The digital security apparatus surrounding a key figure in U.S. federal law enforcement has been unexpectedly penetrated, as the Iranian-linked threat group known as Handala successfully breached the personal email account belonging to FBI Director Kash Patel. The group claimed responsibility for the intrusion, which resulted in the exfiltration and subsequent publication of personal photographs and non-governmental documents, injecting a highly personal dimension into the ongoing geopolitical cyber conflict between Iran and the United States.
Following the assertion of the breach, the Federal Bureau of Investigation (FBI) issued a public confirmation regarding the compromise. Crucially, the agency sought to immediately de-escalate concerns regarding national security implications, explicitly stating that the exposed data was dated and contained no classified or official government information. This distinction is vital, as the successful exfiltration of sensitive government data would represent an entirely different tier of national security crisis.
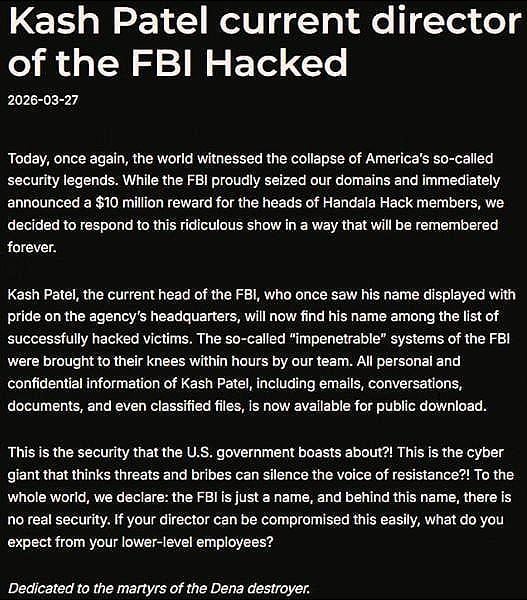
The Handala collective announced its successful operation on one of its affiliated online platforms, framing the attack as a direct act of retaliation. The group asserted that they had defeated what they mockingly referred to as the "so-called ‘impenetrable’ systems of the FBI" in a matter of mere hours. This bold declaration served as a direct challenge to U.S. cybersecurity capabilities.
The motivation for this specific targeting stems from recent, aggressive actions taken by U.S. authorities against the Handala network. The hackers explicitly cited the recent seizure of Handala’s domain infrastructure by the FBI—an action that followed a significant cyber incident targeting the medical technology firm Stryker. Furthermore, the group cited the Department of State’s offering of a substantial reward, potentially reaching $10 million, for actionable intelligence leading to the identification and apprehension of the group’s members. This established a clear tit-for-tat dynamic: a crackdown by U.S. agencies met with a targeted, albeit personal, counter-strike.
Despite the Handala group’s inflammatory rhetoric suggesting they had accessed deep recesses of FBI operational data, the confirmed breach targeted the Director’s private, non-official Gmail account. The hackers, however, disseminated material claiming otherwise. Their initial announcement boasted that "All personal and confidential information of Kash Patel, including emails, conversations, documents, and even classified files, is now available for public download."
Shortly after this claim, the threat actor released a selection of the stolen materials as proof of concept. These materials included watermarked personal photographs and fragments of email correspondence predating Patel’s assumption of his current role as FBI Director. The release strategically focused on material designed to embarrass or compromise the individual rather than immediately expose state secrets, aligning with the characteristics often seen in state-sponsored hacktivism designed for psychological effect.
In a formal response provided to this publication, the FBI acknowledged awareness of the malicious actors attempting to access Director Patel’s private electronic correspondence. The agency affirmed that standard operating procedures were immediately enacted to contain and mitigate any potential fallout. The official FBI statement underscored the nature of the compromise: "The FBI is aware of malicious actors targeting Director Patel’s personal email information, and we have taken all necessary steps to mitigate potential risks associated with this activity. The information in question is historical in nature and involves no government information."
Contextualizing the Handala Threat Actor
To fully appreciate the implications of this incident, it is essential to understand the Handala group’s profile. Operating under various monikers including Handala Hack, Hatef, and Hamsa, this entity emerged onto the global cybersecurity stage in late 2023. Security analysts widely categorize Handala not merely as independent hacktivists, but as a persona utilized by actors working in alignment with, or under the direction of, Iran’s Ministry of Intelligence and Security (MOIS). Their operational tempo suggests state-level backing, despite the veneer of decentralized activism.
Handala’s previous high-profile actions have established a pattern of disruption rather than pure espionage. Prior to targeting the FBI Director’s personal sphere, the group executed a highly damaging attack against the Microsoft enterprise environment of Stryker, a prominent medical technology conglomerate. That incident resulted in the catastrophic erasure of nearly 80,000 devices, demonstrating significant destructive capability and operational reach across critical infrastructure sectors.
The FBI’s statement concluded by reinforcing the U.S. government’s commitment to dismantling the group, reiterating the standing $10 million reward offered through the Department of State’s Rewards for Justice program for information leading to the identification of the Handala Hack Team operating out of Iran. This public linkage of the personal breach incident with an ongoing international manhunt emphasizes the U.S. government’s view of Handala as a serious, state-backed threat actor, irrespective of the content of the most recent leak.
