The landscape of online fraud has matured far beyond simple, isolated attacks targeting a single vulnerability. Today’s sophisticated cybercriminal operations function with the precision and coordination of a specialized relay team, where distinct actors and technological stacks are deployed sequentially to shepherd a fraudulent action from initial reconnaissance through to final monetization. This multi-stage architecture represents a fundamental shift in threat dynamics, demanding an equally evolved defensive posture from digital platforms.
Background: The Erosion of Single-Signal Security
For years, enterprise security relied heavily on discrete verification steps: checking the IP address reputation at connection, validating an email address format, or applying basic velocity checks on new account creation. This approach, while effective against unsophisticated, low-effort attackers, has become fundamentally inadequate against organized crime syndicates.
The core weakness in siloed defense is simple adaptability. If a system blocks access based on a known malicious IP range, the attacker merely rotates their residential proxy pool. If the block is based on a disposable email address, they pivot to using a "aged" corporate email harvested from a previous breach. The attacker is not trying to defeat one checkpoint; they are navigating a gauntlet, and defeating any single checkpoint is sufficient to advance to the next stage. This "chain" logic means that even if 99% of the steps are heavily fortified, the single weak link exploited by a low-tech step is enough to compromise the entire process.
Anatomy of the Modern Attack Chain: From Infiltration to Extraction
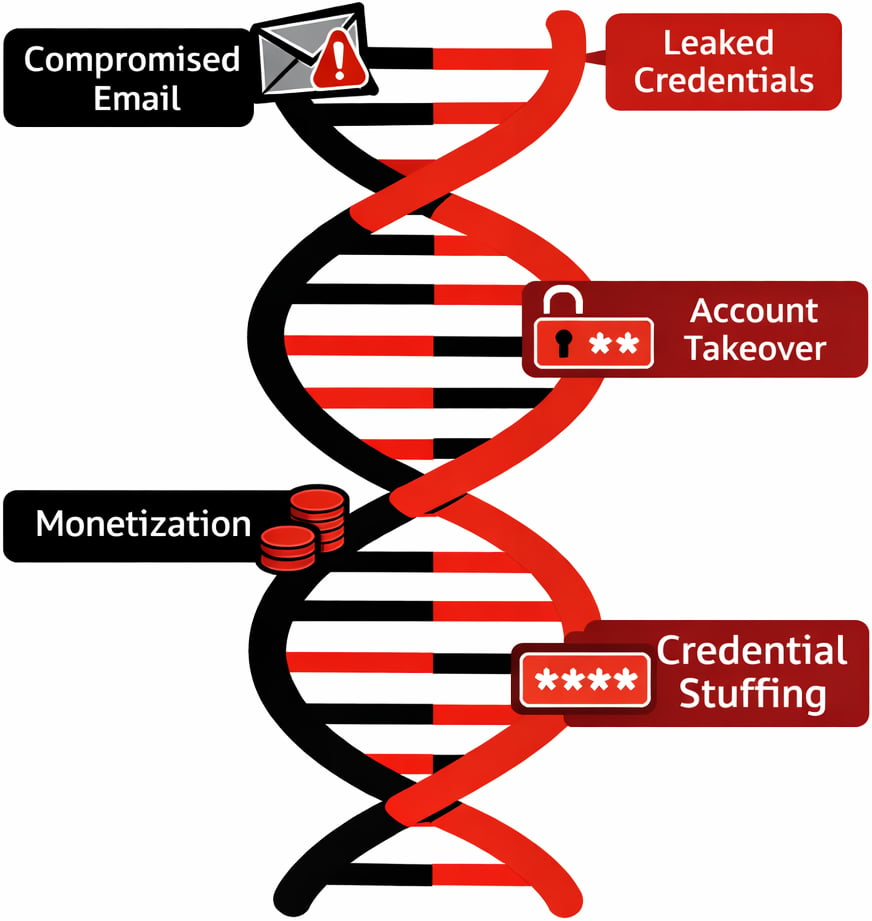
The modern fraud lifecycle can typically be broken down into three critical phases: Infiltration (Scale Generation), Dormancy and Staging, and Monetization (Account Takeover or Exploitation).
