The digital advertising ecosystem is currently grappling with a novel and highly evasive phishing operation specifically engineered to compromise accounts managed through TikTok for Business. This targeted assault exploits the perceived legitimacy and high-throughput capabilities inherent in these business-level accounts, which are prime targets for threat actors seeking to propagate malvertising, sophisticated ad fraud schemes, and the wider distribution of illicit or malicious payloads.
This emerging campaign represents an evolution in credential theft, distinguished by its proactive measures to circumvent automated security analysis tools. Researchers tracking the activity have noted parallels with previous, highly effective campaigns that previously focused on compromising infrastructure within major advertising platforms, such as Google Ad Manager. The persistence of threat actors in targeting advertising management systems underscores their value proposition: access to established, high-visibility distribution channels.
TikTok, as a platform, has a documented history of being leveraged for illicit activities, ranging from the propagation of information-stealing malware embedded within seemingly innocuous video content—often facilitated through "clickfix" style attacks—to widespread cryptocurrency scams disguised as high-profile promotional giveaways. The "Business" tier of accounts is particularly attractive because it grants advertisers elevated permissions, increased audience reach, and often benefits from a baseline level of institutional trust that general user accounts might lack, making their compromised assets far more lucrative for bad actors.
Analysis provided by browser threat detection and response specialists reveals the intricate setup underpinning this attack. The campaign’s phishing infrastructure relies on a specific methodology to host its malicious destinations. Victims are reportedly lured into clicking initial links that ultimately resolve to pages hosted on Cloudflare infrastructure. Crucially, the domains associated with these phishing sites were registered recently, specifically on March 24th, utilizing NiceNIC as the registrar. This registrar has drawn repeated scrutiny from the cybersecurity community due to its frequent association with various cybercriminal operations, suggesting a calculated choice by the attackers to leverage known avenues for anonymity and operational longevity.

While the initial vector—the method by which the malicious link is first delivered to the target—remains under investigation, security researchers speculate that the delivery mechanism mirrors advanced techniques previously documented against other major corporate targets. A key characteristic of this operation is the sophisticated redirection chain designed to filter out robotic inspection. The initial interaction involves a redirect through a seemingly legitimate URL associated with Google Storage. This legitimate hop serves as a smokescreen. Following this, the traffic encounters a Cloudflare Turnstile check. This mechanism is designed to differentiate human users from automated security bots by presenting a non-invasive, browser-based challenge that sophisticated scraping tools or security scanners often fail to solve correctly. Only upon successful "human verification" is the traffic passed onward to the final, malicious destination.
The infrastructure supporting the final payload exhibits common hallmarks of modern phishing operations. The domains used in the attack share similar naming conventions, indicating a centralized management structure, and importantly, they are all served from the same underlying Google Storage bucket, suggesting the attackers have consolidated their hosting environment for efficiency and rapid deployment.
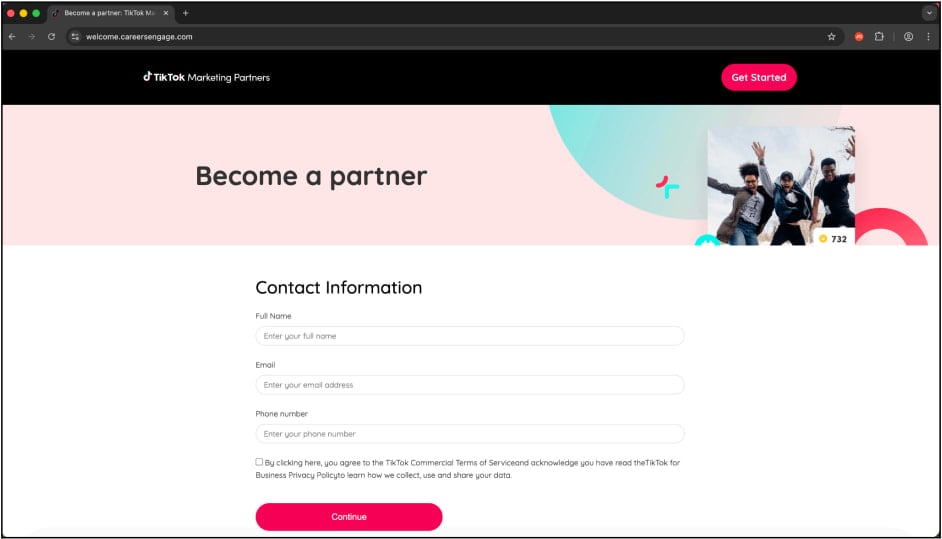
The presentation layer of the attack is meticulously crafted to induce immediate user action, leveraging dual impersonation to maximize potential yield. The malicious pages convincingly mimic both the official TikTok for Business interface and, strikingly, the "Schedule a Call" pages associated with Google Careers. The initial interaction requires the target to input basic identifying information, specifically mandating the use of a business email address. This first step acts as a crucial validation gate; by successfully harvesting a business email, the attacker confirms they are interacting with an employee or administrator who controls valuable digital assets, rather than a casual user.
