The United States Cybersecurity and Infrastructure Security Agency (CISA) has issued an urgent directive compelling federal agencies to immediately remediate specific security vulnerabilities within Apple’s iOS operating system. This directive stems from intelligence indicating that these flaws are being actively weaponized by sophisticated threat actors utilizing the potent Coruna exploit kit, an arsenal capable of facilitating both targeted cyberespionage and increasingly, opportunistic financial crimes such as cryptocurrency theft. The swift action underscores the escalating risk associated with zero-day exploitation targeting mobile ecosystems, particularly when such exploits transition from the realm of state-sponsored surveillance to financially driven criminal enterprises.
The foundation of CISA’s alert rests upon recent, in-depth analysis conducted by researchers at Google Threat Intelligence Group (GTIG). Their findings illuminated the complex architecture of the Coruna exploit kit, which functions not as a singular vulnerability lever, but as a multi-stage attack framework chaining together exploitation attempts against a significant portfolio of 23 distinct iOS security weaknesses. Crucially, many of these vulnerabilities were confirmed to have been leveraged in previous zero-day capacities, meaning they were exploited in the wild before Apple was aware or had released patches. This history elevates the severity classification, as zero-day exploits represent the highest tier of immediate threat due to the complete absence of pre-emptive defenses.
A crucial nuance in the GTIG disclosure, and a factor influencing the scope of the immediate federal mandate, is the mitigation profile of the attack chain. The Coruna exploit sequence, while formidable against older or unpatched systems, exhibits limitations against modern iOS defenses. Specifically, the successful execution of the exploit chain is reportedly thwarted if the target device is utilizing Apple’s Private Browsing feature within Safari or, more significantly, if the device has the advanced anti-spyware safeguard, Lockdown Mode, enabled. Lockdown Mode, introduced by Apple to protect high-risk users, imposes stringent limitations on device functionality, effectively hardening the attack surface against complex remote code execution attempts like those inherent in the Coruna methodology.
From a technical perspective, the capabilities unlocked by a successful Coruna deployment are profoundly concerning. The exploit kit is designed to systematically dismantle layers of iOS security architecture. It furnishes threat actors with the necessary tools to bypass crucial hardware-backed security measures, including Pointer Authentication Code (PAC) bypass mechanisms. Following this, the kit executes a sandbox escape, allowing malicious code to break free from the restricted operational environment mandated for applications. Perhaps most critically, it achieves a Page Protection Layer (PPL) bypass. PPL is a critical kernel-level defense designed to prevent unauthorized modification of memory pages. Successfully subverting PPL grants the attacker the ability to achieve WebKit Remote Code Execution (RCE) and subsequently escalate privileges all the way to the highly coveted Kernel level, effectively granting total, unmonitored control over the compromised device.
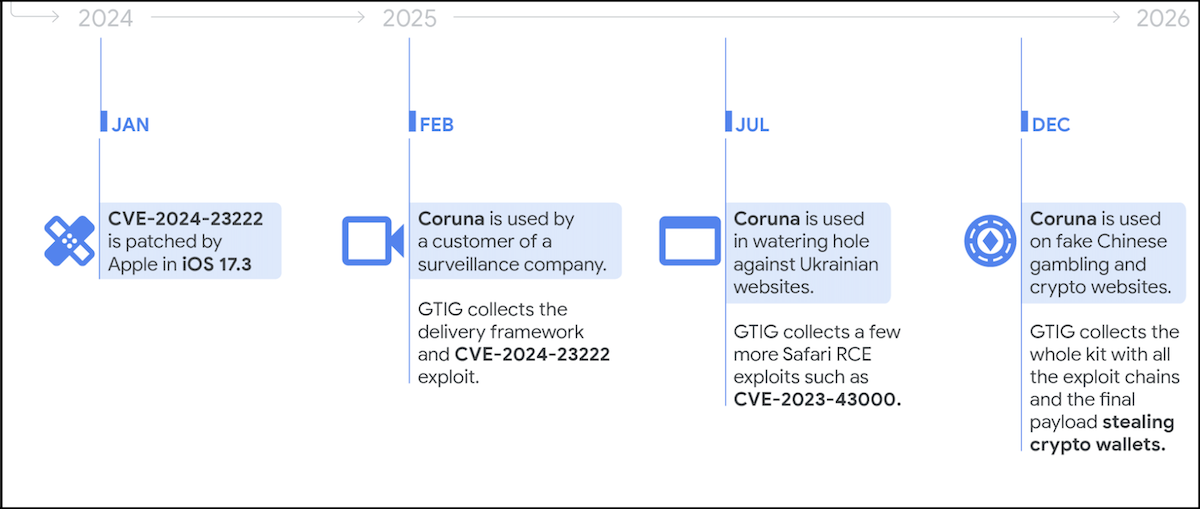
The observed deployment patterns of Coruna paint a troubling picture of threat actor convergence. GTIG analysis revealed the exploit kit’s utilization by a diverse array of malicious entities throughout the preceding year. This includes entities associated with established surveillance vendor customers—suggesting initial development or use within government-grade intelligence circles—as well as groups traditionally linked to nation-state activities, such as the suspected Russian state-sponsored actor designated UNC6353. Furthermore, the kit has fallen into the hands of financially motivated Chinese threat actor groups, exemplified by UNC6691.
