The landscape of professionalized cybercrime is undergoing a subtle yet dangerous evolution as the "Gentlemen" ransomware syndicate expands its operational footprint. Recent forensic investigations have uncovered that this emerging threat actor is no longer relying solely on its proprietary encryption lockers. Instead, it has begun folding established, high-capacity proxy malware into its attack lifecycle, effectively transforming its operations from isolated incidents into a coordinated, bot-powered assault on corporate infrastructure.
The Rise of a Quiet Threat
Emerging on the digital criminal scene in mid-2025, the Gentlemen ransomware-as-a-service (RaaS) operation initially flew under the radar of many global security analysts. While their public-facing data leak portal lists approximately 320 victims, recent telemetry suggests that the group’s true operational reach is significantly broader. Unlike many transient ransomware groups that rely on "spray and pray" tactics, Gentlemen has demonstrated a clear preference for high-value targets, including critical national infrastructure providers, such as the high-profile breach of Romania’s Oltenia Energy Complex late last year, and various enterprise entities like The Adaptavist Group.
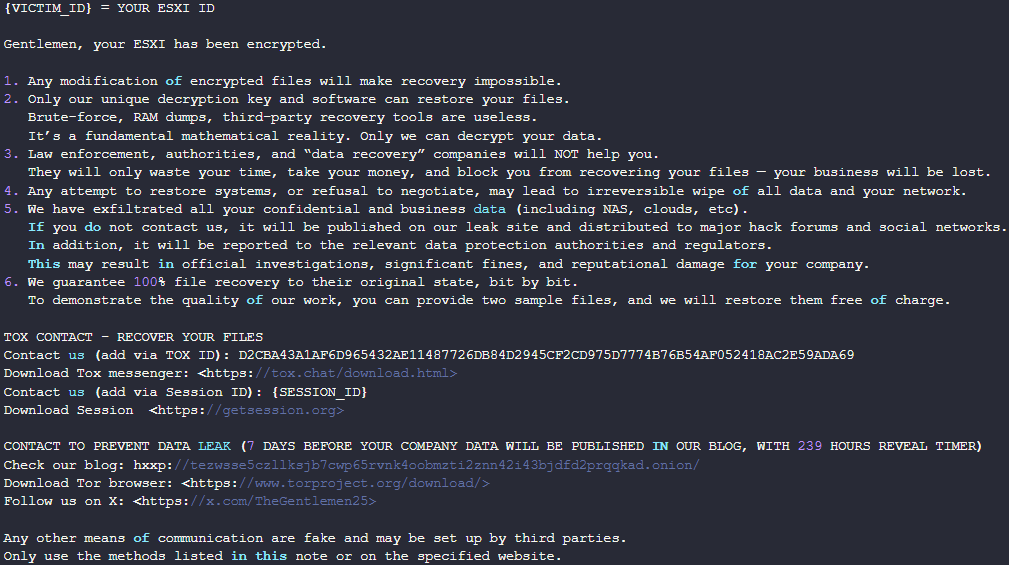
The group’s technical versatility is notable; they maintain a sophisticated Go-based encryption engine capable of compromising Windows, Linux, NAS, and BSD environments, alongside a specialized C-based variant designed to cripple ESXi hypervisors. This cross-platform capability marks them as a modern, platform-agnostic threat actor capable of disrupting entire data centers with surgical precision.

The Pivot to SystemBC
The most alarming development in the Gentlemen group’s tactical evolution is the integration of SystemBC. First identified in the wild around 2019, SystemBC is a persistent, SOCKS5-based proxy malware that acts as a stealthy "highway" for malicious traffic. By embedding SystemBC into their post-exploitation workflow, Gentlemen affiliates are gaining the ability to route communications through a vast, pre-existing network of infected hosts.
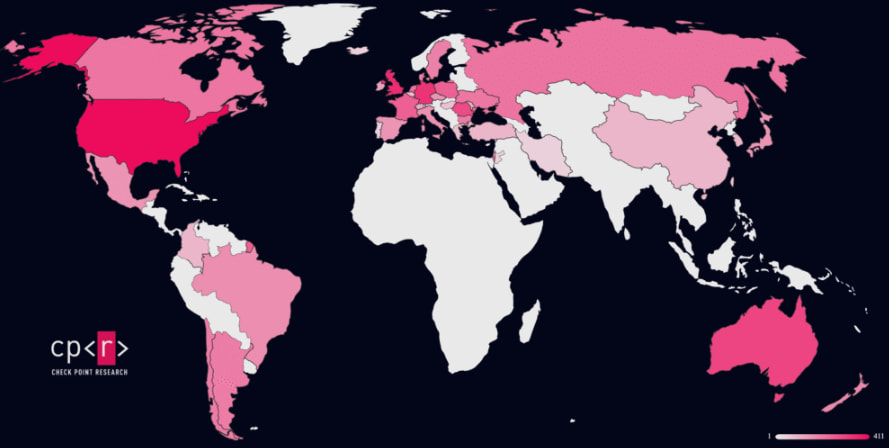
Evidence from recent security audits reveals a Command-and-Control (C2) infrastructure managed by these actors that encompasses over 1,570 distinct infected hosts. Notably, this is not a collection of compromised consumer PCs. The telemetry indicates a distinct focus on corporate and organizational environments, suggesting that the Gentlemen gang is actively curating a network of "beachheads" within professional organizations to facilitate long-term persistence, data exfiltration, and the covert delivery of secondary payloads.
