The security landscape for high-value targets has just become significantly more complex following a stark warning issued by the Netherlands’ primary intelligence and security agencies. Both the Defence Intelligence and Security Service (MIVD) and the General Intelligence and Security Service (AIVD) have jointly alerted the public and government sectors to an escalating, highly targeted cyber espionage campaign. This operation, attributed to Russian state-sponsored threat actors, specifically exploits user trust within popular end-to-end encrypted (E2EE) messaging applications, namely Signal and WhatsApp, to compromise the communications of critical personnel, including government officials, military staff, and investigative journalists.
The core of this sophisticated threat is not a vulnerability within the underlying cryptographic protocols of Signal or WhatsApp—which remain structurally sound—but rather a meticulously crafted manipulation of user behavior. Intelligence sources confirm that the threat actors are leveraging advanced social engineering tactics, weaponizing the legitimate account recovery and device linking mechanisms inherent in these platforms to achieve unauthorized access and persistent surveillance. This pivot toward exploiting the human element, rather than relying solely on software zero-days, represents a significant maturation in the adversary’s operational methodology against targets requiring secure, off-the-record communication.
The Mechanics of Credential Theft: The Chatbot Deception
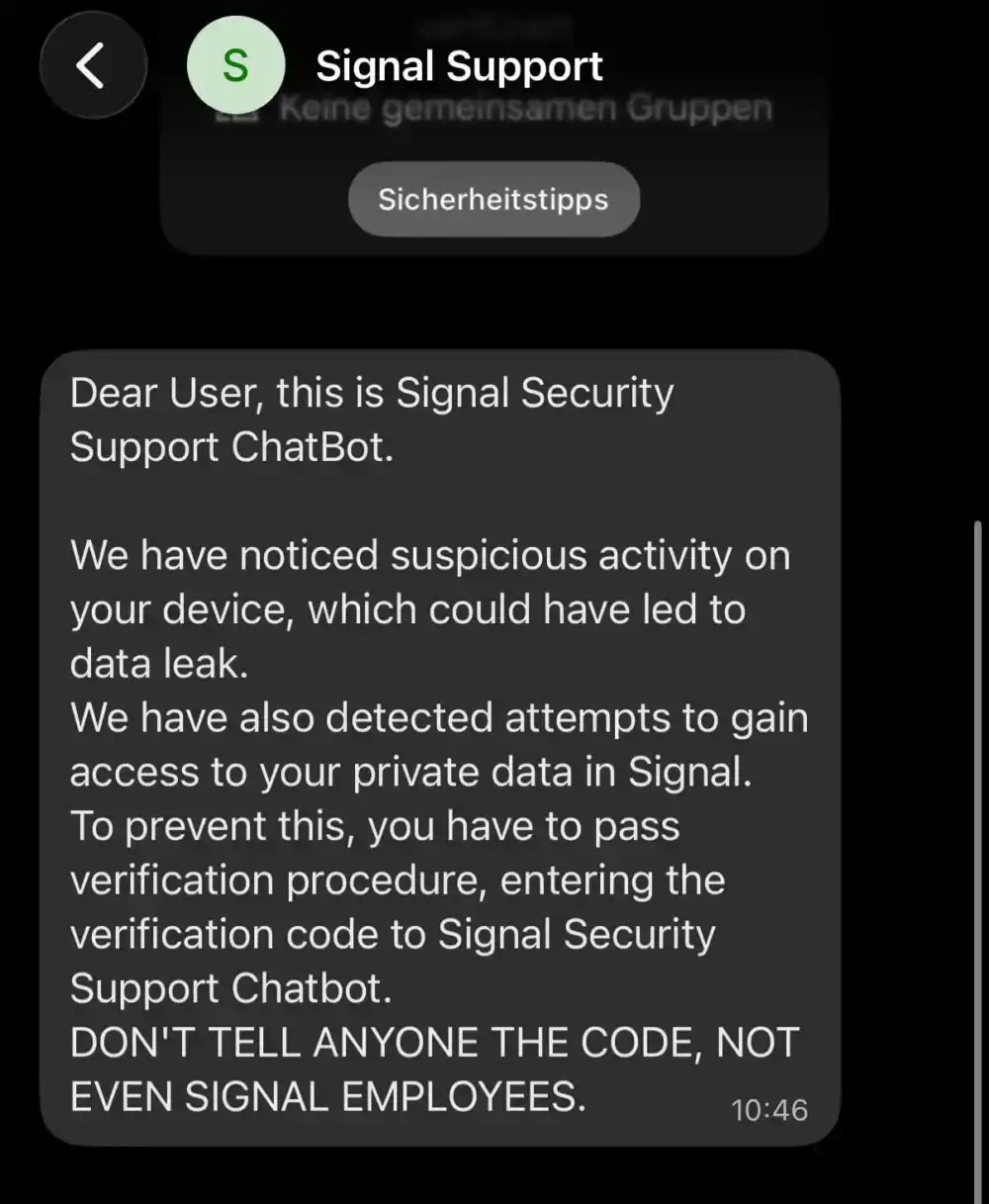
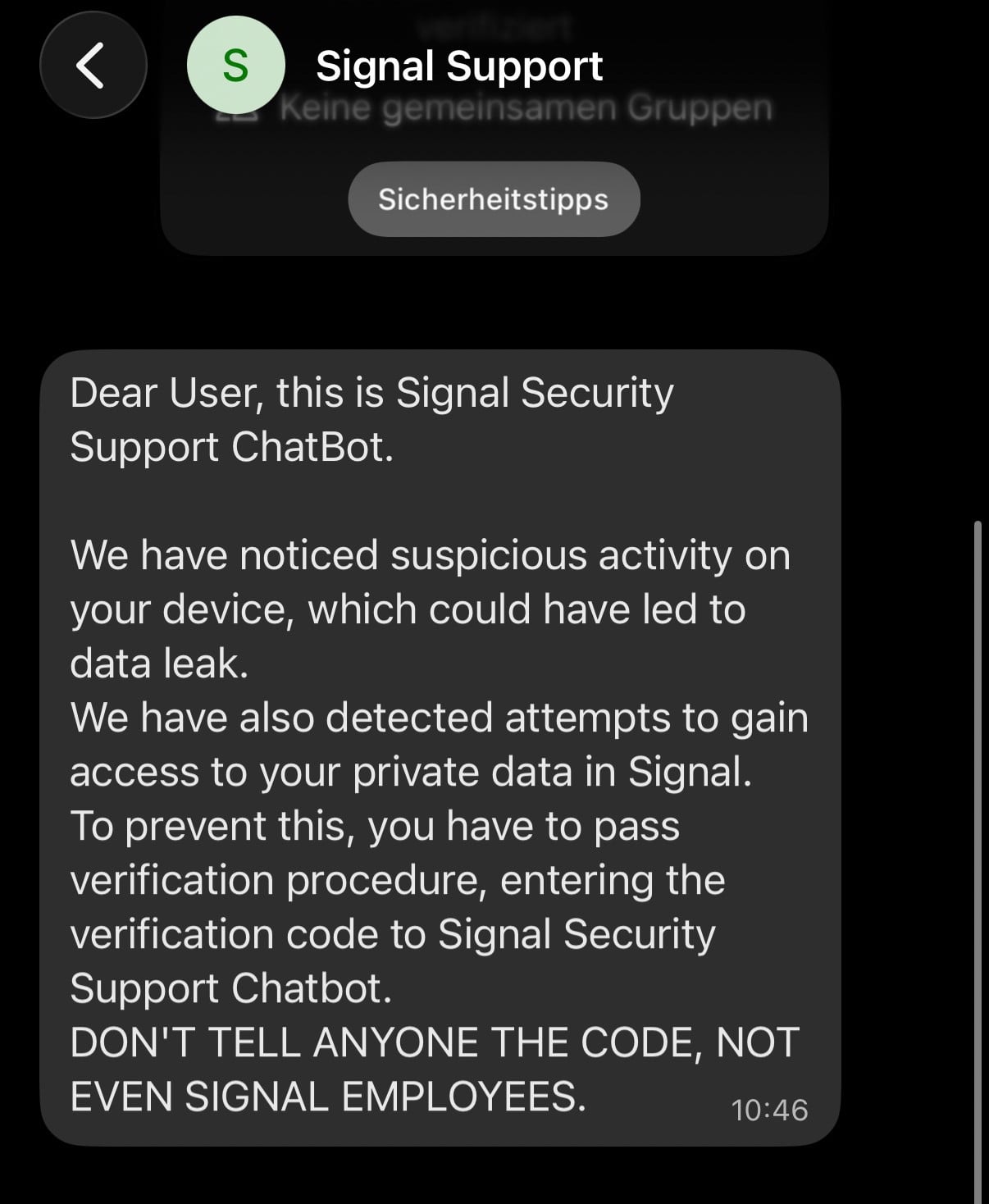
One of the most insidious vectors detailed in the joint Dutch advisory involves a highly targeted phishing sequence masquerading as official support intervention. Threat actors are deploying deceptive messages designed to induce panic and immediate compliance. These messages often arrive under the guise of a "Signal Security Support Chatbot," claiming to have detected anomalous or suspicious activity that poses an imminent threat to the user’s private data or device integrity.
