The landscape of digital security has entered a new, more volatile phase, underscored by the latest findings from Google’s Threat Intelligence Group (GTIG). Their comprehensive review of the 2025 threat environment reveals that security researchers documented 90 distinct zero-day vulnerabilities actively leveraged in real-world attacks throughout the year. This figure represents a significant year-over-year increase, signaling a hardening of adversary tactics and a critical expansion of the attack surface facing global organizations.
This latest tally marks a 15% escalation from the 78 confirmed zero-day exploits tracked in 2024. While this growth pace is substantial, it remains slightly below the peak recorded in 2023, when security vendors grappled with an unprecedented 100 unique, actively exploited zero-days. The consistent elevation of these numbers—hovering near the century mark—suggests that the era of intermittent zero-day discoveries is over, replaced by a steady, industrialized flow of high-value exploits.
The Anatomy of a High-Value Exploit
To contextualize the gravity of these numbers, one must understand the inherent value of a zero-day. These are security flaws within commercial software or hardware that have not yet been publicly disclosed, meaning the vendor lacks a tested patch. For threat actors—whether state-sponsored entities, criminal syndicates, or commercial surveillance firms—a zero-day represents an unadulterated key capable of bypassing conventional defenses. Their primary utility lies in achieving crucial initial footholds: establishing remote code execution (RCE), escalating user privileges to administrative levels, or bypassing established authentication mechanisms.
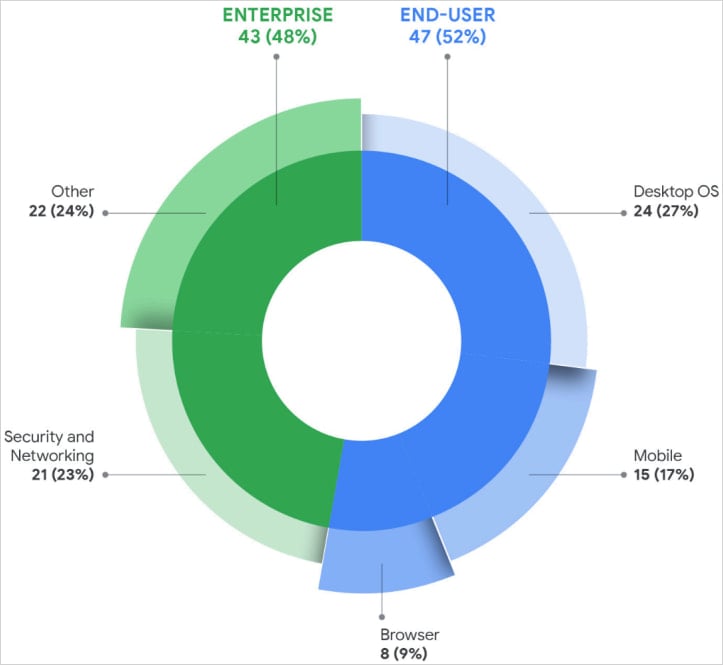
The GTIG analysis segments the 90 exploited zero-days based on their target architecture. The distribution reveals a tactical shift toward infrastructure: 47 vulnerabilities affected end-user platforms, while a slightly smaller, yet critically important, 43 targeted enterprise software and appliances. This near-even split highlights a dual strategy: maintaining access to individual endpoints while simultaneously compromising the centralized systems that manage entire networks.
The technical nature of these exploited flaws further informs the current threat model. The catalog of vulnerabilities exploited in 2025 included the typical suspects: RCE, privilege escalation, injection flaws (like SQL or command injection), deserialization vulnerabilities, and authorization bypasses. However, a dominant underlying factor was memory corruption bugs, specifically use-after-free (UAF) issues. Google researchers determined that memory safety vulnerabilities accounted for a substantial 35% of all zero-days exploited last year. This percentage underscores the industry-wide challenge inherent in managing complex, memory-unsafe languages like C and C++, which still underpin vast swathes of critical infrastructure.

