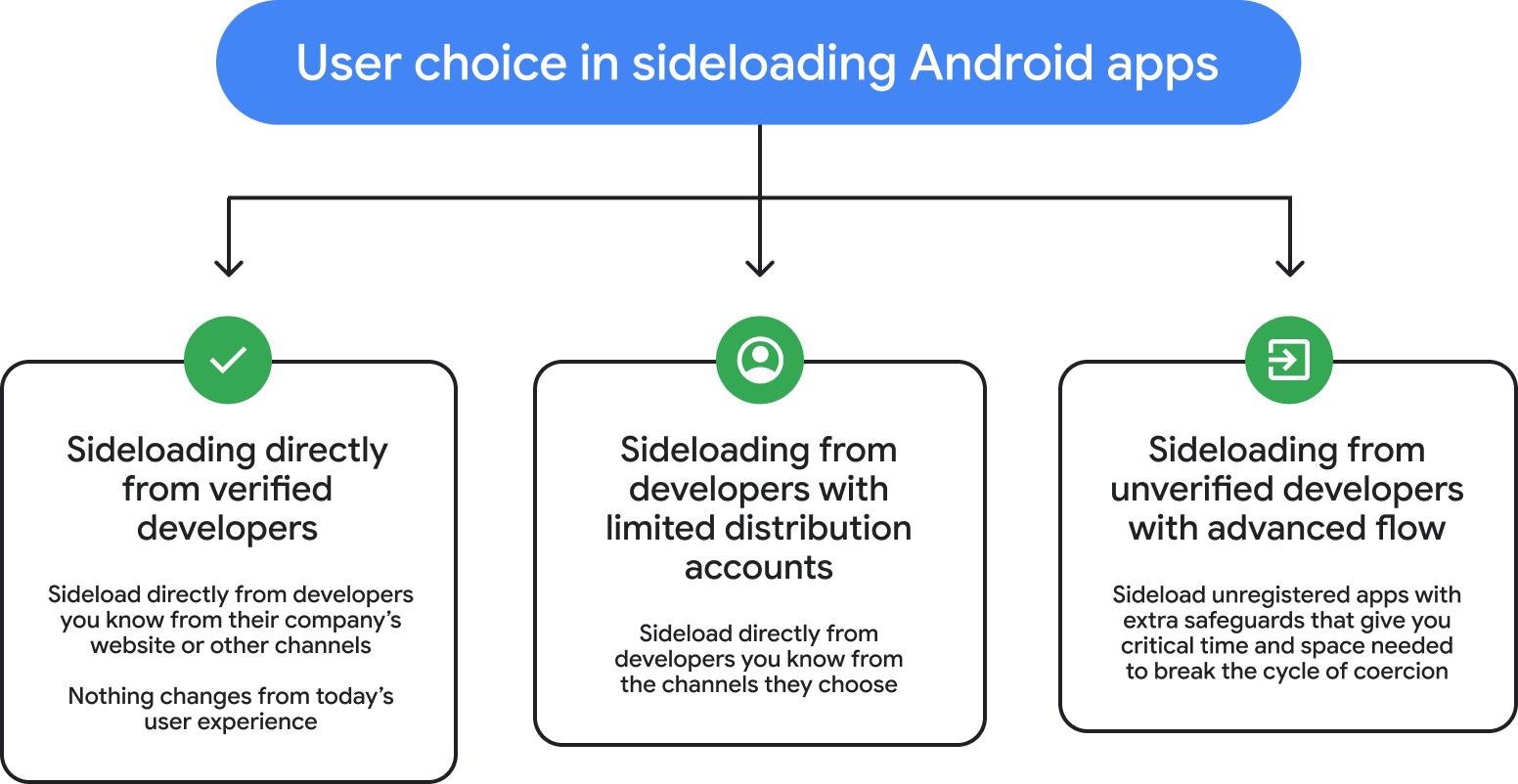
The landscape of mobile application distribution is undergoing a significant structural shift, catalyzed by ongoing efforts to mitigate pervasive digital threats. Central to this evolution is Google’s introduction of a novel security protocol dubbed "Advanced Flow" within the Android operating system. This mechanism is specifically engineered to address the nuanced security risks associated with sideloading Application Package Kits (APKs) sourced from developers whose identities have not yet been formally verified by Google. Scheduled for deployment in August, this new framework attempts to strike a delicate equilibrium: preserving the necessary flexibility for advanced users and niche developers while erecting robust safeguards against the surging tide of malicious software and sophisticated social engineering scams.
