives.

