A recent federal conviction has cast a harsh spotlight on the often-underestimated peril of insider threats within the technology sector. A former data analyst contractor, operating out of North Carolina, has been found guilty for orchestrating a sophisticated extortion scheme targeting his former employer, a significant player in the Software-as-a-Service (SaaS) landscape. This incident underscores the inherent risks associated with granting elevated data access, even to vetted temporary personnel, particularly in environments handling sensitive corporate and personal information.
The targeted entity, identified through unsealed court records as Brightly Software—a firm specializing in intelligent asset management and maintenance software, and acquired by Siemens in August 2022—provides critical operational infrastructure for over 12,000 clients globally. With a workforce exceeding 700 employees and a legacy spanning two decades, the company’s operations are deeply integrated into essential infrastructure management across the US, Canada, the UK, and Australia. The breach of trust by the contractor, identified as 27-year-old Cameron Curry, alias "Loot," highlights a critical failure in access revocation protocols coinciding with contract conclusion.
The Mechanics of the Betrayal
The indictment reveals the calculated nature of Curry’s actions. During his six-month tenure as a data analyst contractor, Curry amassed extensive access to proprietary corporate data, crucially including sensitive payroll information and Personally Identifiable Information (PII) belonging to Brightly employees. The motivation for the scheme appears directly tied to the decision not to extend his contract.
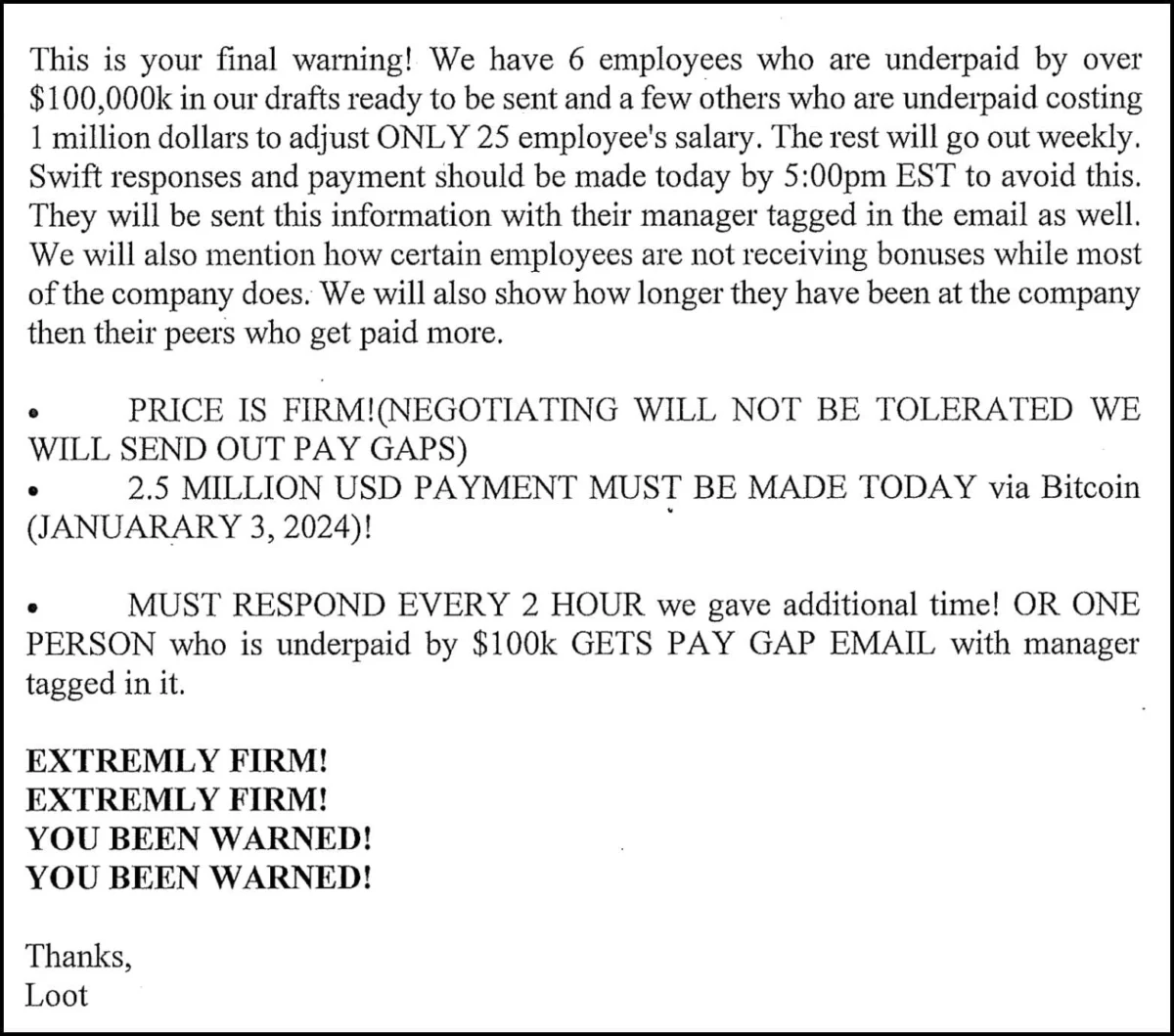
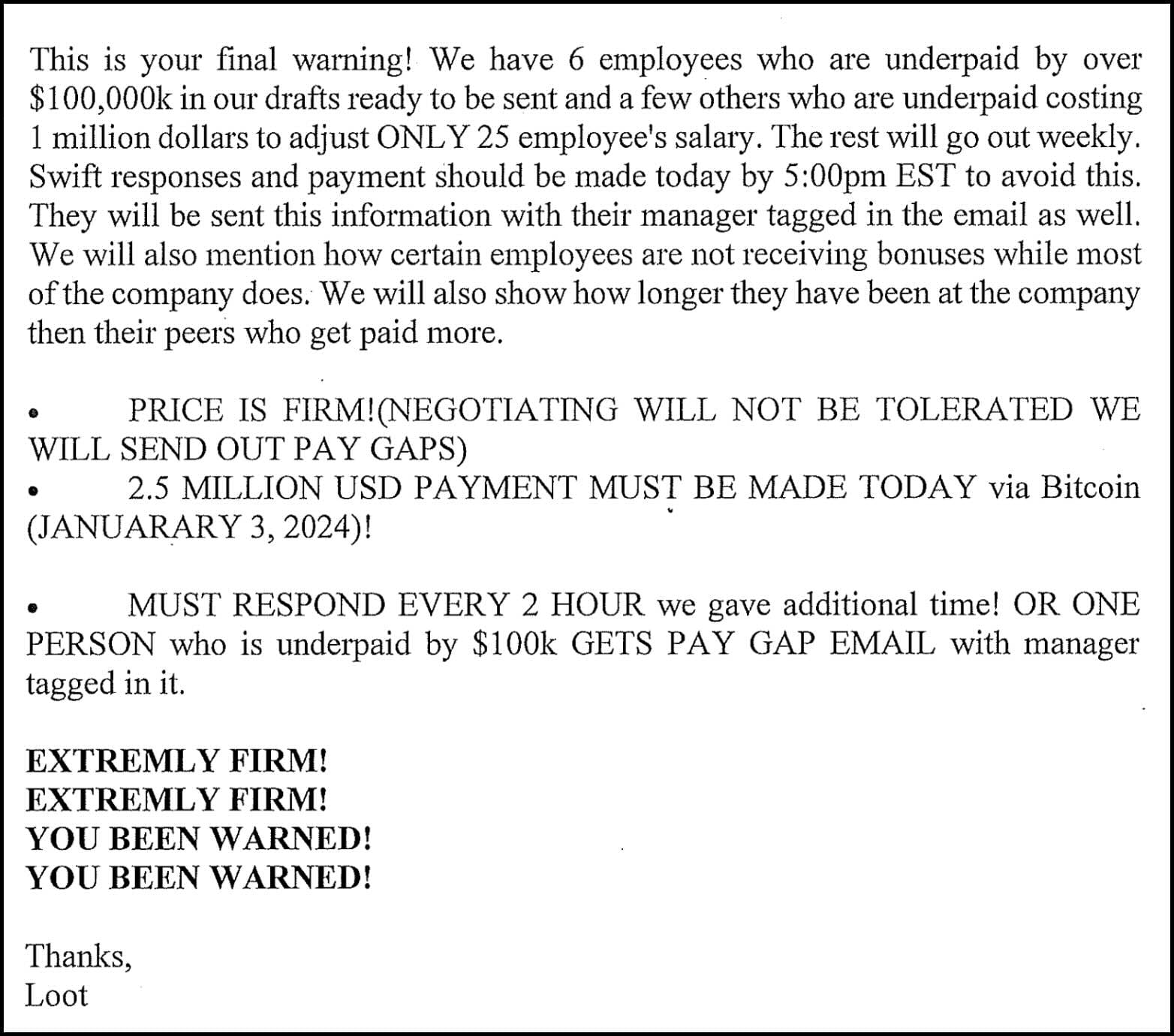