Following this initial data capture, the operation escalates to credential harvesting. Victims are then presented with a secondary page, a high-fidelity clone of a legitimate login portal. This page is not merely a static form; it functions as a reverse proxy. A reverse proxy acts as an intermediary, relaying requests between the victim’s browser and the legitimate service, while simultaneously capturing all submitted data—including usernames, passwords, and, critically, active session cookies—before forwarding the legitimate credentials to the attacker’s exfiltration server.
The implementation of a reverse proxy is a significant security escalation because it allows the threat actors to bypass common authentication safeguards, including standard Two-Factor Authentication (2FA). Because the proxy relays the login attempt in real-time, if a user enters their password and the corresponding 2FA code (or session token), the proxy captures that authentication information and uses it instantly to establish a session on the real service before the session expires or the user realizes any compromise. This technique effectively "steals the session" in transit.
Furthermore, the reliance on Google Single Sign-On (SSO) by many TikTok for Business account holders introduces a cascading risk. Researchers highlight that if an administrator utilizes their Google credentials to access and manage their TikTok advertising profile, a successful compromise of that intermediary login step via the phishing lure results in a "two-for-one" security breach. The attacker gains control over the Google identity, which then immediately compromises the linked TikTok advertising account, effectively seizing control of both advertising ecosystems simultaneously. This interconnectedness amplifies the strategic value of targeting the SSO pathway.
Industry Implications and Background Context
The targeting of TikTok for Business aligns with a broader industry trend where high-value advertising platforms become focal points for credential theft. In the last several years, digital advertising revenue has become a multi-hundred-billion-dollar global industry. Compromising an active business account allows threat actors to instantly monetize their access through fraudulent ad placements, running sophisticated pay-per-click (PPC) scams, diverting advertising budgets to malicious landing pages (malvertising), or selling the access on darknet forums. For organizations, a compromised ad account can lead to severe reputational damage, significant financial losses from unauthorized spending, and potential regulatory scrutiny depending on the nature of the distributed content.
The use of Cloudflare’s infrastructure, while intended for security and performance, is being weaponized here. Attackers leverage the platform’s robust protection against distributed denial-of-service (DDoS) attacks and its advanced bot management to shield their phishing sites. By routing traffic through Cloudflare Turnstile, the attackers ensure that automated forensic analysis, which often relies on headless browsers or non-interactive scripts to crawl landing pages, is effectively thwarted. This forces human security analysts to manually navigate the complex redirect chain, increasing the time-to-detection dramatically.
Expert Analysis: Evasion and Infrastructure Tactics
This campaign showcases a high degree of technical sophistication, moving beyond rudimentary phishing templates. The employment of a reverse proxy, as opposed to simple credential harvesting forms, indicates an investment in advanced tooling. Reverse proxies require more complex setup but offer superior results, especially against services that mandate modern security protocols like tokenized session management or evolving 2FA methods.
The reliance on Google Storage buckets for hosting infrastructure, even if temporary, is a notable tactic. Cloud providers offer generous free tiers and robust, globally distributed content delivery networks (CDNs). By using these legitimate services as a base layer, the malicious domains inherit a degree of trust and resilience, often flying under the radar of domain-based blocklists until the specific malicious payload is identified.
