Cloud Software Group (CSG), the parent entity overseeing Citrix technologies, has issued an urgent directive to network and security administrators worldwide: immediately apply patches to NetScaler Application Delivery Controller (ADC) and NetScaler Gateway appliances to mitigate two newly disclosed vulnerabilities. The timing and nature of the more severe of these flaws—CVE-2026-3055—have raised immediate alarms across the cybersecurity landscape due to its striking resemblance to the notorious, highly-exploited memory-reading vulnerabilities that have plagued the platform in recent years, specifically the infamous CitrixBleed (CVE-2023-4966) and its successor, CitrixBleed2.
The gravity of this situation stems from the inherent architecture of modern enterprise access points. NetScaler ADC and Gateway solutions are foundational components in securing remote access (SSL VPN, CVPN) and managing application delivery for countless organizations. Any vulnerability allowing unauthorized information disclosure in these perimeter devices represents a high-fidelity pathway for threat actors seeking initial network foothold or session hijacking capabilities.
Deep Dive into CVE-2026-3055: The Memory Overread Risk
The most pressing concern is CVE-2026-3055, classified as a critical security defect stemming from inadequate input validation within appliances specifically configured to function as a Security Assertion Markup Language (SAML) Identity Provider (IDP). This vulnerability permits unauthenticated, remote attackers to potentially trigger a memory overread condition. In practical terms, this exploit mechanism allows a malicious actor to read sensitive data residing in the appliance’s memory space. The potential payload includes, but is not limited to, active session tokens, authentication credentials, or other transient data crucial for maintaining secure connections. The ability to exfiltrate session tokens is particularly dangerous, as it enables session hijacking without requiring the attacker to possess any prior credentials or privileged access to the targeted system—a classic recipe for immediate compromise.
CSG’s advisory explicitly communicated the urgency: "Cloud Software Group strongly urges affected customers of NetScaler ADC and NetScaler Gateway to install the relevant updated versions as soon as possible." This level of declarative warning underscores the internal assessment that exploitation risk is immediate and potentially widespread, particularly given the historical precedent set by similar vulnerabilities. Comprehensive remediation guides have been published, detailing the exact steps required to identify vulnerable configurations and deploy the necessary fixes across affected versions of NetScaler ADC and Gateway (specifically targeting versions 13.1 and 14.1, with patches issued as 13.1-62.23 and 14.1-66.59, respectively, alongside specific FIPS and NDcPP builds).
The Echo of Past Catastrophes: Industry Implications
The comparison drawn by security analysts between CVE-2026-3055 and the previous "Bleed" vulnerabilities is not mere hyperbole; it reflects a pattern of systemic risk within memory-handling components of the NetScaler code base. Both CitrixBleed and CitrixBleed2 resulted in massive, multi-year compromises across government agencies, critical infrastructure, and commercial entities globally. These prior incidents demonstrated that once an out-of-bounds read vulnerability is weaponized, its exploitation becomes rapid, widespread, and often goes undetected until post-incident forensics reveal the extent of data exfiltration.
Cybersecurity firms have been quick to voice concerns. WatchTowr noted the distressing familiarity: "Unfortunately, many will recognise this as sounding similar to the widely exploited ‘CitrixBleed’ vulnerability from 2023 and the subsequent ‘CitrixBleed2’ variant disclosed in 2025, both of which were and continue to be actively leveraged in real-world attacks." This ongoing threat landscape is exacerbated by the fact that organizations often struggle to completely purge legacy exposures, leaving vulnerable instances exposed long after patches are available.

Furthermore, while CSG indicated the vulnerability was identified internally, the reality of patch deployment cycles dictates that exploitation attempts are inevitable once the vulnerability details become public. Rapid7 articulated this risk clearly: "Exploitation of CVE-2026-3055 is likely to occur once exploit code becomes public. Therefore, it is crucial that customers running affected Citrix systems remediate this vulnerability as soon as possible." The window between patch release and weaponization is shrinking, demanding proactive threat hunting rather than reactive defense.
Analyzing CVE-2026-4368: Session Integrity at Risk
While CVE-2026-3055 targets data theft via memory reading, the secondary vulnerability, CVE-2026-4368, targets session integrity. This flaw affects NetScaler appliances configured as Gateways (handling SSL VPN, ICA Proxy, CVPN, RDP proxy) or those utilizing AAA virtual servers. This bug leverages a race condition, a notoriously difficult-to-exploit but highly effective class of vulnerability. A low-privilege attacker could theoretically exploit this race condition to cause a user session mix-up. In a production environment, this could mean one user unintentionally gains access to the resources or session data of another user whose connection was processed milliseconds before or after theirs, leading to lateral movement or unauthorized access escalation.
