The digital landscape has witnessed a disturbing escalation in sophisticated financial fraud as a threat group identified as Storm-2755 pivots toward a predatory campaign targeting the payroll systems of Canadian employees. This operation, categorized by cybersecurity analysts as a "payroll pirate" attack, demonstrates a high degree of technical proficiency, specifically in its ability to circumvent standard security measures that were previously considered robust. By leveraging Adversary-in-the-Middle (AiTM) tactics, these actors are not merely stealing credentials; they are hijacking entire authenticated sessions, effectively turning an organization’s own security protocols against itself to divert salaries into illicit accounts.
The Mechanics of the Payroll Pirate
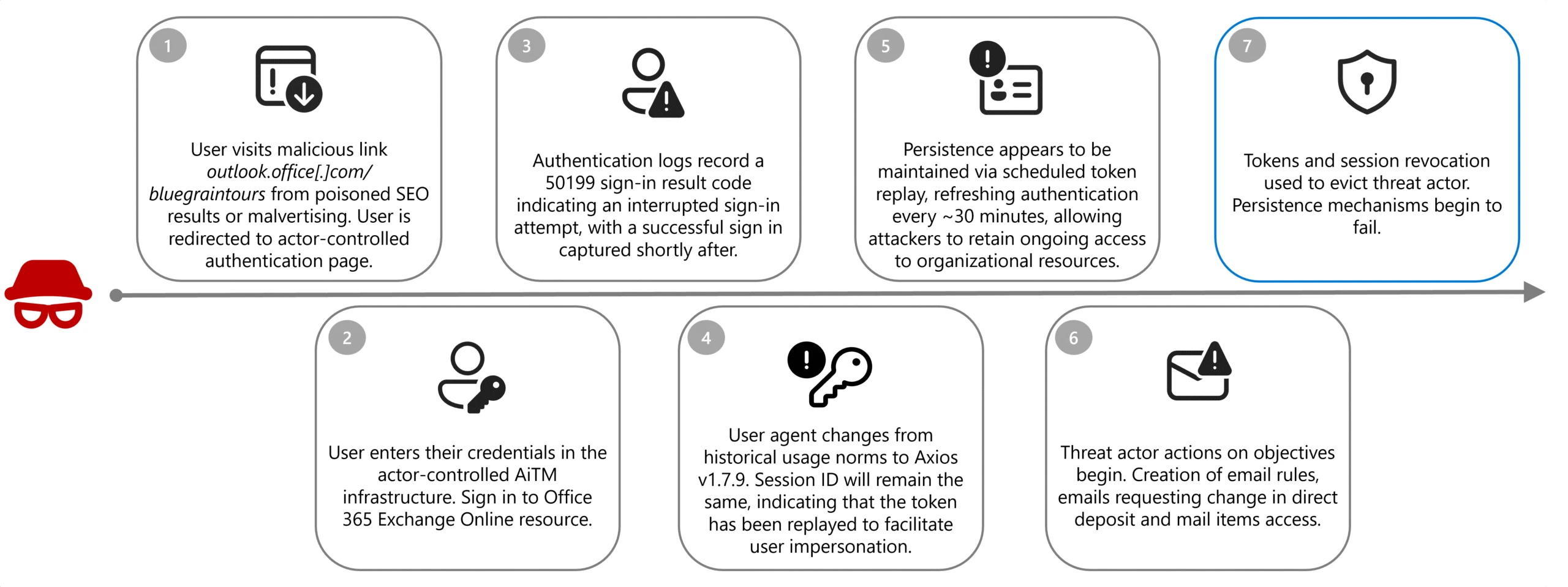
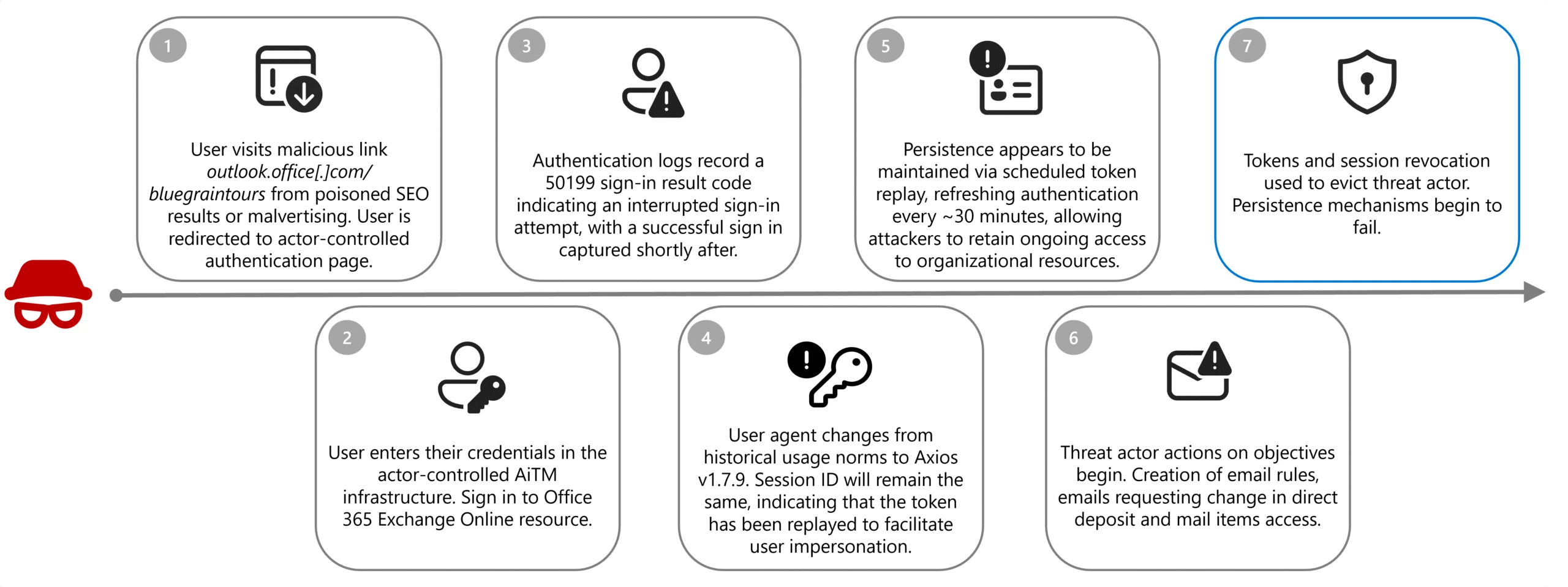
At the heart of the Storm-2755 operation is a masterclass in social engineering coupled with advanced technical exploitation. The attack lifecycle typically begins with search engine optimization (SEO) poisoning or strategic malvertising. The perpetrators ensure that their malicious infrastructure—masquerading as legitimate Microsoft 365 login portals—appears at the top of search results. When a distracted or hurried employee clicks on these links, they are ushered into a proxy-based phishing environment.

Unlike traditional phishing, which captures a static username and password, the AiTM framework functions as a transparent bridge between the user and the legitimate service. The malicious page captures the user’s input in real time and forwards it to the genuine Microsoft authentication service. When the user completes a multifactor authentication (MFA) prompt, the