The burgeoning handheld gaming PC market, characterized by innovative hardware and specialized software layers, recently faced a significant trust challenge following a public accusation leveled against AYANEO concerning its Pocket DS model. A user, reporting findings on a public development forum associated with prominent tech commentators, detailed the discovery of over 1,200 seemingly untriggered screenshots stored locally on their device, alongside alarming reports of substantial background data transmission attributed to the proprietary AYAWindow application. This incident, occurring shortly after AYANEO publicly committed to a "Service Improvement Plan" addressing earlier customer satisfaction issues, immediately cast a shadow over the company’s software integrity and user privacy protocols.
The context surrounding this discovery is crucial. AYANEO, like many competitors in the Android-based handheld space, relies heavily on custom overlay software—in this case, AYAWindow—to bridge the gap between the core Android operating system and the specialized needs of emulation and gaming, such as custom control mapping, performance monitoring, and quick access interfaces. These systems, while essential for user experience, inherently require deeper access privileges into the OS than typical consumer applications, making any unusual behavior inherently more scrutinized.
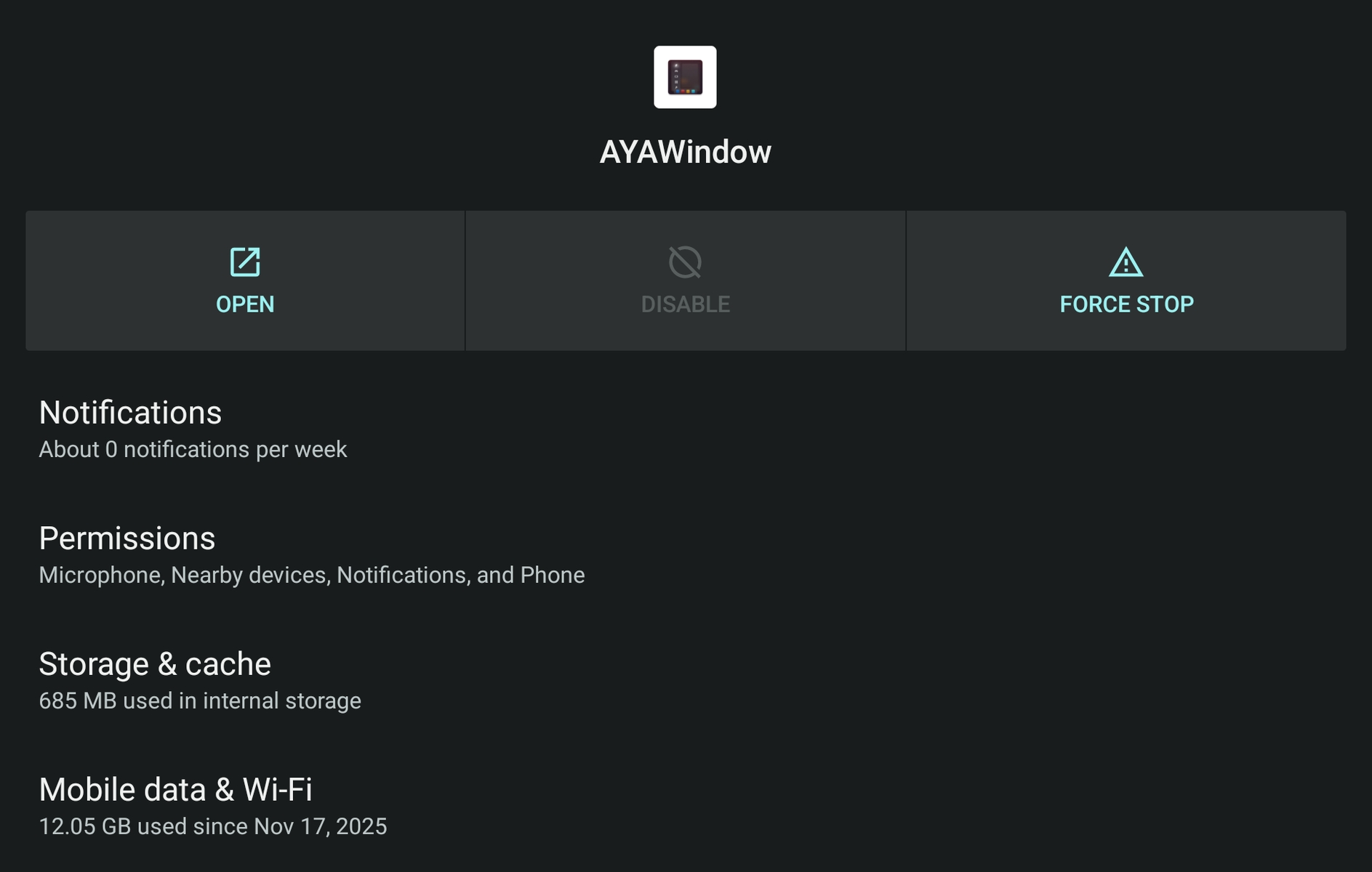
The initial report highlighted the sheer volume of the collected data: more than a thousand captured screen images, ostensibly taken across various gaming sessions, continuously accumulating. In an era hyper-aware of digital surveillance, the presence of such a large, unrequested cache immediately triggered privacy alarms, leading the reporting user to suggest potential unauthorized monitoring or "spying." Compounding this concern was the secondary claim: the AYAWindow process appeared responsible for transmitting over 12 gigabytes of data off the device since November, a figure that suggested heavy, non-obvious background activity.