The complexity of race conditions often means they are less prone to mass, automated exploitation than simple buffer overflows, but they pose a significant threat in targeted, sophisticated attacks where precision timing can yield high-value access. The fact that both vulnerabilities reside in core access components—one for data theft, the other for session corruption—presents a dual-pronged attack surface that security teams must address simultaneously.
The Scale of Exposure and Remediation Challenges
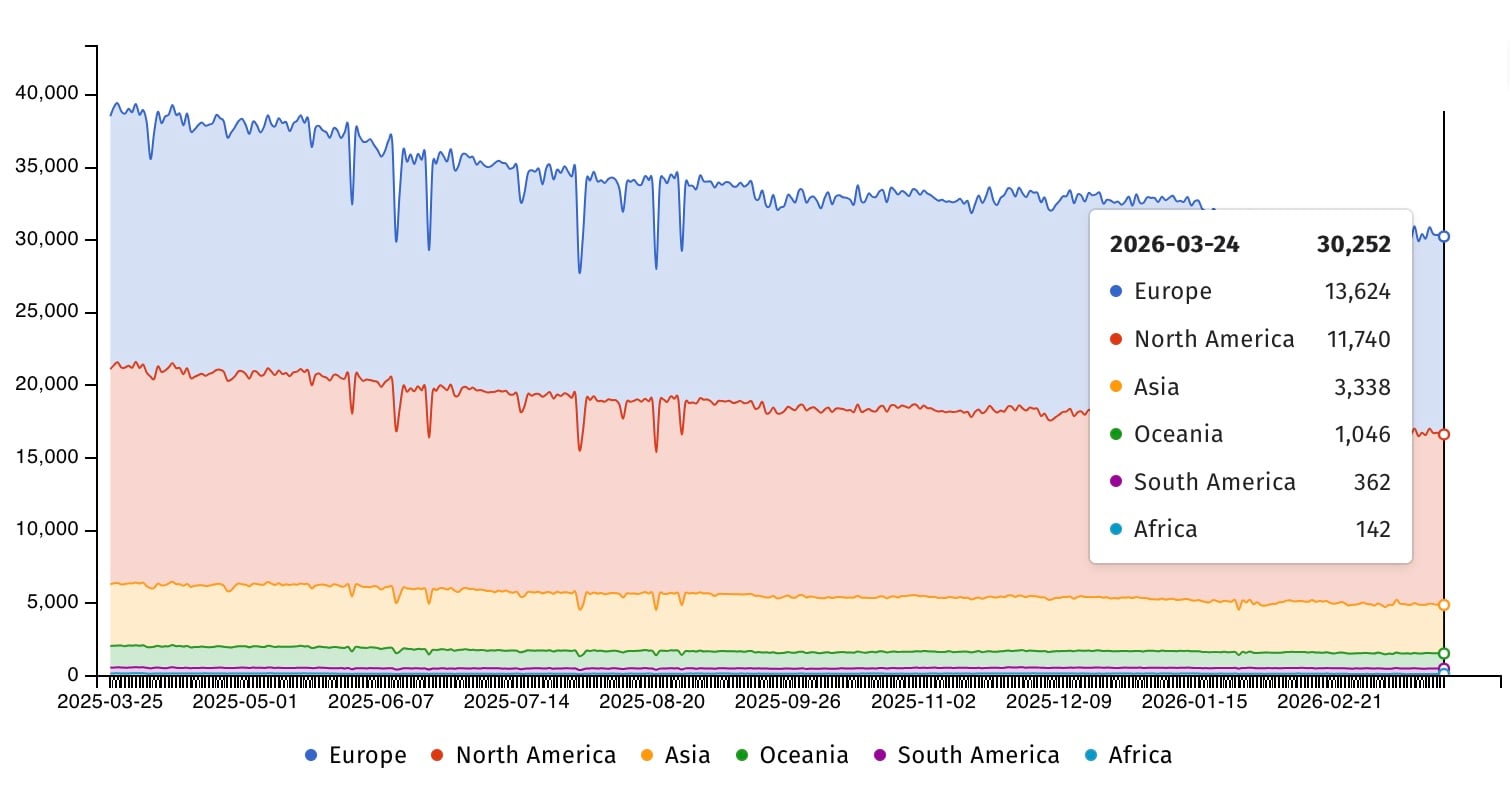
The sheer volume of exposed NetScaler devices underscores the magnitude of the remediation challenge. Security intelligence from groups like Shadowserver indicates that thousands of NetScaler ADC instances (over 30,000 tracked) and thousands of Gateway instances (over 2,300 tracked) remain actively visible on the public internet. While not every exposed device is necessarily vulnerable—patching status varies widely, and not all installations use the SAML IDP feature—the attack surface area is immense.
