The digital security landscape is facing a fresh challenge as threat actors demonstrate a concerning mastery of abusing legitimate cloud infrastructure for deceptive communication. Specifically, indicators point to the systematic exploitation of Microsoft Azure Monitor capabilities to disseminate highly convincing callback phishing campaigns. These operations bypass conventional email security gateways by leveraging the trust inherently associated with official notifications originating directly from the Microsoft cloud ecosystem, masquerading as urgent security warnings related to unauthorized financial transactions.
Azure Monitor, the cornerstone of observability within the Azure platform, is designed to aggregate telemetry, analyze performance metrics, and enforce proactive alerting across an organization’s cloud deployment. Its function is crucial: to notify administrators and users immediately when predefined thresholds or anomalous activities—such as unexpected billing spikes, service degradation, or security events—are detected. It is precisely this mission-critical communication channel that malicious entities have co-opted.
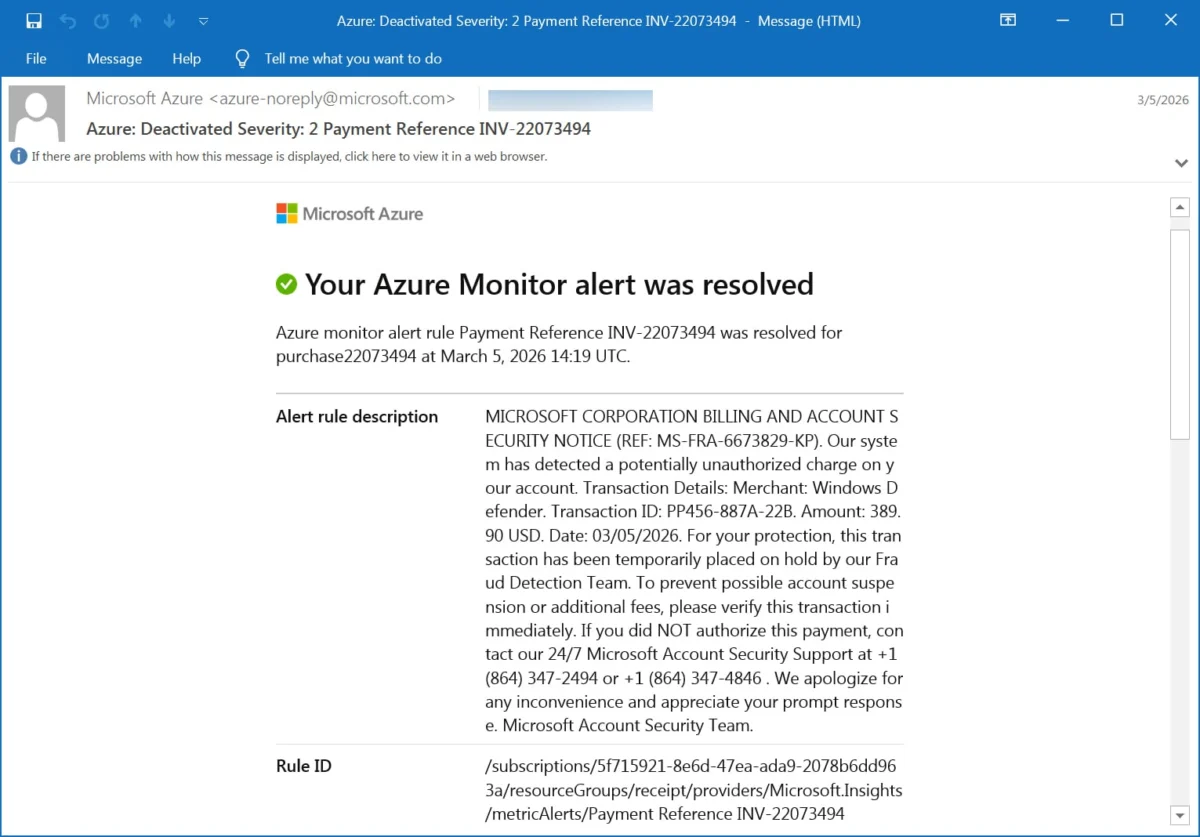
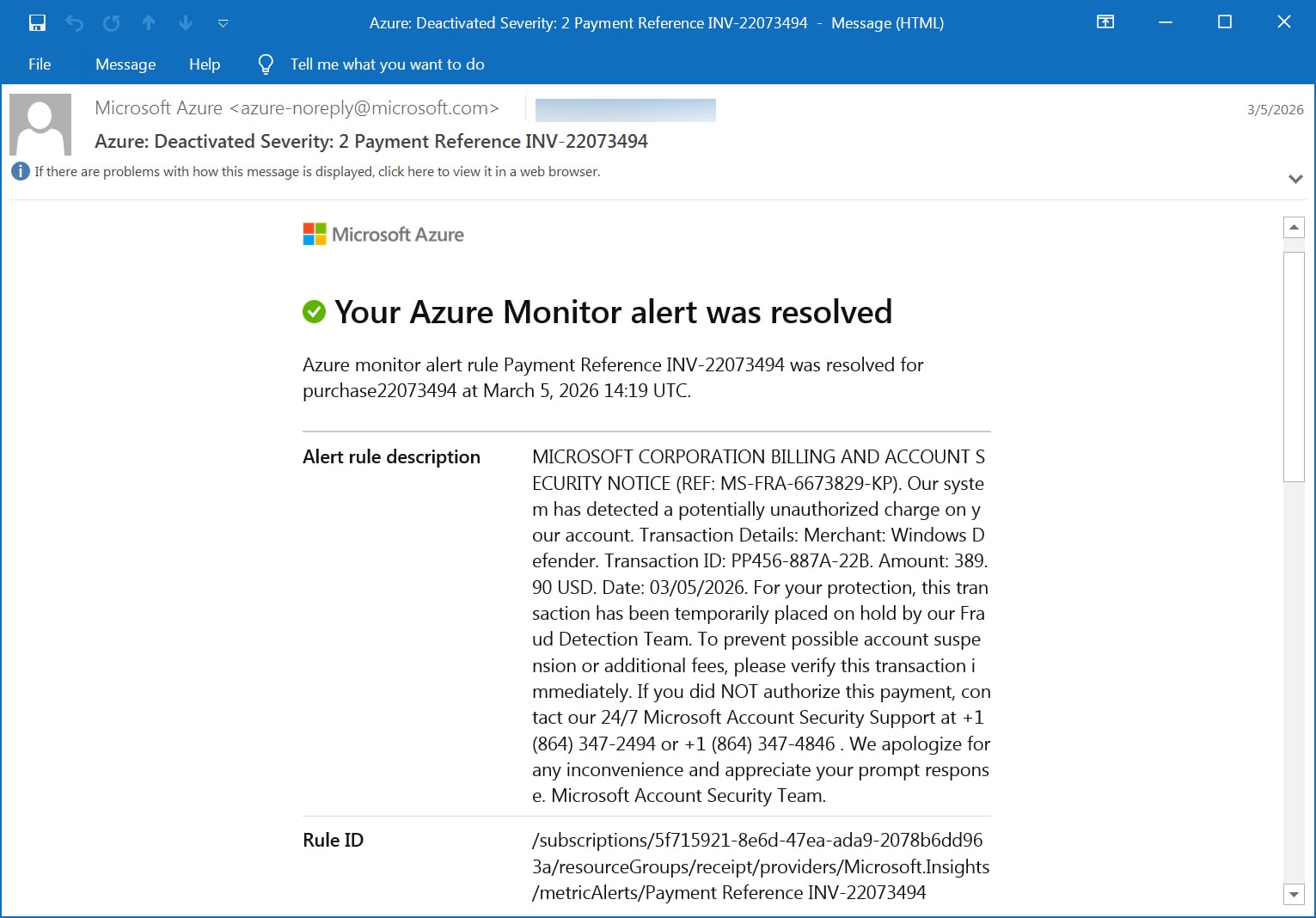
Over the preceding weeks, reports have surfaced across various technical forums and user communities detailing the receipt of emails deceptively branded as official Azure Monitor alerts. These messages consistently employ high-stakes language concerning account security and billing integrity, culminating in an explicit instruction: to contact a provided telephone number for immediate resolution. This tactic is a textbook example of callback phishing, where the goal is to move the victim off the secure digital channel and into a real-time voice interaction where social engineering can be applied directly to extract sensitive data or extort funds.
A typical sample of the fraudulent alert text reads with alarming specificity: "Alert rule description: MICROSOFT CORPORATION BILLING AND ACCOUNT SECURITY NOTICE (REF: MS-FRA-6673829-KP). Our system has detected a potentially unauthorized charge on your account. Transaction Details: Merchant: Windows Defender. Transaction ID: PP456-887A-22B. Amount: 389.90 USD. Date: 03/05/2026l." The urgency is compounded by directives such as, "For your protection, this transaction has been temporarily placed on hold by our Fraud Detection Team. To prevent possible account suspension or additional fees, please verify this transaction immediately." The call to action directs victims to contact "24/7 Microsoft Account Security Support" via numbers like +1 (864) 347-2494 or +1 (864) 347-4846, concluding with a disarming apology.