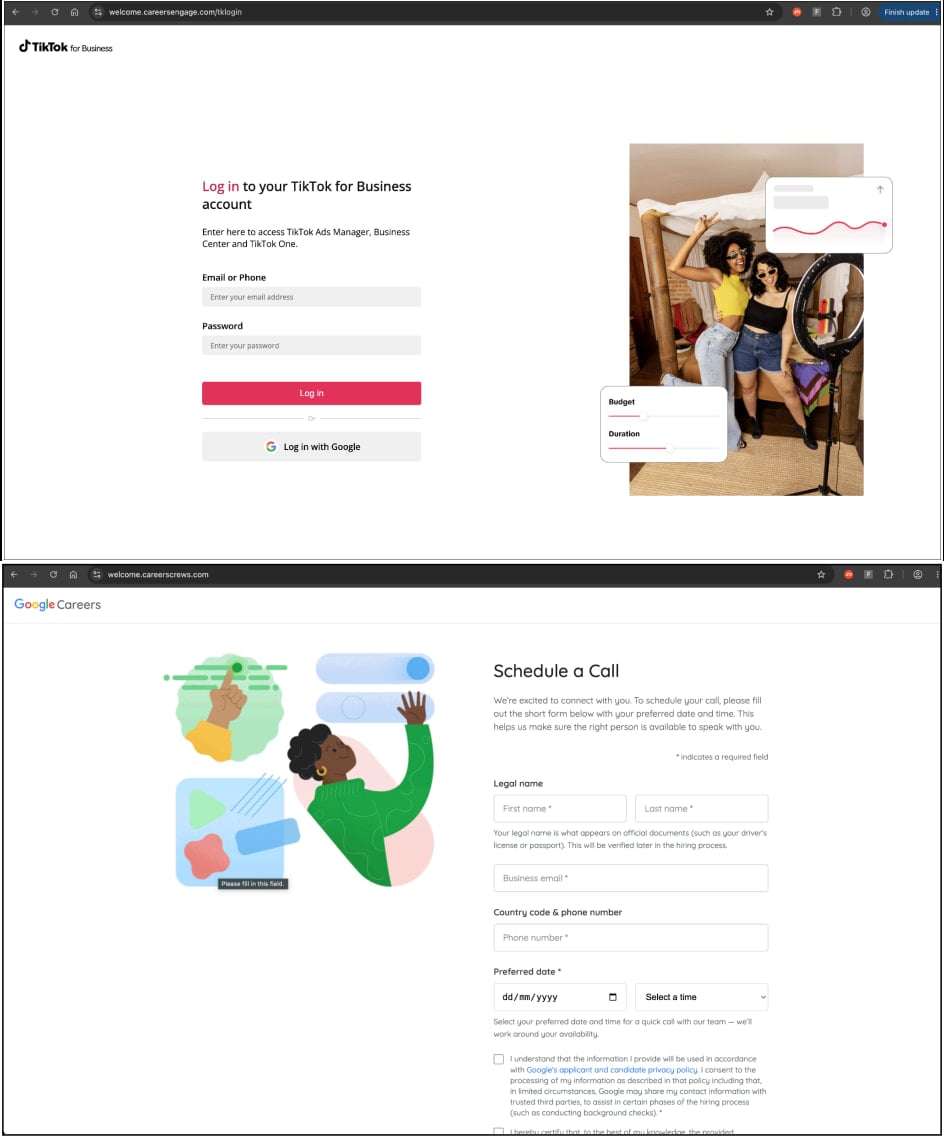
The strategic impersonation of both TikTok Business and Google Careers pages is calculated. The TikTok page targets the immediate administrative function, while the Google Careers page leverages the common professional scenario of job application tracking. Many employees, especially in marketing and tech roles, frequently interact with Google-based scheduling tools for interviews or business meetings, making the lure highly contextual and believable.
Future Impact and Mitigation Trends
The success of this specific evasion technique—using a legitimate redirect, bot challenge, and reverse proxy—will likely influence future phishing toolkits. We can anticipate an increase in similar multi-stage attacks designed to specifically counter browser security extensions and automated security scanners.
For businesses utilizing TikTok for advertising, the implications are clear: traditional perimeter security measures are insufficient. Defense must shift toward identity and access management (IAM) controls that are independent of the login process itself.
Mitigation Strategies Moving Forward:
- Adoption of Passkeys: The most robust countermeasure against session hijacking and credential harvesting remains the widespread adoption of passkeys. Since passkeys rely on platform-specific cryptographic keys rather than shared secrets (passwords), they are inherently immune to reverse proxy attacks that capture static credentials. If an account supports passkeys, users must enable them immediately.
- Strict SSO Monitoring: Organizations leveraging Google SSO for third-party services like TikTok must implement rigorous monitoring on the identity provider (Google Workspace). Any unusual login attempts, geographic anomalies, or rapid session creation following an external click should trigger immediate alerts and temporary account lockouts.
- Domain Verification Discipline: Users must elevate their scrutiny regarding links, especially those delivered outside secure internal communication channels. A fundamental check involves hovering over links to verify the target URL’s domain authority and structure, looking for subtle misspellings or deviations from the known official domains.
- Endpoint Detection and Response (EDR): Enhanced EDR solutions that monitor browser activity for suspicious network connections initiated after a successful login prompt can help identify reverse proxy activity by detecting unexpected outbound traffic associated with a legitimate session.
The continuous evolution of these phishing operations underscores a persistent arms race between threat actors and security providers. As platforms like TikTok expand their commercial footprint, the sophistication applied to breaching these administrative portals will only intensify, demanding a proactive and multi-layered security posture from all business users.