The financially motivated use case highlights a dangerous evolution. UNC6691 was observed deploying Coruna through social engineering vectors disguised as legitimate digital platforms, specifically fake gambling and cryptocurrency exchange websites. Upon infection, the ultimate payload delivered was tailored for financial gain: malware specifically engineered to locate, access, and exfiltrate the victim’s cryptocurrency wallet credentials. This transition signals the commoditization of what were previously considered "spyware-grade" capabilities.
This migration path was further substantiated by independent analysis from mobile security specialists at iVerify. They characterized Coruna as a textbook example of advanced surveillance technology—once the exclusive domain of highly resourced commercial entities selling to government clients—now migrating into the operational toolkit of established nation-state actors and, increasingly, large-scale organized criminal syndicates. This democratization of high-end exploit technology lowers the barrier to entry for complex mobile compromise across the threat landscape.
In response to this mounting evidence, CISA formalized the threat by formally adding three of the 23 identified Coruna vulnerabilities to its authoritative Catalog of Known Exploited Vulnerabilities (KEV) on Thursday. Inclusion in the KEV catalog triggers mandatory remediation deadlines under Binding Operational Directive (BOD) 22-01 for all Federal Civilian Executive Branch (FCEB) agencies. The directive mandates that these specific flaws must be mitigated—either through patching according to vendor instructions, applying alternative security configurations for cloud services as per BOD 22-01 guidelines, or entirely discontinuing the use of the affected product if patching is unfeasible—by the strict deadline of March 26th.

CISA’s public advisory emphasized the systemic risk these vulnerabilities pose: "These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise." This statement serves as a clear signal that infrastructure security teams must treat these specific CVEs with the highest level of urgency, recognizing their proven efficacy in enabling deep system compromise.
While BOD 22-01’s legal jurisdiction is confined to federal entities, CISA explicitly extended its recommendation to the broader digital ecosystem. The agency strongly urged all organizations, particularly those within the private sector that handle sensitive data or manage critical infrastructure, to prioritize the patching of these iOS flaws immediately. The logic is irrefutable: if a tool is known to be actively used by sophisticated adversaries against government targets, it presents an equally potent threat to corporate environments handling intellectual property, financial data, or customer information.
Industry Implications: The Commodification of Exploitation Chains
The Coruna revelations represent more than just a technical vulnerability disclosure; they signify a critical inflection point in the cyber arms race. The migration of "spyware-grade" capabilities—those traditionally requiring immense resources, zero-day research, and specialized infrastructure—into the hands of financially motivated cybercriminals has profound industry implications.
Firstly, it accelerates the obsolescence of traditional mobile security postures. Security teams historically focused on application-layer threats or known malware signatures. Coruna, however, operates at the kernel and hardware-abstraction layer, bypassing many conventional endpoint detection and response (EDR) solutions designed for desktop or server environments. This necessitates a complete re-evaluation of mobile device management (MDM) and security strategies, pushing defense toward proactive, firmware-level integrity checks and rigorous adherence to operating system update cycles.
Secondly, the involvement of financially motivated groups leveraging state-level exploit technology signals a dangerous merger between cyber-espionage capabilities and organized crime economics. While state actors seek geopolitical advantage or intelligence, criminal groups seek direct monetization. The successful deployment of Coruna for crypto-theft validates the return on investment for acquiring or developing such advanced exploit chains. This incentivizes further investment in exploit research across the criminal underworld, potentially leading to a flood of similarly capable toolkits entering the market.
