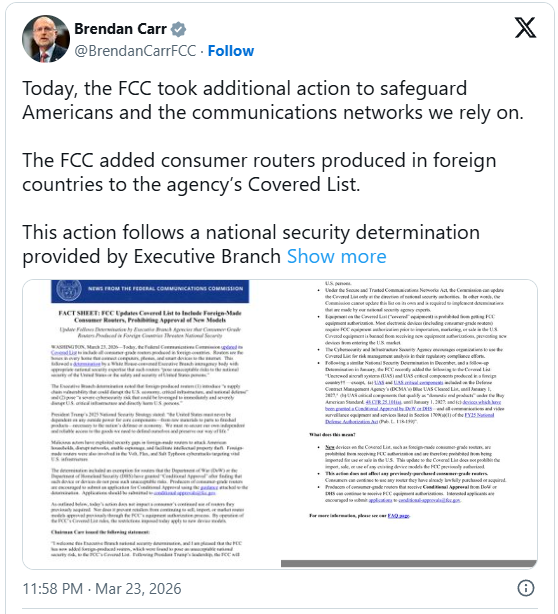
The Federal Communications Commission (FCC) has enacted a sweeping regulatory measure, formally incorporating virtually all consumer routers manufactured outside the United States onto its "Covered List," effectively halting the introduction and sale of new models within American commerce. This decisive action, rooted in deepening concerns over technological sovereignty and national security vulnerabilities, marks a significant escalation in the U.S. government’s strategy to decouple critical communications infrastructure from perceived foreign threats.
This regulatory expansion is executed under the authority granted by the Secure and Trusted Communications Networks Act of 2019. This legislation empowers the FCC to curate and maintain the Covered List—a definitive catalog of communications equipment and services deemed to present an unacceptable risk to the security posture of the nation or the physical safety of American citizens. Historically, the list targeted specific entities and products explicitly linked to espionage or security compromises, such as the established prohibitions against equipment from vendors like Huawei, ZTE, Kaspersky, Hikvision, and Dahua. However, the latest directive pivots from product-specific bans to a sweeping, geography-based exclusion for an entire category of essential networking hardware.
The foundation for this expansive ban is a National Security Determination formally issued on March 20th by an interagency body within the Executive Branch. This determination concluded that the extensive reliance on routers fabricated overseas introduces systemic supply-chain risks of the highest order. The assessment explicitly warned that these vulnerabilities possess the potential to "disrupt the U.S. economy, critical infrastructure, and national defense." Furthermore, the determination posits that these devices could be weaponized to initiate "immediate and severe disruption of U.S. critical infrastructure and directly harm U.S. persons."
This heightened scrutiny is not theoretical; the FCC documentation supporting this mandate pointed directly to recent, high-profile cyber intrusions. Specifically, the agency highlighted the documented activities of sophisticated threat actors—including those associated with state-sponsored operations such as Volt, Flax, and Salt Typhoon—who allegedly leveraged vulnerabilities embedded within foreign-made networking hardware to successfully breach and maintain persistence within vital U.S. telecommunications and infrastructure networks. This evident pattern of exploitation transformed the risk from a potential liability into a demonstrable, active threat requiring immediate regulatory intervention.
Industry Implications: Reshaping the Networking Landscape
The immediate implications for the telecommunications and consumer electronics industries are profound. For the average American consumer, the day-to-day use of existing home networks remains unaffected; current models already in use or on store shelves are grandfathered under the existing regulatory framework and will continue to function and be sold. However, the pipeline for future innovation and market entry for new hardware has been fundamentally altered.
This directive forces a significant recalibration for global networking equipment manufacturers. The previous model, which often relied on optimized, high-volume production facilities located outside U.S. jurisdiction, is now untenable for devices seeking FCC approval for the American market. This essentially mandates a shift toward onshoring, nearshoring, or at the very least, verifiable, trusted sourcing for manufacturing components and final assembly if non-U.S. based entities wish to remain players in the lucrative U.S. router market.
The regulatory environment has evolved rapidly, moving beyond simple certification of radio frequency compliance to encompass deep vetting of supply chain integrity, firmware provenance, and operational security across the entire lifecycle of the device. This places immense pressure on manufacturers to provide unprecedented transparency into their development and production ecosystems—a level of disclosure that many international firms may find commercially or politically difficult to achieve.
