The Council of the European Union has initiated a significant punitive action against transnational cyber threats, formally sanctioning three corporate entities—two based in the People’s Republic of China and one in Iran—alongside two associated individuals. This decisive move underscores the EU’s hardening stance against foreign state-sponsored or affiliated malicious cyber activity that demonstrably impacts the security, integrity, and essential functions of member states and the broader European digital ecosystem. The targeted sanctions package, which includes asset freezes and comprehensive travel bans for the named individuals, reflects a maturation of the EU’s coordinated response framework established under its cyber sanctions regime, which formally commenced in 2019.
The actions against the Chinese entities are particularly noteworthy, given the scale of disruption attributed to them. Integrity Technology Group has been implicated in providing substantial technical and material support for operations spanning 2022 and 2023, directly facilitating the compromise of over 65,000 interconnected devices across six different European Union member nations. This level of wide-scale device compromise points toward the deployment of sophisticated botnet infrastructure, designed not merely for espionage but for persistent network foothold and potential large-scale disruption. The targeting of numerous devices suggests an industrial approach to building an attack surface, potentially leveraging vulnerabilities in Internet of Things (IoT) hardware or widely deployed network infrastructure.
Concurrently, Anxun Information Technology, the second sanctioned Chinese firm, faces scrutiny for offering dedicated hacking services explicitly aimed at undermining the critical infrastructure and vital operational functions of both EU member states and partner nations. The implications here transcend simple data theft; attacks against critical infrastructure—which encompasses energy grids, telecommunications, healthcare systems, and financial services—represent a direct threat to public safety and economic stability. The designation of two specific individuals, identified as co-founders of Anxun Information Technology, confirms the bloc’s intent to hold leadership accountable for the directed campaigns orchestrated by the entity.
This designation framework is closely aligned with parallel efforts from transatlantic partners. Integrity Technology Group’s activities have previously been linked by the U.S. Federal Bureau of Investigation (FBI) in 2024 to the “Raptor Train” botnet. This infrastructure is widely believed to be the operational backbone for the Chinese state-sponsored threat group known as “Flax Typhoon.” The U.S. Treasury Department followed through with its own sanctions against Integrity Technology Group in January 2025, citing its role in enabling the Raptor Train to amass a sprawling network comprising approximately 260,000 compromised devices. Such extensive botnets offer threat actors significant distributed power for denial-of-service attacks, credential stuffing, and large-scale malware distribution.
Furthermore, Anxun Information Technology, also known by the moniker i-Soon, has a long and documented history of offering cyber services on a mercenary basis. The U.S. Department of Justice charged this entity in March 2025 for actively advertising and executing cyberattacks dating back to at least 2011. A significant breach in the operational security of i-Soon in mid-February 2024—a major data leak—exposed internal documentation detailing its structure as a China-affiliated hacking contractor, along with revealing elements of its offensive cyber toolset. This transparency provided by the leak offered intelligence agencies unprecedented insight into the mechanics of state-backed commercialized cyber espionage. Adding weight to these enforcement actions, U.S. authorities have offered substantial rewards, up to $10 million, for actionable intelligence leading to the location of ten key executives and technical personnel from Anxun Information Technology.
The scope of the EU’s action extends firmly into the realm of information warfare and sophisticated influence operations, highlighted by the sanctions levied against the Iranian firm, Emennet Pasargad. This company is directly attributed with conducting numerous influence campaigns. A specific incident cited involves the compromise of an SMS service infrastructure within Sweden, suggesting an attempt to intercept communications or manipulate service delivery for operational advantage.

More visibly, Emennet Pasargad’s activities included hijacking digital advertising billboards to disseminate misinformation campaigns timed to coincide with the 2024 Paris Olympic Games—a clear attempt to disrupt a high-profile international event and sow public discord during a period of heightened global attention.
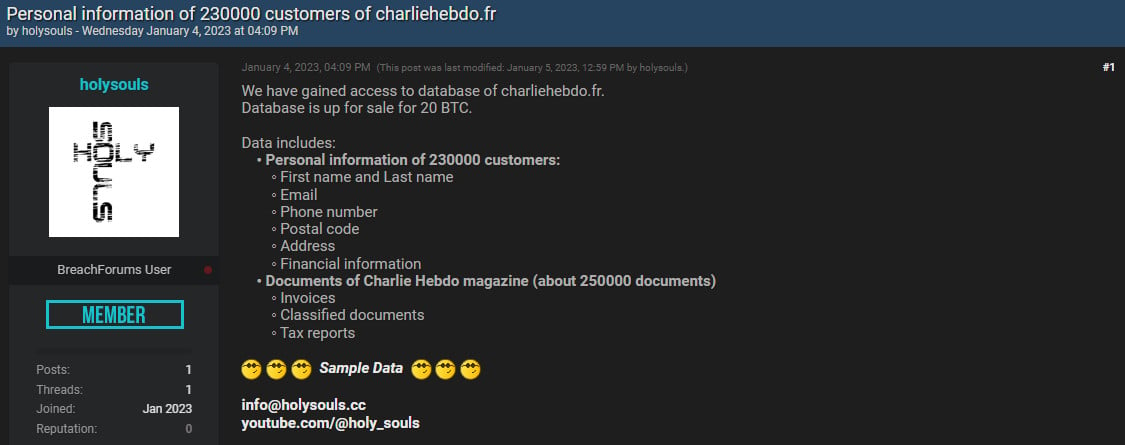
The activities attributed to Emennet Pasargad extend into deeply personal data exploitation. Security intelligence, including reporting from Microsoft, links an actor operating under the alias “Holy Souls” to Emennet Pasargad. In early January 2023, this actor publicly offered to sell the personal records of approximately 230,000 subscribers of the French satirical magazine Charlie Hebdo. The asking price was reportedly 20 Bitcoin, valued near $340,000 at the time, and the actor demonstrated credibility by publishing a sample set containing names and addresses. This type of operation blends state-aligned activity with financially motivated cybercrime, often leveraging the former’s resources for the latter’s gain, or using illicit data sales to fund further operations. Emennet Pasargad’s alleged role as a provider of cybersecurity services to the Iranian government further cements its status as a state-proximate actor engaging in both offensive and disruptive campaigns. This history is not new; in November 2021, the U.S. Department of Justice placed a $10 million bounty on two Iranian nationals contracted by the firm, underscoring years of sustained adversarial action.