The Technical Evasion: Bypassing Trust Boundaries
What elevates this campaign beyond standard domain spoofing or simple email forgery is its reliance on inherent platform trust. These messages are not constructed through fraudulent email servers attempting to mimic Microsoft domains; rather, they are dispatched directly by the Azure Monitor service itself. Threat actors achieve this by configuring alert rules within their own or compromised Azure subscriptions, utilizing the platform’s legitimate notification pipeline, which originates from the verified domain [email protected].
This methodology yields powerful security evasion capabilities. Modern enterprise email defenses are heavily reliant on established authentication protocols: Sender Policy Framework (SPF), DomainKeys Identified Mail (DKIM), and Domain-based Message Authentication, Reporting, and Conformance (DMARC). Because the email traverses Microsoft’s official sending infrastructure, it inherently passes these crucial checks. The visible authentication results, often scrutinized by security analysts, show clean passes across the board: DKIM validation succeeds against microsoft.com, DMARC policy is respected, and SPF confirms the sending IP is authorized. This authentication legitimacy grants the malicious payload immediate credibility, allowing it to sail past many perimeter defenses that flag external, unauthenticated lookalikes.
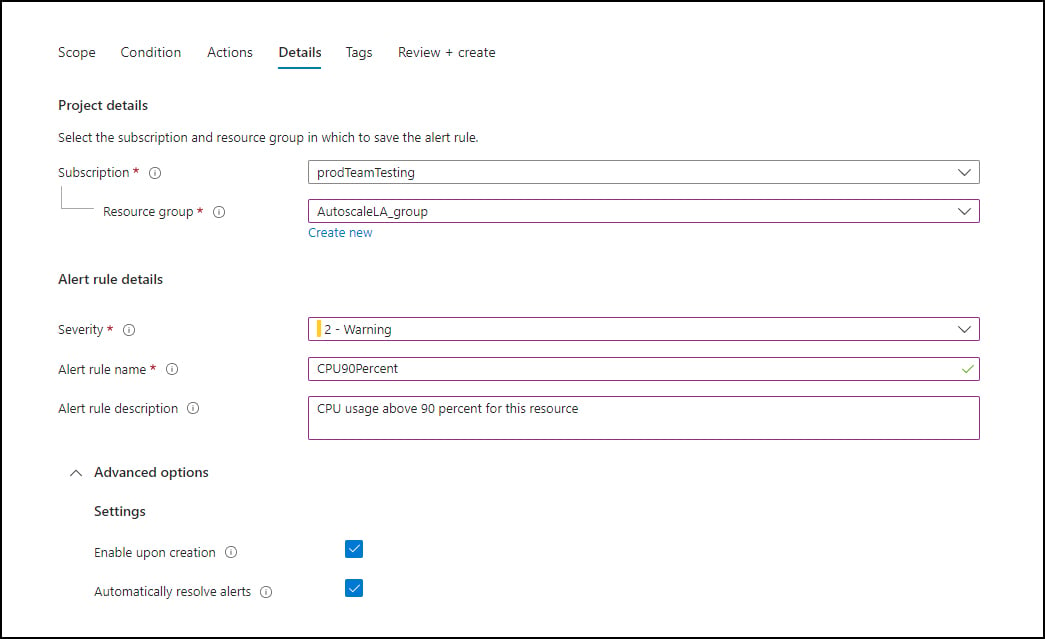
The mechanism for injecting the malicious content exploits a feature within the Azure Monitor alert configuration settings. When setting up metric or log-based alerts, administrators are given a customizable field—the "Alert rule description"—where contextual information about the triggered condition can be placed. Attackers are populating this field with their entire callback phishing script, complete with fabricated transaction details and the fraudulent support phone numbers.
These alerts are then directed not to a standard administrative email address, but to a staging address controlled by the threat actor. This staging address is typically set up as a low-volume mailing list or distribution group within the attacker’s control. The final step involves this controlled list automatically forwarding the legitimate-looking, authenticated alert to a large, untargeted pool of potential victims. This relaying process cleverly preserves the original, pristine Microsoft email headers and authentication metadata, maintaining the illusion of authenticity throughout the delivery chain.
