In a coordinated strike against the proliferation of cybercrime-as-a-service, an international coalition of law enforcement agencies has launched a decisive phase of Operation PowerOFF. This extensive initiative, supported by Europol and involving authorities from 21 nations, has targeted the backbone of the "booter" industry—platforms that commodify Distributed Denial-of-Service (DDoS) attacks for anyone with an internet connection and a digital payment method. By seizing 53 malicious domains, arresting key operators, and issuing warnings to over 75,000 active users, this operation marks a significant escalation in the global effort to curb disruptive cyber warfare.
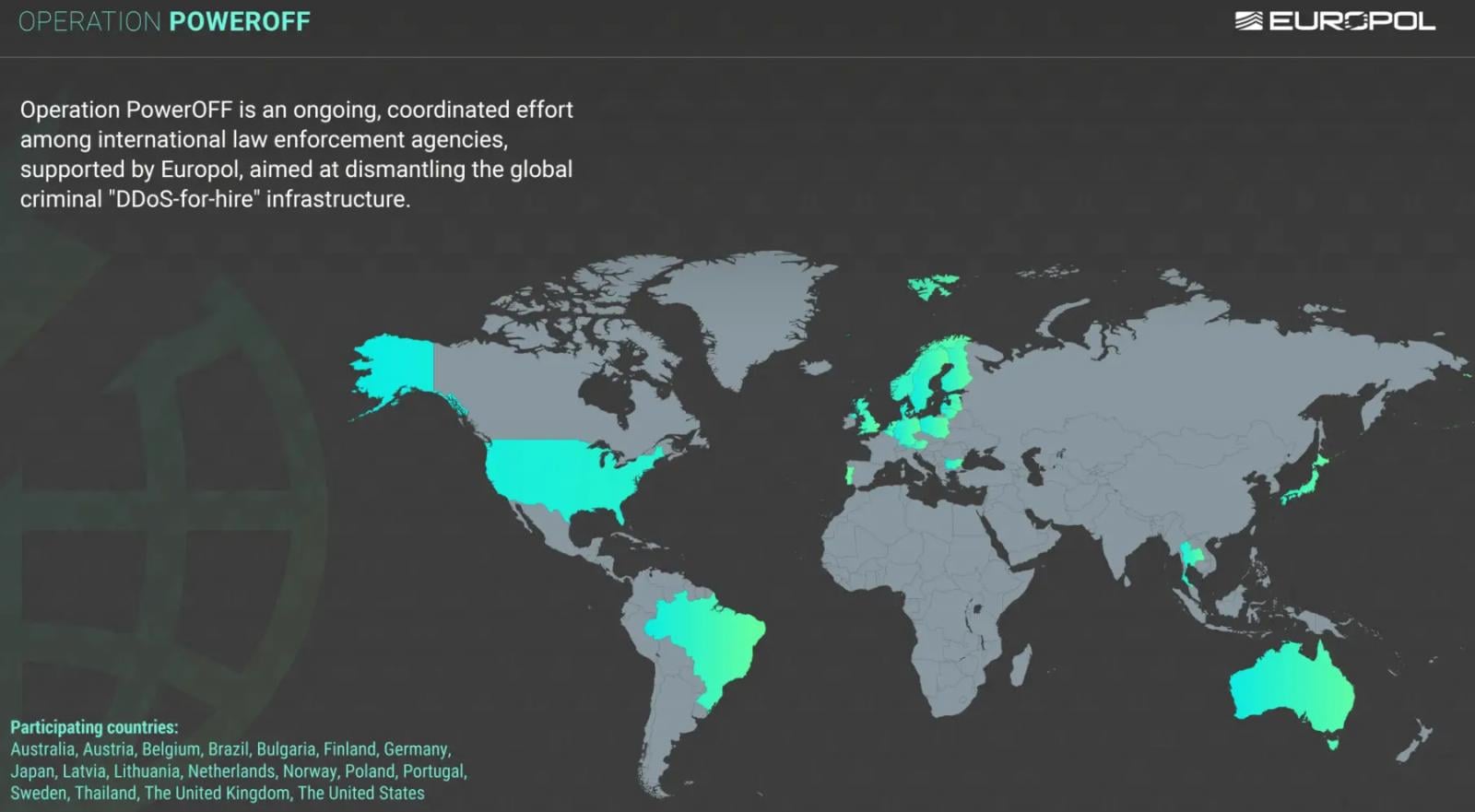
The scope of this operation reflects the borderless nature of modern digital threats. Spanning continents, the coalition includes the United States, the United Kingdom, Australia, Thailand, Japan, and Brazil, alongside several European Union member states. This multi-jurisdictional approach is essential, as the infrastructure supporting DDoS attacks—often consisting of massive botnets of compromised IoT devices and home routers—is geographically dispersed and designed to evade localized regulatory efforts.
The Anatomy of the Booter Industry
To understand the gravity of Operation PowerOFF, one must first recognize the evolution of DDoS attacks from a sophisticated hacker’s tool to a "plug-and-play" commodity. Booter services, often marketed under the thin veil of "stress testing" or "network diagnostics," provide users with an interface to rent the power of a botnet. These services do not require the user to possess any specialized programming knowledge. Instead, a user simply inputs the IP address of a target, selects the duration and intensity of the attack, and pays a fee—often in cryptocurrency.

