The contemporary landscape of personal computing increasingly revolves around self-sufficiency, with the proliferation of the home server, or "home lab," as a testament to this trend. Enthusiasts and power users alike leverage these dedicated machines—often running sophisticated open-source stacks like Nextcloud, Plex media servers, or customized automation platforms—to reclaim autonomy from centralized cloud providers. This level of control is intoxicating; the user dictates the hardware specifications, manages the entire software stack via command line interfaces, and controls the encryption parameters. However, this absolute mastery introduces a profound, yet often neglected, administrative burden: ensuring the continuity of this digital empire beyond the administrator’s active participation. This challenge crystallizes into what can be termed the "Digital Legacy Paradox": the more robustly one secures and isolates their data for privacy, the more inaccessible that data becomes to designated beneficiaries should the primary custodian suddenly vanish.
This sobering realization often strikes during mundane administrative tasks, such as troubleshooting an esoteric network configuration for a family member who lacks the requisite technical fluency. When the infrastructure is complex—involving custom DNS, intricate firewall rules, and multiple layers of cryptographic protection—the system effectively becomes a black box. If the sole individual capable of decrypting the ZFS pool or navigating the Docker orchestration dies or becomes incapacitated, the aggregated digital history—financial records, proprietary creative works, and irreplaceable family media—becomes instantly inaccessible, effectively lost to entropy. This scenario necessitates a mechanism to bridge the gap between absolute digital control and familial access in extremis.
The Shortcomings of Cloud-Centric Legacy Tools
Major technology providers have recognized the need for digital afterlife planning. Services such as Google’s Inactive Account Manager or similar features offered by Apple and Meta allow users to designate trustees to access or delete data stored on those specific proprietary platforms after a period of inactivity. While these tools address data held in the cloud, they are fundamentally inadequate for environments built around sovereign, self-hosted infrastructure.

A local NAS array running a custom Linux distribution, or a collection of Docker containers managed via SSH, exists entirely outside the purview of these corporate legacy managers. Furthermore, relying on a major cloud provider to manage the distribution keys for one’s most sensitive, self-secured data introduces a vulnerability that negates the initial premise of self-hosting: centralized trust. If the objective is to safeguard master encryption keys—the master key to the entire digital kingdom—entrusting them, even conditionally, to a third-party server owned by an entity like Google or Apple represents merely shifting the single point of failure, not eliminating it.
This context demands a solution tailored for the decentralized, self-managed environment. This requirement led to the investigation and implementation of a dedicated system designed to operate solely within the confines of personal infrastructure: the "Dead Man’s Switch" (DMS) configured via specialized open-source utilities, such as Aeterna, which is specifically engineered for this purpose. Its utility lies in its lightweight, containerized nature, allowing deployment on minimal hardware, such as a dedicated Raspberry Pi or integrated directly into the existing NAS/server environment.
Architecting Continuity: The Mechanics of Aeterna
The efficacy of a DMS hinges on its operational logic, which must be robust enough to withstand minor interruptions yet sensitive enough to detect genuine administrator absence. Aeterna implements a clear, three-stage protocol: the Pulse, the Grace Period, and the Payload deployment.
The Pulse is the liveness check, the digital reassurance that the system administrator remains engaged. Each successful pulse resets the countdown timer toward potential activation. The implementation flexibility here is crucial for system administrators whose schedules fluctuate. While an automated cron job pinging the API upon workstation login offers zero-touch maintenance, it introduces a potential failure mode: if the workstation remains offline, the system erroneously triggers. A more prudent, albeit slightly more involved, approach involves a manual confirmation, such as clicking a button on the Aeterna dashboard monthly. This requirement for deliberate, conscious interaction serves a dual purpose: it confirms administrative presence and concurrently forces a periodic audit of the DMS itself, verifying that the underlying service and email configurations remain functional.