The New Regulatory Gate: Conditional Approvals and Transparency Demands
While the blanket ban is severe, the FCC has established narrow pathways for exceptions and ongoing operations. Conditional approval has been specifically extended to certain specialized routers currently utilized by sensitive federal agencies, such as the Department of War (DoW) and the Department of Homeland Security (DHS), particularly those integrated within Unmanned Aircraft Systems (UAS) platforms. These exemptions were granted only after rigorous, bespoke assessments determined that the specific operational context negated the generalized security risk.
For commercial entities operating outside the specialized government exemptions, the door is not entirely closed, but the entrance requirements have dramatically increased. Foreign manufacturers wishing to introduce new consumer-grade router models must now navigate an alternative approval pathway, contingent upon radical transparency. The FCC requires detailed disclosures covering several critical vectors:
- Source Code and Firmware Auditing: Manufacturers must provide access for thorough security auditing of operating systems, firmware binaries, and underlying source code to verify the absence of backdoors, intentional vulnerabilities, or unauthorized remote access mechanisms.
- Manufacturing Provenance: Complete transparency regarding the entire Bill of Materials (BOM), including the origin of all critical semiconductors, components, and sub-assemblies, is now mandatory.
- Ownership and Operational Control: Detailed disclosure concerning the corporate structure, ownership stakes, and ultimate operational control of the manufacturing entity is required to assess potential influence by foreign state actors.
This alternative process is inherently more complex and time-consuming than standard certification. The standard FCC testing cycle, typically spanning a few months under ideal conditions, is now compounded by security vetting procedures that can extend timelines significantly, often stretching into half a year or more, even when cooperation is complete.
Expert Analysis: Geopolitics Meets the Local Network
From a cybersecurity policy perspective, this FCC action is less about typical consumer electronics compliance and more about infrastructure hardening in an era of persistent geopolitical tension. Industry analysts view this as a clear manifestation of the "trust nothing, verify everything" doctrine being applied to the foundational layers of the internet.
"This is a decisive move to secure the edge of the network," notes Dr. Evelyn Reed, a specialist in critical infrastructure resilience at the Atlantic Policy Institute. "Routers are the gatekeepers of data flow. If a state actor controls the gateway, they control the narrative, the traffic, and potentially the ability to execute devastating kinetic or systemic disruptions. The FCC is effectively saying that the risk associated with foreign, opaque supply chains for this hardware is no longer acceptable given current threat intelligence."
The ruling signals a significant pivot toward technological decoupling, moving the U.S. away from the cost efficiencies gained through deeply integrated globalized manufacturing in favor of national security guarantees. While this bolsters defense against state-level cyber warfare, experts caution that it introduces significant market friction.
Future Trends and Market Adaptation
The short-term consequence for U.S. consumers is likely to be increased cost and reduced choice. The added expense associated with stringent security auditing, the necessity of establishing U.S.-compliant or trusted-partner manufacturing hubs, and the inherent delays in the vetting process will inevitably be passed down. Manufacturers who find the compliance burden outweighs the potential profit margin in the U.S. market may strategically elect to withdraw, leading to market contraction in specific hardware segments.
Furthermore, the regulatory scope is already showing signs of creeping expansion. The FCC acknowledged ongoing concerns regarding Unmanned Aircraft Systems (UAS), granting a reprieve for software and firmware updates on existing UAS-related hardware only until January 1, 2027. This temporary measure suggests that similar supply chain scrutiny will soon be applied to other sensitive endpoints, potentially including specialized IoT devices, industrial control system components, and advanced wireless access points integral to 5G and future network deployments.
This move sets a precedent that other allied nations may follow, potentially leading to a splintering of global technology standards where trusted geopolitical partners maintain separate, verifiable supply chains, while non-trusted regions are entirely excluded from critical markets. For domestic producers, this presents an unprecedented opportunity to capture market share, provided they can rapidly scale up production capabilities while meeting the newly rigorous security and transparency requirements. The long-term viability of the U.S. networking sector may hinge on its ability to rapidly build out a secure, resilient domestic manufacturing base capable of producing high-quality, certified communications hardware at competitive costs. This regulatory shift is not merely a ban; it is an aggressive industrial policy directive aimed at national technological self-sufficiency in core digital infrastructure.