The Federal Bureau of Investigation (FBI) has publicly confirmed a significant escalation in cyber espionage activities, directly attributing ongoing, large-scale phishing campaigns against users of encrypted communication applications—notably Signal and WhatsApp—to Russian intelligence services. This official attribution marks a critical shift from generalized warnings about state-sponsored hacking to specific identification of the perpetrators behind sophisticated account takeover operations that have already compromised thousands of high-value targets globally.
The core mechanism of these attacks, as detailed in the agency’s recent Public Service Announcement (PSA), involves a strategic circumvention of end-to-end encryption (E2EE) not by cryptanalytic breakthrough, but through social engineering and account hijacking. This distinction is paramount: the security integrity of the underlying cryptographic protocols remains intact, yet the user’s session—the trusted endpoint—is compromised. The threat actors are exploiting the human element and the device linking features inherent in many commercial messaging applications (CMAs).
While the tactics appear versatile enough for deployment across various CMAs, intelligence suggests a pronounced focus on Signal users. Once control is established over an account, the adversaries gain access to a treasure trove of sensitive data, including complete message histories, contact lists, and the ability to impersonate the victim. This compromised identity can then be leveraged to launch subsequent, highly convincing phishing attacks against the victim’s network, effectively turning a compromised user into an unwitting distribution node for further compromise.
The scale of the operation is significant, with the FBI confirming that "thousands" of accounts have fallen victim worldwide. Critically, the targeting profile is sharply focused on individuals possessing high-value intelligence relevance. This includes current and former U.S. government officials, active military personnel, key political figures, and investigative journalists. This specific targeting profile strongly reinforces the assessment that these are state-directed intelligence collection efforts, rather than opportunistic criminal endeavors.
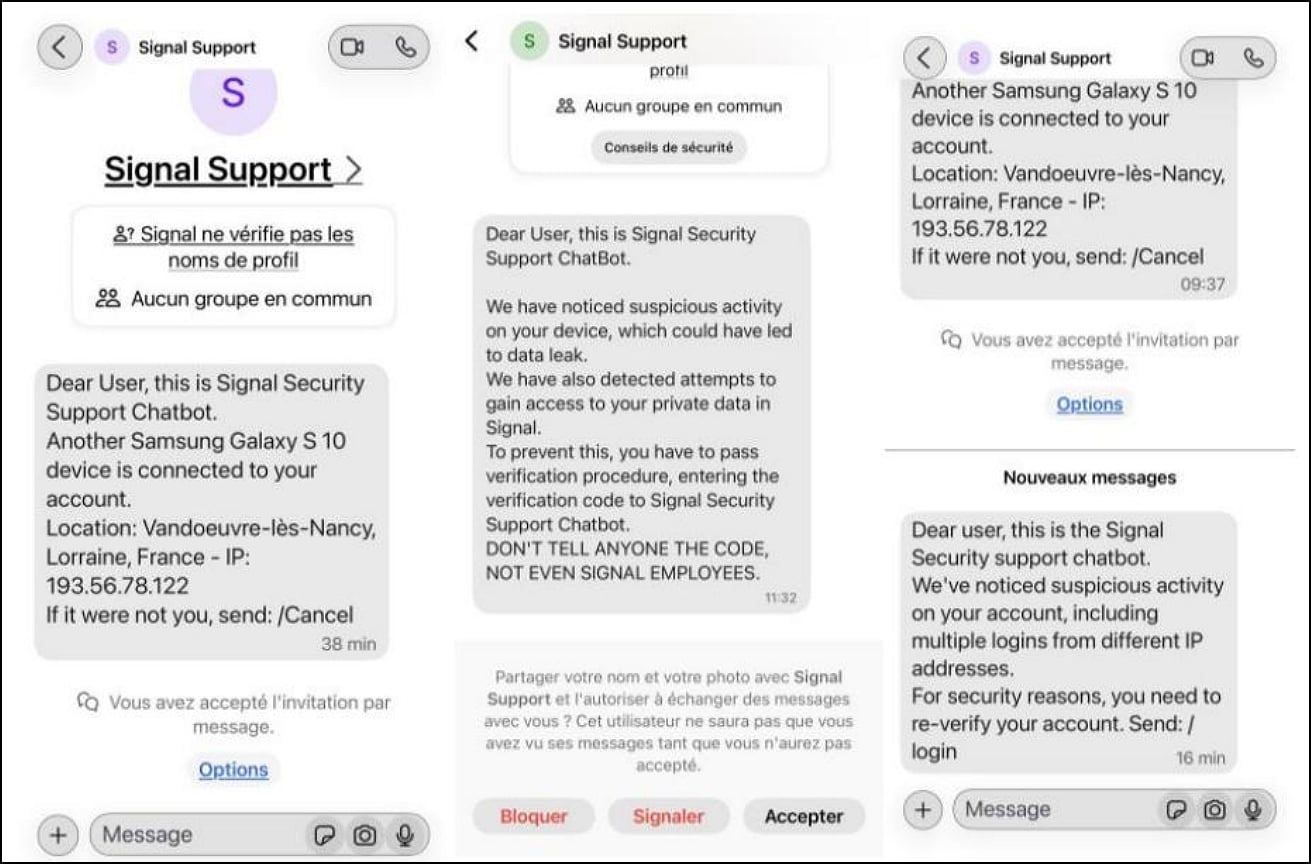
This American confirmation follows a pattern established by allied intelligence agencies. Earlier in the month, Dutch cybersecurity authorities issued stern warnings regarding state-backed actors employing identical account-hijacking methodologies against Signal and WhatsApp users attempting to secure their communications. The Dutch advisory specifically pointed to the manipulation tactics designed to trick users into authorizing the addition of attacker-controlled devices to their legitimate accounts. Shortly thereafter, France’s Cyber Crisis Coordination Center (C4) corroborated these findings, issuing its own alert detailing the widespread and persistent nature of these tactics across multiple European jurisdictions. The synchronization of these international alerts underscores the coordinated nature of the threat landscape.

