The ongoing battle for digital sovereignty and user trust in the internet ecosystem has reached a new inflection point with the deployment of Firefox version 149, an update that sees Mozilla integrating a significant new privacy utility directly into its flagship browser. This move marks a strategic pivot, offering users a permanently free, though capped, Virtual Private Network (VPN) service accessible with a standard Mozilla account. This development is not merely a feature addition; it represents a deliberate attempt by Mozilla to democratize basic VPN functionality, positioning it as an essential, baseline component of modern web browsing, rather than an optional, often costly, subscription service.
The core innovation lies in the scope of this new utility. Unlike the company’s existing, comprehensive commercial offering, Mozilla VPN, which secures all network traffic originating from the operating system, the new built-in tool is strictly siloed to the browser environment. It functions as a secure proxy, routing only the data flowing through the Firefox application itself. This distinction is critical for understanding its intended use case: immediate, on-the-fly protection for browsing activities, particularly when facing the inherent security risks of unsecured networks.
In articulating the rationale behind this feature, Mozilla emphasized its utility in scenarios where transactional privacy is paramount. Whether an individual is utilizing insecure public Wi-Fi hotspots in transit, engaging in sensitive research concerning personal health records, or conducting confidential financial transactions online, the browser-embedded VPN offers an immediate layer of obfuscation. By signing in and toggling the service, users effectively mask their physical location and underlying IP address, rerouting their connection through Mozilla’s secure infrastructure. This immediate shield against passive monitoring is a direct response to the escalating public awareness regarding ISP tracking and sophisticated network-level surveillance.
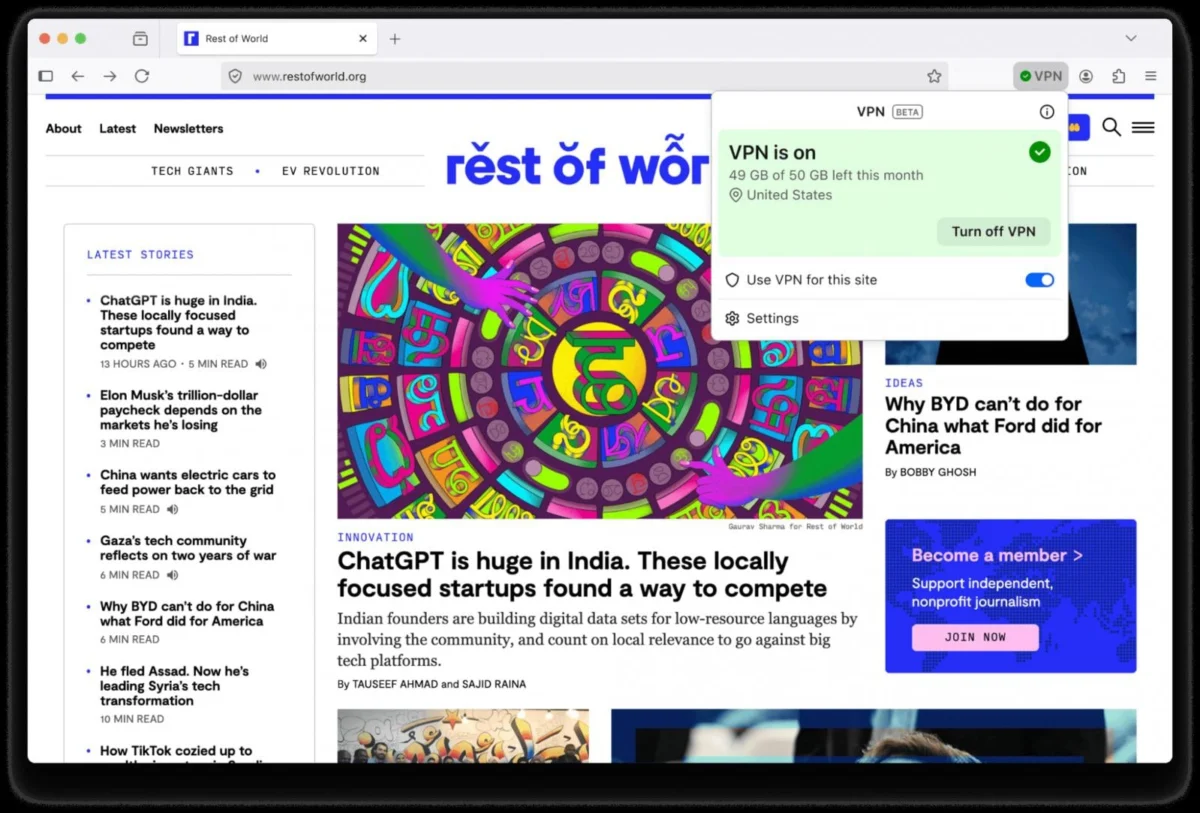
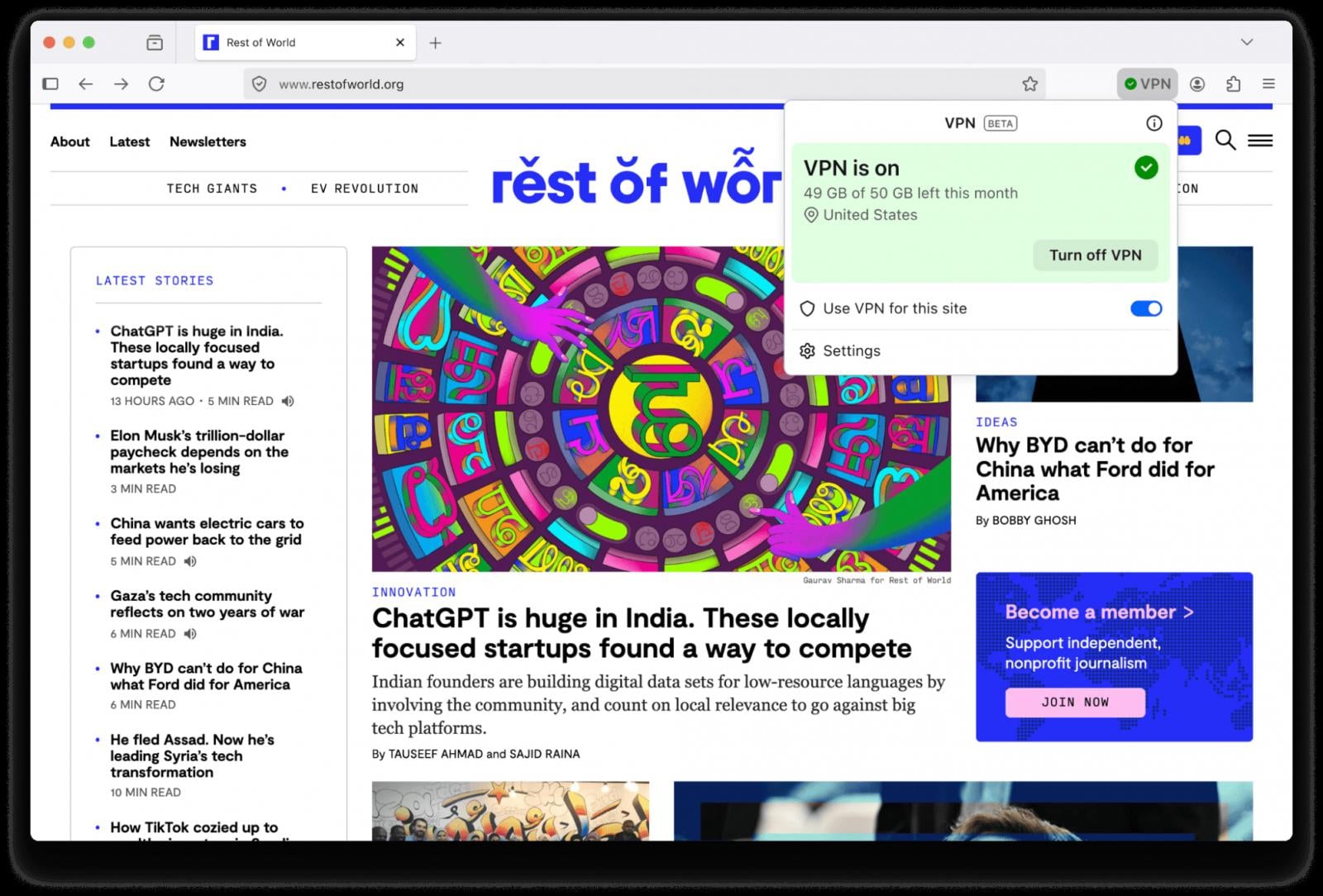
The allocation mechanism for this new service centers on user authentication. Individuals utilizing a registered Mozilla account gain access to a monthly allowance of 50 gigabytes (GB) of data traffic. To manage expectations and prevent unexpected data consumption, the browser incorporates proactive in-app notifications that alert users as they near this specified threshold. This cap, while generous for general browsing, suggests the service is engineered more for enhanced privacy during focused sessions rather than continuous, high-bandwidth activities like heavy streaming or large file transfers, which are typically the domain of fully featured, paid VPN services.

