The digital landscape has been jolted once again by the revelation that Google has issued emergency security updates to address two newly discovered, high-severity vulnerabilities within the ubiquitous Google Chrome web browser, both of which are confirmed to be under active exploitation as zero-days. In a terse security advisory released on Thursday, Google confirmed its awareness that malicious actors are leveraging exploits targeting both CVE-2026-3909 and CVE-2026-3910 in real-world scenarios. This immediate response underscores the persistent and evolving threat landscape facing even the most widely deployed software platforms.
The urgency surrounding this patch cycle stems from the nature of these flaws. The first vulnerability, cataloged as CVE-2026-3909, resides within Skia, the sophisticated open-source 2D graphics library fundamental to rendering web content and the browser’s intricate user interface elements. Specifically, the issue is classified as an out-of-bounds write weakness (CWE-787). Such flaws are notoriously dangerous in rendering engines because they allow an attacker to write data beyond the intended memory buffer. Successful exploitation of an out-of-bounds write can lead to catastrophic outcomes, ranging from a simple denial-of-service condition—crashing the web browser—to the far more severe scenario of arbitrary code execution, granting the attacker deep, persistent access to the user’s underlying operating system.
The second critical flaw, designated CVE-2026-3910, represents a different vector of attack, focusing on the high-performance core of modern web execution: the V8 JavaScript and WebAssembly engine. This vulnerability is described technically as an "inappropriate implementation," suggesting a failure in how the browser engine handles specific operations or interpretations of web standards, leading to exploitable behavior. Given V8’s role in executing complex, dynamic code, exploitation here can also pave the way for remote code execution (RCE), often bypassing standard sandboxing mechanisms if the exploit chain is sufficiently refined.
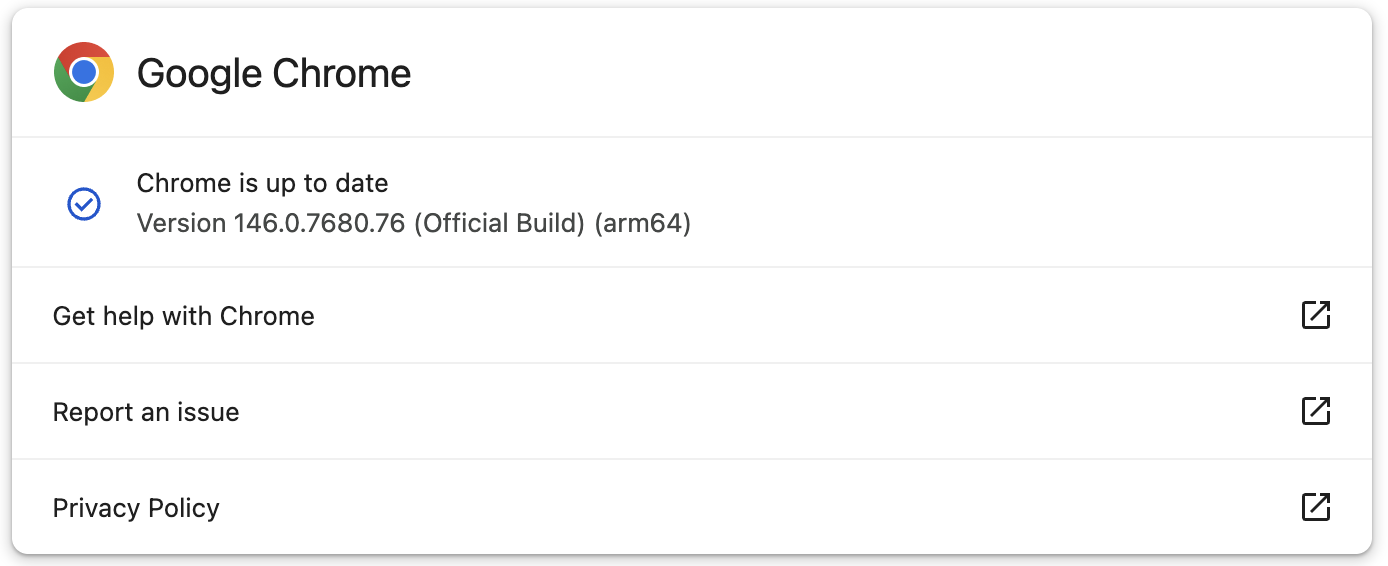
Google’s responsiveness in this instance is notable. The company reported discovering and subsequently patching both vulnerabilities within a rapid two-day window following initial reporting, ensuring the fixes were deployed to users on the Stable Desktop channel. These fixes are being rolled out across all major operating systems: Windows is receiving version 146.0.7680.75, macOS users are slated for 146.0.7680.76, and Linux systems are designated for 146.0.7680.75. While Google notes that the distribution of this out-of-band update may take several days, or potentially weeks, to fully propagate across its massive global user base, initial availability checks confirmed the patches were accessible immediately following the advisory’s release. Users are strongly advised to force an update check within their browser settings or ensure automatic update mechanisms are enabled to minimize their exposure window.
Contextualizing the Escalating Threat Landscape
The rapid succession of actively exploited zero-days highlights a worrying trend in software security, particularly for foundational technologies like web browsers. Chrome, serving as the gateway to the internet for billions, remains a prime target for sophisticated threat actors, ranging from state-sponsored espionage groups to high-level cybercriminal enterprises.
This pair of vulnerabilities marks the second and third zero-days patched by Google since the dawn of 2026. This pace significantly exceeds historical averages. For comparison, the first exploited zero-day of the year, CVE-2026-2441, addressed in mid-February, involved an iterator invalidation bug within Chrome’s implementation of CSS font feature values (CSSFontFeatureValuesMap). While seemingly niche, memory corruption bugs tied to rendering components frequently provide reliable attack surfaces.