The impetus for this development is starkly quantifiable. The Global Anti-Scam Alliance (GASA) has reported staggering figures, estimating that illicit online activities, frequently involving the deceptive installation of compromised applications, resulted in approximately $442 billion in global financial losses last year alone. This massive economic impact underscores the urgent need for systemic countermeasures that move beyond traditional perimeter defenses. For the Android ecosystem, which champions openness and allows for third-party app sources outside the curated Google Play Store, this presents a perpetual security tightrope walk.
Advanced Flow is not a blanket relaxation of security but rather a targeted intervention designed to disrupt the psychological manipulation inherent in many modern cyberattacks. Scammers often rely on creating an immediate, high-stakes scenario—such as threats of financial insolvency, legal repercussions, or harm to a loved one—to coerce victims into taking rapid action. In these moments of manufactured panic, victims are often guided over the phone or through persistent remote access to bypass standard security prompts and consent to installing untrusted software.
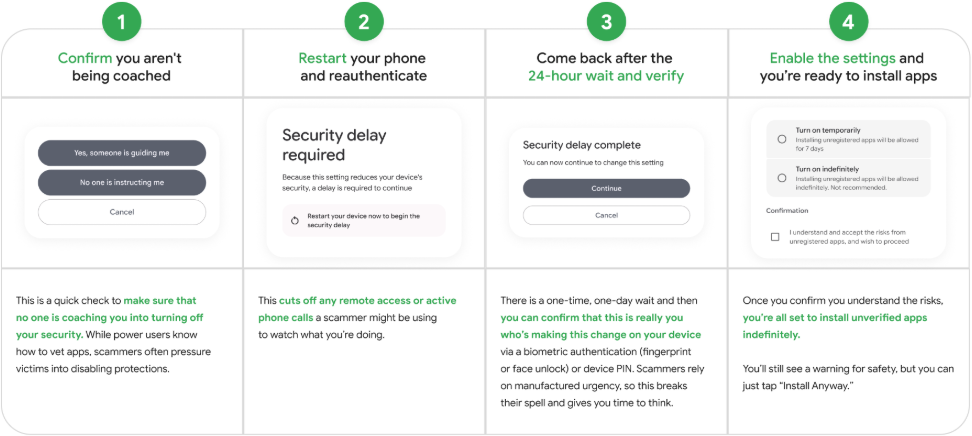
The design philosophy behind Advanced Flow directly counters this tactic by introducing deliberate, cognitive friction. It mandates a multi-stage, one-time setup procedure exclusively for power users opting to install applications from unverified sources. While the precise procedural steps are detailed in forthcoming documentation, the overarching mechanism forces the user to actively acknowledge the elevated risk and complete a more involved authentication or confirmation sequence than a standard installation prompt. This mandatory pause is intended to break the scammer’s coercive momentum, providing the user a crucial window—even if brief—to reconsider their actions or seek external advice before irrevocably compromising their device security.

Once this initial hurdle is cleared, users gain the privilege to install applications from these unverified entities. Crucially, this privilege is time-bound or explicitly reaffirmed. Users will be granted the ability to keep the application active for a limited duration, perhaps one week, necessitating a renewal of the Advanced Flow confirmation, or they can opt for an indefinite exception, which will invariably trigger persistent, high-visibility warnings within the Android interface indicating the application’s unverified status. This constant visual reminder serves as an ongoing deterrent and informational alert, differentiating these sideloaded apps from those vetted through the standard Play Store process.
This new mechanism is intrinsically linked to Google’s broader, long-term strategy: the comprehensive Developer Verification scheme. Announced initially in August of the preceding year, this verification mandate seeks to establish a baseline identity verification standard for all entities publishing Android applications, irrespective of their distribution channel—be it the Play Store, independent APK repositories, or direct developer uploads. The goal is foundational security: ensuring that every developer operating within the certified Android environment has a traceable, verified identity linked to their published code.
It is worth noting the political and practical turbulence surrounding the initial rollout of the Developer Verification scheme. Community feedback, particularly from independent developers and niche application providers who rely on direct distribution for specialized or beta software, prompted Google to revise the original implementation timeline. While the backlash led to a retraction of the immediate, sweeping application of the rule, the core objective remains firm. The August 2026 target for the full implementation of identity verification stands, making Advanced Flow a necessary interim measure to manage the transition period for those who legitimately require sideloading capabilities outside the verified ecosystem.
Industry Implications: Balancing Openness and Control
The introduction of Advanced Flow carries significant implications across the mobile development and cybersecurity industries. For the established, compliant developer community, the impact is minimal; their applications, when distributed via official channels, will continue through existing, streamlined processes. However, for those operating in the grey areas—independent game developers, enterprise internal distribution channels, and open-source projects that value anonymity or rapid deployment without full corporate vetting—Advanced Flow represents both a necessary pathway and an increased bureaucratic hurdle.
