The Federal Bureau of Investigation’s Seattle Division has issued an urgent appeal, actively soliciting information from consumers and gamers who may have been victimized by a series of malicious applications distributed through the widely used digital distribution platform, Steam. This coordinated outreach signals a significant escalation in the investigation targeting an elaborate scheme where otherwise legitimate-appearing video game titles were weaponized to deploy sophisticated malware payloads onto user systems. The agency’s focus spans a specific, concerning temporal window: installations occurring between May 2024 and January 2026, indicating a sustained, multi-year campaign by the threat actor or actors involved.
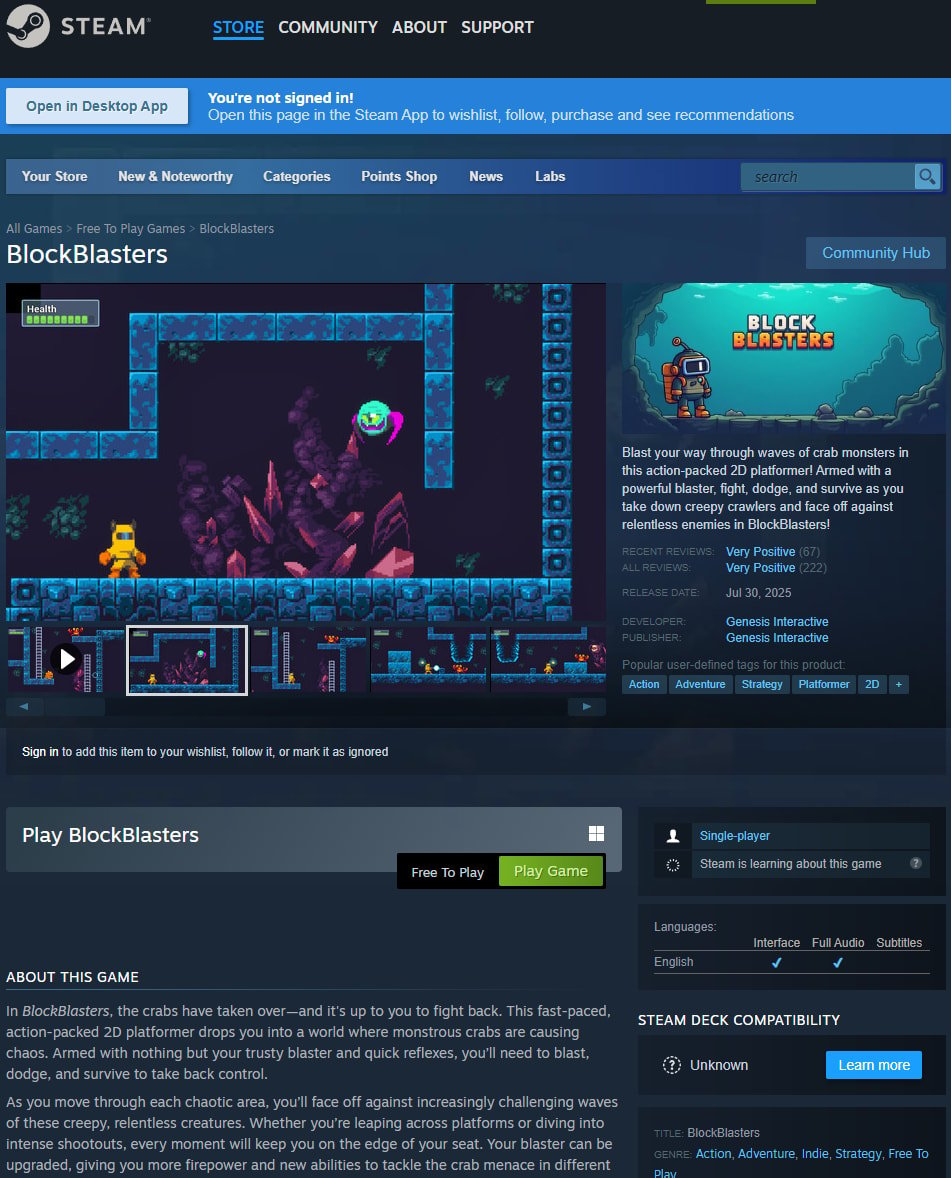
In a formal notification disseminated by the agency, the FBI explicitly stated its objective: "The FBI’s Seattle Division is seeking to identify potential victims installing Steam games embedded with malware. The FBI believes the threat actor primarily targeted users between the timeframe of May 2024 and January 2026." This investigation is not theoretical; it is rooted in confirmed security incidents involving specific titles that infiltrated the platform’s ecosystem. Among the identified compromised software are BlockBlasters, Chemia, Dashverse/DashFPS, Lampy, Lunara, PirateFi, and Tokenova. The inclusion of seven named titles, with the mention of "eight malicious games," suggests a larger attack surface than initially publicized, warranting immediate attention from the community.