The extortion attempt commenced swiftly—mere hours after his contractual engagement officially concluded on December 10th. Utilizing a dedicated Microsoft Outlook address, [email protected], Curry initiated a barrage, sending more than sixty separate communications to various Brightly personnel. The demands were stark: a ransom of $2.5 million, payable in cryptocurrency, in exchange for the suppression of the stolen data.
The evidence presented against Curry was compelling. The extortion emails were not mere threats; they were accompanied by concrete proof of his possession of sensitive material. Screenshots of internal spreadsheets detailing employee PII—including names, dates of birth, home addresses, and detailed compensation structures—were affixed to the messages. This level of detail suggests a deep, privileged dive into the company’s Human Resources and financial databases.
Beyond the direct threat to employee privacy, Curry leveraged regulatory pressure as a secondary weapon. He explicitly threatened to report Brightly to the U.S. Securities and Exchange Commission (SEC) for failing to disclose the data exfiltration as required by federal law. One particularly aggressive message encapsulated his dual-pronged attack: "We will commence the process of disseminating salary information starting January 1, 2024 in phases to all employees and will report you to the SEC after for not reporting the breach." Furthermore, he attempted to inflate the urgency and the perceived internal damage, claiming existing "discrepancies in your books are currently over 16 million USD," suggesting the data theft might expose wider financial malfeasance, thereby creating an environment ripe for "retention issues, a hostile work environment, [and] resentment." He also imposed an escalating fee structure: a $100,000 daily premium should the initial $2.5 million not be remitted promptly.
Corporate Response and Law Enforcement Intervention
