In a move underscoring the persistent fragility of critical enterprise infrastructure, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued a formal directive regarding an actively exploited security vulnerability within the Apache ActiveMQ platform. The flaw, officially cataloged as CVE-2026-34197, represents a significant escalation in the risk profile for organizations relying on this widely deployed, Java-based message broker. As the primary backbone for asynchronous communication across thousands of distributed applications, ActiveMQ’s compromise is not merely a localized technical issue but a systemic threat that could facilitate unauthorized remote code execution (RCE) on a massive scale.
The revelation of CVE-2026-34197 is particularly sobering due to its provenance: the vulnerability remained dormant and undetected within the software’s codebase for an staggering 13 years. Its eventual discovery, facilitated by the application of generative AI—specifically the Claude assistant—highlights a dual-edged reality in modern cybersecurity. While AI-driven security research is successfully surfacing deep-seated, legacy vulnerabilities that human auditing might overlook, threat actors are simultaneously leveraging these same technological advancements to automate the weaponization of such flaws. The researcher behind the discovery, Naveen Sunkavally, identified that the core of the issue lies in deficient input validation, a classic vulnerability pattern that, when exploited, grants an attacker the ability to inject and execute arbitrary code.
The Anatomy of the Threat
Apache ActiveMQ facilitates seamless interaction between disparate systems, acting as a traffic controller for data packets. When a message broker is compromised, the security perimeter of the entire application stack is essentially dissolved. By exploiting the improper input validation mechanisms within the broker, authenticated attackers can bypass standard security controls to gain control over the underlying server.
The urgency behind the current advisory is compounded by the ease with which such an exploit can be deployed. Because the architecture of ActiveMQ is well-documented and widely studied, the post-exploitation phase—where attackers pivot to lateral movement, data exfiltration, or the deployment of ransomware—is often swift. Security researchers have noted that the vulnerability is specifically triggered by suspicious broker connections using the brokerConfig=xbean:http:// query parameter combined with the internal VM transport protocol. These markers, while useful for incident response teams, are also the "fingerprints" of an active compromise, making them a high-priority target for automated scanning and exploitation scripts currently circulating among malicious cyber-actor groups.
Industry Implications and the "Legacy Debt" Problem
The existence of a 13-year-old vulnerability within a project as vital as Apache ActiveMQ serves as a stark reminder of the "technical debt" that plagues modern software development. As open-source projects grow in complexity, the challenge of maintaining secure codebases becomes exponentially harder. Legacy components often go unscrutinized for years, with developers focusing on new feature parity rather than rigorous security auditing of foundational elements.
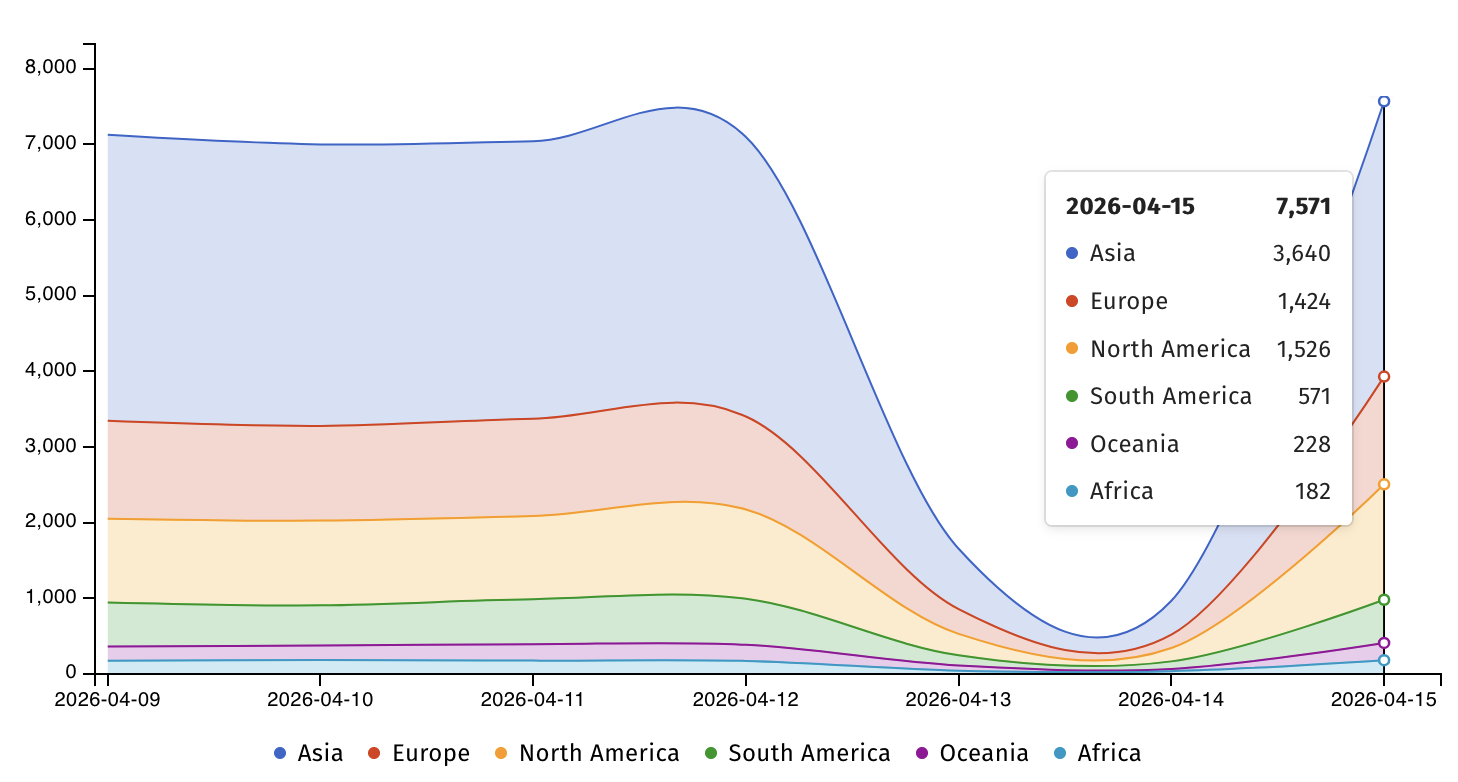
For the industry, this incident necessitates a shift in how we perceive software longevity. Organizations often adopt an "if it isn’t broken, don’t touch it" mentality regarding their server infrastructure. This inertia is exactly what threat actors exploit. When a vulnerability like CVE-2026-34197 is disclosed, the disparity between the sophistication of the attacker and the preparedness of the defender is laid bare. With over 7,500 ActiveMQ instances currently identified as exposed to the public internet, the attack surface is vast. The risk is not limited to federal agencies; it extends to financial institutions, healthcare providers, and logistics firms that rely on the reliability and performance of asynchronous messaging.
Regulatory Pressure and the CISA Mandate
