The digital security landscape is witnessing a significant evolution in social engineering tactics, marked by the increasingly sophisticated abuse of legitimate, widely trusted platforms to circumvent established email and endpoint security protocols. Recent findings highlight a concerning trend where threat actors are leveraging the no-code application development environment, Bubble, to host and deploy highly effective phishing lures specifically targeting Microsoft account credentials. This methodology fundamentally exploits the trust inherent in established infrastructure, rendering traditional security gatekeepers less effective.
The Mechanism of Evasion: Trust as a Weapon
At the core of this attack vector is Bubble’s operational model. Bubble positions itself as an AI-powered, no-code platform, allowing users to conceptualize and deploy functional web applications rapidly. Crucially, the resulting applications are hosted directly on Bubble’s own infrastructure, bearing domains such as *.bubble.io. For enterprise security solutions—particularly email gateways designed to scan URLs for known malicious domains or suspicious redirection patterns—the bubble.io domain carries a high inherent trust score. This established reputation means that links directing users to these hosted applications often pass through security filters unimpeded.
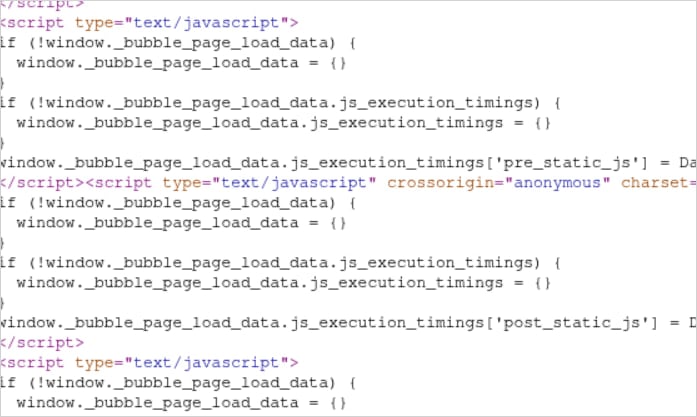
Security researchers have detailed how attackers construct their malicious payloads within this environment. Instead of hosting a direct, easily identifiable phishing form, the attackers engineer Bubble applications that are structurally complex. These applications often involve extensive, convoluted JavaScript bundles coupled with heavy utilization of the Shadow DOM (Document Object Model). This architectural obfuscation serves a dual purpose: it frustrates human analysts attempting to quickly audit the application’s purpose, and more critically, it confuses automated static analysis tools. These tools, programmed to identify patterns associated with typical redirection scripts or known phishing code signatures, frequently misclassify the complex, legitimate-looking structure generated by Bubble’s framework as benign or merely functional code.

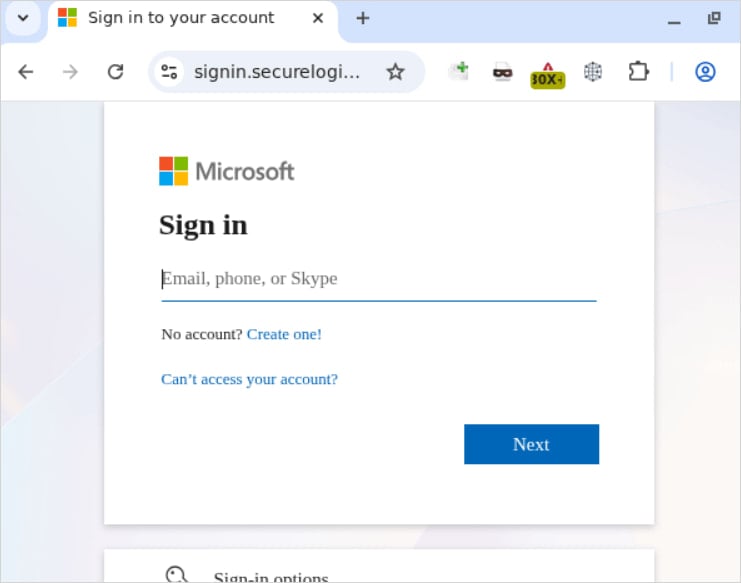
Once the user clicks the seemingly safe link delivered via email or chat, they land on the intermediary Bubble application. This application then executes a calculated redirection to the final destination—the actual credential harvesting page. This final page is meticulously crafted to mimic the genuine Microsoft login portal, often utilizing high-fidelity graphical assets and branding associated with Microsoft 365 or Azure Active Directory. In some observed campaigns, an additional layer of deception is employed: the phishing site is strategically placed behind a Cloudflare challenge, further bolstering the appearance of legitimacy and potentially frustrating automated crawlers that cannot resolve the CAPTCHA or similar verification steps.
The objective remains the illicit capture of sensitive information. Any credentials—usernames, passwords, and potentially multi-factor authentication codes if the attacker is employing advanced techniques—entered into these meticulously forged login forms are immediately relayed back to the threat actor. The successful acquisition of Microsoft 365 credentials grants adversaries deep access to corporate ecosystems, including email archives, calendar data, shared documents, and potentially the keys to broader network access via single sign-on (SSO) dependencies.