From an operational standpoint, accessibility has been prioritized. The VPN feature is activated via a straightforward toggle situated in the upper-right quadrant of the browser interface, ensuring high visibility and ease of use, a hallmark of Mozilla’s user-centric design philosophy. Furthermore, a nuanced traffic management option allows users to conserve their 50GB allowance by selectively routing only the traffic from up to five specified websites through the encrypted tunnel. This fine-grained control acknowledges that not all web interactions require the same level of anonymity.
However, the implementation includes necessary technical exemptions. To maintain operational integrity and prevent common connectivity issues associated with VPNs—such as authentication failures for services requiring specific geographic validation or complications with persistent log-in sessions—certain essential websites and services are explicitly excluded from the VPN routing pipeline. This pragmatic exclusion balances maximum privacy with necessary usability, a trade-off often required in complex network security implementations.
Mozilla’s data governance policy for this specific browser-level VPN is transparent regarding its necessity for service maintenance. The organization commits to collecting only minimal technical telemetry required to ensure the performance, stability, and reliability of the new service. This includes logging success or failure rates of connection attempts and tracking aggregate data consumption over daily periods. Crucially, this contrasts sharply with the more invasive data collection practices sometimes associated with "free" services, reinforcing Mozilla’s core mission-driven commitment to user privacy over monetization through data brokerage.
Geographically, the rollout is currently phased. As of this announcement, the built-in VPN capability is being deployed incrementally to users situated in the United States, the United Kingdom, Germany, and France. There is, at present, no publicly confirmed schedule for extending this feature set to additional jurisdictions, indicating a controlled testing and scaling approach before broader global availability.
