The cybersecurity landscape has been jolted by the discovery of a high-severity authentication bypass vulnerability within the Nginx UI management platform, a tool widely utilized by systems administrators to streamline the configuration and maintenance of Nginx web servers. Tracked under the identifier CVE-2026-33032, this flaw has moved rapidly from a theoretical concern to a weaponized reality, with threat actors actively leveraging the vulnerability to achieve full, unauthenticated control over exposed server instances. The simplicity of the exploit, combined with the widespread deployment of Nginx UI, has created a significant security bottleneck for organizations relying on this interface for web infrastructure management.
The Anatomy of the Flaw
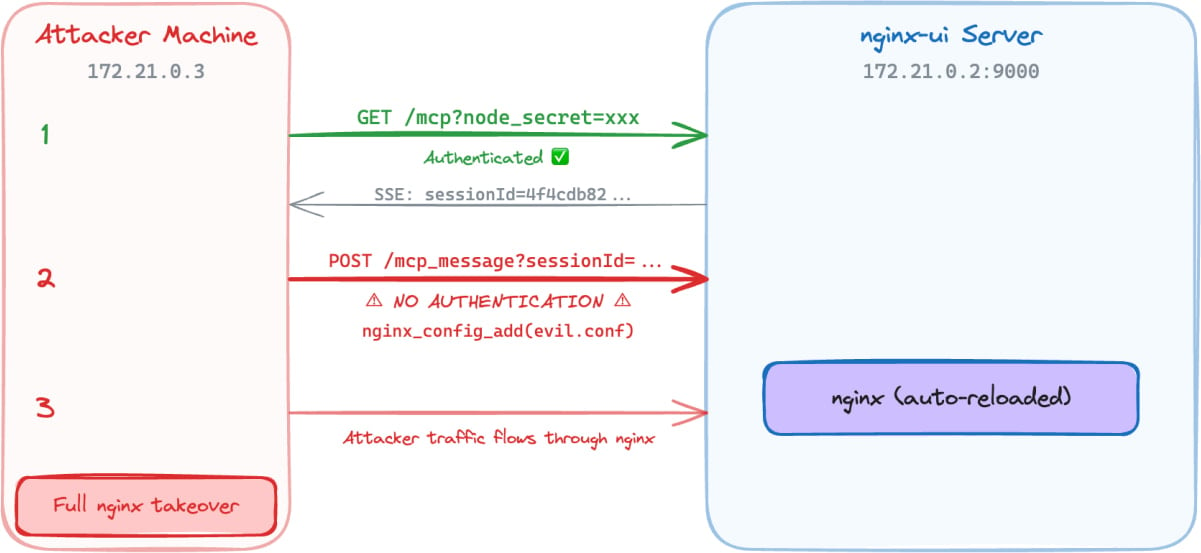
At the heart of the issue lies an oversight in how the Nginx UI software handles the Model Context Protocol (MCP) integration. The MCP, designed to facilitate interaction between AI agents and local development environments or server utilities, requires strict access controls to ensure that only authorized users can trigger sensitive operations. However, researchers identified that the /mcp_message endpoint—a critical gateway for these interactions—was left entirely unprotected.
Because the interface lacks a prerequisite authentication check for this specific endpoint, any remote actor with network visibility can establish an Server-Sent Events (SSE) connection to a target server. Once this connection is initiated, the attacker can open an MCP session and receive a valid sessionID. Armed with this identifier, the malicious actor gains the ability to issue arbitrary commands to the Nginx server. These commands include, but are not limited to, the direct modification or deletion of sensitive Nginx configuration files and the forced reloading of the Nginx service. By manipulating these files, an attacker can effectively redirect traffic, inject malicious headers, or create backdoors, ultimately resulting in a total compromise of the host machine.

Industry Implications and Scale of Exposure
The implications of this vulnerability are profound, particularly given the ubiquity of Nginx in modern web architecture. Nginx serves as the backbone for a massive portion of the internet’s traffic, acting as a reverse proxy, load balancer, and HTTP cache. The Nginx UI project, boasting over 11,000 stars on GitHub and hundreds of thousands of Docker container pulls, is a favorite for developers seeking a graphical interface to manage complex configurations that might otherwise be prone to syntax errors.