Industry Implications: A Crisis for Domain Trust
The weaponization of legitimate cloud platforms, often referred to as "cloud-hopping," represents a growing systemic challenge in cybersecurity. This trend moves beyond simply compromising vulnerable servers; it leverages the established security posture of reputable Software-as-a-Service (SaaS) providers.
For security vendors specializing in email protection, this development necessitates a significant shift in detection methodology. Reliance on domain reputation and blacklisting is clearly insufficient when the payload is hosted on a domain with billions of legitimate transactions. Future solutions must pivot toward advanced behavioral analysis and content scrutiny, even on trusted domains. This requires deeper inspection of code execution paths, dynamic analysis that monitors for unauthorized data transmission following user input, and sophisticated anomaly detection that flags unusual client-server interactions originating from an otherwise trusted subdomain.
Furthermore, the use of no-code/low-code (NCLC) platforms like Bubble by malicious actors exposes a critical blind spot in the governance of these tools. While NCLC environments democratize application development, they inherently lower the barrier to entry for malicious deployment. If these platforms do not implement robust, proactive abuse monitoring and rapid takedown procedures, they become unwitting conduits for cybercrime. The complexity of the generated code—the "massive jumble of JavaScript"—makes manual security review impractical at scale, placing the onus squarely on the platform provider to enforce acceptable use policies through automated means capable of deciphering these obfuscated payloads.
Expert Analysis: The Evolution of Phishing-as-a-Service
This specific abuse of Bubble is not an isolated incident perpetrated by lone actors; it signals the rapid integration of sophisticated evasion techniques into the Phishing-as-a-Service (PhaaS) ecosystem. PhaaS platforms are commercialized toolkits that offer turnkey solutions for launching large-scale campaigns, often bundling highly sought-after capabilities for a subscription fee.
These platforms already feature capabilities designed to defeat modern security stacks, such as advanced session cookie theft, the implementation of Adversary-in-the-Middle (AiTM) proxy layers designed to neutralize standard Two-Factor Authentication (2FA) prompts, geo-fencing logic to avoid security researchers in specific locales, and AI-generated, highly personalized email lures. The integration of legitimate cloud hosting—especially via trusted no-code builders—is the logical next step in increasing the stealth and success rate of these operations. By outsourcing the hosting infrastructure to a platform like Bubble, lower-tier cybercriminals gain access to enterprise-grade evasion techniques without needing the technical acumen to manage compromised servers or exploit zero-day vulnerabilities for hosting.
The complexity of the generated code, as noted by researchers, is a key indicator of this professionalization. It demonstrates that attackers are actively reverse-engineering the output of NCLC tools to understand how to create structurally unique, yet functionally malicious, code that bypasses heuristics. This is an arms race where the sophistication of the attacker’s deployment environment directly challenges the efficacy of the defender’s analytical tools.
Future Impact and Proactive Defense Strategies
The adoption of this hosting strategy across the cybercriminal ecosystem signals a paradigm shift toward infrastructure agnostic phishing. As NCLC platforms proliferate across finance, marketing, and internal tooling, threat actors will invariably map and test every major provider—not just Bubble—for similar abuse potential.
For organizations, this necessitates a multilayered defense strategy that emphasizes context over mere URL reputation:
- Dynamic Content Analysis: Security tooling must evolve to execute and analyze web content in a sandboxed environment, watching for post-load behaviors like credential submission or unauthorized script execution, regardless of the hosting domain’s trust score.
- User Education Reinforcement: User training must shift focus from "avoiding bad links" to recognizing the subtle contextual anomalies of a login request. Training should emphasize checking the true URL immediately following an unexpected login prompt, even if the preceding link appeared safe.
- MFA Beyond Passwords: While AiTM attacks are increasingly prevalent, organizations must accelerate the adoption of phishing-resistant Multi-Factor Authentication (MFA) methods, such as FIDO2/WebAuthn hardware keys, which cryptographically bind the authentication session to the legitimate domain, rendering credential harvesting ineffective even if the password is stolen.
- Platform Accountability: Industry pressure on NCLC providers is essential. These platforms must invest heavily in abuse detection mechanisms specifically tailored to recognize malicious intent within their unique generated code structures. Proactive scanning of new deployments for signs of phishing infrastructure must become a core operational priority, perhaps leveraging machine learning models trained on the specific output patterns of these development environments.
The exploitation of Bubble’s infrastructure underscores a fundamental challenge in the modern internet architecture: the blurring line between legitimate digital utility and malicious deployment. As long as high-trust domains can host functionally deceptive content, cybercriminals will continue to leverage them to deliver high-impact attacks against critical assets like Microsoft 365 environments. Vigilance must now extend beyond the link itself and deeply into the execution environment of the content being delivered.

