The Cybersecurity and Infrastructure Security Agency (CISA) has issued a directive compelling U.S. federal agencies to immediately address critical vulnerabilities within the Apple iOS ecosystem that have been actively weaponized by sophisticated threat actors utilizing the DarkSword exploit framework. This urgent action underscores the severe, real-world impact of mobile platform vulnerabilities when they fall into the hands of state-sponsored or financially motivated cyber syndicates capable of weaponizing complex exploit chains.
The foundation of this heightened alert lies in a recently disclosed technical breakdown by the Google Threat Intelligence Group (GTIG) in collaboration with iVerify researchers. Their investigation pinpointed DarkSword as a potent delivery mechanism that orchestrates a multi-stage compromise by chaining together a sequence of six distinct vulnerabilities. These flaws, tracked under identifiers CVE-2025-31277, CVE-2025-43529, CVE-2026-20700, CVE-2025-14174, CVE-2025-43510, and CVE-2025-43520, represent a highly dangerous combination. When successfully chained, these vulnerabilities grant an adversary the capability to shatter the isolation mechanisms (sandboxes) inherent in iOS, elevate their operational privileges to system-level access, and ultimately achieve arbitrary Remote Code Execution (RCE) on targeted, unpatched devices.
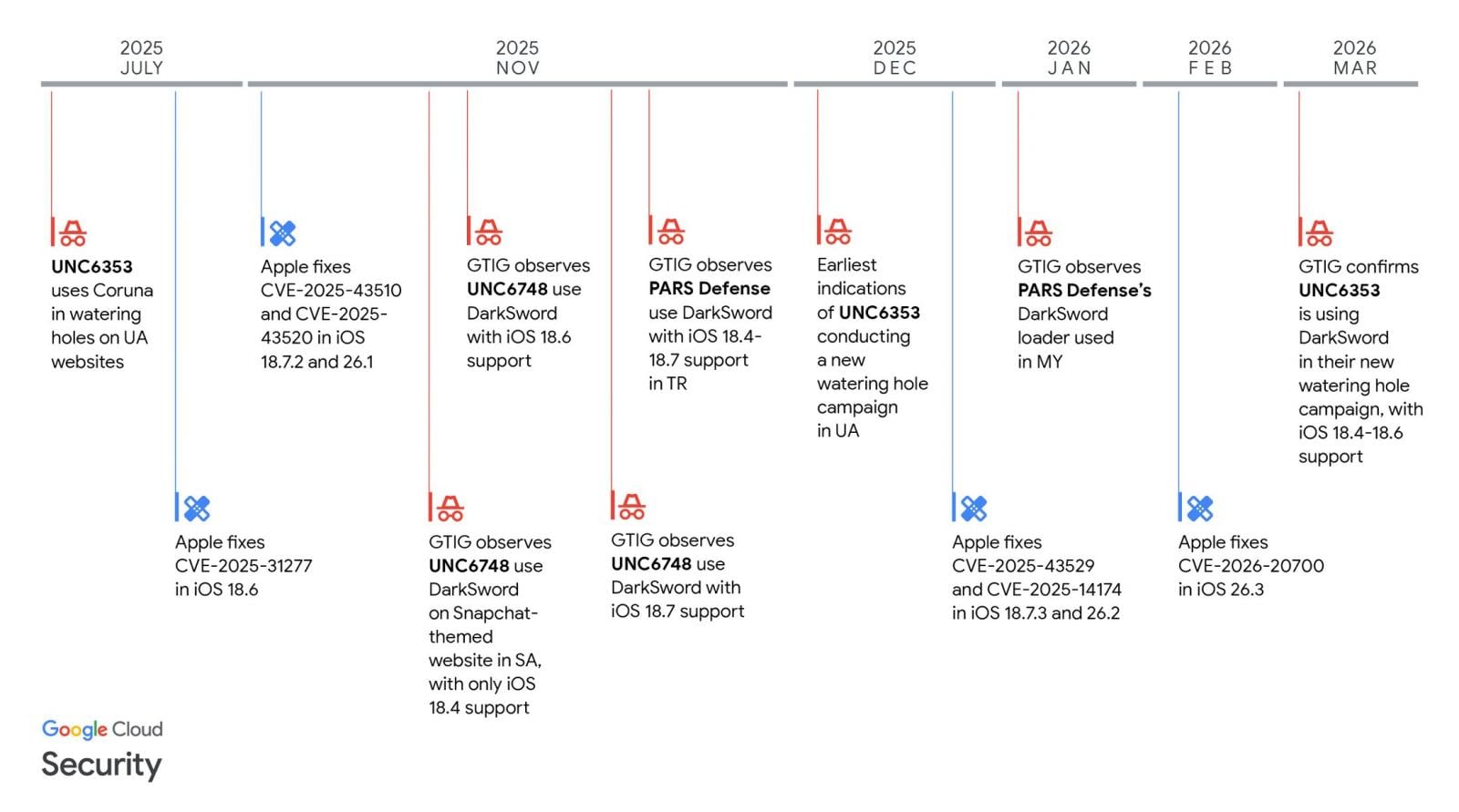
Apple has proactively addressed these security gaps through subsequent software updates. However, the critical window of exposure remains for systems running specific, now-outdated versions of the operating system, specifically iOS 18.4 through iOS 18.7. For federal entities managing vast inventories of mobile devices, this narrow version range dictates the scope of the immediate remediation effort.