The Technical Counter-Narrative: Caching Gone Awry
In response to the controversy, an individual believed to be affiliated with AYANEO addressed the concerns directly on the issue tracker. This explanation steered the narrative away from intentional surveillance and towards a technical failure—specifically, a persistent caching bug within the AYAWindow utility.
The core defense centered on the application’s function to generate visual thumbnails for rapid in-system previewing, often used within application launchers or system menus for quick navigation. The representative asserted that the Pocket DS is designed to create these visual caches for optimized performance. The critical breakdown, according to this explanation, was a failure in the subsequent cleanup routine. The bug prevented the system from automatically deleting these temporary screen captures once they were no longer needed for caching purposes, resulting in an exponential, albeit unintentional, accumulation of image files.

While the screenshot discovery was explained as a memory management flaw, the significant data egress—the reported 12GB transfer—required a separate technical dissection. The response posited that the reported traffic was not solely attributable to AYAWindow transmitting personal data, but rather a consequence of how the underlying Android operating system aggregates network activity under specific User IDs (UIDs).
In Android architecture, processes are often grouped by their system privileges. If AYAWindow executes under the android.uid.system group, its observed data usage statistics become intertwined with all other applications and system services that share that identical UID. Therefore, the reported 12GB figure represented the total outbound traffic associated with that privileged system context, not the unique payload generated by the AYAWindow application itself. This is a common point of confusion when analyzing network logs on deeply integrated Android systems, where resource utilization reporting can be opaque to the average end-user.
Industry Implications: Trust in Custom Android Layers
This incident underscores a persistent tension in the handheld PC space, particularly for manufacturers utilizing Android as a base OS. Unlike Windows-based handhelds, which run a familiar, mature desktop environment, Android handhelds depend almost entirely on proprietary vendor software to deliver a console-like experience. This reliance creates an elevated risk profile regarding data handling and transparency.
For manufacturers like AYANEO, establishing user trust is paramount, especially when launching new, complex hardware platforms. Early operational hiccups, such as the service boycotts AYANEO had recently sought to rectify, can be quickly overshadowed by perceived privacy breaches. The public nature of the discovery—originating from a user report posted on a public repository—amplified the visibility and severity of the initial claim far beyond what a private support ticket might have achieved.
From a software engineering perspective, this event serves as a stark reminder of the need for rigorous testing of cleanup and resource management routines, particularly those interacting with core system resources like file storage and network monitoring. In the context of custom firmware on specialized hardware, the potential for unintended consequences from poorly managed caches or logging mechanisms is significantly higher than on standardized consumer devices. An uncleaned cache of screenshots is not merely wasted storage; it represents a potential vector for future security risks or, at the very least, a profound erosion of user confidence.
Expert Analysis: Differentiating Bugs from Malice
In evaluating such claims, cybersecurity professionals typically adhere to a principle of Occam’s Razor, preferring the simplest explanation that fits the evidence—in this case, the technical bug explanation over a deliberate surveillance operation. However, the perception of malice often outpaces technical clarification in the court of public opinion.
The accumulation of 1,200 screenshots suggests a highly inefficient, poorly capped logging mechanism. If AYAWindow were indeed attempting to covertly record user activity for external transmission, it would likely employ more sophisticated, targeted capture methods rather than generating and retaining thousands of large image files locally. The presence of the files before the massive data transfer suggests a causal chain: capture, storage, and then perhaps an attempt (or system default) to synchronize the cache, leading to the large observed bandwidth spike.
The misinterpretation of UID-based network reporting is also a recurring theme in technical support interactions. System processes often share the system UID to perform low-level tasks—such as managing power states, display outputs, or system-level updates. When a user monitors network traffic, they see the combined result. For AYANEO, this is an opportunity not just to fix the cache bug, but to improve the diagnostic tools provided to users, perhaps implementing a more granular traffic breakdown that separates application-specific traffic from shared system traffic.
Future Impact and Mitigation Strategies
The immediate impact for AYANEO involves managing the narrative and demonstrating swift, transparent remediation. The commitment to pushing a fix quickly is essential. However, the long-term impact relates to the perception of their software development lifecycle. Users of specialized hardware often accept a higher degree of initial instability in exchange for cutting-edge features, but they demand absolute fidelity on privacy and security foundations.
Moving forward, AYANEO and similar niche manufacturers must adopt best practices to preempt such public relations crises:
- Enhanced Auditing and Logging Transparency: Any system application with elevated privileges should log its data collection activities in an easily accessible, human-readable format, detailing why a screenshot was taken and where the corresponding data was sent.
- Resource Quotas: Implementing hard, non-negotiable quotas for temporary file storage related to features like caching prevents runaway accumulation, rendering the "bug" functionally harmless even if the cleanup fails temporarily.
- Independent Security Review: For critical proprietary layers like AYAWindow, commissioning third-party security audits before major releases can identify potential privacy pitfalls and reporting ambiguities before they reach the end-user.
The Pocket DS, designed to capitalize on the nostalgia of dual-screen gaming while leveraging modern Android power, represents a complex intersection of emulation, custom OS layering, and consumer expectations. This incident, while likely rooted in a simple coding oversight regarding cache management and data attribution, forces a broader industry reckoning on how proprietary system software communicates its operations to the end-user. In the connected device landscape, the default assumption for any undocumented local storage or high data usage is often suspicion, demanding proactive transparency from hardware vendors to maintain the fragile bond of consumer trust. The rapid deployment of the promised patch, coupled with clear communication regarding the network traffic statistics, will be the true measure of AYANEO’s commitment to its Service Improvement mandate.