system issues a session cookie or OAuth access token. Because the attacker is proxying the entire flow, they capture this token before the user is redirected to the actual portal. By replaying this token, the attacker gains full, persistent access to the victim’s account without ever needing to solve the MFA challenge themselves.
Establishing Stealth Persistence
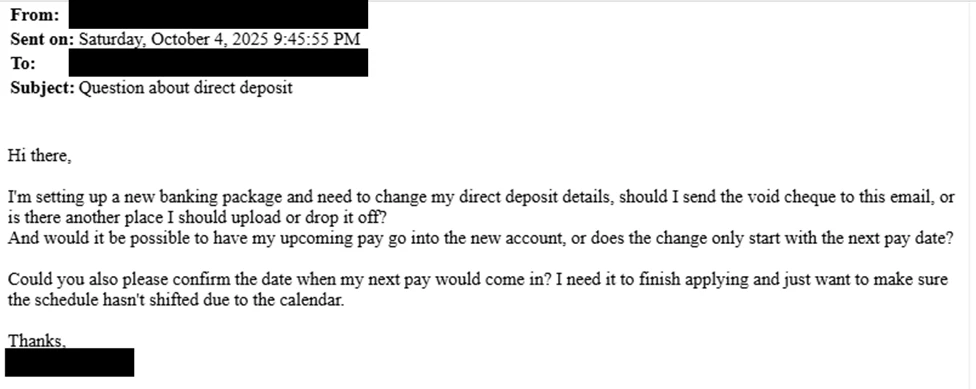
Once the attacker has secured a foothold within the corporate environment, the objective shifts from credential theft to financial extraction. To maintain a low profile, the threat actors immediately implement automated inbox rules. These rules act as a digital screen, intercepting any communication from HR departments or payroll administrators containing keywords like "direct deposit," "bank," "salary," or "account update." By shunting these messages into hidden or obscure folders, the attackers ensure the victim remains oblivious to the impending financial theft.
With the victim’s mailbox compromised, the threat actors adopt the persona of the employee. They initiate correspondence with HR, using forged documents or urgent, fabricated requests to update direct deposit banking information. Should these social engineering attempts encounter resistance or administrative friction, the attackers move to a more direct approach. Utilizing the hijacked session tokens, they gain unauthorized entry into enterprise human capital management (HCM) platforms such as Workday. Once inside, they perform the manual intervention themselves, altering bank account routing numbers to ensure that the next pay cycle deposits the employee’s salary directly into a fraudulent account controlled by the criminal syndicate.