In the face of immediate, verifiable threats to employee welfare and potential regulatory fallout, Brightly made a calculated decision to mitigate the immediate risk. The company transferred $7,540 worth of Bitcoin to a cryptocurrency wallet controlled by Curry. This payment, however, proved insufficient to halt the threat, likely serving only as a down payment or an initial attempt to de-escalate the situation before fully engaging law enforcement.

Following the transfer, Brightly formally reported the incident to federal authorities. This swift escalation triggered an intensive investigation by the Federal Bureau of Investigation (FBI). On January 24th, agents executed a search warrant on Curry’s North Carolina residence, successfully seizing numerous electronic devices that yielded critical forensic evidence supporting the indictment.
Curry was subsequently released on bond in January 2024. He now faces significant legal jeopardy, specifically six counts of transmitting or willfully causing interstate communications with the intent to extort a victim company, each carrying a potential sentence of up to twelve years in federal prison.
In a brief statement provided following the conviction announcement, Brightly confirmed awareness of the Department of Justice’s success in securing the conviction. The company emphasized its full cooperation with the FBI and DOJ, deferring further comment due to the ongoing legal proceedings.
Industry Context: The Evolving Insider Threat Landscape
This incident serves as a stark reminder that the most damaging breaches often originate not from sophisticated external zero-day exploits, but from trusted insiders leveraging legitimate access. For SaaS providers like Brightly, whose business model hinges on robust data security and client trust, the betrayal by an internal contractor is uniquely damaging.
