The recent unveiling of the 2026 State of Browser Security Report paints a stark picture for cybersecurity professionals: the corporate browser has fundamentally transformed, yet security postures remain dangerously anchored to legacy assumptions. Data compiled throughout 2025 indicates that the browser has decisively transitioned from a mere application gateway to the de facto operating system for modern knowledge work, creating profound, often unaddressed, security vulnerabilities across the enterprise landscape. This report marks 2025 as the definitive inflection point where AI-native browser capabilities graduated from niche experimentation into ubiquitous business functionality.
The Browser’s Metamorphosis: From Viewer to Executor
To fully grasp the gravity of the security deficit highlighted by the report, one must appreciate the sheer scope of the browser’s evolution over the preceding twelve months. Historically, the browser served as a relatively passive rendering engine—a window through which users accessed Software-as-a-Service (SaaS) platforms. That paradigm is obsolete. The contemporary browser is now an active, dynamic execution environment.
The integration of sophisticated Artificial Intelligence—manifested through embedded copilots within enterprise applications and standalone generative interfaces—has fundamentally altered user interaction. Employees are no longer just clicking links; they are tasking the browser environment to read sensitive data streams, synthesize complex information, draft critical communications, automate multi-step workflows, and generate operational code. In essence, the browser context has become the primary intersection point where productivity is realized and sensitive data is processed.
This elevation of the browser’s functional role contrasts sharply with its security treatment. In the majority of large organizations, security architectures still categorize the browser as a peripheral concern, managed primarily through rudimentary network access controls or traditional endpoint detection and response (EDR) agents. These legacy frameworks were never designed to monitor, govern, or inspect the granular, in-session activities—such as real-time data input into AI models or complex lateral movements within a browser context—that define modern productivity. The result, as the 2026 data confirms, is a rapidly expanding security vacuum precisely where the most valuable and dynamic work is occurring.
The Mainstreaming of Generative AI in Workflows
The report’s telemetry from 2025 confirms that Generative AI (GenAI) is no longer an ancillary tool but a deeply embedded component of daily enterprise operations. Keep Aware’s analysis reveals that a significant 41% of all end-users actively engaged with at least one AI web tool during their workday, with the average employee leveraging nearly two (1.91) distinct AI tools per person. This widespread adoption means that activities critical to business continuity—from synthesizing proprietary market research to generating new software modules—are now routed through these AI intermediaries, all initiated and managed within the browser.

This massive uptake highlights a critical governance failure: adoption has drastically outpaced effective oversight. While IT departments might formally approve one or two designated enterprise-grade AI platforms, the reality on the ground is characterized by fragmentation. Driven by convenience or the desire to bypass perceived internal friction, employees routinely utilize personal accounts for high-stakes tasks. This shadow usage bypasses established data loss prevention (DLP) policies, corporate authentication mechanisms, and monitoring controls, embedding significant, unmanaged risk directly into the workflows that rely on these tools.
The risks extend beyond mere prompt engineering. Personnel are actively feeding proprietary source code, unpublished financial forecasts, confidential client data, and regulated personal information into these external AI systems. Because these actions occur within the browser session—often involving copy/paste or file uploads to a web interface—traditional security stack components (like network firewalls or standard endpoint scanners) possess insufficient context or capability to intercept the exfiltration of this high-value information. Security teams are effectively blind to the data’s journey at its most vulnerable stage.
The Illusion of Application Control: Data Leakage in "Trusted" Ecosystems
A significant challenge revealed in the report directly undermines long-standing organizational strategies centered on application whitelisting or blocking. Organizations have traditionally relied on securing known SaaS applications, assuming that blocking access to unapproved sites mitigates data exposure risk. The 2026 findings shatter this assumption, demonstrating that sensitive data exposure is heavily concentrated within the very platforms deemed "trusted."
A month-long audit of authenticated sessions showed that critical data uploads—including intellectual property and PII—were overwhelmingly directed toward established enterprise collaboration suites: SharePoint, Google Workspace services, Slack, and Box. The critical differentiating factor, however, was the identity under which these uploads occurred. Many instances involved employees using personal credentials to upload corporate data into these sanctioned environments, effectively cloaking the activity from enterprise governance structures monitoring only corporate accounts.