Industry Context and The Erosion of Trust in Observability Tools
This exploitation highlights a persistent vulnerability in the security posture of modern cloud environments: the inherent conflict between administrative utility and security exposure. Cloud monitoring tools are designed for maximum deliverability and transparency; they must ensure administrators never miss a critical alert regarding service availability or billing anomalies. Threat actors are systematically turning this intended reliability into a vector for deception.
The shift toward Infrastructure as Code (IaC) and automated deployment, while improving efficiency, simultaneously expands the attack surface for configuration-based abuse. An attacker who gains even temporary, low-privilege access to an Azure environment—perhaps through a compromised developer credential or a weak service principal—can create these sleeper alert rules. Once established, the rule can persist and execute its malicious payload repeatedly until detected and manually disabled by a security team investigating the resulting emails.
This trend is not unique to Azure Monitor; similar abuses have been documented utilizing AWS CloudWatch, Google Cloud Operations Suite, and various ticketing systems where administrators can define custom notification messages. The lesson for the industry is that the security perimeter must extend beyond the ingress and egress of the platform itself to include the integrity of configuration settings that govern outbound communications.
Expert Analysis: Social Engineering Meets Infrastructure Abuse
From an expert analysis perspective, this campaign represents a sophisticated blending of technical evasion and high-leverage social engineering. The choice of callback phishing over traditional click-through phishing is significant. Click-through phishing (where the victim clicks a malicious link) can often be mitigated by browser security features, URL scanning, and endpoint protection. Callback phishing, conversely, seeks to initiate a direct, voice-based confrontation.
- Immediacy and Control: A phone call forces an immediate response, capitalizing on panic generated by the fake charge notification. Once on the phone, the attacker gains complete control over the interaction, bypassing email filters and browser security layers entirely.
- Impersonation Depth: Impersonating the "Fraud Detection Team" of a globally recognized entity like Microsoft allows the scammer to leverage deep-seated user anxiety regarding financial data and service access. The use of Windows Defender as the cited merchant adds a layer of familiarity and perceived relevance, even for users who might not be primary Azure subscribers but might hold personal Microsoft accounts linked to billing.
- Targeting Enterprise Footprints: The corporate theme suggests a potential pivot towards Business Email Compromise (BEC) precursors. If these emails are landing in corporate inboxes, they are likely targeting IT administrators, finance departments, or cloud engineers who are accustomed to receiving authentic Azure notifications. Successful manipulation here could lead to credential harvesting for the cloud tenant or unauthorized financial transfers disguised as legitimate service payments.
The reference to specific, high-precision alert categories—invoices, payments, and new order notifications—confirms that the attackers are mapping their social engineering narrative directly onto the language of cloud financial management, making the lures highly plausible within a technical context.
Future Impact and Mitigation Strategies
The persistence of this technique implies that, absent direct platform intervention from Microsoft, these phishing attempts will continue to thrive until end-users develop acute suspicion regarding any unsolicited request for real-time verification via telephone, regardless of the email’s origin authentication.
Implications for Cloud Providers:
Cloud providers like Microsoft must urgently review the scope of customizable fields within their notification services. If a field permits arbitrary, high-impact text insertion that controls external communication, stricter filtering or mandatory contextual linking to the actual monitored resource should be enforced. For instance, an alert description should perhaps only permit text referencing the specific metric ID or resource name, rather than allowing freeform text that constitutes a complete call-to-action script. Furthermore, internal monitoring should flag the creation of new alert rules that utilize high-urgency keywords ("SECURITY NOTICE," "FRAUD," "IMMEDIATE ACTION") combined with external contact information.
Recommendations for Security Teams:
For organizations utilizing Azure, defense must be multi-layered:
- Internal Policy Dissemination: Security awareness training must be updated specifically to address infrastructure-originated phishing. Employees must be trained that Microsoft will never request sensitive verification or issue security holds via an unsolicited phone number provided in an automated alert. All billing or security concerns should be routed through established, pre-verified support channels or directly via the Azure portal login.
- Alert Configuration Audits: Security and governance teams must regularly audit all active Azure Monitor alert rules, specifically looking for descriptions that contain external phone numbers, explicit calls to action, or non-standard verbiage. This should be integrated into routine compliance checks.
- Conditional Access Policies: Where possible, Multi-Factor Authentication (MFA) should be enforced universally, making it significantly harder for attackers to use stolen credentials—even if they manage to trick an employee into providing them over the phone.
The exploitation of Azure Monitor alerts represents a dangerous evolution in phishing methodology, leveraging the very tools designed to secure cloud operations as conduits for fraud. It underscores a fundamental reality: in the age of sophisticated cloud tooling, trust must be earned through verification, not assumed based on authentication headers.