Geopolitical Echoes and Threat Actor Attribution
The concern surrounding DarkSword transcends mere technical exploitation; it is deeply interwoven with geopolitical tensions and targeted espionage objectives. Security analysis has firmly linked the deployment of this exploit kit to several well-resourced threat groups. One notable association is with UNC6748, an entity reportedly tied to the client roster of PARS Defense, a Turkish commercial surveillance vendor. More alarming, however, is the connection to UNC6353, a threat group widely suspected of conducting operations aligned with Russian intelligence interests.
The payloads observed following a successful DarkSword deployment are particularly insidious. GTIG documented the deployment of three distinct malware families, all tailored for information exfiltration. These include GhostBlade, described as an aggressive JavaScript-based infostealer; GhostKnife, a more robust backdoor designed for the large-scale exfiltration of sensitive data; and GhostSaber, another JavaScript implant capable of executing arbitrary code while simultaneously harvesting victim data.
UNC6353, in particular, has demonstrated a sophisticated, multi-pronged approach, deploying both the DarkSword kit alongside the related Coruna iOS exploit kit. Their operational methodology, as observed by researchers, involved "watering-hole" attacks. This technique relies on compromising legitimate, high-traffic websites—in this specific case, Ukrainian sites focused on e-commerce, industrial equipment, and local services—to infect unsuspecting users who visit these domains using their iPhones.

The architecture of the DarkSword framework itself suggests a design optimized for stealth and rapid exfiltration. Observations indicate that once the primary data theft objective is achieved, the malware systematically erases its temporary files and terminates its processes. This ephemeral nature points toward an operational profile geared toward short-term, high-value intelligence gathering, specifically designed to maximize the chances of evading post-incident forensic detection. Mobile security firm Lookout, which initially identified DarkSword during an investigation into Coruna attack infrastructure, has posited that the toolset is being utilized in cyber-espionage campaigns consistent with the requirements of Russian intelligence services, often intertwined with actors pursuing distinct financial incentives.
CISA’s Binding Operational Directive
In response to the confirmed active exploitation of these flaws, CISA formalized the urgency by adding three of the six DarkSword vulnerabilities—CVE-2025-31277, CVE-2025-43510, and CVE-2025-43520—to its Catalog of Known Exploited Vulnerabilities (KEV). The inclusion on the KEV triggers mandatory compliance under Binding Operational Directive (BOD) 22-01 for all Federal Civilian Executive Branch (FCEB) agencies. This directive mandates that agencies must implement necessary mitigations within a strict two-week timeframe. With the directive issued on Friday, the deadline for remediation was set for April 3rd.
CISA’s official guidance is unequivocal: "Apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are unavailable." The agency further emphasized the systemic risk these vulnerabilities pose, stating, "These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise."
While BOD 22-01 legally binds only federal agencies, CISA’s public advisory extends a crucial recommendation to the broader cybersecurity community. Private sector organizations, critical infrastructure operators, and any entity managing significant fleets of mobile endpoints are strongly encouraged to treat this advisory with the same urgency as federal mandates, given the demonstrated effectiveness of the DarkSword chain across different threat actor profiles.
Industry Implications: The Commoditization of Advanced Exploitation
The existence and proliferation of exploit kits like DarkSword represent a significant inflection point in the cyber threat landscape. Historically, the ability to chain together multiple zero-day or near-zero-day vulnerabilities to achieve RCE on a major mobile platform like iOS was the exclusive domain of nation-states or highly capitalized cybercriminal organizations possessing deep reverse-engineering capabilities.