Phase 1: Infiltration and Scale Generation
The assault begins with automation aimed at achieving massive scale with minimal operational cost. Attackers leverage sophisticated botnets and custom scripts to initiate thousands of registrations across targeted platforms—be it e-commerce sites, SaaS providers, or financial applications.
This stage requires obscuring basic infrastructure identifiers. This is achieved through the heavy deployment of residential proxies. Unlike easily identifiable data center IPs or known VPN endpoints, residential proxies route traffic through legitimate, compromised residential endpoints. To the target system, this traffic appears indistinguishable from genuine, geographically dispersed home users. This masks the origin point and bypasses IP reputation filters designed to catch bulk traffic from singular sources.

Furthermore, the credentials used are not freshly generated. They are frequently "aged" or "seasoned" profiles, often sourced from data dumps or previous compromises. These compromised accounts possess historical login data, cookies, or linked activity, lending them a veneer of legitimacy that circumvents checks designed to flag brand-new user profiles. In some cases, attackers use mobile device emulators or specialized SDK manipulation to generate device fingerprints that mimic long-term, genuine users, further deepening the deception.
Phase 2: Dormancy and Staging
Once initial accounts are successfully provisioned, the immediate aggressive actions cease. This transition is vital for evading detection rules based on rapid high-value activity. The fraudulent accounts enter a staging period, where they engage in low-intensity, human-like interactions. They might browse non-critical pages, wait a predetermined period, or perform minor, non-monetary transactions. This behavior is designed to train baseline risk models into accepting the accounts as legitimate users with established history.
This phase is where the tools often shift. While registration might have relied on headless browsers and complex proxy chains, the staging phase often involves human operatives or less sophisticated automation to mimic organic browsing patterns, intentionally moving away from the initial, high-risk automated environment.
Phase 3: Account Takeover (ATO) and Monetization
This final stage is the payoff. Utilizing credentials obtained via credential stuffing campaigns, phishing success, or malware payloads, the attacker executes the Account Takeover (ATO). The credentials, which might have been flagged if used immediately after registration, are now introduced to an account that the system has already scored as "low risk" due to the dormancy period.
The monetization vector varies: draining balances, exploiting promotional credits, executing high-value purchases, or using the compromised account to launch further phishing attacks against the victim’s contact network. Critically, the hand-off between actors is common here. The initial account creator might sell access to a specialized "money mule" or fund drainer who possesses the specific expertise—and separate infrastructure—required to liquidate the assets quickly.
The Pitfalls of Siloed Defense Mechanisms
The segmented nature of the attack chain reveals why reliance on singular data points leads to pervasive security gaps and costly operational overhead through false positives.
IP Reputation Blind Spots: Relying solely on IP reputation is a high-risk strategy. Legitimate customers frequently operate from shared IP spaces—corporate VPNs, university networks, or mobile carrier Network Address Translation (NAT) systems. A handful of bad actors utilizing a residential proxy in one of these shared blocks can pollute the reputation score for hundreds of clean users. Defenders are then forced into the untenable position of either blocking legitimate traffic (false positives) or allowing known risky traffic through.

Email Verification Limitations: While email verification services are essential for weeding out obvious throwaways, modern attackers have adapted. They utilize compromised, aged email accounts from major providers (which are inherently difficult to block universally) or leverage services that generate high-quality synthetic identities built from fragments of real user data, passing basic domain reputation checks with flying colors.
Identity and Device Controls: Static identity checks (name, address, date of birth matches) are easily circumvented by synthetic identity fraud, where unique combinations of real data pieces are stitched together to create a seemingly valid profile. Similarly, device fingerprinting tools that focus only on blatant anomalies like rooted devices or known emulators miss sophisticated attacks where the fraudster operates on a standard, clean device that was compromised prior to interaction with the platform (e.g., via malware installed on the user’s personal machine).
The most significant failure occurs when an ATO campaign follows a successful credential stuffing wave. Bot detection tools successfully block the automated stuffing attempt. However, once the attacker switches to manual login using the same stolen credentials, the security system sees only human input—a seemingly legitimate username and password entry—and grants access, effectively bypassing the bot defense layer entirely.