This reveals that security controls focused purely on the application layer (e.g., "Is this Slack? Yes? Allow.") are insufficient. The modern threat vector is context-dependent: the risk is not which application is being used, but how it is being used, and crucially, under which authorization it is operating. Legacy DLP tools, architected around monitoring email egress points, network packet inspection, or endpoint file system activity, are fundamentally incapable of inspecting the dynamic, ephemeral actions occurring within a browser tab—such as data typed directly into a chat window or a document pasted into a cloud editor’s web interface. This gap necessitates a shift toward in-session, browser-native visibility.
The Evolving Threat Landscape: Attacks Bypass Perimeter Defenses
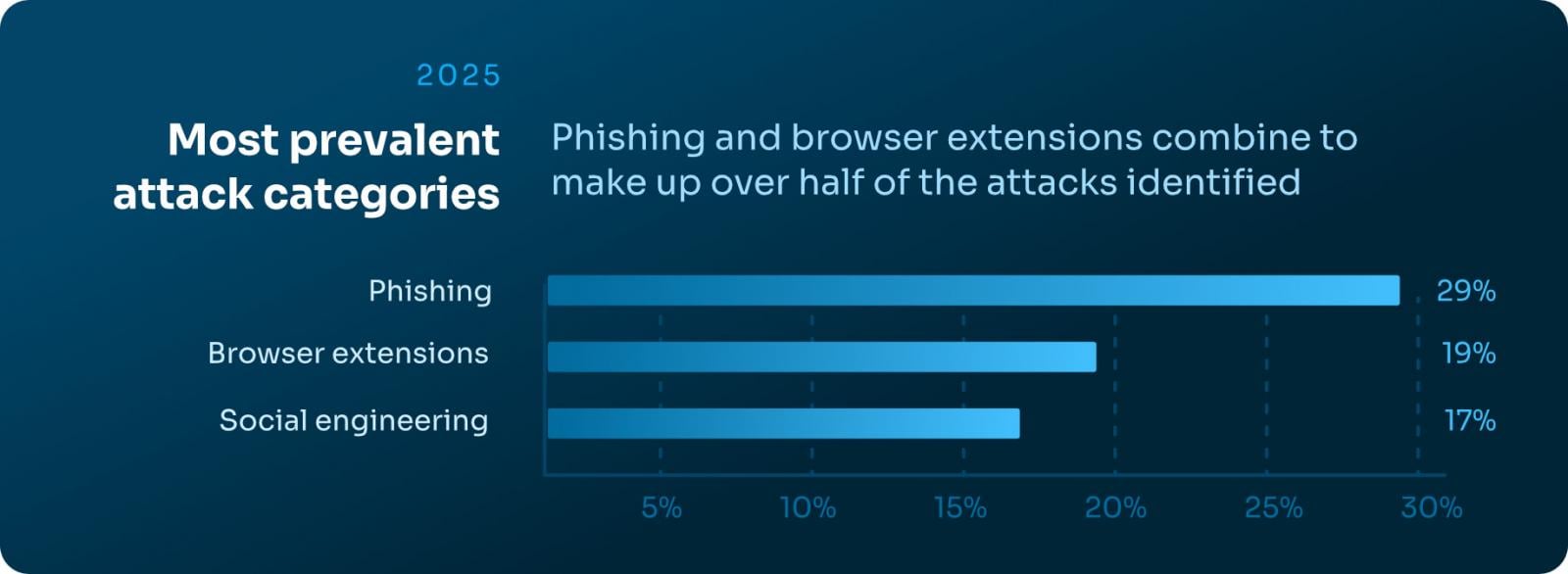
While security teams invested heavily in hardening the traditional trilogy of defenses—email gateways, network perimeters, and endpoint hardening—attackers have logically migrated their focus to the path of least resistance: the user’s browser session. The report details a clear strategic pivot by threat actors, evidenced by the primary attack categories observed throughout 2025.

