A highly capable, China-attributed advanced persistent threat (APT) cluster, designated UAT-9244 by threat intelligence specialists, has been systematically infiltrating telecommunication service providers across South America since the beginning of 2024. The campaign’s scope is notable for its broad target range, successfully compromising systems spanning traditional Windows endpoints, various Linux distributions, and critical network-edge devices essential for carrier operations. This persistent reconnaissance and compromise campaign signifies a focused effort to gain deep access within vital regional communication backbones.
Research conducted by Cisco Talos indicates a strong, though not definitively proven, linkage between UAT-9244 and established Chinese espionage entities, specifically mentioning associations with the threat actors historically tracked as FamousSparrow and Tropic Trooper. While UAT-9244 operates as a distinct activity cluster, the high confidence in this assessment stems from overlapping methodologies, shared families of tooling, and strikingly similar victim profiles observed across attacks previously attributed to these well-known groups. Intriguingly, the researchers also acknowledge that UAT-9244 targets a profile consistent with another known actor, Salt Typhoon, yet they have not yet established a concrete, verifiable connection connecting the two operationally. This divergence in attribution, despite overlapping targets, suggests either a sophisticated compartmentalization strategy by the sponsoring entity or the deployment of shared, modular toolsets across loosely affiliated groups.
The current campaign distinguishes itself through the deployment of an entirely new, undocumented suite of malware families, tailored for diverse operating environments common within telecommunications infrastructure. This arsenal comprises three primary components: TernDoor, a specialized backdoor for Windows environments; PeerTime, a Linux-focused backdoor that leverages the BitTorrent protocol for covert communications; and BruteEntry, a dedicated reconnaissance tool designed to establish resilient proxy infrastructure, often referred to as Operational Relay Boxes (ORBs).
Deep Dive into the Bespoke Toolset
The deployment of TernDoor on Windows systems showcases a refined approach to evading detection, relying on the well-established technique of DLL side-loading. The threat actor initiates this by executing the legitimate, signed Windows executable, wsprint.exe. This benign process is then manipulated to load malicious code residing in BugSplatRc64.dll. Upon loading, the malicious DLL executes a decryption routine in memory, ultimately injecting the final payload into the msiexec.exe process space, effectively hiding its execution from simpler endpoint monitoring tools.

Further cementing its foothold, TernDoor incorporates an embedded Windows driver, named WSPrint.sys. This driver grants the attacker low-level system control, specifically enabling the termination, suspension, and resumption of arbitrary processes—a powerful capability for neutralizing defensive applications or ensuring the continued operation of the malware itself. Persistence within the compromised host is meticulously established through the creation of scheduled tasks, coupled with targeted modifications to the Windows Registry. Critically, the malware employs registry manipulation to actively obscure the presence of the scheduled task itself, complicating forensic analysis aimed at discovering the method of re-activation. Once established, TernDoor offers a comprehensive remote shell capability, allowing threat actors to issue arbitrary commands, manage files across the system, exfiltrate configuration data, and execute a self-uninstallation routine if necessary.
The threat actor’s attention to Linux environments, particularly crucial in carrier networks hosting network functions and specialized hardware, is highlighted by PeerTime. This ELF (Executable and Linkable Format) backdoor is architecturally agnostic, explicitly compiled to target multiple processor architectures, including ARM, AARCH, PPC, and MIPS. This multi-architecture support strongly implies the malware was purpose-built to infect a wide array of embedded systems and specialized network appliances—precisely the types of devices underpinning modern telecom infrastructure.
The development of PeerTime exhibits modern coding practices; Cisco Talos analysis identified two distinct variants: one written in traditional C/C++ and a second variant built upon the Rust programming language. The presence of Simplified Chinese debug strings within the instrumentor binary of at least one variant provides a strong, though not definitive, indicator of the development team’s origin. Execution involves in-memory decryption and loading of the payload, followed by the renaming of the malicious process to mimic a legitimate system service, a classic evasion tactic.