Deconstructing the Evasion Strategy: Bypassing Encryption Through Endpoint Compromise
The common thread uniting the advisories from the FBI, the Dutch, and C4 is the precise method used to subvert secure messaging: the malicious linking of devices. These phishing campaigns systematically target the established trust mechanisms built into platforms like Signal and WhatsApp, which rely on secure pairing, often via QR code scanning or the manual input of verification codes, to establish a secure channel between a primary device and a secondary one (like a desktop client).
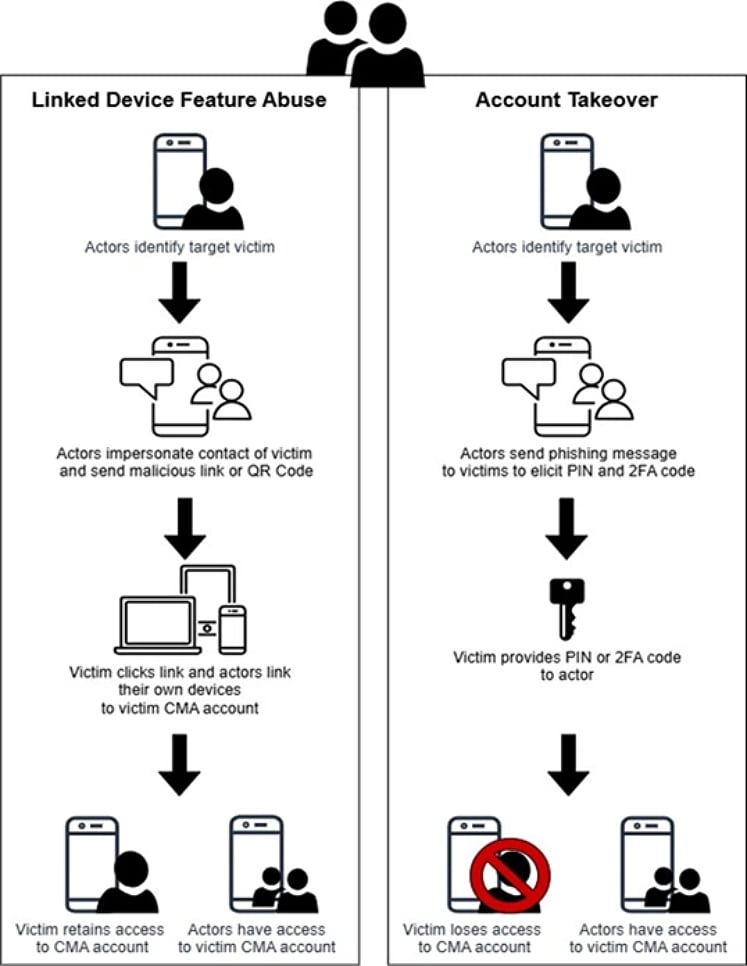
The modus operandi centers on sophisticated impersonation. Threat actors predominantly deploy phishing messages masquerading as official support channels for the messaging application. These fraudulent communications create a manufactured sense of urgency or legitimacy, prompting the target to take an immediate, detrimental action. This action usually involves one of two primary vectors: either divulging a one-time verification code sent during an account setup or registration process, or, more commonly in the case of linked devices, scanning a malicious QR code displayed on the attacker’s screen.
When a user scans an attacker’s QR code, they are effectively telling the application to link the attacker’s device to their authenticated account. Crucially, this process does not require the attacker to know the victim’s password or PIN; it only requires physical or remote access to the victim’s phone long enough to complete the pairing sequence, often under false pretenses. In the context of remote phishing, the attacker orchestrates a scenario where the victim believes they are verifying a login or resolving a supposed security issue, leading them to scan the malicious code presented by the threat actor.
Once a device is linked, the compromise becomes silent and persistent. The attacker can then monitor all incoming and outgoing communications, access group chats, and actively send messages under the guise of the legitimate user. This infiltration capability is exceptionally dangerous because it allows the adversary to engage in "trusted insider" communication, potentially extracting further intelligence from the victim’s contacts or manipulating operational security decisions.
It is vital for technical audiences to internalize the FBI’s explicit clarification: these successful compromises are not evidence of vulnerabilities in Signal’s or WhatsApp’s E2EE implementation. The encryption remains mathematically sound. Instead, the attacks exploit weaknesses in user behavior, platform onboarding procedures, and the established security model that necessitates user confirmation for device pairing.
