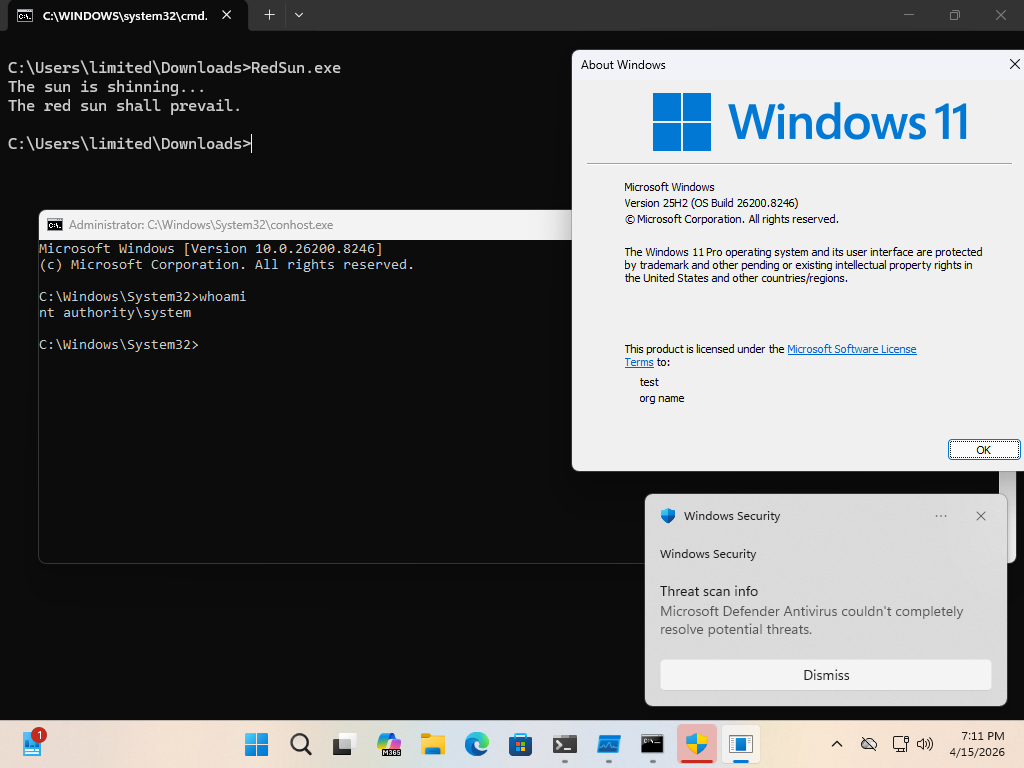
A critical security flaw in Microsoft Defender, identified by the security researcher known as "Chaotic Eclipse," has sent shockwaves through the cybersecurity community. Dubbed "RedSun," this local privilege escalation (LPE) vulnerability allows a standard user on a fully patched Windows environment—ranging from Windows 10 and 11 to various iterations of Windows Server—to gain full SYSTEM-level privileges. The disclosure of this zero-day follows a growing trend of public exploit releases that highlight a deepening rift between independent security researchers and corporate vulnerability disclosure programs.
The Anatomy of the RedSun Exploit
At its core, the RedSun vulnerability is a logical flaw in how Microsoft Defender manages file interactions, specifically when dealing with cloud-tagged files. The exploit functions by leveraging the Cloud Files API, a system component designed to optimize storage by managing files that reside in cloud storage services like OneDrive.
When Microsoft Defender detects a malicious file possessing a specific cloud tag, its internal remediation logic attempts to intervene. In a bizarre technical oversight, the antivirus engine—designed to neutralize threats—is effectively tricked into rewriting the identified file back to its original location. The exploit sequence is sophisticated: the researcher uses an oplock (opportunistic lock) to win a race condition involving the Volume Shadow Copy service. By manipulating this window of opportunity, the exploit employs a directory junction or reparse point to redirect the file rewrite operation.
Instead of restoring a benign file, the process forces the system to overwrite C:Windowssystem32TieringEngineService.exe with a malicious payload. Because the Cloud Files infrastructure operates with high-level permissions, the system executes the attacker-planted file as SYSTEM. Once the code is running with these elevated credentials, the attacker effectively gains total control over the operating system, bypassing all standard user-level security boundaries.

Expert Verification and Technical Nuance
The validity of the RedSun exploit has been confirmed by industry experts, including Will Dormann, a principal vulnerability analyst at Tharros. Dormann’s analysis corroborates that the exploit is functional on the most recent, fully patched Windows releases. He noted that the exploit’s efficacy is bolstered by its ability to bypass standard file system protections through the misuse of built-in API behaviors.