Industry analysis consistently shows that insider threats account for a significant percentage of data breaches, often involving data theft for financial gain or malicious disruption. The sophistication here—combining PII theft with threats of regulatory exposure—moves beyond simple disgruntled employee behavior and into organized criminal extortion tactics.
The decision to use cryptocurrency for the initial payoff is standard procedure for extortionists, offering a layer of obfuscation, though the use of a relatively small initial sum ($7,540) compared to the $2.5 million demand suggests a test of the company’s compliance or perhaps an indicator of the attacker’s immediate liquidity needs.
Analysis of Vulnerabilities and Systemic Failures
The root cause analysis of this breach points to several critical security and procedural lapses common across the industry:
-
Inadequate Off-Boarding and Access Revocation: The most glaring failure is the ability of the contractor to execute the extortion scheme immediately after his access was technically terminated. Effective security posture demands instantaneous revocation of all credentials, VPN access, and application logins the moment a contract ends, or even earlier if contract non-renewal is confirmed. The fact that Curry had time to exfiltrate and then threaten to release data after his access window closed suggests a delay in either the termination process or a persistent, unauthorized access mechanism.
-
Principle of Least Privilege (PoLP) Violation: Curry, as a data analyst contractor, should have only accessed data strictly necessary for his defined tasks. Access to comprehensive payroll data, including salaries and full PII sets for the entire staff, often exceeds the baseline requirement for analytical roles. This over-provisioning of access provided the necessary ammunition for a high-value extortion attempt.
-
Data Segmentation and Encryption: The ease with which Curry could compile spreadsheets containing highly sensitive employee PII suggests poor data segmentation. Critical HR data should reside in highly restricted environments, preferably encrypted both at rest and in transit, with access logged and monitored with extreme scrutiny, especially for non-permanent staff.
Broader Industry Implications and Future Security Directives
For the broader technology and SaaS sectors, the Brightly case mandates a review of third-party risk management. Siemens’ acquisition of Brightly places a larger corporate entity under the shadow of this incident, potentially affecting stakeholder confidence in the security maturity of acquired assets.
Cybersecurity experts suggest that organizations must move toward Continuous Insider Threat Monitoring (CITM), rather than relying solely on perimeter defenses or static access audits. This involves behavioral analytics that flag anomalous data access patterns—such as an analyst suddenly downloading large, broad swaths of PII or accessing files outside their usual work hours or project scope—regardless of the user’s employment status.
Furthermore, the threat to report the company to the SEC highlights the growing tactic of weaponizing regulatory compliance against the victim. Companies must have pre-established, legally vetted incident response plans that address regulatory disclosure deadlines concurrently with technical remediation and law enforcement engagement. Delaying disclosure due to fear of regulatory penalty only emboldens attackers who leverage that fear for financial gain.
Distinguishing Incidents: Contextualizing Data Exposure
It is crucial to note that Brightly has faced other security challenges, which complicate public perception. The company previously notified customers in May 2023 regarding a separate, unrelated data breach involving its legacy SchoolDude online platform, which exposed credentials and personal data for nearly three million users. While the current extortion case involves internal data theft executed by a contractor, the prior, large-scale external breach demonstrates a history of challenges in securing diverse data stores, potentially offering the extortionist (Curry) an assurance that the company was already perceived as vulnerable.
The legal proceedings, culminating in Curry’s conviction, represent a successful outcome for federal enforcement agencies tackling digital extortion. However, the underlying vulnerability—the excessive access granted to a temporary analyst—remains the most potent lesson for IT and security leadership globally. The cost of vigilance, in terms of implementing Zero Trust architectures and rigorous access governance, pales in comparison to the potential financial and reputational fallout demonstrated in this $2.5 million extortion attempt. The industry must treat contractor vetting and off-boarding with the same rigor applied to C-suite executive access, recognizing that privilege, regardless of employment duration, is a potent tool for exploitation.