A severe, maximum-severity vulnerability discovered within the widely deployed FreeScout open-source helpdesk and shared mailbox platform has opened the door for threat actors to achieve unauthenticated Remote Code Execution (RCE) through what security researchers categorize as a true zero-click attack vector. This newly identified security gap, cataloged as CVE-2026-28289, represents a sophisticated bypass mechanism that completely invalidates a recently implemented mitigation intended to address a predecessor vulnerability, CVE-2026-27636, which previously required user authentication and specific upload permissions.
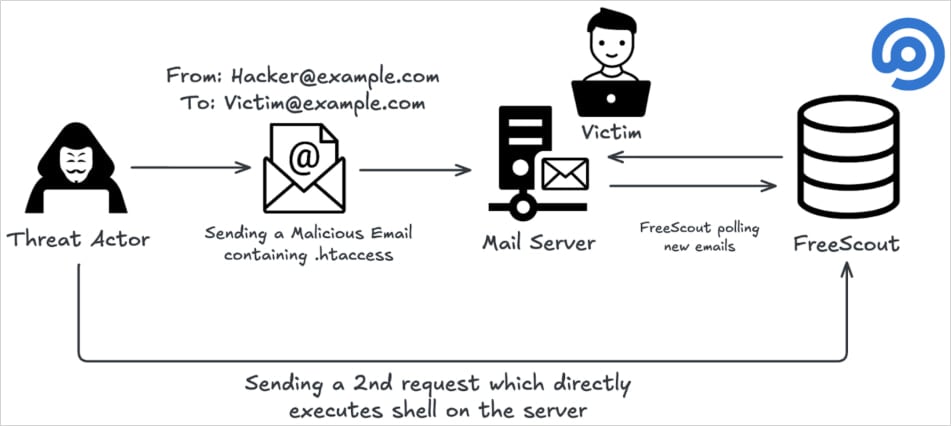
The core finding, detailed by the security firm OX Security, highlights a fundamental weakness in how the platform processes file attachments delivered via email. Exploitation hinges on the ability to send a single, specifically crafted email to any address actively monitored by the FreeScout instance. This capability transforms a routine communication channel into a direct execution pipeline into the underlying server infrastructure.
The Anatomy of the Bypass: Unicode Obfuscation
To understand the severity of CVE-2026-28289, one must examine its relationship with the preceding flaw, CVE-2026-27636. That earlier vulnerability allowed authenticated users with file upload rights to inject malicious code, typically by uploading files with restricted extensions or those prefixed with a dot (dotfiles), which often hold elevated significance in Unix-like operating systems, such as the .htaccess file used by Apache web servers.
The vendor’s initial attempt to remediate CVE-2026-27636 involved hardening filename validation routines. These routines were designed to sanitize inputs, specifically looking for prohibited extensions or names beginning with a period character. However, the OX Research team demonstrated that this validation was brittle and susceptible to evasion through the strategic insertion of non-visible characters.
The specific technique involves leveraging the Unicode Zero Width Space (U+200B). This character, while technically present in the filename string, is rendered invisibly by most display systems and, crucially, was not accounted for in the sanitization logic. When a malicious file—for example, a payload disguised as [U+200B].htaccess—is processed, the subsequent application logic strips away this invisible character. The resulting filename, now stripped of the zero-width space, is simply .htaccess, successfully triggering the conditions necessary to exploit the original RCE vulnerability (CVE-2026-27636), as the input validation layer has been effectively sidestepped before the critical file-saving operation occurs.
Zero-Click Escalation: The Attachment Vector
What elevates CVE-2026-28289 from a serious authentication bypass to a critical zero-click vulnerability is the mechanism by which the malicious file is introduced. Researchers confirmed that this bypass can be activated simply by delivering a malicious attachment to an inbox configured within the FreeScout environment.

When FreeScout fetches and processes an email containing such an attachment, it often stores these payloads in a predictable, accessible directory, noted in this case as /storage/attachment/. Because the system subsequently allows access to these stored attachments via the web interface, an attacker who successfully tricks the system into saving their crafted file gains an immediate, unauthenticated pathway to interact with that file through HTTP requests. By serving the file, or by manipulating the server environment through the uploaded file (like an Apache configuration file), the attacker can compel the server to execute arbitrary operating system commands. The absence of any requirement for user login or interaction to trigger the initial file upload chain cements its classification as a zero-click threat—the highest level of exploitability severity.