The critical mechanism for reporting potential victimization is a structured online questionnaire provided by the FBI. This form is designed to gather forensic data pertinent to the primary objectives of the malware operators: the systematic theft of digital assets and unauthorized account access. Specifically, investigators are probing user experiences related to cryptocurrency transactions, the compromise of digital wallets, subsequent unauthorized fund transfers, and the hijacking of various online accounts tied to the compromised PCs. Furthermore, the investigative questionnaire seeks ancillary evidence, such as screenshots of communications with promoters or individuals vouching for the integrity of these malicious games. This detail is crucial, as it suggests the distribution network may have relied on social engineering or coordinated influencer marketing to lure unsuspecting users, allowing investigators to trace the financial and promotional pathways used to monetize the scheme.
The FBI has reassured potential victims regarding the handling of submitted data. A statement confirms the agency’s statutory obligation to identify those harmed by federal crimes under investigation. Critically, the Bureau emphasized that "All identities of victims will be kept confidential." This assurance is vital for encouraging broad participation, as users may fear professional or personal repercussions from admitting compromise. Moreover, the agency clarified the authenticity of the communication channels utilized, confirming that the websites and dedicated email address ([email protected]) referenced in mass notifications sent on March 12, 2026, are official and authorized for this specific inquiry. This level of procedural clarity is often necessary in large-scale cyber investigations where phishing attempts mimicking law enforcement contacts are common.
Contextualizing the Threat: The Erosion of Trust in Digital Distribution
This FBI action shines a harsh spotlight on the persistent security vulnerabilities within even the most established digital storefronts, even those with ostensibly robust vetting processes. Steam, operated by Valve Corporation, serves as the dominant platform for PC gaming distribution, hosting tens of thousands of titles. Its vastness and open nature—allowing developers to publish relatively easily—create an attractive vector for threat actors seeking high-volume access to end-user systems.
The malware deployed through these compromised games typically falls into the category of Information Stealers (Infostealers). These programs are engineered for stealth and persistence, designed not merely to crash systems but to silently exfiltrate valuable data. In the modern threat landscape, this data includes session cookies, stored passwords, browser history, and, most lucratively, the private keys or seed phrases associated with cryptocurrency wallets. The temporal focus of the FBI’s inquiry, spanning nearly two years, suggests that these specific malware strains were highly effective and evaded detection by platform security measures for an extended period, likely evolving their obfuscation techniques over time.
The background of previous, well-documented incidents underscores the severity of the current investigation. The case involving BlockBlasters serves as a stark illustration of the tangible financial damage inflicted. This free-to-play 2D platformer, initially appearing benign, was later found to harbor a "cryptodrainer" malware. The public revelation of this compromise was particularly damaging, occurring when streamer Raivo Plavnieks (RastalandTV) discovered over $32,000 drained from his cryptocurrency wallet while fundraising for cancer treatment—a situation that amplified the public outrage and the perceived malice of the attackers. Subsequent analysis by blockchain investigators like ZachXBT pegged the total estimated loss across 261 accounts at approximately $150,000, with other researchers citing an even larger victim pool nearing 500.

Similarly, the crafting game Chemia housed a multi-stage infection chain. Threat actors, identified by some researchers as the group known as EncryptHub, managed to introduce the HijackLoader malware, which subsequently fetched the Vidar information stealer. Further analysis revealed the presence of EncryptHub’s proprietary "Fickle Stealer," a bespoke tool capable of harvesting credentials, browser data, and crypto wallet information. The proliferation of such customized tools indicates a degree of sophistication beyond simple opportunistic attacks; these actors are investing in tooling tailored for high-yield data exfiltration.
The PirateFi incident further highlights the rapid deployment and subsequent removal cycle typical of these schemes. This game, distributing the Vidar infostealer, was available for only about a week in February 2025, yet it is estimated that up to 1,500 users may have downloaded it before Valve acted. Steam’s subsequent warning to users who had launched the game—advising comprehensive security measures including antivirus scans and potential OS reinstallation—underscores the deep level of system compromise these Infostealers achieve.
Industry Implications: The Burden of Platform Responsibility
The persistent ability of malicious actors to inject functional malware into a major digital marketplace like Steam raises significant questions regarding platform security governance and the efficacy of automated review processes. For Valve, the implications are profound, affecting both user trust and the platform’s reputation as a safe digital environment.