The presence of UNC6353, a suspected Russian state actor, alongside UNC6691, a financially driven group, also suggests potential cross-pollination or the sale of exploit access. Nation-state actors might monetize their zero-day research by selling limited access or components of their toolkits to criminal syndicates, creating a lucrative secondary market that further destabilizes the global security landscape. For organizations relying on Apple’s default security architecture, this means the threat profile has fundamentally shifted from generic hacking to targeted, highly sophisticated infiltration.
Expert-Level Analysis: Deciphering Kernel Privilege Escalation
To fully appreciate the threat posed by Coruna, one must dissect the significance of the bypassed security mechanisms. The three primary bypasses—PAC, Sandbox, and PPL—represent a systematic dismantling of Apple’s layered security model, which is rooted in techniques pioneered by the iPhone Secure Enclave and subsequent architectural hardening efforts.
Pointer Authentication Code (PAC) Bypass: PAC leverages specialized CPU features (like ARMv8.3-A) to cryptographically sign pointers in memory, ensuring that memory addresses cannot be tampered with by injecting malicious code. Bypassing PAC indicates the attackers have found a way to either forge these signatures or exploit logic flaws in how PAC is implemented or verified during execution flow. This is a low-level victory, essential for redirecting program execution flow to attacker-controlled code paths.
Sandbox Escape: The iOS sandbox is designed to isolate applications from the core operating system and other applications. A successful escape means the malware, initially contained within the limited permissions of a compromised application (perhaps via a malicious browser rendering engine like WebKit), gains the ability to interact with system files, access sensitive application data, or execute system-level calls.
Page Protection Layer (PPL) Bypass: PPL is arguably the most critical defense overcome by Coruna. PPL operates at the hardware memory management unit (MMU) level, enforcing strict permissions on physical memory pages, preventing any process—even those with elevated privileges—from writing to kernel-protected memory regions. Achieving a PPL bypass allows the attacker to overwrite kernel code or data structures directly, fundamentally corrupting the integrity of the operating system state. This permits the final leap to Kernel privileges, ensuring persistence, complete data exfiltration, and the ability to implant rootkits or other stealthy backdoors that survive reboots.
The ability to chain these three complex exploits together is what defines Coruna as "spyware-grade." It signifies mastery over multiple, disparate security domains within the iOS kernel and hardware architecture.
Future Impact and Trends: Defense Against Exploit Commoditization
The CISA directive serves as a necessary stopgap, but the long-term response requires systemic changes. The trend of high-fidelity exploit chains moving from government surveillance tools to criminal finance operations is set to accelerate, driven by the immense profitability of cryptocurrency theft and the availability of advanced exploit brokers.
Trend 1: Focus on Proactive Hardening Over Reactive Patching: Given the zero-day nature of the vulnerabilities exploited by Coruna, organizations must pivot toward defenses that assume compromise is inevitable. This involves increased reliance on application whitelisting, stringent network segmentation for mobile devices, and, where feasible, mandating the use of advanced protection features like Apple’s Lockdown Mode for employees handling highly sensitive information, even if it impacts some day-to-day convenience.
Trend 2: Elevated Risk Assessment for Mobile Endpoints: Mobile devices can no longer be treated as secondary endpoints protected solely by basic passwords or MDM profiles. They must be treated with the same rigor as servers regarding patching cadence, configuration management, and continuous monitoring for anomalous kernel behavior, which advanced mobile threat detection (MTD) solutions aim to provide.
Trend 3: International Regulatory Convergence: As exploit kits like Coruna cross national boundaries to target financial assets, there will likely be increased pressure for international coordination regarding vulnerability disclosure and mandatory patching timelines, especially concerning mobile platforms used globally by government and critical infrastructure personnel. CISA’s public alert functions as a soft form of this coordination, urging the global community to adopt similar urgent remediation steps.
Ultimately, the Coruna exploit kit underscores a fundamental truth in modern cybersecurity: the sophistication gap between defenders and determined attackers is constantly narrowing, particularly when state-level research methodologies are absorbed by profit-driven criminal organizations. For federal agencies and the private sector alike, the immediate remediation of these three critical iOS flaws is the first, non-negotiable step in adapting to this evolving, high-stakes threat environment. Failure to address these weaknesses risks not just data breaches, but potentially catastrophic loss of control over mission-critical mobile platforms.