Industry Implications: The Erosion of Personal and Professional Boundaries
This incident serves as a stark, high-profile illustration of a pervasive trend in modern cyber conflict: the deliberate blurring of lines between an official’s personal digital footprint and their professional duties. For cybersecurity professionals, this attack highlights several critical industry implications that extend far beyond the immediate fallout for Director Patel.
Firstly, the success of Handala in compromising an email account associated with a Director-level official at the FBI—even if personal—sends a potent message about the continued vulnerability of individuals, regardless of their affiliation with top-tier security organizations. It underscores that sophisticated nation-state actors are willing to dedicate resources to low-hanging fruit, such as personal accounts often secured with weaker multi-factor authentication (MFA) or less rigorous password hygiene than official government accounts.
Secondly, the exploit likely serves as a crucial piece of intelligence gathering, even if the immediate data release was non-classified. Personal emails often contain correspondence with colleagues, contacts, or even unencrypted discussions about professional matters that may reveal vulnerabilities, timelines, or relationships that can be leveraged in future, more sophisticated attacks. This is the classic "spear-phishing prelude"—using personal compromise to map the social network and potential entry points into secure government systems.
Thirdly, the incident forces a critical re-evaluation of executive digital hygiene policies across government and C-suites globally. While agencies have robust protocols for official devices and networks, the "off-the-clock" digital life of high-value targets remains a significant blind spot. The attack demonstrates that the human element, particularly in private life, is often the weakest link in an otherwise hardened security posture. Industry experts have long warned that employees using the same personal credentials or reusing security questions across both professional and private platforms create an unacceptable risk vector.
Expert-Level Analysis: Exploitation Tactics and Attribution Challenges
From a technical analysis perspective, the Handala group’s successful breach of a major personal email provider (like Gmail, as suggested by the context) points toward common, yet persistent, vulnerabilities. Given the speed of the alleged compromise, tactics likely centered on credential stuffing attacks utilizing previously exposed data dumps from unrelated breaches, or sophisticated social engineering that bypassed MFA protections.
Attribution, while strongly leaning toward Iranian state influence due to the group’s documented history and alignment with MOIS objectives, remains complex in the cyber domain. However, the specific timing—directly following U.S. enforcement actions—strongly suggests state-sanctioned retribution rather than purely opportunistic hacktivism. The primary objective here appears to be strategic messaging and degradation of morale, rather than kinetic espionage. By targeting a visible FBI leader personally, the message is amplified: "We can reach you where you feel safest."
The FBI’s response, confirming the breach but downplaying the data sensitivity, is standard operational procedure designed to prevent adversaries from gaining undue psychological leverage or signaling panic. However, the very confirmation validates the adversary’s capability, creating a complex dilemma for security leadership: acknowledge the operational reality or risk appearing either incompetent or dishonest.
A key analytical point is the group’s use of "classified files" in their claims, even if later refuted by the FBI. This is a calculated disinformation tactic designed to maximize media sensationalism and sow distrust, forcing targets to spend resources verifying claims that may be entirely fabricated. This falls squarely within the definition of psychological operations (PsyOps) often employed by state-backed actors.
Future Impact and Evolving Cybersecurity Trends
The fallout from this incident will likely accelerate several evolving trends within cybersecurity governance, particularly concerning government personnel security:
1. Mandatory Separation of Digital Identities: There will likely be increased pressure, if not mandates, for senior government officials to maintain completely separate, highly secured digital identities for personal use, potentially requiring the use of specialized, government-vetted personal email services or stricter MFA enforcement across all personal accounts linked to professional profiles.
2. Enhanced Personal Digital Vetting: The vetting processes for high-ranking officials may need to expand beyond financial and criminal history to include more rigorous assessments of personal digital hygiene, including the security posture of linked personal devices and cloud storage accounts.
3. The Rise of Retaliatory Hacktivism: As U.S. and allied nations increase their proactive disruption of foreign malicious infrastructure (like seizing domains), state-sponsored groups like Handala will likely pivot further toward highly visible, retaliatory, and personal attacks against officials. This shifts the conflict zone from enterprise infrastructure to the private lives of decision-makers, raising questions about jurisdiction and acceptable international norms of engagement.
4. Focus on Supply Chain for Personal Use: If the compromise originated from a third-party application or service connected to the Director’s personal Gmail, this opens a new area of scrutiny in the cyber supply chain—not just for corporate vendors, but for personal productivity and communication tools used by personnel with security clearances or high-level access.
Ultimately, the Handala breach of Director Patel’s personal email inbox, while confirmed by the FBI to be limited in official scope, is a significant strategic event. It demonstrates the persistent, adaptive threat posed by Iranian-aligned actors and serves as a critical case study in the modern vulnerability landscape where personal digital security can become an unexpected front in geopolitical cyber warfare. The successful extraction of any data, coupled with the public relations victory of claiming a high-value target, fuels the group’s legitimacy and operational funding, making the $10 million reward an increasingly necessary measure to neutralize this escalating threat vector.