The Infrastructure Target: Where the Exploits Land
The concentration of enterprise exploitation offers significant insight into attacker objectives. The most frequently compromised enterprise systems were not merely standard servers but components vital for network integrity and access control: security appliances, core networking infrastructure, Virtual Private Networks (VPNs), and virtualization platforms.
The rationale behind targeting these assets is straightforward from an adversary’s perspective. These systems often possess inherent trust within the network perimeter. Furthermore, many legacy or specialized appliances frequently lag in robust Endpoint Detection and Response (EDR) coverage compared to standard workstations or servers, creating blind spots ideal for long-term, covert persistence. Compromising a VPN gateway, for example, grants an attacker an always-on, authenticated pathway deep into the corporate topology.
Operating systems remained the most heavily targeted software category overall. Attacks leveraging zero-days against these foundational layers comprised 24 exploits in desktop operating systems and 15 in mobile platforms. This heavy focus confirms that operating systems remain the ultimate prize, offering comprehensive control over the environment.
Conversely, the exploitation of zero-days within web browsers saw a pronounced downturn, dropping to just eight documented instances in 2025. This decline is a significant departure from previous years. Google analysts suggest this may be a positive indicator, potentially reflecting years of dedicated security hardening within major browser engines, including sandboxing improvements and more rigorous memory safety enforcement in JavaScript engines. However, an equally plausible, and more concerning, alternative explanation is that threat actors are evolving. They may be shifting their focus to exploiting vulnerabilities after initial access is gained, or they are employing far more sophisticated evasion techniques to mask their browser-based intrusions from detection mechanisms designed to catch traditional exploit chains.
Vendor Exposure and Shifting Allegiances
Analyzing which vendors bore the brunt of these attacks provides a clear map of the immediate risk landscape. Microsoft was identified as the vendor facing the highest volume of zero-day exploitation, with 25 documented vulnerabilities leveraged against its products. This is consistent with its ubiquitous presence across enterprise environments, making it a high-yield target. Google followed with 11 exploited zero-days, trailed by Apple with eight. Vendors specializing in infrastructure—Cisco and Fortinet—each saw four exploits, while Ivanti and VMware accounted for three apiece.
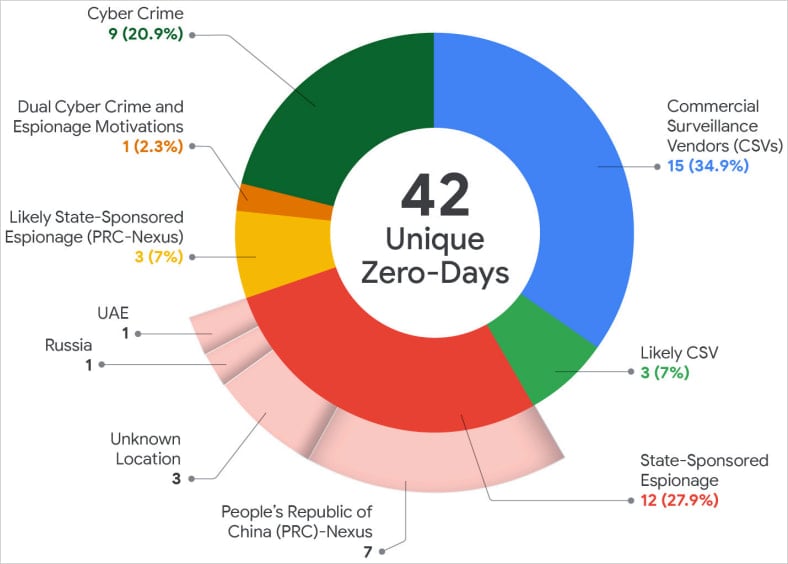
The most striking revelation in the 2025 assessment pertains not to who was attacked, but who was doing the attacking. For the first time in Google’s historical tracking of zero-day exploitation, Commercial Spyware Vendors (CSVs) and their direct clientele surpassed state-sponsored espionage groups in the volume of undocumented flaw utilization.