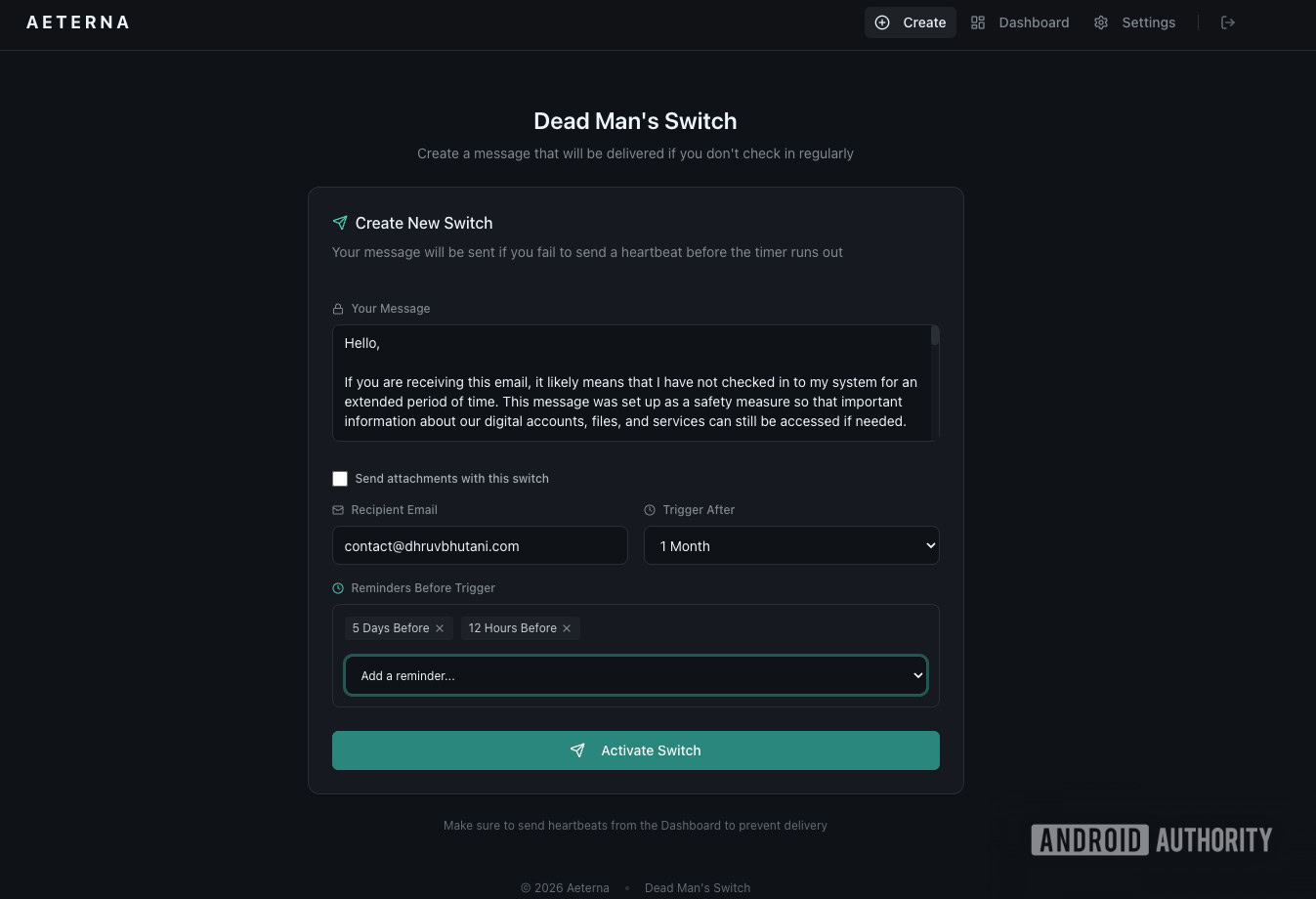
The Grace Period defines the acceptable window of administrative absence. A configuration of 30 days was selected as a pragmatic compromise: it accommodates extended travel or periods of intense professional focus where server maintenance is deferred, yet it is short enough to ensure timely response in a genuine emergency. Crucially, robust DMS implementation demands tiered notification. Receiving alerts at intermediate intervals (e.g., 15 and 25 days) prevents accidental activation. A single missed check-in due to a short illness might be acceptable; a sustained absence necessitates escalation. These progressive alerts serve as internal reminders rather than immediate triggers.
For a self-hosted solution, Reliability transcends mere feature parity—it is foundational. The DMS application must be afforded the same resilience as critical production services. This involves deploying the container on hardware with uninterruptible power supply (UPS) backup and, critically, ensuring the final notification mechanism is dependable. Utilizing a major, established SMTP relay service (like Gmail or SendGrid) for the final payload delivery is recommended over trying to maintain a private, authenticated mail server for this singular, high-stakes communication. The risk of the critical emergency email being flagged as spam or failing due to a minor local network outage outweighs the marginal benefit of complete self-containment for the notification layer. Rigorous testing, including intentionally allowing the timer to expire to observe notification delivery across various email clients, is non-negotiable before finalizing the setup.