The attacker’s narrative pivots around the necessity of an immediate "verification procedure." This procedure demands the victim input sensitive authentication credentials, specifically the one-time SMS verification code sent to their phone—a code that is typically required only during initial setup or device migration—and, critically, the user’s private Signal Personal Identification Number (PIN). By tricking the user into voluntarily surrendering these two essential keys, the adversary gains the necessary leverage to execute a full account takeover.
The technical consequence of this information handover is devastating for the target. Upon obtaining the SMS code and PIN, the malicious actor can register the victim’s phone number on their own controlled device. Crucially, the attackers can then immediately sever the legitimate user’s access by reassigning the account to a different, attacker-controlled phone number. This act effectively locks out the rightful owner while granting the adversary full, real-time access to the compromised account’s message streams, contact lists, and group memberships.
The Illusion of Recovery: A Subtle Post-Compromise Trap
What makes this particular attack scenario exceptionally dangerous, as highlighted by the AIVD and MIVD, is the potential for the victim to remain unaware of the breach for an extended period. Signal, in its architecture, stores all chat history locally on the user’s device. When the legitimate user, now locked out, attempts to recover their service using their existing telephone number, they are able to successfully register a new account. Because this process restores their historical local message database, the victim may review their past conversations and erroneously conclude that no unauthorized activity has taken place.
This perception of normalcy is a critical failure point in threat detection. As the intelligence agencies explicitly warned, the victim’s assumption that "nothing is wrong" could be dangerously incorrect. While the victim regains access to past data, the attacker retains persistent monitoring capabilities on the newly registered account linked to the original number, or they may continue monitoring through the old, hijacked number if the attacker chose a different registration path. The psychological element here is potent: the victim feels they have simply re-secured their account, whereas the adversarial persistence remains intact or has merely shifted posture.

Signal itself has publicly acknowledged these highly targeted phishing campaigns, firmly stating that the security of their core encryption and infrastructure remains unbreached. Their response underscores that these breaches are sophisticated external social engineering operations designed to subvert user security protocols, rather than flaws in the end-to-end security model itself.
Weaponizing Device Linking: Covert Surveillance
Beyond the full account takeover method, the advisory details a second, more subtle attack vector that targets the device linking features ubiquitous in modern secure messaging. Both Signal and WhatsApp offer functionality that permits users to link secondary devices—such as desktop clients, tablets, or web interfaces—to their primary mobile account. This linking process universally relies on the user scanning a unique QR code presented by the secondary device using their primary mobile application, thereby authorizing synchronization of messages.
In this attack variant, threat actors entice victims into scanning a malicious QR code or clicking a specially crafted link, often disguised as an invitation to a specialized, high-stakes group chat or a verification process initiated by a seemingly trusted contact. When the victim complies, instead of linking a legitimate secondary device, they are unknowingly linking the attacker’s endpoint to their active account.
The implications of a successful device link are profound. The attacker gains the ability to read current message streams, monitor ongoing conversations in real-time, and transmit messages disguised as the legitimate user. A key differentiator here is that, unlike a full account hijack where the victim is locked out, the victim often retains continuous access to their own primary device. This persistence of access on the victim’s side makes detection exponentially harder, as there is no immediate system alert or lockout notification to trigger suspicion. The surveillance is effectively invisible to the primary user.