Looking back at the previous year, 2025 saw Google address a total of eight zero-days exploited in the wild. Many of these critical findings were attributed to the diligent work of Google’s internal Threat Analysis Group (TAG), a unit specializing in tracking and neutralizing zero-days often linked to highly targeted spyware operations against journalists, activists, and political dissidents. The fact that the first quarter of 2026 is already approaching the frequency of mid-year activity in 2025 suggests a potential acceleration in vulnerability discovery and weaponization cycles.
Industry Implications: The Dependency Chain Risk
The identification of CVE-2026-3909 within the Skia library carries significant weight beyond Chrome itself. Skia is an open-source library, meaning it is integrated into numerous other software projects, including other browsers, mobile operating systems, and various desktop applications that require robust 2D graphics rendering capabilities.
This dependency chain amplifies the risk exponentially. When Google patches a vulnerability in a core library like Skia, it sets off a critical chain reaction across the technology ecosystem. Other vendors utilizing the same vulnerable version of Skia must now scramble to integrate the fix, often facing delays due to their own internal testing and deployment pipelines. For security professionals, this means that simply updating Chrome is insufficient; a comprehensive inventory of all software leveraging the affected version of Skia is necessary to ensure holistic coverage. This highlights the inherent fragility in relying on shared, complex open-source components—a single weak link can compromise an entire technological infrastructure.
The V8 engine vulnerability (CVE-2026-3910) speaks to the increasing complexity of the web platform. As JavaScript and WebAssembly become more powerful, enabling desktop-grade applications to run entirely within the browser sandbox, the attack surface within these execution engines expands. Attackers are consistently targeting the JIT compilers, garbage collectors, and core object handling routines within V8, seeking subtle logical flaws that permit memory corruption or control flow hijacking.
Expert Analysis: The Shift to Memory Safety
The prevalence of memory safety vulnerabilities—such as the out-of-bounds write in Skia—reinforces a major long-term trend in software development: the industry-wide push toward memory-safe languages. While C++ remains foundational for performance-critical components like Skia and V8, the sheer volume of memory safety bugs being found and exploited suggests that the mitigation burden placed on developers to manually enforce memory boundaries is proving unsustainable against determined adversaries.
Security experts have long advocated for migrating performance-critical components to languages like Rust, which enforces memory safety at compile time, thereby eliminating entire classes of vulnerabilities like buffer overflows and use-after-free errors by design. While a full transition for a project as massive and mature as Chrome is a multi-decade endeavor, each actively exploited zero-day serves as a stark reminder of the cost associated with legacy, inherently unsafe codebases. The frequency of these flaws puts immense pressure on the browser vendors to invest heavily in fuzzing, static analysis, and formal verification techniques to catch these memory errors before they reach the wild.
Furthermore, the decision by Google to restrict details regarding the active exploitation incidents—stating that access to bug details and links will remain restricted until a majority of users are patched—is a standard but crucial defensive measure. This "withholding" policy aims to prevent the public release of exploit code (Proof-of-Concept or weaponized versions) from accelerating the infection rate. The restriction is particularly vital when third-party libraries are involved, as the fix must propagate across all dependent projects before full disclosure can occur without endangering users of those other systems.
The Role of Vulnerability Reward Programs (VRPs)
The continuous flow of high-quality vulnerability reports, even those that become zero-days, is intrinsically linked to the success of bug bounty programs. In a related disclosure, Google highlighted the substantial investment it made in its Vulnerability Reward Program (VRP) throughout 2025, paying out over $17 million to 747 security researchers.
This massive financial incentive structure is a cornerstone of modern vulnerability management. It effectively crowdsources security auditing, leveraging global expertise far beyond the capacity of any internal security team. The researchers rewarded are often the very individuals who discover these complex logic errors before malicious actors can fully weaponize them. The continued high payout level reflects the escalating sophistication required to find critical flaws in mature software like Chrome. Without such robust programs, it is highly probable that the number of zero-days discovered and weaponized would be significantly higher.
Looking Ahead: Future Impact and Defense Strategies
The immediate future for Chrome users demands vigilance. Organizations must treat the deployment of version 146.0.7680.75 (or the relevant OS version) as a top-tier security priority. For enterprise environments, this often necessitates bypassing standard patch management schedules for out-of-band security releases, employing tools that can force immediate updates across endpoints, especially for privileged users or those accessing sensitive data.
Looking forward, the pattern established this year suggests that threat actors are becoming increasingly effective at rapidly developing zero-day exploits, possibly aided by advancements in AI-assisted exploit generation or better analysis of historical patch diffs. Defenders must adapt by focusing on layered security:
- Browser Hardening: Utilizing advanced security features built into modern browsers, such as enhanced site isolation, stricter sandboxing policies, and memory tagging extensions, which can sometimes disrupt an exploit chain even if a memory corruption bug is triggered.
- Network Monitoring: Implementing advanced endpoint detection and response (EDR) systems capable of spotting the behavior associated with zero-day exploitation—such as unusual process spawning or unexpected network activity originating from the browser process—even when the initial exploit signature is unknown.
- Supply Chain Auditing: For organizations relying heavily on custom applications or internal tooling built atop Chromium, rigorous auditing of dependencies, particularly graphics libraries, scripting engines, and networking stacks, is paramount.
The latest emergency patches confirm that in the high-stakes game of cybersecurity, no software, regardless of its ubiquity or the resources dedicated to its security, is entirely immune. The cat-and-mouse game between defenders and attackers continues to be played out in the most fundamental layers of our digital infrastructure, demanding continuous, rapid iteration in defensive postures.