The landscape of browser security has been dramatically reshaped by the emergence of the VoidStealer malware, which has pioneered a sophisticated, debugger-centric method to circumvent Google Chrome’s Application-Bound Encryption (ABE) protections. This development marks a critical juncture in the ongoing arms race between application security teams and sophisticated threat actors, as VoidStealer successfully targets and extracts the highly protected v20_master_key—the cryptographic linchpin for all sensitive stored browser data—directly from the process memory.
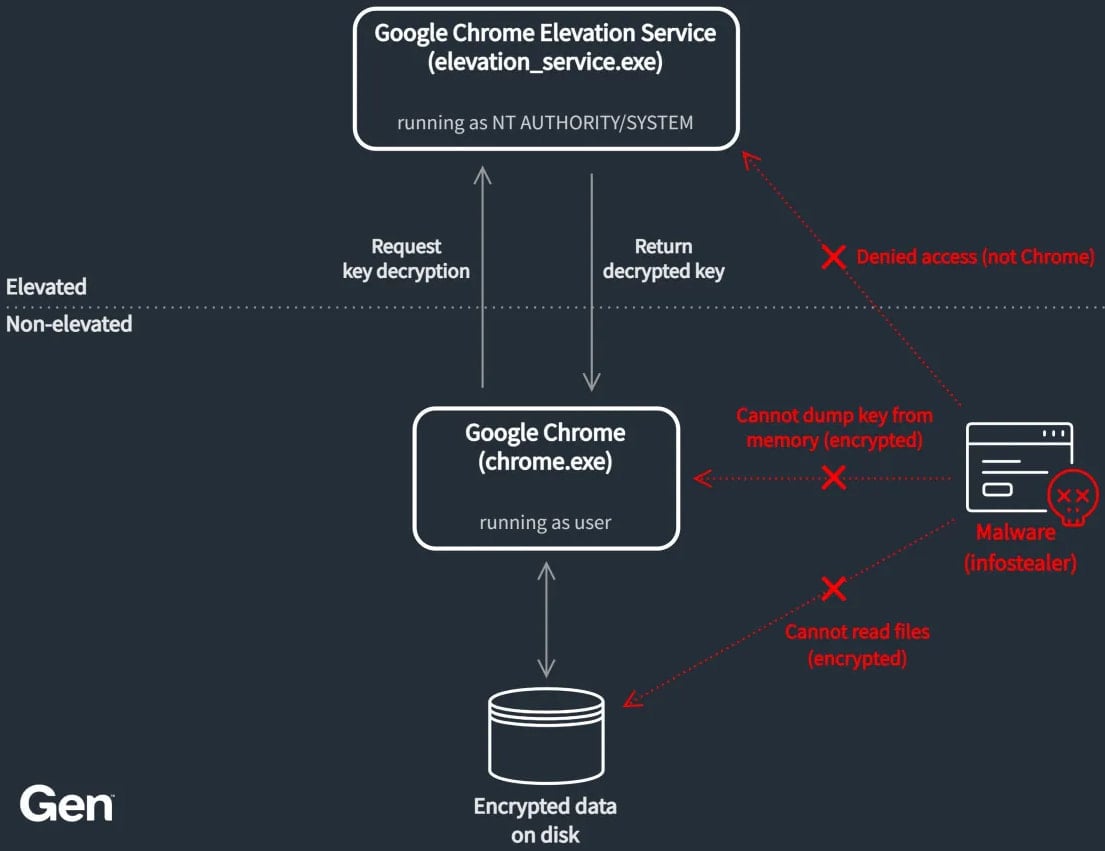
Application-Bound Encryption, introduced by Google in Chrome version 127 (released in June 2024), was designed as a robust defense against credential harvesting malware. Its fundamental principle is to ensure that the browser’s master key remains encrypted on the local disk, rendering it inaccessible to standard user-level processes. Decryption, under normal operating conditions, is strictly gated by the Google Chrome Elevation Service, which operates with elevated SYSTEM privileges and performs rigorous validation on any requesting process before releasing the key. This architectural separation was intended to create an insurmountable barrier for traditional information stealers that rely on low-privilege access.
However, initial attempts to bypass ABE quickly materialized. Multiple families of infostealers, alongside publicly available open-source proof-of-concept tools, demonstrated methods to circumvent the initial security posture. Google responded by iterating on ABE, deploying patches and enhancements to counter these early vectors. Yet, the cat-and-mouse game continues, with new malware variants consistently surfacing, employing ever more nuanced evasion techniques. VoidStealer, according to analysis from Gen Digital, the security firm overseeing major consumer brands like Norton and Avast, represents the most novel and alarming progression in this trend.
Vojtěch Krejsa, a threat researcher at Gen Digital, explicitly stated that VoidStealer is the first observed threat actor in the wild to deploy this specific debugger-based attack against ABE. Unlike prior methods that might have involved complex privilege escalation chains or direct code injection into protected processes, VoidStealer utilizes a technique rooted in low-level debugging primitives, specifically hardware breakpoints, to intercept the master key while it is temporarily decrypted in volatile memory.