Industry Implications and the Erosion of Legacy MFA
The success of the Storm-2755 campaign serves as a sobering wake-up call regarding the limitations of "legacy" multifactor authentication. For years, organizations have relied on SMS-based or app-based push notifications as the gold standard of defense. However, the rise of AiTM frameworks has rendered these methods insufficient against determined, financially motivated actors.
This shift forces a broader industry reassessment of what constitutes "phishing-resistant" authentication. Experts argue that the industry must transition toward FIDO2-based authentication, such as hardware security keys (e.g., YubiKeys) or device-bound passkeys. These technologies utilize cryptographic challenges that cannot be proxied or captured by a third-party relay, effectively nullifying the threat posed by session token theft. The failure to adopt these standards is no longer just a technical oversight; it is an invitation for financial loss that can cripple both employees and the reputation of the enterprise.
The Evolution of Business Email Compromise (BEC)
Payroll piracy is the latest, and perhaps most aggressive, evolution of Business Email Compromise (BEC). Traditionally, BEC scams focused on executive impersonation—convincing a junior accountant to wire funds to a "vendor" for a fictitious emergency. Today, the focus has shifted to the granular, personal level of the individual employee. By targeting the payroll link, attackers gain a reliable, repeatable source of income that is often harder for corporations to detect until it is too late.
The scale of the problem is staggering. As reported by the FBI’s Internet Crime Complaint Center (IC3), BEC fraud resulted in over $3 billion in losses in the previous year alone, with more than 24,000 recorded complaints. When these losses are compounded by the psychological toll on employees who suddenly find their livelihood intercepted, the ripple effects are significant. Organizations are now facing the reality that they must secure not only their central databases but the individual endpoints and authentication habits of every employee.
Strategic Defensive Posture
For organizations aiming to bolster their defenses against such agile adversaries, a "defense-in-depth" approach is mandatory. This includes:
- Phishing-Resistant Authentication: Moving beyond legacy MFA to hardware-backed or FIDO2-compliant authentication is the single most effective barrier against AiTM attacks.
- Conditional Access Policies: Implementing granular access controls that verify the device, location, and behavior of a user session. If a session originates from an unknown IP or an unauthorized geographic region, it should trigger an immediate re-authentication or session revocation.
- Proactive Monitoring of Inbox Rules: Security operations centers (SOCs) should automate the detection of suspicious inbox rules—specifically those that move, delete, or hide emails containing financial keywords.
- Verification Protocols for Payroll Changes: HR and finance departments must move away from email-based requests for banking changes. Implementing an out-of-band verification process—such as a mandatory video call or a secure, multi-step portal-based approval process—prevents attackers from abusing the email channel.
- Token Lifecycle Management: Regularly revoking active sessions and enforcing short-lived token lifetimes reduces the window of opportunity for an attacker using a stolen session cookie.
Future Trends: The Automation of Fraud
As we look toward the future, the integration of automation and artificial intelligence in these attacks is inevitable. We are already seeing evidence of "phishing-as-a-service" platforms that provide non-technical criminals with the infrastructure to run AiTM campaigns effortlessly. As these tools become more accessible, the volume of payroll pirate attacks is likely to grow, extending beyond Canada and the United States to target global markets.
Moreover, as organizations harden their email environments, attackers will likely diversify their tactics to target other productivity platforms, such as Slack, Microsoft Teams, or internal project management software. The "payroll pirate" model will be refined to incorporate deepfake audio or video, allowing attackers to mimic employees during "verification" calls with HR staff.
The battle between cybersecurity professionals and groups like Storm-2755 is an arms race of convenience versus security. While organizations strive to make the user experience as frictionless as possible, attackers are exploiting that very convenience to bypass the front door. The challenge for the modern enterprise is to cultivate a security culture that recognizes the legitimacy of the threat, understands that traditional passwords and simple MFA are no longer sufficient, and treats the protection of payroll data with the same urgency as the protection of proprietary trade secrets.
In conclusion, the emergence of Storm-2755 is a significant milestone in the evolution of cyber-enabled financial crime. It highlights the vulnerability of the modern, cloud-centric workforce and underscores the necessity for a fundamental shift in how we handle digital identity. Organizations that fail to evolve their security stack to meet these new realities risk becoming the next headline in an already crowded ledger of financial losses. The path forward is clear: abandon legacy authentication, scrutinize the communication channels between HR and staff, and assume that every session, no matter how securely it appears to be guarded, is a potential target for interception.