The illicit marketplace for compromised financial data has historically been defined by its chaotic, "buyer-beware" nature. For decades, individuals engaged in carding—the unauthorized use of stolen credit card credentials—navigated a digital landscape characterized by rampant exit scams, law enforcement honeypots, and service instability. However, as the global cybercrime landscape matures, the amateurish, ad-hoc methods of the past are being replaced by a highly structured, risk-averse operational model. A recently surfaced document circulating within underground forums provides a window into this transformation, detailing a rigorous, standardized methodology for vetting stolen data suppliers.
This shift toward professionalization is not merely a preference; it is a survival necessity. As traditional financial institutions enhance their fraud detection capabilities and international law enforcement agencies intensify their disruption operations, the "cost of doing business" for threat actors has skyrocketed. The document, which serves as an informal handbook for aspiring and mid-tier fraudsters, underscores a transition from opportunistic, high-risk gambling to a disciplined, supply-chain-focused approach to cybercrime.
The Evolution of the "Carding" Supply Chain
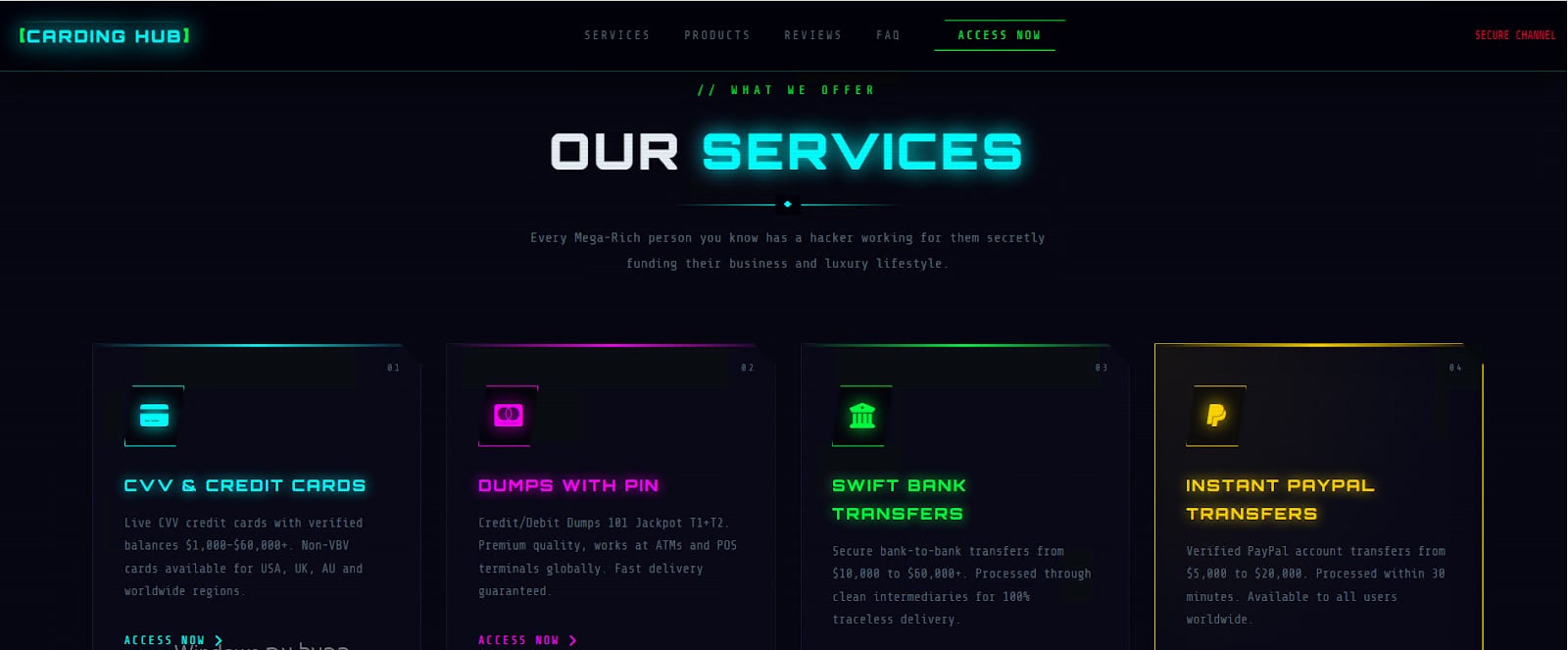
At the heart of this evolution is a fundamental re-evaluation of the vendor-buyer relationship. In the early days of carding, actors often operated on a trial-and-error basis, purchasing credentials from any available source and hoping for a return on investment. Today, the focus has shifted toward supplier due diligence. The guide explicitly warns against the allure of flashy, high-visibility marketplaces, arguing that true legitimacy in the criminal underworld is defined not by marketing or UI design, but by long-term survivability.
This emphasis on "survivability" reflects a broader trend: the most effective shops are those that have demonstrated resilience against the constant pressure of takedowns and internal feuds. For the modern threat actor, the primary risk has shifted from simple technical failure to the risk of being defrauded by a "partner" or inadvertently conducting business with an operation compromised by law enforcement. Consequently, the vetting process described in the guide is extensive, mirroring the procurement standards found in legitimate corporate environments.