A point of contention in the security community regarding this specific disclosure is the use of the EICAR test file within the exploit code. EICAR is a standard, non-malicious file used specifically to test the response of antivirus software. Because the exploit uses EICAR to trigger the flawed rewrite behavior, many antivirus vendors immediately flag the exploit executable. However, the researcher demonstrated that by simply encrypting the EICAR string within the binary, they could significantly reduce the detection rate among traditional security tools, highlighting how easily such exploits can be obfuscated to evade signature-based detection.
A Growing Crisis in Coordinated Disclosure
The emergence of RedSun is not an isolated incident. It follows on the heels of another LPE vulnerability dubbed "BlueHammer," which was also disclosed by Chaotic Eclipse and subsequently patched by Microsoft as CVE-2026-33825 in the April 2026 update cycle. The researcher has explicitly stated that these public disclosures are a form of protest against the policies and conduct of the Microsoft Security Response Center (MSRC).
The allegations leveled by the researcher suggest a toxic environment for independent investigators. According to public statements, the researcher claimed to have been subjected to aggressive corporate behavior, describing interactions that felt less like professional collaboration and more like intimidation. These accusations touch upon a wider, systemic issue in the cybersecurity industry: the precarious power dynamic between massive software vendors and the researchers who find their flaws. When researchers feel that their professional reputations are being threatened or their work is being ignored—or worse, weaponized against them—the industry loses the "safety valve" of responsible disclosure.
Industry Implications and the Erosion of Trust
The fallout from this incident raises fundamental questions about the sustainability of the current vulnerability reporting model. Coordinated Vulnerability Disclosure (CVD) relies entirely on trust. When that trust breaks down, the results are predictable: researchers may opt to sell exploits on the black market to criminal syndicates or nation-state actors, or they may choose to release them publicly as a "scorched earth" tactic.

For enterprises, the existence of a high-privilege exploit that remains functional even after Patch Tuesday updates is a significant risk. If an attacker can escalate privileges from a low-level account to SYSTEM, they gain the ability to disable security software, install rootkits, exfiltrate sensitive data, and move laterally across a network with impunity. Security teams must now consider that even "fully patched" systems may have architectural vulnerabilities that reside in the very tools intended to protect them.
Future Trends: Security Architecture under Scrutiny
The RedSun exploit points to a larger problem: the complexity of modern operating systems. By integrating deep-level hooks for cloud synchronization and automated remediation, Microsoft has inadvertently created new, complex attack surfaces. The "Cloud Files API" is a prime example of a feature that, while convenient for users, adds layers of logic that are difficult to secure against race conditions and file system manipulation.
Moving forward, the industry is likely to see a shift toward more rigorous auditing of these "helper" APIs. Developers are increasingly moving toward memory-safe languages and more robust permission-isolation models, yet the legacy codebases of Windows remain a challenge. Furthermore, the incident underscores the need for better "Red Teaming" exercises that focus on the interaction between antivirus engines and OS kernel-level services.
Microsoft’s Stance and the Path Ahead
In response to inquiries regarding the researcher’s claims and the nature of the vulnerability, Microsoft maintains a standard stance on the importance of CVD. A spokesperson reiterated that the company remains committed to investigating security reports and protecting customers through timely updates. They emphasize that CVD is an industry-standard practice intended to ensure that vulnerabilities are mitigated before they can be weaponized in the wild.
However, the corporate boilerplate response does little to address the human element of the conflict. The cybersecurity research community is currently in a state of reflection, debating whether current bug bounty and disclosure frameworks provide enough protection for the individuals providing the labor. Without a more transparent and respectful engagement process, corporations like Microsoft risk alienating the very people who help identify flaws before they are exploited by malicious actors.
Conclusion: A Wake-Up Call for Security Teams
The RedSun zero-day serves as a potent reminder that software security is not a static destination but a continuous, volatile process. As long as researchers feel disenfranchised, the risk of "revenge disclosure" will remain a threat to global infrastructure.
For IT and security administrators, the immediate takeaway is the need for defense-in-depth strategies. Relying solely on a single endpoint protection agent is insufficient when that agent itself contains exploitable logic. Organizations should prioritize principle-of-least-privilege (PoLP) configurations, monitor for anomalous file system behavior, and maintain a rigorous patch management lifecycle.
As the industry moves toward 2027, the relationship between researchers and vendors will define the next chapter of cybersecurity. If the industry cannot find a way to reconcile the need for swift corporate patching with the rights and needs of the research community, the frequency of such disruptive public disclosures is likely to increase, further endangering the security of the global digital ecosystem. The RedSun exploit is not merely a technical failure; it is a symptom of a larger, more complex breakdown in the collaborative framework that keeps our systems safe.