VoidStealer operates as a Malware-as-a-Service (MaaS) platform, actively advertised on various dark web forums since at least mid-December 2025. The introduction of this advanced ABE bypass was integrated into the malware’s Version 2.0 update, signaling a strategic investment by the MaaS operators into defeating state-of-the-art browser defenses. The advertising materials circulating within illicit communities highlight the capability to bypass ABE as a key selling point for the updated payload.

The Mechanics of Memory Interception
The ingenuity of VoidStealer’s attack lies in its precise timing and reliance on hardware capabilities. The goal is to capture the v20_master_key during the infinitesimal window when the browser process has decrypted it for immediate use—a state where it resides in plaintext within the process’s address space.
The execution sequence is meticulously orchestrated:
-
Process Suspension and Debugging Attachment: VoidStealer initiates a new instance of the target browser (Chrome or Microsoft Edge, evidenced by targeting
chrome.dllormsedge.dll) in a suspended state. Crucially, it immediately attaches itself to this new process as a debugger. This attachment is key, as it grants the malware significant control over the target process’s execution flow without necessarily requiring the elevated privileges needed for traditional injection. -
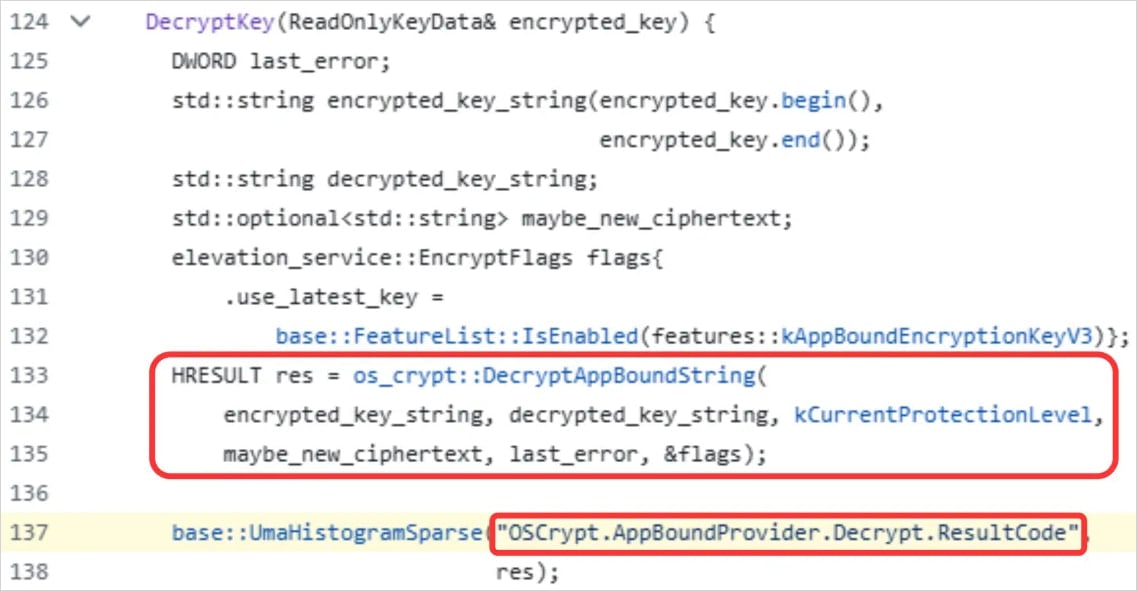
Breakpoint Setup via Instruction Scanning: Once attached, the malware waits for the target DLLs to be mapped into the browser’s memory space. Upon loading, VoidStealer scans the loaded module code for a specific, recognizable string pattern related to ABE decryption routines. Associated with this string is a specific
LEA(Load Effective Address) instruction. The address of this instruction serves as the precise target for the hardware breakpoint. -
Hardware Breakpoint Deployment: Unlike software breakpoints, which modify the instruction stream itself (and can be detected by the target process), hardware breakpoints utilize the CPU’s debug registers (DR0-DR7). These registers allow the system to halt execution when a specific memory address is accessed or executed, regardless of modifications to the code segment. VoidStealer strategically sets this hardware breakpoint across all existing and newly spawned threads within the browser process.
-
Trigger and Key Extraction: The malware waits for the browser process to resume execution. The ideal scenario, as noted by Gen Digital analysts, is browser startup. During initialization, the browser accesses ABE-protected data, forcing the process to temporarily decrypt the master key for immediate use in decrypting cookies and session data. When the execution hits the instruction monitored by the hardware breakpoint, the CPU triggers an exception, and control is handed back to the debugger—VoidStealer.
-
Register Analysis and Exfiltration: Upon regaining control via the breakpoint, VoidStealer inspects the CPU registers. The objective is to locate the register containing a pointer that references the plaintext
v20_master_keyin memory. Once identified, the malware employs theReadProcessMemoryAPI call to securely read the key directly from the process heap before the browser can clear it or before the ABE decryption routine completes its cleanup cycle.