Data Integrity and the "Freshness" Metric
The guide articulates a clear hierarchy of data quality, moving beyond the commoditization of credit card numbers toward a nuanced understanding of "freshness." In the parlance of the underground, the value of a record is directly proportional to its source. Data obtained through sophisticated infostealer malware, which captures browser cookies and session tokens in addition to raw card details, is prioritized over older data sourced from mass-market phishing campaigns.

This focus on data provenance highlights an industry-wide recognition that the shelf-life of compromised credentials is shrinking. As banks and payment processors deploy faster anomaly detection, the window of opportunity for exploiting a stolen card is often measured in hours, or even minutes. Shops that can consistently provide high-quality, "fresh" data from reputable sources—such as point-of-sale breaches or targeted malware deployments—are rising to the top of the ecosystem. This, in turn, creates a competitive pressure on shops to maintain technical infrastructure that can support rapid, high-volume data ingestion and validation.
Trust in a Trustless Ecosystem
One of the most paradoxical elements of the underground economy is the desperate search for trust in an environment designed to be anonymous and deceitful. The guide addresses this by advocating for "community validation" through established, invite-only forums. The author actively discourages reliance on internal reviews or testimonials, which are easily manufactured, and instead instructs users to perform longitudinal analysis on a vendor’s history within the community.
This vetting protocol involves tracking a vendor’s presence across multiple platforms, analyzing their engagement in technical discussions, and observing how they handle disputes. By treating these shops as long-term partners rather than anonymous retail sites, actors are effectively building a decentralized, reputation-based trust model. This transition toward curated, exclusive vendor groups marks a significant departure from the open-access, mass-market shops that dominated the previous decade.
Technical Due Diligence and Operational Security (OPSEC)
The guide’s technical checklist serves as a masterclass in risk mitigation. Beyond basic browser security, it outlines a protocol for validating the infrastructure of a potential supplier. This includes analyzing domain age, inspecting SSL certificate configurations, and searching for the presence of multiple mirror domains or "failover" sites. The logic is sound: a shop that has invested in robust, redundant infrastructure is statistically less likely to be a "fly-by-night" scam operation.
Furthermore, the document provides detailed instructions on OPSEC, which reveals the extent to which threat actors are now prioritizing their own digital hygiene. The move away from direct, traceable financial transactions toward privacy-focused cryptocurrencies like Monero, combined with the use of dedicated, compartmentalized virtual machines for every transaction, indicates that even entry-level actors are adopting the tools and tactics once reserved for nation-state-affiliated groups. This "trickle-down" of advanced cyber-tactics poses a significant challenge for law enforcement, as the technical barrier to entry for effective, hard-to-track fraud continues to fall.
Future Implications: A More Resilient Underground
The shift toward structured, professionalized vetting has profound implications for the future of cybercrime. By building redundancy and adaptability into their workflows, threat actors are creating a more resilient criminal economy. When a single marketplace is seized or shut down, the infrastructure of the surrounding community is no longer shattered; instead, actors simply migrate to the next vetted supplier in their network.
This resilience complicates the work of cybersecurity professionals and intelligence agencies. Traditional disruption tactics—such as domain seizures or the arrests of high-profile site administrators—may temporarily inconvenience individual actors, but they are increasingly insufficient to dismantle the broader, decentralized networks of trust and supply that have formed in the shadows.
Moreover, the increasing sophistication of these actors suggests that the next generation of fraud will be characterized by greater precision. By focusing on quality over quantity and prioritizing long-term relationships, criminals are reducing their own exposure while maximizing the success rate of their campaigns. The result is an underground economy that is not only more efficient but also more difficult to infiltrate and monitor.
Intelligence-Driven Defense
From a defensive standpoint, this document acts as a roadmap for understanding the adversary. By knowing how threat actors evaluate their own suppliers, security teams can better anticipate how those actors will behave when a shop is compromised or a new, high-quality source of data enters the market. The emphasis on "survivability" and "reputation" provides specific indicators that security organizations can use to monitor for emerging threats.
As the lines between traditional, opportunistic cybercrime and structured, professionalized fraud continue to blur, the security industry must adapt. We can no longer treat underground marketplaces as monolithic, chaotic entities. Instead, we must analyze them as complex, evolving businesses that are governed by their own internal logics, vetting procedures, and standards of quality. By shifting from reactive, site-by-site takedowns to a deeper, intelligence-driven understanding of how these networks operate, defenders can identify the critical pressure points that threaten the stability of the entire ecosystem.
The professionalization of the carding economy is a wake-up call. It demonstrates that our adversaries are learning, adapting, and becoming increasingly disciplined. To maintain an edge, the cybersecurity community must match this rigor with a proactive, intelligence-led approach that focuses not just on the tools of the trade, but on the evolving psychology and methodology of those who wield them. The era of the "amateur" criminal is fading, replaced by a sophisticated, networked industry that demands an equally sophisticated and persistent response.