Industry Implications and the Erosion of Trust
The targeting of government and military personnel underscores a critical shift in cyber espionage priorities. While initial phishing campaigns often targeted broad corporate bases, this focused effort on individuals with access to sensitive state secrets demonstrates an adversary seeking maximum intelligence yield with minimal technical noise. The reliance on messaging apps stems from their perceived security posture; targets often default to E2EE applications believing they are entirely safe from state-level interception, a belief these attacks systematically dismantle.
The industry implication here extends beyond mere application security; it challenges the concept of "secure communication" in the public sphere. For high-stakes environments, the efficacy of E2EE is fundamentally dependent on the user’s operational security (OPSEC). When state actors successfully engineer social exploits that bypass cryptographic safeguards, it forces a re-evaluation of security stacks. Organizations are now compelled to implement stricter policies regarding the use of personal communication devices for classified discussions, regardless of the application’s encryption status.
Furthermore, this highlights a systemic challenge for platform providers. While Signal and WhatsApp cannot control the external environment or user gullibility, they bear the responsibility of mitigating user-facing risks. Signal’s immediate transparency is commendable, but the continued viability of device linking and PIN recovery mechanisms as potential attack surfaces requires ongoing scrutiny. Security experts often argue that multi-factor authentication (MFA) implemented via SMS is inherently weaker than application-based TOTP (Time-based One-Time Password) solutions precisely because of the susceptibility of SMS to interception or—as seen here—social engineering leverage during account recovery.
Expert Analysis: The Blurring Line Between Cyber Espionage and Human Exploitation
From a threat intelligence perspective, these operations are textbook examples of low-cost, high-reward cyber espionage. Developing zero-day exploits for encrypted platforms is resource-intensive and yields limited scalability. In contrast, engineering a convincing phishing lure tailored to the victim’s perceived operational context—such as flagging "suspicious activity" on a device used for sensitive communication—requires far less technical sophistication but guarantees high success rates against well-placed targets.
The attribution to Russian state-sponsored groups is consistent with established patterns of targeting Western governmental and journalistic infrastructure to influence policy, gather intelligence ahead of geopolitical events, or preemptively identify sources and methods. The objective is clear: to establish persistent, covert channels into decision-making ecosystems.
The persistence of these techniques suggests that previous alerts, including those last year targeting Signal’s device linking and other campaigns exploiting WhatsApp’s functionality, have not deterred the actors. This indicates that the threat groups view the risk of exposure as outweighed by the intelligence gain, or they have successfully adapted their lures to evade detection by security-aware personnel.
Future Impact and Mitigation Trends
The immediate future of secure communications defense will likely focus on hardening user behavior and enhancing platform countermeasures against these specific social engineering workflows.
-
Enhanced PIN and SMS Code Protocols: Messaging platforms may need to explore ways to decouple the SMS recovery code—the most vulnerable element—from the PIN requirement during registration, or introduce additional friction points that are harder to automate or socially engineer, such as requiring biometric confirmation on the primary device before broadcasting a recovery code.
-
Proactive Device Linking Audits: For organizations handling sensitive data, mandatory, frequent auditing of linked devices across all communication platforms will become standard procedure, not merely a recommendation. Users must be trained to manually check and revoke unknown linked sessions immediately upon any system notification or behavioral anomaly.
-
Contextual Security Awareness Training: Traditional phishing training is insufficient. Training must evolve to simulate application-specific exploits, demonstrating exactly how an attacker can abuse recovery flows, QR codes, and device linking in real-time scenarios relevant to their day-to-day use of Signal and WhatsApp. The psychological manipulation inherent in the "support chatbot" narrative must be explicitly addressed.
-
Adoption of Hardware Security Keys: For the highest tiers of government and military personnel, a decisive shift away from SMS-based recovery toward physical hardware security keys (e.g., FIDO2 standards) for primary account authentication is the logical next step. While this adds logistical overhead, it effectively neutralizes the social engineering vector that relies on tricking users into reading out codes from their phones.
In conclusion, the warning from the Dutch services serves as a stark reminder that in the realm of state-sponsored cyber conflict, the encryption strength of the protocol is only as strong as the weakest link: the end-user. Adversaries have successfully pivoted from costly technical infiltration to highly effective, low-cost human exploitation against the world’s most trusted messaging platforms.