The rapid integration of reactive Python notebook environments into the data science and machine learning workflow has brought unprecedented efficiency to developers. However, this shift toward interactive, browser-based execution environments has introduced a new frontier for cyber adversaries. A recent surge in malicious activity targeting the Marimo reactive Python framework highlights the growing danger of supply chain and infrastructure abuse. By weaponizing a critical remote code execution (RCE) vulnerability, threat actors are transforming these collaborative research tools into staging grounds for sophisticated, blockchain-backed malware, effectively bypassing traditional network security perimeters.
The Anatomy of the Marimo Exploitation
The focal point of this security crisis is CVE-2026-39987, a pre-authentication RCE flaw that grants attackers the ability to execute arbitrary commands on systems running vulnerable versions of the Marimo platform. The speed at which this vulnerability was weaponized—less than 10 hours following its public disclosure—underscores a troubling trend in the cybersecurity landscape: the "zero-day gap" is rapidly closing as automated exploit development tools become more accessible to low-level threat actors.
Once the vulnerability is triggered, the impact is comprehensive. In observed campaigns, attackers have moved beyond simple reconnaissance, instead focusing on high-value asset extraction. By gaining unauthorized access to the underlying environment, these actors are systematically harvesting environment variables, which often contain sensitive credentials for cloud databases, API keys, and internal service tokens. The subsequent lateral movement, particularly against PostgreSQL and Redis clusters, demonstrates a calculated effort to monetize access through data exfiltration or by embedding persistent backdoors within the victim’s infrastructure.

The Trojan Horse in AI Hubs
Perhaps the most sophisticated aspect of this campaign is the strategic abuse of Hugging Face Spaces. As a premier repository for AI models, datasets, and interactive demos, Hugging Face possesses a high level of "domain trust" among security appliances and firewalls. Attackers have recognized that traffic originating from such a reputable source is far less likely to trigger automated threat detection systems compared to traffic from known command-and-control (C2) servers.
By hosting malicious payloads on Hugging Face, threat actors have effectively camouflaged their activities. In one notable instance, an attacker utilized a space titled vsccode-modetx. This name is a classic example of typosquatting, designed to mimic legitimate Microsoft VS Code extensions or Kubernetes management agents. By distributing a dropper script alongside a binary named kagent, the attacker creates a veneer of legitimacy. Security analysts monitoring the traffic see a connection to a trusted AI platform, masking the underlying process of downloading and executing the NKAbuse malware.
The Evolution of NKAbuse
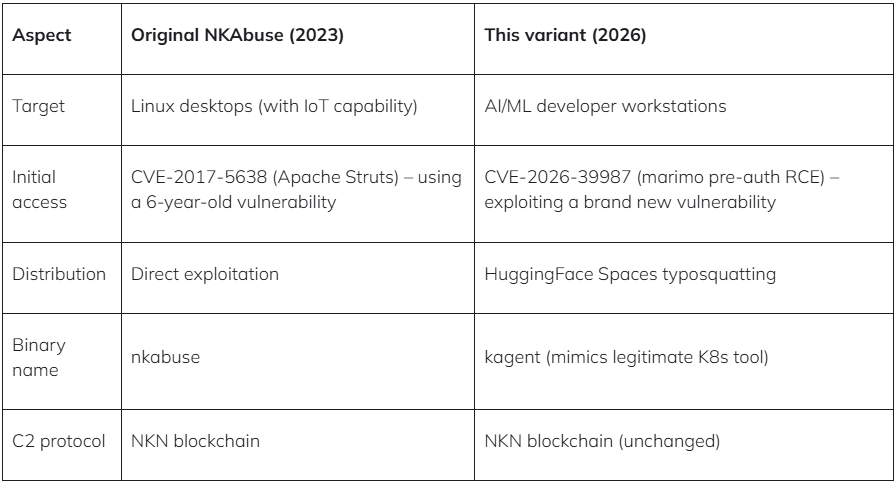
The malware being deployed in these attacks represents a significant evolution of the NKAbuse family. Originally identified in late 2023, NKAbuse gained notoriety for its novel use of the New Kind of Network (NKN) blockchain technology. By leveraging a decentralized peer-to-peer network for its command-and-control communication, the malware achieves a level of stealth that is exceptionally difficult to mitigate using traditional IP-based blocking.