Despite various international law enforcement efforts—most notably the 2024 operations that dismantled significant portions of loader-server infrastructure—the SystemBC ecosystem has proven remarkably resilient. Its ability to turn infected Virtual Private Servers (VPS) into a modular proxy network ensures that even if one node is neutralized, the broader infrastructure remains functional. The Gentlemen group’s adoption of this tool signals a transition toward a more "industrialized" form of ransomware delivery.

Anatomy of an Attack
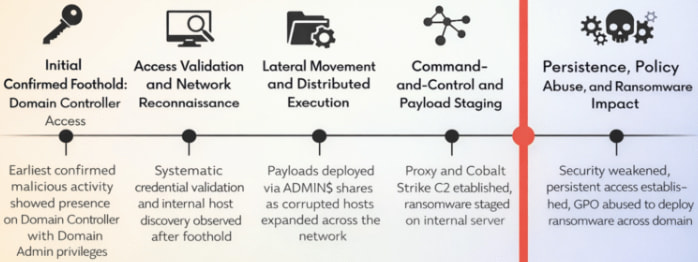
While the initial access vector for these specific campaigns remains obscured by the attackers’ careful sanitization of logs, the subsequent stages of the attack chain paint a picture of a highly disciplined adversary. Once inside a network, the threat actors prioritize the acquisition of Domain Admin privileges. By operating from a compromised Domain Controller, the attackers effectively bypass local security controls, granting them the keys to the entire kingdom.
The reconnaissance phase is characterized by a methodical approach to credential harvesting. Using tools like Mimikatz, the attackers systematically map the network and identify high-value targets. Once the stage is set, they deploy Cobalt Strike—the industry standard for post-exploitation—via Remote Procedure Call (RPC). This allows them to move laterally through the victim’s network, staging the final ransomware payload on internal servers.
The final blow is delivered with cold, programmatic efficiency. Leveraging native Group Policy (GPO) propagation, the attackers trigger a near-simultaneous execution of the encryptor across the domain. This synchronization is designed to overwhelm IT security teams and prevent the implementation of containment measures, such as network isolation, before the encryption process completes.
The encryption logic itself is equally refined. Utilizing a hybrid cryptographic scheme—a combination of X25519 (Diffie–Hellman) for key exchange and XChaCha20 for file encryption—the malware generates unique, ephemeral key pairs for every individual file. This approach is not only cryptographically robust but also performance-optimized; to avoid triggering behavioral detection systems that monitor for high I/O spikes, the malware only partially encrypts larger files (1%, 3%, or 9%), while fully locking files under 1 MB. Before the final encryption, the malware performs a "scorched earth" sweep, terminating database services, backup software, and virtualization processes, while wiping Shadow copies and system logs to prevent recovery.
Industry Implications and Strategic Shifts
The Gentlemen group’s trajectory reflects a broader trend within the RaaS ecosystem: the shift from "lone wolf" tactics to a collaborative, tool-agnostic model. By integrating mature post-exploitation frameworks like Cobalt Strike with persistent proxy networks like SystemBC, they are mirroring the operational maturity of state-sponsored Advanced Persistent Threat (APT) groups.
This shift presents a significant challenge for incident response teams. Traditional signature-based defenses are increasingly insufficient against actors who frequently rotate their infrastructure and rely on living-off-the-land (LotL) techniques. The use of SystemBC as a proxy layer means that malicious traffic often originates from "trusted" or legitimate servers, making it incredibly difficult for network security appliances to distinguish between a legitimate remote-access session and an active data exfiltration event.
Furthermore, the geographic distribution of the victims—heavily concentrated in the United States, United Kingdom, Germany, Australia, and Romania—indicates a targeted economic strategy. By focusing on nations with strong regulatory frameworks and high costs associated with downtime, the Gentlemen group maximizes its leverage during extortion negotiations.
Looking Ahead: The Future of Ransomware Persistence
As the Gentlemen syndicate continues to recruit new affiliates through dark web forums, we can expect to see further refinement in their "toolchain." The integration of SystemBC is likely just the beginning. Security researchers anticipate that such groups will continue to adopt modular, "as-a-service" components, allowing them to remain agile in the face of evolving security countermeasures.
The danger for modern enterprises lies in the "dwell time" that these proxy infrastructures provide. With a botnet of 1,570 hosts at their disposal, attackers can maintain a dormant presence in a network for weeks or months, waiting for the optimal moment to strike. This necessitates a fundamental change in how organizations approach threat hunting. Defenders must shift their focus from merely blocking known malicious binaries to monitoring for anomalous network behavior, such as unusual SOCKS5 traffic patterns, unauthorized use of GPO, and suspicious remote execution calls.
In response to these developments, security experts are advocating for a more robust defense-in-depth strategy. This includes the implementation of granular network segmentation, the adoption of zero-trust architecture to prevent lateral movement, and the regular, offline testing of backup integrity. As the Gentlemen group demonstrates, the ransomware threat is no longer just about the locker—it is about the entire, invisible infrastructure that supports the crime.
For defenders, the current situation serves as a stark reminder that the "gentlemanly" moniker of this group is anything but accurate. They are a well-funded, highly organized, and technically proficient adversary that is successfully bridging the gap between commodity malware and professional cyber-espionage. Protecting against them requires not just better tools, but a more profound understanding of how modern ransomware operations sustain their momentum in a globalized, hyper-connected digital economy. As we move through 2026, the ability of organizations to detect and disrupt these proxy-powered attack chains will be the deciding factor in whether they become the next headline or remain resilient against this evolving tide of digital extortion.