Industry Context: The Self-Hosted Vulnerability Landscape
FreeScout occupies a significant niche in the enterprise software ecosystem. It is positioned as a self-hosted, open-source alternative to proprietary, cloud-based customer relationship management (CRM) and ticketing solutions like Zendesk or Help Scout. This self-hosting model, while attractive to organizations prioritizing data sovereignty, compliance, or cost control, inherently shifts the burden of immediate patching and security maintenance onto the end-user organization.
The project’s substantial community engagement, evidenced by over 4,100 stars and 620 forks on its GitHub repository, confirms its widespread deployment. More alarmingly, preliminary scans using platforms like Shodan indicated approximately 1,100 publicly exposed instances of FreeScout servers globally. For a vulnerability that grants immediate, unauthenticated RCE, this install base represents a substantial attack surface ripe for exploitation.
The discovery underscores a perennial challenge in the software supply chain, particularly concerning open-source projects that become de facto industry standards. While the transparency of open source facilitates rapid community review, it also provides threat actors with detailed insight into the source code, making the discovery of subtle patch bypasses like this more feasible for sophisticated adversaries.
Expert Analysis: The Pitfalls of Shallow Patching
From a defensive security engineering perspective, CVE-2026-28289 serves as a textbook example of a "patch-gapping" vulnerability. This occurs when a security fix addresses the symptom (e.g., blocking explicit dotfiles) without fully correcting the root cause (e.g., the application’s permissive handling of user-supplied filenames during storage and subsequent interpretation).
Security experts consistently warn against validation routines that rely solely on simple string matching or blacklist approaches. A robust security architecture requires layered defenses (Defense in Depth) and context-aware validation. In this scenario, the validation mechanism failed to account for the semantic ambiguity introduced by Unicode control characters. The core principle violated is that external input, particularly from untrusted sources like email attachments, must be treated as inherently malicious until rigorously validated and sanitized in a context-aware manner—not just sanitized for visible characters.
The vendor’s security bulletin confirmed the scope: versions up to and including 1.8.206 are affected. The immediate fix, version 1.8.207, was released four days following the disclosure, signaling a swift acknowledgment of the critical nature of the flaw. However, the latency between patch release and patch deployment across thousands of self-hosted instances creates a significant window of opportunity for active exploitation.
Broader Implications and Mitigation Strategies
The potential fallout from a successful exploitation of CVE-2026-28289 is comprehensive, potentially leading to:
- Total Server Compromise: RCE allows attackers to execute commands with the privileges of the web server process, often leading to the installation of persistent backdoors.
- Data Exfiltration and Breach: Access to the mail server contents, internal configurations, and potentially adjacent systems connected to the server’s network.
- Lateral Movement: The compromised FreeScout server can serve as a pivot point to probe and attack internal corporate networks, a common tactic in modern ransomware and espionage campaigns.
- Service Disruption: System integrity attacks leading to denial of service.
Beyond the mandatory immediate upgrade to version 1.8.207, OX Security provided an essential secondary recommendation that speaks directly to the underlying server configuration risk associated with RCE via file uploads: disabling AllowOverrideAll within the Apache configuration file.
AllowOverrideAll instructs Apache to honor configuration directives contained within .htaccess files located within the application directories. Since the exploitation chain relies on uploading a malicious .htaccess file to trigger RCE, disabling this directive ensures that even if an attacker successfully uploads the file, the web server will ignore its malicious directives, thus neutralizing the final stage of the remote code execution payload delivery. This server-level hardening provides a crucial compensating control, safeguarding systems even if the application-level patch is delayed or incomplete.
Future Trends: The Arms Race Against Obfuscation
The discovery of the zero-width space bypass is indicative of a continuing arms race in application security. As developers become more adept at implementing blacklists and basic sanitization, threat actors are increasingly turning to character encoding and Unicode features to mask malicious payloads. This necessitates a paradigm shift in application security testing (AST) methodologies, moving toward deeper, semantic analysis of input rather than surface-level string filtering.
Future defensive measures must incorporate stricter canonicalization—the process of reducing all forms of input to a single, standard representation before validation—to ensure that zero-width characters, non-printing control characters, and various encoding schemes are neutralized before they ever reach the file-saving or command execution routines.
While no active exploitation of CVE-2026-28289 had been publicly documented at the time of this analysis, the technical feasibility and the high-value target profile of exposed FreeScout instances suggest that exploit tools are likely already under development or in circulation within illicit communities. Organizations running this platform must treat this vulnerability with the highest urgency, prioritizing the upgrade and applying the recommended server-side hardening measures immediately to preempt inevitable threat actor activity. The ease of initial access—a simple, unauthenticated email—makes this a near-perfect candidate for widespread, automated scanning and exploitation campaigns.