Expert Analysis: The Imperative of Multi-Signal Correlation
Effective digital defense is no longer about applying sequential filters; it is about holistic risk modeling achieved through multi-signal correlation. This approach moves beyond "Is this IP bad?" to "Is this IP, behaving with this device fingerprint, using this type of email, attempting this specific sequence of actions, characteristic of known abuse?"
When signals are correlated, the contextual picture sharpens dramatically:
- Contextual Risk Elevation: An IP address that might appear mildly suspicious in isolation—perhaps flagged due to a VPN connection—is suddenly flagged as highly malicious when correlated with a brand-new device fingerprint attempting to register multiple accounts simultaneously, especially if those accounts immediately try to exploit a known promotional vulnerability.
- Behavioral Weighting: A user logging in from a seemingly clean device and location can still be identified as high-risk if their interaction speed mimics robotic activity, or if their session timeline aligns precisely with known patterns associated with post-credential stuffing account takeover attempts. Modern decision engines weigh hundreds or thousands of data points—ranging from network telemetry to minute behavioral metrics—to derive a single, highly accurate risk score.
- Unifying the Security Stack: Organizations must decommission the practice of treating IP intelligence, identity verification, and device analytics as separate departmental tools. These disparate data streams must converge into a unified risk engine. Each event, from initial browsing to final checkout, must be assessed against the totality of available contextual data, ensuring that the assessment is dynamic and reactive to the entire lifecycle of the session.
This unified modeling drastically reduces the operational friction caused by false positives. Legitimate users, whose signals align with established positive behavior profiles, sail through verification processes unimpeded. Meanwhile, determined adversaries, who must use imperfect combinations of stolen/spoofed assets, generate high-risk correlations that trigger appropriate friction or outright denial.
Industry Implications and Case Study: Combating Registration Abuse
The adoption of correlated intelligence is crucial across industries, but it is particularly impactful in sectors reliant on high-volume user onboarding, such as Software as a Service (SaaS) and gaming platforms that offer high-value free trials or referral bonuses.
Consider a growing SaaS platform offering a feature-rich free tier designed to drive conversion. Organized abusers quickly weaponize this free access to scrape proprietary datasets or test stolen payment credentials en masse. Initial defenses—blocking known bad IPs and blacklisting disposable emails—provide only temporary relief, alienating genuine small businesses and freelancers who share public network resources.
By implementing a correlation engine, the platform begins scoring registrations based on the confluence of factors:
- Device Fingerprint Reuse: Multiple new accounts created within minutes, all possessing an identical, novel device fingerprint (indicating an emulator or scripted environment).
- Network Velocity: A cluster of registrations originating from an IP range recently associated with automated login attempts.
- Behavioral Deviation: New accounts immediately attempting to access administrative functions or API endpoints reserved for premium tiers.
These aggregated signals allow the system to identify coordinated abuse clusters rather than treating each registration as an isolated event. The platform can then deploy targeted, proportionate responses—such as mandatory CAPTCHA challenges specifically for the cluster, or silently imposing rate limits on scraped data exports—while ensuring that the majority of legitimate trial signups experience zero interruption. This iterative feedback loop, where confirmed abuse and confirmed good users refine the scoring model, continuously increases the cost and complexity for the fraudster, driving down the rate of return on their efforts.
Future Impact and Trends: Staying Ahead of the Adversary
The trend is clear: attackers are professionalizing their operations, treating fraud as a complex logistical challenge that requires modular tools and segmented labor. They will continue to invest heavily in obscuring network origins (e.g., better residential proxy rotation, development of zero-day proxy evasion techniques) and perfecting synthetic identity creation.
To maintain an advantage, security teams must shift focus from detection to prediction and contextual response. The future of fraud prevention lies in real-time threat intelligence integration—leveraging global threat maps and dark web monitoring to ingest intelligence about emerging credential leaks or new tooling before they manifest as attacks on the platform.
Organizations that successfully integrate IP intelligence, device telemetry, identity verification, and deep behavioral analytics into a single, coherent risk framework will establish a much higher operational barrier for cybercriminals. This unified perspective ensures that security decisions are based on comprehensive context rather than incomplete snapshots, ultimately balancing aggressive loss prevention with a frictionless experience for the genuine user base. The battleground is no longer about blocking bad actors; it is about intelligently distinguishing the genuine customer from the sophisticated, multi-layered fraud operation.