The sentencing of 23-year-old Kamerin Stokes to 30 months in a federal penitentiary marks a definitive conclusion to a brazen chapter of cyber-criminality that targeted the booming online sports betting industry. Stokes, a Tennessee resident operating under the online pseudonym "TheMFNPlug," was found guilty of facilitating the unauthorized sale of tens of thousands of compromised DraftKings accounts. His incarceration serves as a stark reminder of the escalating risks associated with credential-stuffing attacks and the persistent threat posed by secondary markets for illicit digital access.
The scope of the operation, which saw nearly 68,000 DraftKings accounts exposed in a November 2022 breach, underscores a fundamental vulnerability in modern digital platforms: the reliance on recycled user credentials. Stokes did not act in isolation. The original breach was the work of two other individuals, Nathan Austad (known in cyber circles as "Snoopy") and Joseph Garrison, who leveraged vast databases of stolen login credentials to bypass authentication protocols. By systematically testing these stolen email-password combinations against the betting platform’s infrastructure, the perpetrators successfully gained unauthorized entry to a significant percentage of the user base.
Once the accounts were compromised, the focus shifted from simple access to direct financial theft. Prosecutors revealed that the group’s activities resulted in the illicit withdrawal of approximately $635,000 from roughly 1,600 accounts. The methodology was notably efficient: perpetrators would link a new, attacker-controlled payment method to the compromised account, perform a minimal $5 deposit to verify the payment channel, and subsequently drain the account’s existing funds. This systematic plundering forced the sports betting giant to issue substantial refunds to affected users, illustrating the profound financial and reputational damage that such breaches inflict upon companies operating in high-trust, high-stakes environments.

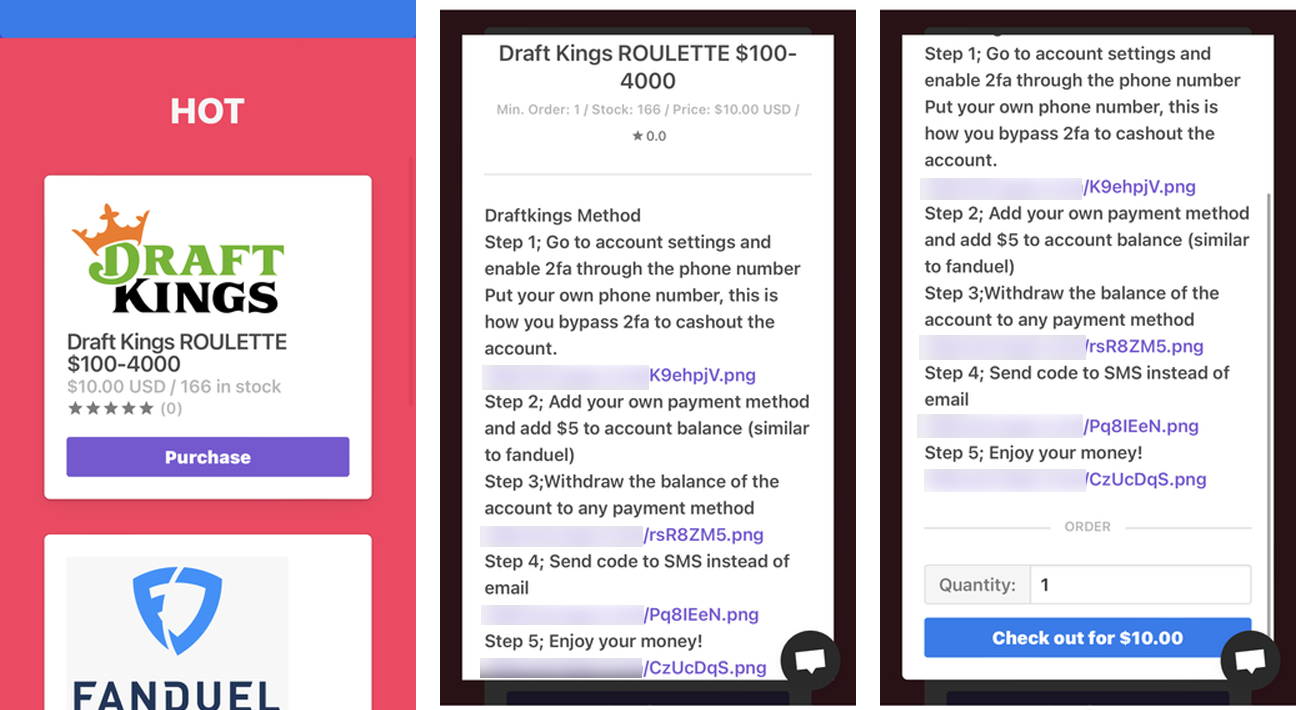
Stokes played a critical role in the distribution chain. While Austad and Garrison managed their own "shops" for selling access to hijacked accounts—extending their reach beyond DraftKings to include FanDuel and various retail entities—Stokes operated as a high-volume reseller. He purchased compromised credentials in bulk, subsequently listing them on his own platform to a secondary market of bad actors eager to exploit the accounts. This tiered structure of cyber-crime is emblematic of the modern "as-a-service" ecosystem, where specialized actors focus on either the breach, the infrastructure, or the distribution, effectively commoditizing the theft of digital identities.