This technique sidesteps the need to trick the Elevation Service, as it bypasses the storage vulnerability entirely by targeting the runtime state of the key.
Contextualizing the Bypass: The Evolution of Browser Security
The introduction of ABE was a significant milestone following years of successful credential theft via browser data scraping. Attackers had long relied on compromising the operating system (often via initial malware payloads) and then exploiting the fact that Chrome stored its master key, albeit encrypted, in accessible locations (like the Windows Data Protection API blob). Even when the key was protected by DPAPI, malware that achieved user-level access could often use tools like Mimikatz or specialized DPAPI crackers to retrieve the necessary key material.
ABE aimed to decouple the master key from the user context, binding it instead to the specific application instance running under the system’s control—a layered defense. The initial bypasses focused on exploiting logical flaws in how ABE interacted with certain APIs or specific operating system behaviors that allowed malware to coerce the decryption service into revealing the key under false pretenses.
VoidStealer’s adoption of the debugger/hardware breakpoint approach signifies a more fundamental shift. It demonstrates that threat actors are willing to incorporate highly technical, low-level exploitation techniques previously seen primarily in red-teaming tools or academic research, moving them into mainstream criminal toolkits.
The researchers suggest that VoidStealer likely did not invent this specific implementation but rather adapted it from the publicly available open-source project known as "ElevationKatz." ElevationKatz is part of the broader ChromeKatz toolset, which has historically served to demonstrate weaknesses in Chrome’s cookie-dumping security model. While VoidStealer’s code exhibits modifications, the core logic leveraging hardware breakpoints for runtime memory capture appears directly derived from these publicly accessible exploits, illustrating the rapid weaponization cycle in the cybercriminal ecosystem.
.webp)
Industry Implications and Expert Analysis
The successful deployment of this hardware breakpoint technique has profound implications across the security industry, particularly for endpoint protection vendors and browser developers.
1. Erosion of Runtime Protections: The primary concern is that if an attacker can reliably intercept a key during its brief existence in plaintext memory, many security models relying on protecting persistent storage become less effective. Hardware breakpoints are notoriously difficult to detect from within the target process itself, as they are handled by the CPU, not the operating system kernel in a way that standard anti-rootkit or anti-hooking technologies easily monitor.
2. The Threat of MaaS Commoditization: The fact that a commercialized MaaS platform like VoidStealer integrated this technique so quickly indicates that the barrier to entry for advanced exploitation is lowering. Sophisticated techniques are being commoditized, meaning smaller, less skilled criminal groups can purchase access to high-efficacy tools capable of defeating modern browser security features.
3. The Need for Hardware-Assisted Isolation: This incident elevates the importance of technologies that move sensitive operations away from the standard user-space memory model. Solutions involving Trusted Execution Environments (TEEs) or advanced process isolation that strictly limit memory introspection capabilities—even for debuggers—will become increasingly critical. If the master key were only accessible within a hardware enclave, this type of memory read attack would fail.
4. Challenges for Detection: Traditional behavioral analysis systems often focus on anomalous process creation or API calls associated with privilege escalation. VoidStealer’s method is relatively clean: it involves legitimate debugging operations on a process it spawned itself. Detecting this requires extremely deep introspection capabilities—monitoring hardware register states or detecting the specific pattern of instruction scanning used to set the breakpoint—which is computationally expensive and often introduces performance overhead, creating a trade-off for security vendors.
Future Trajectories and Mitigation Challenges
Google’s response to previous ABE bypasses focused on hardening the decryption workflow and potentially altering the timing or memory allocation patterns associated with the master key. However, the debugger trick demands a more fundamental architectural rethink.
Future defensive strategies must address the vulnerability window itself:
- Dynamic Key Re-derivation: Instead of maintaining a single, long-lived
v20_master_keyin memory for the duration of a session, Chrome could explore re-deriving or refreshing the key more frequently, or perhaps only instantiating it for the precise cryptographic operation needed, minimizing the plaintext exposure window to microseconds. - Debugger Detection Refinements: While hardware breakpoints are difficult to detect, software solutions might focus on detecting the setup phase—the suspicious scanning of DLL headers for specific instruction sequences or the rapid, controlled setup of debug registers in a pattern inconsistent with standard development or debugging practices.
- Kernel-Level Integrity Checks: Enhancing Chrome’s own integrity checks, potentially involving kernel-level hooks or callbacks (if feasible without introducing performance regressions), to verify that the process environment hasn’t been externally manipulated by a debugger before sensitive decryption operations commence.
The VoidStealer breakthrough underscores a perpetual reality in cybersecurity: security features are often defined by their weakest implementation detail. While ABE represents a strong cryptographic concept, its successful execution within the constraints of a standard operating system environment leaves exploitable seams. As attackers adopt techniques rooted in low-level CPU features like hardware breakpoints, the defense must move toward solutions that isolate critical data not just logically, but physically, within the computing architecture. This incident serves as a clear warning that relying solely on software-enforced boundaries for high-value secrets is an insufficient long-term strategy.