The history of previous Citrix vulnerabilities suggests a slow, painful patching process for many organizations. The US Cybersecurity and Infrastructure Security Agency (CISA) has repeatedly highlighted this issue. For instance, CISA flagged CitrixBleed2 as actively exploited in August 2025, enforcing a near-immediate patching deadline for federal agencies. In total, CISA has cataloged 21 Citrix vulnerabilities as being exploited in the wild, seven of which have been linked directly to ransomware operations. This track record establishes a strong pattern: if it’s a critical Citrix flaw, it will be weaponized, and failure to patch quickly translates directly into heightened organizational risk, potentially leading to catastrophic operational impact, including ransomware deployment.
Expert Analysis: Memory Safety and the Perimeter Defense Dilemma
From an engineering perspective, repeated memory safety issues in high-performance network appliances point toward systemic challenges in secure software development lifecycle (SDLC) practices, particularly concerning C/C++ codebases handling network packet parsing and state management. Out-of-bounds reads (OOBR) are classic memory corruption bugs. While modern languages offer built-in memory safety, high-performance network infrastructure often relies on lower-level languages for speed, necessitating rigorous manual memory auditing and fuzzing—processes that these recent findings suggest may have been insufficient.
The primary implication for the industry is a heightened scrutiny of all network perimeter devices that handle authentication state or terminate VPN tunnels. These devices are the "keys to the kingdom." Attackers prioritize them because a single successful compromise grants them deep insight into enterprise traffic and user identities. For organizations utilizing NetScaler, the immediate future involves not just applying the vendor-supplied binaries but undertaking comprehensive post-patch verification.
Future Impact and Trends: Moving Beyond Reactive Patching
The cycle of discovery, patching, and inevitable exploitation of NetScaler flaws forces organizations to re-evaluate their entire posture regarding these devices. Future security strategies must pivot from reactive application of vendor patches to proactive defense-in-depth architectures.
-
Segmentation and Least Privilege: If an appliance must remain exposed for remote access, rigorous network segmentation must isolate it from core internal assets. Furthermore, configurations should be audited to ensure that only absolutely necessary services (e.g., specific SAML functions) are enabled, minimizing the potential blast radius should a vulnerability surface in an unused code path.
-
Automated Vulnerability Management: The speed at which these flaws become zero-days necessitates a dramatic reduction in time-to-patch. Organizations must invest in automated systems capable of identifying vulnerable assets globally, pulling down approved patches, and deploying them across distributed environments within hours, not days or weeks. The Shadowserver data on exposed devices highlights the vast number of unmanaged or poorly inventoried assets that remain at risk.
-
Zero Trust Integration: As these vulnerabilities compromise established perimeter trust (like VPN sessions), organizations must accelerate the transition to Zero Trust Network Access (ZTNA) architectures. Even if an attacker steals a NetScaler session token via CVE-2026-3055, a robust ZTNA framework should prevent that token from granting blanket access to the internal network, requiring continuous authentication and authorization checks for every resource request.
-
Threat Intelligence Integration: Security operations centers (SOCs) must immediately integrate indicators of compromise (IOCs) related to memory corruption exploits into their monitoring pipelines. Given the similarity to past attacks, specific telemetry patterns indicative of memory manipulation attempts should trigger high-severity alerts, even before formal exploit code is publicly released.
In conclusion, the emergence of CVE-2026-3055 is a stark reminder that foundational infrastructure security remains a volatile challenge. Cloud Software Group’s urgent call to action must be heeded without delay. For network administrators, this is not a routine maintenance task; it is an emergency security mandate directly tied to preventing the next major enterprise breach fueled by compromised remote access infrastructure. The time elapsed between reading this advisory and completing the patch deployment is a direct measure of organizational risk exposure.