From a cybersecurity standpoint, this move represents a sophisticated shift from reactive malware detection to proactive user conditioning. Traditional mobile security relies heavily on static analysis, behavioral monitoring, and reputation scoring of applications. While these tools remain essential, they are increasingly circumvented by highly targeted, zero-day, or polymorphous malware. Advanced Flow shifts some of the burden back to the user, but critically, it empowers them by providing structured resistance against social engineering. By making the process inconvenient only when a user is engaging with an unverified source, Google effectively weaponizes the required effort against the scammer’s primary tool: speed and deception.
For security researchers and platform integrity teams, Advanced Flow provides a valuable control group. It segregates installs based on verification status, allowing for more granular telemetry on security incidents originating from sideloaded versus official sources. If successful, this could lead to more tailored future security enhancements, perhaps dynamically adjusting device permissions or sandboxing behaviors for apps installed via this flow, even after the initial verification.
Expert Analysis: The Psychology of Friction in Security
Security architecture often struggles with the usability paradox: the more secure a system is, the more cumbersome it becomes for the legitimate user. Advanced Flow appears to be an intentional application of behavioral economics in security design. Experts in human-computer interaction (HCI) often discuss "sludge," which refers to any process that requires extra steps or cognitive load. In the context of fraud prevention, introducing strategic sludge is a known tactic.
The effectiveness hinges on the assumption that a user actively targeted by a scammer—who is under duress—will be less likely to navigate a multi-step, unusual process than a power user who is deliberately seeking out a specific, unverified application. A scammer coaching a victim wants them to click "OK" three times rapidly; they do not want the victim to stop, read an intermediary warning screen, and then manually confirm a secondary authorization within a separate system menu. This momentary delay forces a cognitive check. The system demands the user consciously state, "Yes, I understand this is outside the standard safety net, and I am proceeding deliberately."
This contrasts sharply with the historical method of sideloading, where a single toggle switch ("Install unknown apps") often provided permanent access without recurring checks. The temporary nature of the Advanced Flow permission (the week-long option) suggests an understanding that even power users might forget the context of an installation after several days, prompting a necessary security re-evaluation.
Future Trajectory and Evolving Threats
The August rollout of Advanced Flow is positioned as a bridge to the fully implemented Developer Verification system. As the latter comes online, the need for Advanced Flow may diminish for apps that successfully complete the verification process. However, the utility of the flow itself may persist for several reasons:
- Non-Certified Devices: While the verification mandate targets "certified Android devices," there remains a segment of the market utilizing custom ROMs or older, uncertified hardware where Google Play Services are unavailable or intentionally excluded. These environments will always require some form of manual installation, and Advanced Flow offers a standard safety envelope where none previously existed.
- Beta and Experimental Software: Developers testing bleeding-edge features or hardware integration often require rapid distribution methods that cannot wait for the full verification pipeline. Advanced Flow legitimizes this testing channel under a controlled security context.
- Regulatory Environments: As jurisdictions worldwide, particularly in Europe under evolving digital markets legislation, mandate greater app store choice, the mechanism for securely installing alternatives to proprietary stores becomes paramount. Advanced Flow could serve as a model for how regulators might enforce security standards on alternative app marketplaces without completely closing off access.
Looking ahead, the sophistication of malware will continue to evolve, likely focusing on exploiting vulnerabilities within the Advanced Flow mechanism itself—perhaps by attempting to immediately re-trigger the high-pressure scenario after the initial flow is completed, or by exploiting the temporary nature of the permission window to execute delayed-action payloads. Consequently, this system will necessitate ongoing updates, potentially incorporating behavioral analysis that monitors the activity of an unverified application, not just its installation vector. If an app installed via Advanced Flow begins exhibiting highly suspicious network activity or permission escalation attempts shortly after installation, the system might automatically revoke the temporary permission, forcing another manual review.
In essence, Google is engineering a dynamic security posture that recognizes user intent and context. By segmenting users into risk profiles—the verified majority and the explicitly self-selecting power users—they can apply security overhead precisely where it is most needed, while acknowledging that absolute lockdown is antithetical to the open nature that defines the Android platform for many advanced users and developers. The success of Advanced Flow will ultimately be measured not just in the reduction of successful scams, but in its ability to remain unobtrusive enough for legitimate power users while remaining frustrating enough to deter automated or coercive social engineering attacks.