This modern variant has been repurposed as a highly capable Remote Access Trojan (RAT). While the original iterations were largely focused on orchestrating large-scale Distributed Denial of Service (DDoS) attacks, the current strain is tailored for precision infiltration. It supports a wide array of shell commands, enabling operators to manipulate the infected system, move laterally through the network, and maintain persistent access via mechanisms like systemd services, cron jobs, or macOS LaunchAgents. The integration of WebRTC, ICE, and STUN protocols for NAT traversal further ensures that the malware can communicate with its operators even from behind restrictive enterprise firewalls, rendering traditional perimeter defenses largely ineffective against such advanced connectivity techniques.

Strategic Implications for the AI Ecosystem
The exploitation of the Marimo framework serves as a cautionary tale for the broader AI development community. As companies rush to adopt reactive notebooks and low-code AI tools, they are often prioritizing speed and developer experience over rigorous security architecture. This creates a systemic vulnerability where the very platforms intended to accelerate innovation become the weakest links in the enterprise security posture.
The reliance on platforms like Hugging Face, while essential for the collaborative nature of modern AI, introduces a "third-party trust" problem. If developers assume that all assets hosted on a reputable platform are inherently safe, they neglect the necessary security hygiene—such as sandboxing, network egress filtering, and robust identity management—required to protect their infrastructure. The incident involving Marimo proves that attackers are watching these platforms closely, waiting for any sign of a vulnerability that can be exploited to reach the backend services connected to them.
Expert-Level Defensive Strategies
For security operations center (SOC) teams and infrastructure engineers, the lessons from these attacks are clear. First, the dependency on reactive notebooks must be met with strict access control. The /terminal/ws endpoint, which has been identified as a primary vector in this Marimo vulnerability, should be shielded from external exposure. If an application requires public access, it must be gated behind robust authentication and VPNs rather than exposed directly to the public internet.
Second, the industry must move toward a "Zero Trust" model for internal development tools. This includes implementing egress filtering that prevents servers from reaching out to unauthorized domains—even those that appear reputable. In this scenario, if an internal server is compromised, its inability to "phone home" to a malicious Hugging Face space would have halted the download of the kagent binary, effectively neutralizing the attack before it could establish persistence.
Furthermore, monitoring for unusual behavior in developer environments is critical. Security teams should look for "living-off-the-land" techniques, such as the use of curl or wget within non-standard service containers, or the appearance of unrecognized processes disguised as system agents. Behavioral analysis is increasingly the only way to detect threats that leverage legitimate infrastructure to conduct malicious operations.
Looking Toward the Future
The convergence of AI development platforms and advanced malware techniques is a harbinger of future cyber-threat trends. We are likely to see an increase in "infrastructure-as-a-weapon" attacks, where attackers exploit the inherent trust placed in development ecosystems to deploy persistent threats. As AI becomes more deeply embedded in corporate workflows, the surfaces for such attacks will only expand.
Looking ahead, the onus is on both the platform maintainers and the end-users. Framework maintainers must prioritize security-by-design, ensuring that endpoints are secure by default and that updates can be deployed rapidly. Simultaneously, organizations must treat their AI development infrastructure with the same level of security rigor applied to their core production environments. The era of assuming that development tools are "safe" is over; in an environment where even the most trusted platforms can be subverted, constant vigilance and proactive threat hunting are the only viable defenses.
The Marimo incident is a wake-up call. It demonstrates that as the technical landscape becomes more sophisticated, so too do the methods of intrusion. By understanding the interplay between the underlying vulnerability, the abuse of trusted hosting platforms, and the stealthy nature of blockchain-driven malware, organizations can better prepare themselves to defend against the next wave of sophisticated cyber-attacks. The transition to version 0.23.0 for Marimo users is the immediate tactical requirement, but the long-term solution lies in a fundamental shift toward robust, skeptical, and layered security architecture across the entire software development lifecycle.