DarkSword’s entry into the threat ecosystem, particularly its association with actors seemingly operating under geopolitical mandates but also displaying financial motives, suggests a worrying trend: the commoditization or sharing of sophisticated exploitation frameworks. This democratization lowers the barrier to entry for complex mobile compromise.
For the mobile security industry, this highlights several pressing concerns. First, the rapid succession of high-impact vulnerabilities discovered in established, mature operating systems like iOS suggests that even rigorous security development lifecycles (SDLCs) are struggling to keep pace with adversarial innovation, particularly in areas like memory safety and complex inter-process communication handling, which are often the weak links exploited in such chains.
Second, the nature of the malware payloads—GhostBlade, GhostKnife, GhostSaber—points toward a shift from broad, noisy ransomware campaigns to highly targeted, low-and-slow intelligence operations, particularly against entities operating in conflict zones or those possessing politically sensitive information. The focus on short-term surveillance (ephemeral malware) rather than persistent access indicates that the attackers value the immediate intelligence gathered over maintaining a long-term foothold, a hallmark of sophisticated espionage.
Expert Analysis: The Persistence of Mobile Attack Surface
From an expert perspective, the CISA action underscores the critical need to re-evaluate mobile device management (MDM) and endpoint security policies within government and high-value private sector organizations. The fact that the vulnerabilities are confined to a specific range (iOS 18.4 to 18.7) provides a clear, actionable target set, but the underlying mechanism that allowed six flaws to align in a functional exploit chain demands deeper scrutiny of Apple’s security engineering.
Security architects must move beyond simple patch management and implement defense-in-depth strategies tailored for mobile platforms. This includes rigorous enforcement of application allow-listing, enhanced network monitoring capable of detecting anomalous data egress patterns from mobile devices, and zero-trust principles applied even to managed endpoints. If a device is compromised via RCE, standard perimeter defenses are rendered useless.
Furthermore, the involvement of commercial surveillance vendors like PARS Defense in the supply chain raises significant vendor risk management flags. Organizations must now scrutinize the provenance of their security tools and services, ensuring that no third-party vendor, even one ostensibly providing security solutions, is inadvertently or intentionally introducing backdoors or sharing exploited capabilities with adversarial state actors. The nexus between the commercial surveillance industry and known espionage groups represents a significant, often overlooked, vector for national security threats.
Future Impact and Defensive Trends
The DarkSword incident serves as a potent harbinger for future mobile security challenges. We can anticipate several trends emerging from this event:
- Increased Focus on Browser-Based Exploitation: Watering-hole attacks targeting web browsers remain a highly effective delivery method because they require minimal user interaction beyond visiting a compromised site. Future exploits will likely focus on refining JavaScript engine vulnerabilities or WebKit zero-days to facilitate the initial execution phase, making browser sandboxing effectiveness paramount.
- The Persistence of Multi-Stage Chains: Attackers are clearly investing heavily in developing chains that rely on chaining multiple, lower-severity vulnerabilities to achieve a high-severity outcome (RCE). This makes vulnerability detection and patching exponentially more complex, as patching one flaw in the chain may not stop an attack relying on the remaining five.
- Mandatory Mobile Threat Defense (MTD): For the federal space, the CISA directive will undoubtedly spur faster adoption and stricter enforcement of Mobile Threat Defense (MTD) solutions that offer runtime integrity checks and behavioral analysis, rather than relying solely on signature-based detection or application-layer patching. MTD solutions might be better positioned to detect the subtle behavioral anomalies indicative of GhostBlade or GhostKnife activity post-exploitation.
- Supply Chain Scrutiny on Commercial Spyware: Expect heightened regulatory and intelligence focus on companies that develop or sell surveillance technology. The line between legitimate surveillance tools and cyberweapons is becoming increasingly blurred, necessitating clearer international standards and export controls on these potent technologies.
In conclusion, the CISA mandate regarding DarkSword is not just a routine patching exercise; it is a direct response to a highly advanced, multi-faceted threat campaign targeting the secure foundation of government communications. For all organizations relying on the confidentiality and integrity of data accessed via mobile devices, the time for reactive patching is over; proactive, layered defense against RCE-level mobile exploitation must now be the standard operating procedure.