Deconstructing the Payload: Information Architecture for Crisis
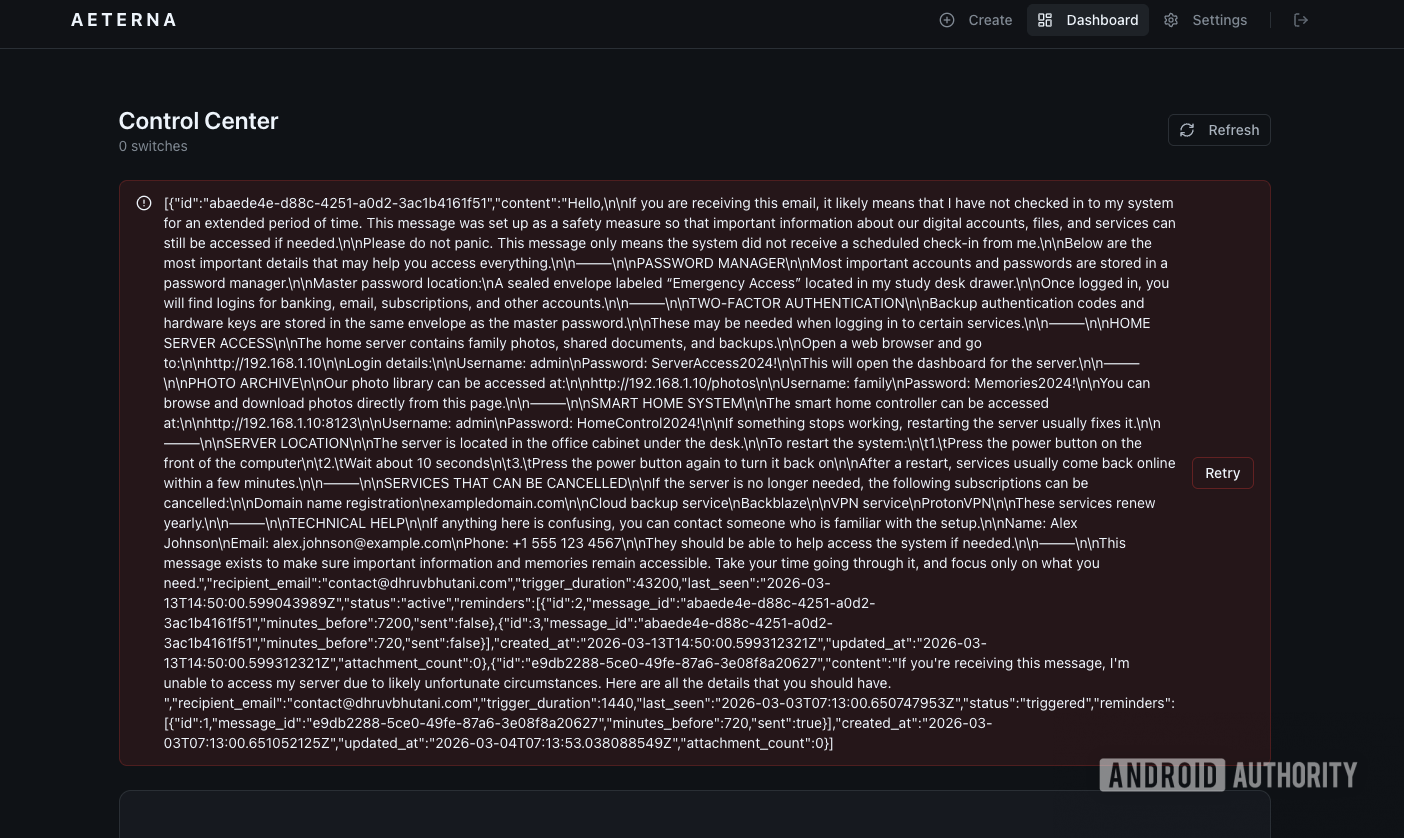
The mechanism of triggering is only half the battle; the content delivered—the Payload—determines the ultimate success of the continuity plan. The payload must adhere to the principle of "Just-In-Time, Just-Enough Information." It cannot be an exhaustive technical schematic, which would overwhelm a non-technical recipient during a crisis, but it must contain the absolute minimum data required to unlock essential services and initiate shutdown protocols.