Industry Implications and Regulatory Tightening
The simultaneous imposition of sanctions by the EU against actors tied to both Beijing and Tehran sends a potent message about the geopolitical landscape of cyber conflict. For multinational corporations operating within Europe, these designations necessitate immediate and rigorous due diligence updates. The sanctions mandate that EU citizens and entities are strictly prohibited from providing any funds, financial assets, or economic resources to the listed parties. This effectively cuts off access to the EU financial system and transactional infrastructure, a critical blow for any organization attempting to maintain business continuity or service delivery within the bloc.
From an industry perspective, the targeting of Integrity Technology Group and its association with the Raptor Train botnet serves as a stark warning regarding the supply chain risks embedded in networked devices. Organizations relying on hardware or software components originating from or passing through supply chains linked to these sanctioned entities must now undertake comprehensive audits to ensure no backdoors or persistent access mechanisms remain embedded within their operational technology (OT) or IT environments. The compromise of 65,000 devices suggests a high volume, low-touch infiltration strategy—a hallmark of state-sponsored efforts seeking broad access rather than deep, surgical penetration of a single target.
The specific targeting of Anxun/i-Soon reinforces the growing recognition that commercial cyber service providers are often indistinguishable from state intelligence assets. The exposure of i-Soon’s toolkit via the 2024 leak demonstrates that the intellectual property developed for hire can be used as evidence against the sponsoring state. This places pressure on technology providers globally to adopt stricter vetting processes for clients that may have opaque governmental ties, especially concerning clients who seek services related to large-scale data exfiltration or infrastructure testing.
Expert Analysis: The Blurring Lines of Statecraft
The convergence of espionage, influence operations, and data monetization seen in these cases illustrates a core feature of modern geopolitical cyber conflict: the blurring of lines between intelligence agencies, proxy groups, and commercial hacking firms. The Iranian case, in particular, demonstrates the utility of using influence operations (like the Olympic billboard hijacking) to achieve strategic, non-financial objectives, while simultaneously engaging in financially lucrative, yet disruptive, data theft (like the Charlie Hebdo subscriber list). This multi-faceted approach maximizes strategic impact while providing plausible deniability, even when the underlying capabilities are state-supported.
The effectiveness of the EU’s response lies in its financial leverage. Asset freezes and restrictions on economic engagement are designed to degrade the operational capacity of these entities by limiting their ability to procure zero-day exploits, fund infrastructure leasing, or transact in major currencies accessible within the European economic sphere. However, experts caution that actors like those sanctioned often possess sophisticated workarounds, utilizing decentralized finance mechanisms or non-Western banking systems. Therefore, the sanctions regime must be viewed as a critical deterrent and disruption tool, rather than an absolute blockade.
Future Impact and Evolving Trends
The EU’s consistent application of cyber sanctions, now targeting 19 individuals and seven entities since 2019, signals a commitment to establishing international norms of behavior in cyberspace through punitive economic measures. This trajectory suggests several anticipated developments:
- Increased Granularity of Targeting: Future sanctions are likely to become more granular, focusing not just on primary entities but on specific executives, technical leads, and the financial conduits used to launder sanction-evading funds. The US pursuit of Anxun/i-Soon executives sets a precedent the EU may increasingly follow.
- Focus on Supply Chain Vulnerability: As state-backed actors continue to exploit the globalized digital supply chain (as seen with Integrity Technology Group), expect regulatory frameworks within the EU to tighten requirements for transparency and risk assessment concerning hardware and software originating from high-risk jurisdictions. This aligns with broader digital sovereignty initiatives.
- Integration with Geopolitical Stance: Cyber sanctions will remain tightly coupled with broader diplomatic and trade relations. Actions against Chinese and Iranian actors reflect current tensions in areas extending beyond cybersecurity, such as human rights, regional security, and economic coercion. The sanctions serve as a non-kinetic tool in a wider diplomatic toolbox.
- Counter-Influence Measures: The demonstrated ability of actors like Emennet Pasargad to manipulate public information spaces during major events will likely prompt increased investment in both defensive digital resilience (protecting national narrative integrity) and proactive attribution, allowing for rapid, coordinated counter-messaging when influence operations are detected.
In summary, the latest wave of EU sanctions represents a significant escalation in the use of economic tools to enforce digital security boundaries. By specifically targeting the enablers of large-scale device compromise and sophisticated information warfare, Brussels is signaling that malicious cyber activities—regardless of geographic origin—will carry tangible financial and operational costs within the European market.