Industry Implications: The Trust Deficit in Commercial Messaging
The official linkage of these attacks to Russian intelligence elevates the issue from a routine cybersecurity threat to a matter of national security and geopolitical espionage. For organizations that rely on CMAs for sensitive internal or external communications—especially in high-risk sectors like defense contracting, diplomatic services, and critical infrastructure—this incident fundamentally challenges the perceived security baseline of these platforms.
The reliance on E2EE has historically positioned these applications as the gold standard for secure mobile communication, often preferred over traditional SMS or email due to their strong cryptographic guarantees. However, this incident highlights a critical vulnerability in the deployment model: the weakest link in any chain is the interface between the technology and the user. Security architects must now incorporate the potential for CMA account takeover into their threat modeling, recognizing that a platform deemed "unbreakable" cryptographically can still be rendered useless by social engineering.
For platform developers, this raises difficult questions about the friction required for device linking versus security. Signal, for instance, prioritizes user privacy and accessibility, which necessitates an easy way to migrate or link devices. However, the current attack vectors exploit this very ease of linkage. Future security enhancements might need to involve more robust, multi-factor authentication protocols for linking new devices, perhaps requiring biometric verification or a secondary, out-of-band confirmation step that cannot be easily manipulated through the initial phishing lure.
Furthermore, the use of these compromised accounts to launch secondary phishing waves demonstrates a mature, multi-stage operational tempo typical of advanced persistent threat (APT) groups. By using trusted identities, the success rate for subsequent attacks targeting the victim’s associates—who are likely operating under the assumption of security—increases dramatically. This creates a cascading failure risk across organizational networks and personal contact spheres.
Expert Analysis: The Evolution of State-Sponsored Deception
From an intelligence perspective, the operationalization of these messaging platforms by Russian intelligence signifies a strategic pivot. As traditional espionage vectors—such as network intrusion into corporate servers or direct interception of unencrypted traffic—become more difficult due to enhanced organizational defenses, threat actors are shifting focus toward exploiting the trusted communication channels used by their targets for day-to-day coordination.
Security analysts note that this tactic aligns perfectly with established Russian intelligence doctrine: low-cost, high-return operations leveraging social engineering to achieve intelligence objectives without triggering expensive, high-profile defensive reactions associated with traditional malware deployment or zero-day exploitation. Tricking an official into scanning a QR code is significantly cheaper and less traceable than developing and deploying sophisticated malware capable of bypassing modern endpoint detection and response (EDR) systems.
The key to the attackers’ success lies in the "trust inertia." Once a user is convinced they are communicating with Signal or WhatsApp support, the impulse to comply quickly overrides caution. Experts suggest that sophisticated threat actors are likely employing advanced psychological profiling to tailor their phishing lures, exploiting specific organizational protocols or known stress points within targeted agencies or companies to maximize the likelihood of compliance. The impersonation must be flawless, often incorporating near-perfect knowledge of the victim’s context, suggesting a level of preparatory intelligence gathering prior to the final execution phase.
Moreover, the use of these compromised accounts for onward phishing suggests a long-term intelligence goal. It is not merely about stealing current communications; it is about establishing persistent, low-profile listening posts within trusted digital ecosystems. These posts can monitor evolving relationships, identify emerging targets, and potentially exfiltrate data over an extended period, masked by the legitimate traffic flow of the compromised user.
Future Impact and Defensive Trends
The immediate future of secure communication defense will revolve around enhancing user education and demanding greater platform accountability regarding device management. The FBI’s advice to remain suspicious of unexpected messages and never share verification codes is foundational, but in the face of highly targeted attacks, passive education may prove insufficient.
One critical defensive trend emerging is the push for "device health checks" integrated directly into messaging applications. If an application detects an unusual device linking event—perhaps an unsupported operating system or a geographically anomalous location for a new link—it should trigger a mandatory, non-bypassable re-authentication challenge that cannot be satisfied via the initial phishing vector (e.g., requiring a specific PIN entry only known to the original user, not a code sent over SMS).
Furthermore, organizations must mandate the use of multi-device management features that allow administrators or individual users to easily audit and remotely revoke linked devices. If a user suspects compromise, the ability to instantly sever all secondary sessions is paramount to minimizing data exposure.
From an intelligence perspective, expect threat actors to refine their social engineering techniques further, perhaps moving away from overt "support impersonation" toward more subtle, context-specific lures—for example, a message appearing to come from a trusted colleague referencing a recent, real-world event, followed by a request to "check this secure link on my new tablet" (which requires the victim to scan a QR code).
In conclusion, the FBI’s explicit attribution confirms that state-level espionage is actively subverting the user layer of ostensibly secure communication tools. While end-to-end encryption remains a powerful tool against passive interception, this threat landscape underscores that digital security is a holistic challenge, where sophisticated adversary tradecraft exploits the human interface to circumvent even the strongest cryptographic barriers. For high-value targets, the era of absolute trust in a single MFA factor, like a verification code or a single QR scan, must now be considered over.