Perhaps the most startling aspect of the case was Stokes’s blatant disregard for judicial authority. Following his initial arrest, entry of a guilty plea, and subsequent release pending sentencing, Stokes demonstrated a level of audacity that shocked prosecutors. Rather than retreating, he relaunched his illicit marketplace under the provocatively defiant tagline "fraud is fun." In a justification that appeared to defy logic, he reportedly resumed his criminal enterprise to generate the funds necessary to pay for his legal defense. This recidivism ultimately led to the revocation of his pretrial release and his remand into federal custody, culminating in the 30-month sentence, three years of supervised release, and a heavy financial penalty involving over $1.3 million in restitution and significant asset forfeiture.
Industry Implications: The Persistence of Credential Stuffing
The DraftKings case is a quintessential example of why credential stuffing remains the "scourge" of the digital economy. Because consumers frequently reuse passwords across multiple websites, a single breach at a minor online retailer can provide the keys to a kingdom for a major financial platform. For companies in the sports betting, e-commerce, and fintech sectors, this presents an existential security challenge.
Industry analysts point out that traditional username/password authentication is no longer sufficient. The prevalence of these automated attacks necessitates a move toward more robust, multi-layered security architectures. This includes the widespread adoption of multi-factor authentication (MFA), particularly hardware-based security keys or app-based push notifications, which effectively nullify the utility of stolen passwords. Furthermore, modern behavioral biometrics and sophisticated bot-detection software are becoming essential tools for identifying the anomalous, rapid-fire login attempts that characterize credential-stuffing campaigns.

Beyond the technical solutions, there is an urgent need for organizational vigilance regarding account lifecycle management. The speed with which these attackers were able to add new payment methods and drain funds suggests that security teams must prioritize real-time anomaly detection for account changes. If a user’s account suddenly associates with a new, unverified payment source, it should trigger an immediate "stop" or secondary verification protocol. The financial industry is moving toward "Zero Trust" architectures, where no user or device is trusted by default, even if they possess the correct password.
The Human Element in Cyber-Crime
The behavior exhibited by Stokes—the cavalier attitude toward federal law and the public marketing of his illicit services—highlights a growing trend in the demographics of cyber-crime. We are seeing a shift from the archetypal, shadowy hacker working in isolation to a more interconnected, social-media-savvy generation of digital criminals. These individuals often view their illicit activities as "hustles" or "gigs," using platforms like Telegram and dark-web forums to build brands and customer bases.
This "gamification" of crime poses a significant challenge for law enforcement agencies. The barriers to entry for these cyber-crimes are historically low, as the necessary tools, databases, and expertise are readily available on the dark web. When criminals believe they can operate with a degree of impunity or that the potential financial reward outweighs the risk of incarceration, the frequency of such attacks increases. The firm response from the Department of Justice in this instance—imposing both significant prison time and substantial financial penalties—is designed to act as a deterrent, signaling that the digital frontier is no longer a lawless space.
Future Trends: Where the Digital Underground Goes Next
As defenses against simple credential stuffing continue to harden, the threat landscape is evolving. We are observing a transition toward more targeted, sophisticated attacks, including "session hijacking" or "adversary-in-the-middle" (AitM) attacks, which can bypass even standard MFA by stealing the session cookies of a user. Furthermore, the integration of generative AI into the attacker’s toolkit allows for the creation of more convincing phishing campaigns and the automation of even more complex account takeover tactics.
The "shops" that Stokes and his cohorts operated are also becoming more decentralized and resilient. As platforms are shut down, others rise in their place, often hosted in jurisdictions that do not cooperate with international law enforcement. The fight against this form of cyber-crime is therefore becoming a permanent state of affairs, requiring constant innovation in security technology and continuous collaboration between private-sector cybersecurity firms and government entities.
The sentencing of Kamerin Stokes is a milestone, but it is not a solution. It highlights the necessity of a holistic approach to security that combines technical defensive measures, rigorous user authentication standards, and the aggressive prosecution of those who facilitate the commoditization of stolen data. As the digital betting and retail sectors continue to expand, the lesson from this case is clear: security can no longer be an afterthought; it must be the foundation upon which digital customer trust is built. The era of the "low-effort" heist is ending, but the battle to protect the digital identity of the average consumer is only just beginning.