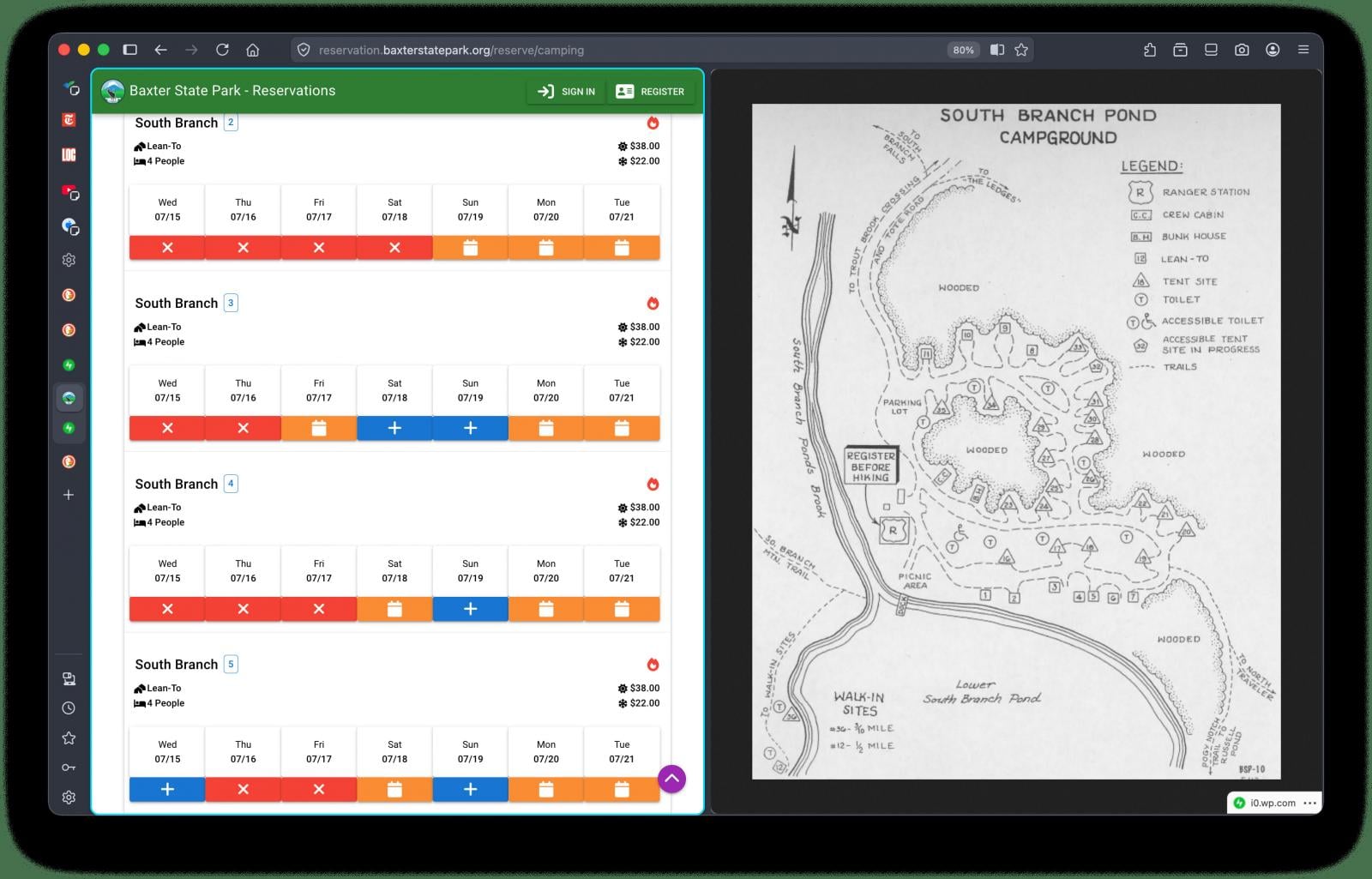
Beyond the significant VPN integration, Firefox 149 introduces other notable feature enhancements aimed at improving productivity. Chief among these is the long-anticipated Split View functionality. This feature, which has seen widespread adoption in competing Chromium-based browsers for some time, enables users to partition the browser window vertically, displaying two separate web pages side-by-side simultaneously. Mozilla champions this feature for workflows that necessitate comparison, planning, or simultaneous data entry—such as cross-referencing research materials, managing complex administrative forms like tax filing, or facilitating multi-source note-taking without constantly toggling between full-screen tabs.
Security posture also receives a mandated upgrade. Firefox 149 now employs an automated defense mechanism that actively blocks incoming notification requests and instantly revokes existing permissions granted to any website identified as malicious by the robust Safe Browsing security system. This preemptive action reduces the attack surface presented by compromised sites that frequently exploit notification permissions to push persistent, intrusive, or malicious alerts to users.
Finally, the release is accompanied by essential foundational maintenance. Version 149 addresses a substantial number of security vulnerabilities, cataloged in the associated security advisories. The comprehensive list details 46 distinct issues, with a significant portion—more than half—classified under high or critical severity ratings. The technical nature of these fixes points to core stability improvements, targeting memory management errors such as user-after-free flaws, boundary condition errors like out-of-bounds access, vulnerabilities within the Just-In-Time (JIT) JavaScript engine, and critical sandbox escape mechanisms. Patching these deep-seated issues is paramount for maintaining the integrity of the browser as a secure application environment.