What makes PeerTime particularly challenging to track is its Command and Control (C2) methodology. It functions as a peer-to-peer (P2P) backdoor utilizing the widely used BitTorrent protocol. This decentralized communication method obscures C2 traffic within legitimate network flows, making traditional firewall rules or signature-based network monitoring significantly less effective. PeerTime can solicit new commands and download secondary payloads directly from other compromised peers within the infected network swarm, relying on the BusyBox utility to write these newly acquired files onto the host system.
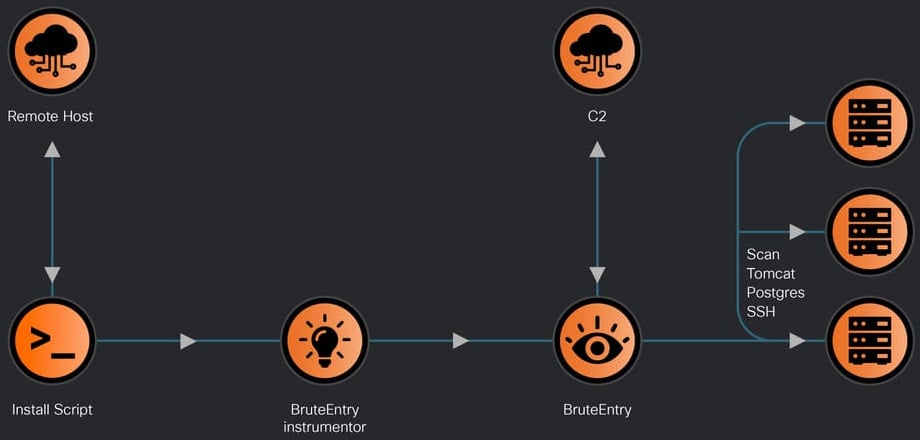
Rounding out the toolkit is BruteEntry, which serves a distinct, infrastructure-building role. This component consists of a Go-based instrumentor binary coupled with a dedicated brute-forcing engine. The primary objective of BruteEntry is the transformation of already compromised devices into scanning nodes, or ORBs, thereby expanding the attacker’s network reach and resilience. Devices running BruteEntry are tasked with actively scanning the external internet or internal network segments for new, vulnerable targets. The brute-force component focuses specifically on common, high-value network services: SSH, PostgreSQL (Postgres), and Apache Tomcat web servers. Crucially, the results of these login attempts, including successful credentials or failure reports, are relayed back to the primary C2 infrastructure, providing operational feedback on the status of the ongoing reconnaissance and enumeration tasks.

Industry Implications and Strategic Context
The targeting of telecommunication providers by state-sponsored actors is not a novel phenomenon, but the sophistication and breadth of the UAT-9244 toolkit present escalated concerns. Telecommunications networks are the fundamental arteries of modern digital economies, carrying government, military, financial, and civilian traffic. Compromising these entities provides an adversary with unparalleled opportunities for mass surveillance, data exfiltration, and the potential for strategic disruption or sabotage in times of geopolitical tension.
The focus on South America suggests a deliberate strategy to gain intelligence foothold in regions experiencing rapid digital transformation and potentially facing less mature state-level cybersecurity defenses compared to North American or European markets. By compromising network edge devices and embedded systems—often overlooked in standard endpoint security sweeps—UAT-9244 achieves a level of persistence and visibility deep within the network architecture that is extremely difficult to eradicate once established.
The adoption of P2P C2 via BitTorrent (PeerTime) represents an evolution in operational security for the threat actor. Traditional APTs often rely on fixed C2 domains or IP addresses, which security vendors can rapidly sinkhole or block. A P2P network, however, distributes the C2 responsibility across the victim pool itself, making complete disruption significantly harder. The malware becomes self-sustaining and highly resilient to takedown efforts.
