The recent discovery of a critical security vulnerability within the Marimo reactive Python notebook environment has underscored the precarious nature of rapid-deployment development tools. Classified as CVE-2026-39987, this remote code execution (RCE) flaw allows unauthorized actors to bypass authentication protocols entirely, gaining unfettered access to the host system. The incident has sent shockwaves through the data science and machine learning communities, as the speed between public disclosure and active, malicious exploitation was measured in mere hours.
The Technical Anatomy of the Vulnerability
Marimo has gained significant traction as a modern alternative to traditional Jupyter-style notebooks, favored for its reactive execution model and ease of deployment. However, the architectural design choice that prioritized accessibility for developers has become its greatest liability. The vulnerability lies within the /terminal/ws WebSocket endpoint. In affected versions (0.20.4 and earlier), this specific endpoint failed to implement any form of authentication check.
By design, this endpoint was intended to expose an interactive terminal interface to users within the browser-based notebook environment. Because the implementation lacked a verification handshake, any client capable of establishing a connection to the network-exposed Marimo instance could interact with the WebSocket. Consequently, an attacker could open a command-line interface that executes with the same privilege level as the Marimo process itself. If the process is running as a root or sudo-enabled user—a common configuration in ad-hoc development containers—the attacker effectively gains full control over the host machine.

A Masterclass in Rapid Exploitation
The lifecycle of this threat highlights the escalating sophistication of automated and semi-automated adversary reconnaissance. Security telemetry indicates that malicious actors began scanning for vulnerable instances almost immediately following the project’s security advisory publication. Within 12 hours of the disclosure, over 125 unique IP addresses were observed conducting active reconnaissance against the specific URI associated with the terminal endpoint.
The primary exploitation chain observed by security analysts followed a highly efficient, "surgical" methodology. Rather than utilizing bulky, noisy automated scripts that might trigger network-based intrusion detection systems (IDS), the operators favored a manual, methodical approach.
- Validation: The attacker initiated a connection to the unauthenticated terminal endpoint, executing a minimal command string to confirm that the shell was responsive and that command injection was successful.
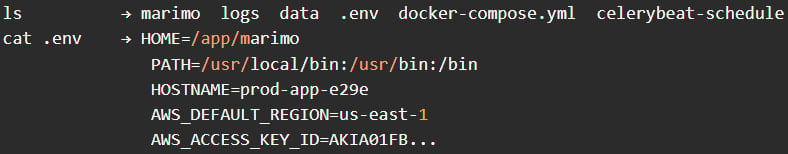
- Environment Reconnaissance: Once the foothold was established, the operator issued standard Unix commands—
whoami,pwd, andls—to map the file system. This allowed them to understand the context of the environment, specifically identifying whether the notebook was running within a containerized environment or on a bare-metal server. - Credential Harvesting: The primary objective was the rapid extraction of sensitive configuration files. The attackers prioritized the
.envfiles and hidden directories containing SSH keys. These files are gold mines for lateral movement, as they often contain hardcoded cloud provider credentials, database connection strings, and API keys for third-party services. - Data Exfiltration: The entire process, from initial connection to the extraction of sensitive secrets, was completed in under three minutes. The attackers intentionally avoided high-visibility actions such as installing persistent backdoors or initiating cryptocurrency miners, choosing instead to "smash and grab" high-value credentials before disconnecting.
Industry Implications and the "Notebook" Security Paradigm
The Marimo incident serves as a poignant case study for the security challenges inherent in the modern data science stack. Researchers, ML engineers, and data analysts frequently deploy notebooks on cloud instances or shared servers to leverage high-performance compute (HPC) resources. In their quest for productivity, these users often bind applications to 0.0.0.0 (all network interfaces) to facilitate easy access from various devices.

When combined with a tool that provides a direct shell interface, this configuration creates a "path of least resistance" for attackers. The industry has long grappled with the tension between "frictionless developer experience" and "secure-by-default architecture." Projects that prioritize the former often assume that notebooks will only ever be accessed from trusted, internal networks. However, the ubiquity of cloud-based environments means that these services are frequently reachable from the public internet, even if they were never intended to be exposed.
Furthermore, this event highlights the danger of "disclosure lag." While the developers acted responsibly by releasing version 0.23.0, the window between the publication of the advisory and the availability of the patch was sufficient for opportunistic attackers to weaponize the provided information. This places an immense burden on DevOps and SecOps teams, who must now treat every open-source software update not just as a feature improvement, but as a potential high-priority emergency patch.
Future Trends in Vulnerability Response
The rapid exploitation of CVE-2026-39987 signals a shift in the threat landscape. We are moving toward an era where the time-to-exploit (TTE) for a newly disclosed vulnerability is approaching zero. Attackers are increasingly leveraging AI-driven reconnaissance tools that can ingest security advisories, parse them for the vulnerable code path, and automatically generate exploit scripts.
To defend against this, organizations must move beyond reactive patching. The following strategies are becoming industry standard for those managing high-risk development environments:
- Zero-Trust Networking: Tools like Marimo should never be exposed directly to the internet. Access should be restricted to authenticated users via a VPN, a zero-trust network access (ZTNA) solution, or an identity-aware proxy that performs authentication before the request ever reaches the application.
- Immutable Infrastructure: For data science workloads, moving toward ephemeral, immutable containers that are destroyed and recreated on a regular schedule can limit the utility of stolen credentials, as the environment’s state is frequently wiped.
- Proactive Egress Filtering: While ingress filtering is standard, many developers neglect egress filtering. If a containerized notebook environment has no business reason to connect to external servers other than to reach a specific registry, blocking all other outbound traffic can effectively neutralize many credential-stealing exfiltration attempts.
- Secrets Management: Relying on
.envfiles stored in plain text on the file system is a critical security anti-pattern. Adopting centralized, encrypted secrets management services—such as HashiCorp Vault or cloud-native key management systems—ensures that even if an attacker gains shell access, they do not have immediate access to production credentials.
Conclusion: A Call for Defensive Vigilance
The Marimo security event is not an isolated incident; it is a symptom of a broader ecosystem where speed is often valued above hardened security postures. While the Marimo developers provided a swift fix, the incident serves as a warning for the broader developer community. Security is not a state that is achieved once; it is a continuous process of auditing, monitoring, and adapting.
Users who have not yet updated to version 0.23.0 are strongly advised to do so immediately. However, patching is only the first step. Given the nature of the breach—specifically the targeting of environment variables and SSH keys—it is imperative that any organization that may have had a vulnerable instance exposed to a shared or public network perform a full rotation of all credentials that were present within those environments. Assuming the environment is "clean" after an update is a dangerous fallacy. In the current threat climate, if a window of opportunity was open, the safest assumption is that it was tested. Moving forward, the integration of rigorous security scanning in the CI/CD pipeline, coupled with an architectural philosophy that treats every endpoint as a potential attack vector, will be essential for those building the next generation of data-driven applications.