When such a foundational piece of management software suffers from a critical authentication bypass, the attack surface is not limited to enterprise data centers; it extends to personal projects, small-to-medium business web hosting, and even complex CI/CD pipelines. Internet scanning data provided by security researchers indicates that approximately 2,600 instances of the software are currently reachable via the public internet. Geographically, these exposed instances are concentrated in major technology hubs, including the United States, China, Germany, Indonesia, and Hong Kong, suggesting that the risk is truly global in scope.
The Risk of AI-Integrated Management Tools
This incident serves as a stark reminder of the security risks associated with integrating emerging protocols—such as the Model Context Protocol—into existing infrastructure management tools. While the goal of the MCP is to improve developer productivity by allowing AI agents to interact directly with server environments, it effectively expands the "trust boundary." If the implementation of these protocols does not rigorously enforce the Principle of Least Privilege, the convenience of automated configuration management can quickly become a liability.
Industry analysts suggest that the speed at which this vulnerability moved from initial discovery to active exploitation is indicative of a broader trend in the threat landscape: "exploit-as-a-service" and the rapid operationalization of proof-of-concept (PoC) code. As soon as technical details and PoCs are published to platforms like GitHub or discussed in cybersecurity forums, threat actors immediately incorporate them into automated scanners. In this case, the time gap between the official patch release on March 15 and the widespread availability of exploitation details provided a narrow window for defenders to mitigate the risk before automated botnets began their hunt for vulnerable instances.

Defensive Strategies and Remediation
For organizations and individual administrators, the immediate priority is to identify and patch any instance of Nginx UI running a version earlier than 2.3.6. However, simply updating the software is often only one component of a robust security posture. Given the nature of the exploit, administrators should also perform a thorough forensic audit of their Nginx configuration files to ensure that no unauthorized changes were introduced during the period the server was exposed.
Beyond patching, this event underscores the necessity of "defense-in-depth" strategies. Management interfaces, regardless of their utility, should never be exposed to the public internet by default. Best practices dictate that such tools should be placed behind a VPN, restricted to specific IP whitelists, or guarded by robust, multi-factor authentication (MFA) gateways. Relying solely on the authentication mechanisms built into a third-party management tool is increasingly insufficient, as evidenced by the frequency of auth-bypass vulnerabilities reported in the wild.
Future Trends and the Path Forward
Looking ahead, the cybersecurity community expects to see more scrutiny applied to management interfaces that incorporate LLM-driven features and agentic workflows. As companies rush to adopt AI-powered operational tools, the focus on securing the communication channels between these agents and the underlying infrastructure will become a critical differentiator between resilient and vulnerable systems.
Furthermore, the incident highlights the ongoing struggle with the "patch gap." Even when software maintainers act responsibly—releasing a patch within 24 hours of receiving a vulnerability report, as was the case here—the delay in end-user adoption allows attackers to gain a foothold. This disparity between the speed of the vendor’s response and the speed of the user’s implementation remains one of the most persistent challenges in modern cybersecurity.
As we move toward a future where infrastructure management is increasingly automated and driven by AI, the need for proactive, automated security validation becomes paramount. Organizations can no longer rely on manual updates or periodic checks. Instead, they must integrate continuous security monitoring and automated patch management into their workflows. Tools that allow for "Breach and Attack Simulation" (BAS) can help teams verify whether their existing network controls—such as firewalls or intrusion detection systems—would actually stop an attacker from reaching a vulnerable endpoint like the one identified in CVE-2026-33032.
In conclusion, while the Nginx UI vulnerability has been addressed through the release of version 2.3.6, the damage caused by the brief period of exploitation serves as a wake-up call for the developer community. The integration of advanced protocols into management interfaces necessitates a higher standard of security auditing and a commitment to keeping administrative portals behind strictly controlled network perimeters. Security is not a static state achieved by a single update; it is an ongoing process of monitoring, hardening, and rapid response that must keep pace with the evolving capabilities of those seeking to exploit the digital world. The lesson of this event is clear: in an era of rapid technical innovation, the fundamental tenets of network security remain as vital as ever.