The data underscores the efficacy of techniques that leverage browser functionality itself:
- Browser-based credential harvesting: Attacks designed not just to steal credentials but to harvest them in real-time as the user interacts with legitimate login prompts, often utilizing sophisticated JavaScript injection or form-grabbing techniques invisible to static network analysis.
- Session Hijacking and Manipulation: Exploits targeting weaknesses in session management or relying on client-side code execution to persist malicious payloads or redirect sensitive actions.
- In-Browser Malware Delivery: Shifting away from traditional executable downloads, attackers now focus on delivering and executing polymorphic or fileless malware directly within the sandbox of the browser, often leveraging memory corruption or sophisticated web assembly exploits.
Furthermore, the analysis of phishing infrastructure reveals a disturbing trend that negates common defensive heuristics. The median age of observed malicious phishing domains exceeded 18 years. This directly invalidates the strategy of relying on blocking "new" or recently registered domains. Attackers are increasingly leveraging decades-old, seemingly trusted infrastructure—perhaps compromised subdomains of legitimate entities or long-dormant domains that have escaped blocklists—to host their current campaigns.
The sophistication of modern social engineering is also contributing to detection evasion. Campaigns frequently employ complex layers designed specifically to defeat automated scanners and threat intelligence feeds: cloaking technology to show benign content to automated bots while serving malicious payloads to human victims, chained redirect structures, and conditional execution gates (like CAPTCHA challenges) that only trigger the final malicious step after initial automated inspection has passed. Consequently, the true nature of the attack is only revealed at the moment of execution within the victim’s active browser session—a moment that traditional security layers have already missed.
The Persistent, Privileged Danger of Browser Extensions
Browser extensions, often perceived as low-risk productivity enhancers, continue to represent a pervasive and dangerously under-governed risk vector within enterprise environments. These add-ons operate with exceptionally high privileges, embedding persistent code directly into the user’s active session, often maintaining this access indefinitely without subsequent security review.
Keep Aware’s 2025 telemetry highlights the severity of this issue: 13% of all unique extensions installed across monitored environments were categorized as posing High or Critical security risk. This statistic is alarming because it demonstrates the routine infiltration of potentially hostile code into production environments via seemingly benign marketplace downloads.
The problem is compounded by the misleading nature of extension categorization. Extensions labeled as "productivity" tools frequently request expansive permissions—access to all cookies, monitoring of all web requests, and read/write access to local storage. Such broad permissions grant the extension deep, continuous visibility into everything the user sees and enters, including credentials, financial data, and proprietary communications. The marketplace labeling offers negligible security assurance; branding sophistication often masks requests for elevated, session-critical privileges.
Static security measures, such as point-in-time extension reviews or static allowlists, are proving increasingly ineffective against the dynamic nature of the extension ecosystem, which sees frequent permission changes and updates. Effective management of this vector demands a paradigm shift toward continuous, behavior-based monitoring—inspecting what the extension actually does with its granted permissions during active browsing, rather than simply trusting its initial claims.
Implications for Future Security Strategy
The convergence of ubiquitous AI tools, the browser’s functional evolution into an OS layer, and the inherent weaknesses in legacy control structures necessitates a radical re-evaluation of enterprise security architecture. The primary finding of the 2026 report is that security must become browser-native.
Future security frameworks must prioritize visibility and control at the point of execution. This requires capabilities that can:
- Contextualize AI Interaction: Monitor the flow of data into and out of generative AI models, regardless of the specific platform or account used.
- Enforce Identity within the Session: Distinguish between corporate and personal identities operating within the same browser window to enforce usage policies granularly.
- Inspect In-Session Behavior: Analyze keystrokes, copy/paste operations, and real-time uploads to block data leakage before it exits the user’s control plane, effectively extending DLP capabilities into the application layer itself.
- Continuously Govern Extensions: Maintain a dynamic risk profile for every installed extension based on its observed behavior, not just its initial description.
The browser is now the central nervous system of digital work. Organizations that continue to treat it as a peripheral access point risk catastrophic data exposure and operational compromise as AI-driven workflows accelerate. The findings compel a strategic mandate: security must move into the browser to match the speed and complexity of modern enterprise activity.