Industry Implications: The Commoditization of Baseline Privacy
Mozilla’s introduction of a free, high-limit browser VPN fundamentally alters the competitive landscape for privacy tools. Historically, VPNs operated within a distinct market segment, characterized by subscription models predicated on system-wide encryption. By embedding a capable, zero-cost alternative directly into the browser—the primary gateway to the modern internet—Mozilla is effectively commoditizing baseline IP masking.
This action pressures existing standalone VPN providers, particularly those targeting casual users or those seeking only browser-level security. If millions of Firefox users find the 50GB monthly allowance sufficient for their daily needs, the perceived necessity of purchasing a separate, entry-level VPN subscription diminishes considerably. This forces established commercial VPN players to pivot toward emphasizing their premium features: system-wide protection, faster speeds, larger data allowances, advanced tunneling protocols, and jurisdiction-specific server infrastructure that caters to regulatory or corporate compliance needs.
For the broader tech industry, this move underscores the growing consumer expectation that essential security and privacy features should be integrated by default, rather than bolted on as afterthoughts or sold separately. We are witnessing a trend where foundational security tools—like ad-blocking (which Firefox has long championed) and now basic encryption—are becoming expected features of any leading software platform. This development aligns with Mozilla’s long-standing mission to keep the internet open and accessible, viewing privacy as a right, not a premium add-on.
Expert Analysis: Architectural Trade-offs and Trust Models
From an architectural standpoint, the distinction between browser-scoped and system-scoped VPNs is crucial. A browser-only proxy is inherently simpler to implement and maintain because it only needs to intercept and manage HTTP/HTTPS traffic originating from the Firefox process. This simplicity contributes to lower overhead and easier maintenance of the data caps. However, this also means that other applications on the device—email clients, gaming platforms, background synchronization services, or system updates—will continue to use the user’s unmasked, true IP address. This limitation defines the service’s scope: it protects what you are browsing within Firefox, but not that you are browsing, or what other network activity is occurring.
The reliance on a Mozilla account for activation is a deliberate strategic choice, balancing user convenience with data accountability. By tethering the service to a Mozilla ID, the organization establishes a transparent trust relationship. The commitment to logging only performance metrics (connection success/failure, data volume used) rather than browsing content or specific destination sites is a critical differentiator. Security analysts will closely monitor the geographical location of the routing servers (currently U.S.-based) and Mozilla’s adherence to its stated minimal data retention policies, as this forms the bedrock of user trust in this "free" offering. A free service that collects no meaningful user data is vastly superior, in privacy terms, to a paid service with opaque logging practices.
Future Impact and Emerging Trends
The rollout of the integrated VPN is likely to accelerate the feature parity arms race among major browser developers. While Chrome has focused heavily on sandboxing and resource management, features like Split View suggest a greater acknowledgment of desktop productivity use cases. Mozilla’s aggressive pursuit of integrated security tools places competitive pressure on Google to enhance its own built-in privacy offerings, potentially leading to further democratization of security features across the browser market.
Furthermore, this move may influence how users perceive and interact with digital boundaries. As basic encryption becomes ubiquitous within the browser, the next frontier will likely involve more granular, application-specific controls over data exposure, perhaps extending beyond simple IP masking to include advanced fingerprinting resistance or automatic protocol negotiation based on the sensitivity of the accessed domain.
The success of Firefox 149’s VPN will ultimately be judged on its stability during the initial rollout phase in key markets (US, UK, DE, FR) and its ability to scale without compromising the promised data minimization commitment. If Mozilla can maintain performance and trust while managing the infrastructure costs of 50GB allowances for a large user base, it sets a powerful precedent for how non-profit technology stewards can successfully integrate critical digital infrastructure tools directly into consumer applications. The inclusion of significant security patches alongside these functional upgrades solidifies the narrative: Firefox 149 is not just an update; it is a statement reinforcing the browser’s role as the primary defense perimeter for the modern internet user.