The inclusion of CVE-2026-34197 in CISA’s Known Exploited Vulnerabilities (KEV) Catalog is a formal acknowledgment of the severity of the threat. Under Binding Operational Directive (BOD) 22-01, Federal Civilian Executive Branch (FCEB) agencies are now under a strict legal obligation to patch these vulnerabilities within a two-week window, setting a firm deadline of April 30. This mandate is more than a recommendation; it is an acknowledgment that the federal enterprise is a primary target for sophisticated adversaries who view these vulnerabilities as low-hanging fruit.

However, the ripple effects of this directive reach far beyond government borders. When CISA highlights a vulnerability, it effectively provides a roadmap for non-state actors and cyber-criminal syndicates to focus their efforts on private-sector targets that may be slower to react. The agency’s warning to private-sector defenders to prioritize patching is a necessary call to action, reflecting a reality where the boundary between public and private cybersecurity is porous. If a federal agency is at risk, so is the interconnected ecosystem of vendors, contractors, and partners that rely on that same infrastructure.
Expert Analysis: The Future of Defensive Posture
Moving forward, the industry must transition from reactive patching to a more proactive, context-rich defensive posture. The reliance on manual security assessments is no longer sufficient in an era where software supply chains are increasingly complex and global.
- Autonomous Validation: The rise of tools that can autonomously validate whether a security control is actually effective—or if a patch has been correctly implemented—is a critical development. As highlighted by the recent discourse surrounding autonomous validation, identifying "what is exploitable" is more important than simply counting the number of vulnerabilities. Proving that controls hold under pressure is the next frontier of cybersecurity.
- Hardening Legacy Infrastructure: Organizations must aggressively audit their use of legacy open-source tools. This involves not only patching known flaws but also restricting access to management interfaces, implementing robust network segmentation, and employing zero-trust architectures that assume the message broker itself could be compromised.
- Continuous Monitoring: The "13-year-old bug" narrative should spur organizations to invest in deeper, more continuous log analysis. Relying on perimeter defenses is insufficient when the vulnerability exists within the application logic itself. As recommended by the researchers who discovered this flaw, monitoring for specific query parameters like the
brokerConfig=xbeanstring in logs is a baseline requirement for identifying intrusion attempts.
Looking Ahead
The incident involving CVE-2026-34197 is not an isolated event; it is symptomatic of a broader trend where historical security oversights are being unearthed at an accelerating rate. As we look toward the remainder of the year, we can expect a continued surge in the exploitation of legacy bugs as attackers weaponize AI to mine public repositories and project archives.
The industry’s response to this specific Apache ActiveMQ vulnerability will serve as a bellwether for its ability to handle similar crises in the future. The organizations that thrive will be those that view cybersecurity not as a cost center or a compliance checkbox, but as a core component of their operational architecture. This requires a cultural shift toward transparency, rapid remediation, and an unflinching commitment to identifying and addressing the deep-seated vulnerabilities that reside within the software we often take for granted.
Ultimately, the goal is to reduce the "window of exposure." When a vulnerability is identified, the time between disclosure and universal patching must be compressed. If the industry fails to adapt to the speed at which modern exploits are developed, we will continue to see these cycles of emergency warnings and frantic, last-minute remediation. The security of the digital economy rests on the recognition that every line of code, regardless of how old or how "standard" it is, must be treated as a potential gateway for those who seek to disrupt our critical infrastructure. Patching is only the first step; the final step is a permanent hardening of our digital foundation against the inevitable discovery of the next long-hidden flaw.