The integrity of software distribution channels has once again been called into question following a sophisticated security breach involving the CPUID project. Attackers successfully leveraged a compromised API to manipulate the download delivery mechanism on the project’s official website, effectively turning a trusted repository into a delivery vector for malicious executables. This incident highlights a critical vulnerability in how developers manage third-party integrations and infrastructure, even when their primary software binaries remain cryptographically intact.
The Anatomy of the Compromise
The breach, which occurred between April 9 and April 10, targeted the delivery infrastructure rather than the software source code itself. During a six-hour window, visitors attempting to download industry-standard hardware monitoring tools, such as CPU-Z and HWMonitor, were inadvertently redirected to malicious payloads hosted on external storage services like Cloudflare R2.
What made this attack particularly insidious was the inclusion of legitimate, digitally signed executables within the downloaded packages. These were paired with a malicious Dynamic Link Library (DLL) file—specifically named CRYPTBASE.dll—which facilitated a technique known as DLL sideloading. By placing this rogue library in the same directory as the legitimate application, the attackers ensured that when a user launched the monitoring tool, the system would inadvertently execute the malicious code first. This method is highly effective at bypassing basic signature-based antivirus detection because it relies on the trusted status of the accompanying signed binary.
Advanced Malware Characteristics
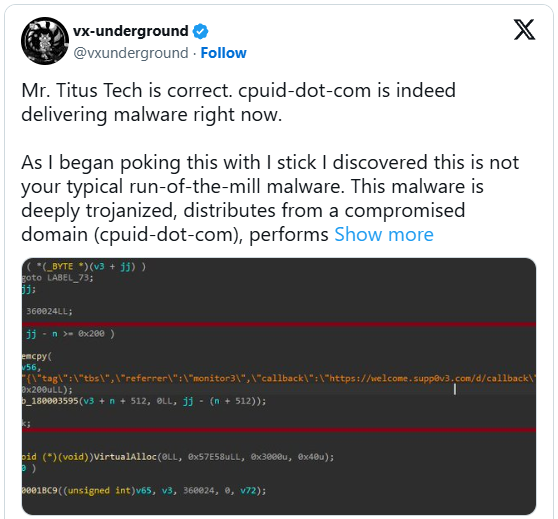
Security researchers and threat hunters who analyzed the incident have noted that this was not a generic opportunistic attack. The malicious payload, identified in subsequent investigations as the STX RAT (Remote Access Trojan), represents a sophisticated piece of spyware designed for long-term persistence and data exfiltration.
The malware employs several advanced techniques to maintain a low profile. It utilizes an Inno Setup wrapper with a Russian-language installer, which serves as a red flag for observant users but may appear mundane to others. Once executed, the malware performs a series of "anti-sandbox" checks. These routines are designed to determine if the code is running within a virtualized or controlled environment—common in automated malware analysis labs. If the malware detects it is being watched, it remains dormant. If it determines the environment is a legitimate user machine, it proceeds to establish a Command and Control (C2) connection to exfiltrate system data and potentially deploy additional modules.
Furthermore, the malware operates primarily in-memory, a tactic aimed at evading Endpoint Detection and Response (EDR) systems that monitor disk-based activity. By proxying Windows NTDLL functionality through a .NET assembly, the threat actors successfully masked their interactions with the operating system, making the infection difficult to trace even for advanced security software.
The Broader Implications for Software Supply Chains
This incident is a textbook example of the "Software Supply Chain Attack" phenomenon, which has become a preferred strategy for advanced persistent threat (APT) actors and cybercriminals alike. Because utilities like CPU-Z and HWMonitor are ubiquitous in technical circles—used by everyone from casual overclockers to enterprise IT administrators—they represent high-value targets.

By compromising the distribution platform rather than the software build server, the attackers avoided triggering integrity alarms that would have occurred if the primary executable had been modified. This approach exploits the inherent trust that users place in official developer websites. Even when a company follows best practices by signing their binaries, they remain vulnerable if their secondary APIs or content delivery networks (CDNs) are not subjected to the same rigorous security posture.
Industry analysts suggest that this campaign is linked to previous operations, including a similar attack against the popular FileZilla FTP client. The consistency in C2 infrastructure and the nature of the payloads suggest a coordinated effort to target "infrastructure software"—tools that are installed on virtually every development and administrative machine globally. The geographic distribution of the victims, spanning from Brazil and Russia to China, confirms that the threat actors are casting a wide net across diverse sectors, including manufacturing, telecommunications, and high-stakes consulting.
Strengthening Defense Against Distribution Poisoning
For organizations, this incident serves as a stark reminder that traditional perimeter security is insufficient. When an official, trusted website is compromised, standard firewall and reputation-based filtering often fail to block the download.
To mitigate the risks of future supply chain attacks, security professionals are increasingly recommending the following practices:
- Hash Verification: Always compare the hash (SHA-256) of downloaded files against the values provided on the official, verified developer documentation pages. If a mismatch is detected, the binary should never be executed.
- Network Behavioral Analysis: Because modern malware like the STX RAT requires communication with a C2 server, monitoring for anomalous outbound traffic—especially to unclassified or newly registered domains—is critical.
- Application Control: Implementing strict application whitelisting and monitoring for unusual DLL loading behaviors can prevent sideloading attacks from succeeding, even if the primary binary is signed.
- Sandboxed Installations: For high-security environments, testing software in an isolated sandbox before deploying it to production workstations is an essential layer of defense.
Future Trends and Outlook
The focus on "utility-grade" software by threat actors is a trend that is expected to escalate. As developers move toward more complex, API-driven websites and integrated cloud distribution, the attack surface grows significantly. The fact that the breach occurred while the primary developer was away on holiday underscores the vulnerability of small, independent projects that lack 24/7 security operations centers (SOCs) or automated integrity monitoring.
Moving forward, we are likely to see a shift toward "Zero Trust" software consumption. This involves treating every download—even from reputable sources—as potentially compromised until verified. Vendors will be under increasing pressure to implement more robust API security, multi-factor authentication for administrative accounts managing download portals, and automated integrity scanning for every file served through their platforms.
While the CPUID team successfully resolved the issue and restored the integrity of their distribution channels, the damage to user trust is significant. The incident serves as a wake-up call for the entire software development ecosystem: the security of the binary is only half the battle; the security of the delivery pipe is equally, if not more, critical. As we look toward the remainder of the year, the industry must prioritize end-to-end supply chain visibility to ensure that the tools designed to monitor system health do not become the very instruments that jeopardize it.