Furthermore, the use of multiple languages in the toolset (Rust, C/C++, Go) and the cross-platform nature of PeerTime indicate a mature development pipeline, capable of producing specialized, optimized code for specific operational environments rather than relying on generic, easily detectable cross-platform frameworks. The presence of Rust in PeerTime is particularly noteworthy; while still niche in malware development, Rust offers memory safety features that can complicate traditional exploitation analysis, potentially leading to more stable and robust backdoors.
Expert Analysis of Evasion and Persistence
The methodology employed by UAT-9244 demonstrates a clear understanding of modern security monitoring paradigms. TernDoor’s reliance on DLL side-loading via a legitimate, signed Microsoft executable (wsprint.exe) is a technique designed to bypass application whitelisting controls and confuse static analysis tools that might flag unsigned executables. Injecting the final payload into msiexec.exe leverages a process already trusted by the operating system to perform system-level tasks, masking malicious activity under the guise of routine installation services. The kernel-level interaction provided by the embedded driver (WSPrint.sys) allows the attacker to manipulate the operating system at a foundational level, giving them the capability to terminate security agents or manipulate logging mechanisms without alerting standard user-mode security products.
BruteEntry’s function as an ORB builder highlights a key element of state-sponsored cyber operations: infrastructure development. By turning compromised telco equipment into proxies, the threat actor achieves several tactical advantages: they anonymize their subsequent attacks, increase their available bandwidth for data staging, and distribute the risk of discovery across a wide network of compromised victims. This strategy shifts the focus from simple data theft to building a long-term, deniable platform for future espionage or potential disruption operations. The targeting of SSH, Postgres, and Tomcat is highly tactical, as these services are frequently used for administrative access, database backend connections, and web application hosting within enterprise and carrier environments, respectively.
The attribution assessment, while high confidence regarding association with known Chinese clusters, underscores the current difficulty in definitively mapping distinct campaigns. APTs frequently share toolkits, personnel, and strategic objectives. The lack of a "solid connection" to Salt Typhoon, despite similar victimology, suggests that these groups may operate with a degree of operational separation—perhaps designed to provide plausible deniability should one cluster be discovered and analyzed extensively.
Future Impact and Defensive Strategies
The UAT-9244 campaign serves as a potent indicator that the threat landscape targeting critical infrastructure, particularly telecommunications, is intensifying and specializing. Future attacks are likely to further leverage P2P protocols for C2 and increase the utilization of multi-architecture malware targeting specialized network hardware, moving beyond conventional server and workstation compromise.
For defenders within the telecommunications sector, the immediate priority must shift toward anomaly detection within network traffic and process behavior, rather than relying solely on signature matching. Specific defensive actions must include:
- Hardening Edge Devices: Implementing strict segmentation and disabling unnecessary administrative protocols (like exposed SSH or management interfaces) on network edge hardware and embedded systems, especially those running non-standard operating systems susceptible to ARM/MIPS exploitation.
- Monitoring Process Injection: Deploying advanced endpoint detection and response (EDR) solutions capable of detecting unusual parent-child process relationships (e.g., wsprint.exe spawning unexpected code execution paths or process hollowing into msiexec.exe).
- Decentralized C2 Detection: Developing and deploying network security monitoring tools capable of identifying unusual P2P protocol usage patterns, particularly those exhibiting high-frequency communication with unknown or dynamically changing peers, which can signify BitTorrent-based C2.
- Proactive Driver Analysis: Enhancing scrutiny of kernel-mode drivers loaded onto systems, as the use of custom drivers like WSPrint.sys for process manipulation is a hallmark of highly persistent, sophisticated intrusions.
The emergence of UAT-9244, armed with TernDoor, PeerTime, and BruteEntry, reinforces the reality that state-sponsored adversaries are investing heavily in bespoke, resilient toolsets designed specifically to overcome modern defensive layers in the world’s most critical digital infrastructure. Continuous, adaptive threat intelligence and proactive architectural hardening remain the only viable defense against such persistent, evolving threats.