This shift signifies a profound commercialization and democratization of high-end offensive capabilities. While nation-states historically monopolized the acquisition and deployment of zero-days for intelligence gathering, the report suggests that sophisticated commercial entities are now leading the charge. The implication is that access to zero-day exploits is becoming less restricted by geopolitical boundaries and more dictated by financial capacity. State-sponsored groups have not disappeared, but their visibility may be reduced as they potentially pivot toward more subtle, long-term operational security (OPSEC) to avoid detection, while CSVs aggressively deploy these tools for high-value corporate or governmental targets sought by their paying clients.
The GTIG report explicitly notes this transformation: “This continues to reflect a trend we began to observe over the last several years—a growing proportion of zero-day exploitation is conducted by CSVs and/or their customers, demonstrating a slow but sure movement in the landscape.”
Nation-State Activity and Financial Motivations
Despite the rise of commercial actors, nation-state threats remain a persistent and targeted challenge. Among state-sponsored operations, China-linked espionage groups maintained the highest level of activity, exploiting 10 distinct zero-days in 2025. Their operational focus, consistent with geopolitical objectives, centered heavily on gaining persistent, long-term access to critical infrastructure—specifically edge devices, security appliances, and networking gear—to facilitate strategic intelligence collection.
A secondary, yet increasingly important, threat vector emerged from financially motivated actors. Ransomware groups and data extortion syndicates were responsible for exploiting nine distinct zero-days in 2025. This marks an escalation in sophistication for criminal organizations. Historically, ransomware actors relied on phishing, weak credentials, or known vulnerabilities (N-days). Their adoption of zero-days suggests a significant investment in offensive research or, more likely, procurement from specialized exploit brokers, indicating a blurring line between state-level tradecraft and organized crime.
The AI Factor and Future Trajectories
Looking ahead to 2026, the GTIG researchers forecast that the pace of zero-day exploitation will likely remain elevated, largely due to the accelerating impact of Artificial Intelligence (AI) tools on vulnerability research. The integration of advanced machine learning models into fuzzing frameworks and static/dynamic analysis tools promises to automate the discovery of complex vulnerabilities, including subtle memory safety issues, at an unprecedented speed. This increased automation will lower the barrier to entry for discovering novel exploits, potentially overwhelming the existing vulnerability disclosure and patching pipeline.
The report highlights the "Brickstorm" campaign as a case study illustrating the evolving mindset of sophisticated attackers. This campaign demonstrated a shift away from merely stealing existing source code to actively discovering zero-day flaws within future or recently deployed software products, emphasizing proactive exploitation over reactive compromise.
Mitigating the Inevitable: A Call for Resilience
In an environment where the disclosure-to-patch window is shrinking, and the complexity of exploited flaws is increasing, reliance solely on preventative measures is insufficient. Google’s recommendations center on operational resilience and aggressive attack surface reduction.
Organizations must prioritize minimizing the exposure of high-value assets. This includes stringent network segmentation, rigorous application of the principle of least privilege across all user and service accounts, and actively shrinking the external footprint of critical infrastructure components like VPN concentrators and management interfaces.
Furthermore, the findings underscore the necessity of advanced, behavior-based detection. Since zero-days, by definition, bypass signature-based security tools, continuous monitoring for anomalous activity—such as unexpected process execution, unusual network beaconing, or unauthorized privilege escalation attempts—is paramount. Rapid detection enables containment before an initial zero-day exploit can pivot into a full-scale compromise. Finally, maintaining hyper-efficient incident response workflows, ensuring patches are tested and deployed within hours rather than days for critical vulnerabilities, is no longer optional but a fundamental requirement for survival in this elevated threat climate. The industry is now engaged in an arms race where speed of response is the primary differentiator between a minor incident and a catastrophic breach.