The danger lies in the democratization of this destructive capability. What was once the domain of state-sponsored actors or advanced persistent threat (APT) groups is now accessible to teenagers, disgruntled employees, and petty criminals. By stripping away the technical barriers to entry, booter platforms have turned the internet into a volatile environment where any website, game server, or enterprise portal can be forced offline within seconds. The operators of these platforms often attempt to insulate themselves from legal liability by including terms of service that forbid illegal use, yet these policies are almost never enforced, and the platforms fail to implement rigorous verification processes to ensure that the user actually owns the target infrastructure.
A Paradigm Shift in Law Enforcement Strategy
The latest iteration of Operation PowerOFF signals a fundamental shift in how law enforcement agencies approach digital crime. Historically, authorities focused primarily on apprehending the architects of malware or the administrators of darknet marketplaces. While these "high-value" targets remain a priority, the current strategy recognizes that the resilience of the cybercrime ecosystem is built on a massive, decentralized user base. By directly engaging 75,000 individuals through personalized electronic communications—emails and warnings sent directly to the accounts linked to these services—law enforcement is shattering the illusion of anonymity.
These communications serve a dual purpose: they act as a legal deterrent, documenting the individual’s illicit activity for potential future prosecution, and they serve as a psychological shock to the user base. By making the consequences of using these services tangible, the coalition aims to shrink the market demand for DDoS-for-hire platforms.
Furthermore, the operational sprints leading up to this phase involved meticulous technical forensic analysis. Investigators dismantled the command-and-control (C2) infrastructure that enables these services to function. When 53 domains were taken offline, it was not merely a superficial removal of a website; it was a surgical strike against the backend servers that manage the botnet swarms.

The "Prevention" Phase: A New Frontier
As the operation transitions into its prevention phase, the focus has shifted toward proactive disruption. Europol and its partners are no longer just reacting to crimes after they occur; they are actively shaping the digital environment to discourage participation in cybercrime.
One of the most innovative aspects of this strategy is the use of search engine optimization (SEO) and targeted advertising to intercept potential offenders. When a user searches for terms related to "DDoS tools" or "booter services," they are increasingly likely to encounter law enforcement-sanctioned warnings rather than the tools themselves. By removing over 100 URLs from search results that promote these illegal services, the authorities are effectively "de-platforming" the criminal ecosystem from the mainstream web.
Additionally, the introduction of on-chain warning messages represents a cutting-edge approach to disrupting the financial incentives of these attacks. By tagging cryptocurrency transactions linked to known illegal services, investigators can alert the blockchain community and potentially flag the illicit origin of funds, making it increasingly difficult for operators to "cash out" their proceeds.
Industry Implications and the Road Ahead
The long-term success of Operation PowerOFF will depend on the sustainability of these prevention efforts. The cybersecurity industry has long struggled with the "whack-a-mole" nature of botnets, where a dismantled service is often replaced by a new, more resilient iteration within days. However, the sheer scale of the 75,000-user intervention suggests that the cost of entry into the booter market is rising. When the user base is intimidated and the infrastructure is frequently disrupted, the profitability of operating a booter service declines, eventually forcing the market to contract.
For enterprise and infrastructure security, these developments offer a temporary reprieve but highlight a persistent reality: the infrastructure of the internet is inherently vulnerable. The widespread use of IoT devices with poor security configurations provides an endless supply of "zombie" hardware that can be weaponized. Until manufacturers adopt "security-by-design" principles—such as forcing users to change default credentials and patching vulnerabilities in firmware—the supply side of the DDoS-for-hire market will remain robust.
Industry experts observe that while this operation is a resounding success, it must be matched by a commitment to collective defense. Organizations must move beyond static firewalls and adopt adaptive, context-rich validation mechanisms. As the threat landscape evolves, AI-driven exploits are beginning to chain multiple vulnerabilities together, meaning that traditional perimeter security is no longer sufficient. The recent wave of zero-day exploits underscores that the battle against DDoS is merely one front in a broader, more sophisticated war for digital stability.
Conclusion
Operation PowerOFF is a landmark event in the history of international cyber policing. It demonstrates that when sovereign nations align their resources, intelligence, and legal frameworks, they can exert significant pressure on the shadowy networks that facilitate digital disruption. By targeting the entire lifecycle of a DDoS attack—from the user who buys the service to the infrastructure that facilitates it, and finally the financial channels that reward it—the coalition is moving toward a more holistic model of digital governance.
The message to the cybercriminal community is clear: the era of consequence-free, "disposable" cyberattacks is coming to an end. As law enforcement continues to refine its tactics—integrating proactive search engine disruption, forensic blockchain analysis, and large-scale user identification—the threshold for engaging in illegal cyber activity will continue to rise. While the threat of DDoS will likely persist as long as the internet remains open and decentralized, initiatives like Operation PowerOFF prove that the digital world is becoming a significantly more difficult and dangerous environment for those who seek to weaponize it.