The payload was structured around four critical data vectors:

- Master Credential Access: The single most vital piece of information is the master password to the designated, encrypted password manager (e.g., Bitwarden or KeePassXC). Since nearly all subsequent financial, legal, and service credentials reside within this vault, it serves as the gateway to the entire digital estate.
- Multi-Factor Authentication (MFA) Bypass: Even with the master password, modern security protocols often halt progress at the MFA stage. The payload must detail the physical location of emergency backup TOTP seeds or hardware key recovery codes. This mitigates the risk of being locked out by standard security layers designed to thwart external breaches.
- Operational Access and Maintenance Guides: This section provides explicit, simplified instructions for accessing and maintaining the most utilized, family-centric services, notably the shared photo archive and critical smart home interfaces (like Home Assistant). Including a curated list of internal IP addresses and default local login credentials streamlines access to these resources, preventing confusion over URL resolution.
- The Decommissioning Protocol (Kill Switch Guide): Paradoxically, ensuring continuity also means planning for cessation. This guide outlines the process for safely terminating non-essential, high-cost services (e.g., certain cloud subscription mirrors), migrating necessary archival data to simple, plug-and-play external drives, and finally, shutting down the server infrastructure entirely. Including contact details for a trusted, technically proficient external associate serves as a final escalation point should internal family members prove unable to proceed.
A significant security consideration arises when storing credentials destined for transmission. Storing the actual master password in plain text within the DMS configuration is inherently risky, even if the application itself is secured. The mitigation employed here introduces a real-world two-factor element: the payload itself contains only the location of a physical, cryptographically sealed "Emergency Envelope" hidden in a secure location (e.g., a home safe or office study). An attacker compromising the server would only gain access to the location clue, not the actual decryption keys, thus maintaining the integrity of the encryption architecture.
Industry Implications: Confronting the Home Lab’s "Bus Factor"
The focus on hardware redundancy in the self-hosting community—obsessing over RAID configurations, ECC memory, and high-availability power solutions—is well-justified for data integrity against component failure. However, this obsession often overlooks the Bus Factor, a concept borrowed from software engineering that quantifies the minimum number of key personnel required to maintain a project’s operational status. For the typical home lab, the Bus Factor is invariably one: the administrator.
When the administrator is removed from the equation, the system, however physically resilient (RAID 6, dual PSUs), becomes functionally fragile. Layers of sophisticated security, designed to repel external threats, inadvertently create impenetrable barriers for internal stakeholders. An overly complex, highly encrypted setup—a hallmark of dedicated privacy—becomes an active liability to the family.
Implementing a robust DMS forces a critical self-audit, effectively externalizing the administrator’s tacit knowledge. The process of documenting the system into a digestible payload necessitates simplification. If the operational flow of the home lab cannot be adequately summarized in a concise post-mortem document, the underlying architecture is likely over-engineered for its practical household utility. This forced clarity often reveals years of accumulated technical debt—untouched local DNS entries, deprecated port forwards, or unnecessarily complex networking layers—that can be streamlined, benefiting long-term maintainability regardless of the DMS trigger.
Future Trends in Digital Estate Management
The trend toward edge computing and increased personal data sovereignty suggests that self-hosting will only become more pervasive, making the DMS concept increasingly relevant. Future iterations of these continuity tools will likely incorporate more sophisticated, automated mechanisms that move beyond simple email payloads.
One significant development could be the integration of decentralized identity solutions. A DMS could be programmed to release verifiable credentials (VCs) to pre-approved family members’ secure digital wallets upon trigger. This moves the delivery mechanism from vulnerable email protocols to cryptographically verifiable claims, offering greater security for the released secrets.
Furthermore, the legal and technical communities are slowly recognizing the need for standardized protocols that bridge traditional estate law with digital assets held outside regulated financial institutions. As home servers transition from enthusiast novelties to essential utilities managing health records, financial transactions, and intellectual property, the "Dead Man’s Switch" will evolve from a personal contingency plan into a necessary component of comprehensive digital estate governance, ensuring that personal infrastructure remains an asset, not an inaccessible monument, upon the administrator’s departure. Implementing such a system, while morbid in conception, is ultimately an act of long-term stewardship over one’s digital life and legacy.