The core challenge lies in balancing an open ecosystem—essential for independent developer success—with the necessity of stringent security vetting. When malware is introduced post-publication, often through updates to seemingly legitimate, already-approved software, automated scanning tools designed for initial ingestion struggle to keep pace. Threat actors exploit the time gap between deployment and manual review or user reporting.
This trend forces a critical re-evaluation across the entire software distribution sector. If widely trusted storefronts cannot reliably prevent the dissemination of credential-stealing malware, consumers are forced into a state of perpetual suspicion regarding every download. This erodes the fundamental value proposition of a centralized, curated marketplace. For the gaming industry, where in-game purchases, digital libraries, and associated accounts hold significant monetary and personal value, this erosion of trust translates directly into hesitation to engage fully with digital ecosystems.
Furthermore, the focus on cryptocurrency theft signals a maturation of cybercriminal tactics targeting the gaming demographic. Gamers are often early adopters of new technologies, including decentralized finance (DeFi) and cryptocurrencies, making them a high-value target pool. Attackers are moving beyond simple credit card fraud to target the more difficult-to-trace and potentially higher-value assets stored in digital wallets.
Expert Analysis: Malware Evolution and Defense Evasion
From a cybersecurity perspective, the identified malware families—Vidar, HijackLoader, and bespoke stealers—demonstrate adherence to contemporary evasion tactics. Modern Infostealers rarely rely on single-stage execution. Instead, they employ multi-layered delivery systems. The use of loaders like HijackLoader suggests a modular approach, allowing the threat actor to swap out the final payload (the stealer) based on observed security controls or to maximize payload effectiveness against specific targets.
The successful propagation over an 18-month window suggests the malware utilized techniques to bypass static analysis. This likely includes:
- Polymorphism and Obfuscation: Code that changes its signature with each execution, defeating signature-based antivirus detection.
- Living Off the Land (LotL): Utilizing legitimate system tools (like PowerShell or WMI) for post-exploitation tasks, blending malicious activity with normal system operations.
- Sandbox Detection: Sophisticated checks to determine if the file is running within a virtualized security analysis environment. If a sandbox is detected, the malware remains dormant or executes benign code, only activating on a genuine user machine.
The FBI’s request for communication screenshots hints at a social engineering component, likely leveraging platforms like Discord or direct messaging within Steam itself. Threat actors often create elaborate front-ends—fake developer accounts, compelling game trailers, or endorsements from seemingly legitimate community figures—to bypass user skepticism. Tracing these communications is critical for dismantling the human element of the attack infrastructure, which often precedes the technical deployment.
Future Impact and Trends in Digital Platform Security
The repercussions of this extensive FBI investigation will likely ripple through platform security practices for years. We can anticipate several trends emerging as a direct response:
1. Enhanced Developer Scrutiny and Sandboxing: Valve and competitors will likely be pressured to implement stricter, possibly mandatory, code-signing requirements and enhanced pre-publication sandboxing that simulates real-world user environments for longer durations. This may involve stricter limitations on the types of system calls newly uploaded executables can make until they achieve a certain trust rating.
2. Proactive Threat Intelligence Sharing: The success of this FBI effort in identifying victims will depend heavily on ongoing cooperation between law enforcement, cybersecurity firms (like those who initially identified the malware), and the platform operator. A future model may involve near real-time threat intelligence feeds shared directly between security researchers and Steam’s internal security teams to quarantine suspicious files faster.
3. Focus on Post-Installation Remediation: The advice given to PirateFi victims—reinstalling the operating system—highlights the devastating potential of these Infostealers. Future platform security communications will need to emphasize immediate, decisive remediation steps for users whose software has been flagged, moving beyond simple antivirus scans to address rootkit or deep-level persistence mechanisms.
4. Legal and Regulatory Pressure: As cybercrime involving digital platforms escalates, there will be increasing regulatory scrutiny directed at platform owners regarding their due diligence in protecting consumer assets. Lawsuits seeking damages on behalf of affected users are a distinct possibility, potentially forcing platform operators to bear some financial responsibility for damages resulting from security failures that allowed such malware to persist.
The FBI’s active solicitation for victims marks a crucial juncture in addressing this sustained attack vector. It transitions the response from reactive removal to proactive victim remediation and criminal intelligence gathering, aiming to map the entire criminal enterprise—from the developers who packaged the malware to the recipients of the stolen cryptocurrency—in an effort to dismantle the operation permanently. For the gaming community, this serves as a stark reminder that the security of digital assets is a shared responsibility, requiring vigilance even within trusted digital storefronts.

