Authored by the Huntress Tactical Response Team
For the seasoned security operations center (SOC) analyst, an alert concerning brute-force activity targeting an externally exposed Remote Desktop Protocol (RDP) port is often relegated to the lowest tier of triage. It is a common, almost expected, form of low-level noise—the digital equivalent of checking the locks on the front door repeatedly. However, within one such seemingly routine instance, the Huntress Tactical Response Team discovered a critical pathway that extended far beyond a simple network intrusion, leading directly into the core infrastructure supporting Ransomware-as-a-Service (RaaS) operations and their indispensable Initial Access Brokers (IABs). This investigation serves as a potent reminder that the faintest digital trace can often unravel the most complex criminal architectures.
Contextualizing the Initial Breach: The RDP Vulnerability
The foundation of this incident was the perennial security oversight: an RDP endpoint accessible directly from the public internet. Despite years of industry warnings disseminated through whitepapers, dedicated webinars, and constant community discourse, many organizations find themselves operationally constrained, requiring external RDP access for various legitimate business functions, often without implementing sufficient compensating controls like multi-factor authentication (MFA) or network segmentation.

The incident commenced with a standard alert indicating domain enumeration activity within the targeted environment. Upon receipt, the SOC team immediately initiated a forensic deep dive, beginning the necessary process of working both backward and forward along the threat actor’s observed kill chain.
Deconstructing the "Bread and Butter" Attack
Security monitoring frameworks, such as MITRE ATT&CK, often present intrusion lifecycles in a clean, linear progression. In the operational reality faced by defenders, however, alerts frequently arrive mid-sequence, forcing analysts to reconstruct the initial point of entry alongside mapping potential future lateral movement vectors.
Investigation of the affected host’s Windows event logs confirmed the initial hypothesis: the RDP service had been subjected to a relentless brute-force assault. While this technique is endemic in the threat landscape, its investigation can be unexpectedly complex, especially in environments retaining default logging configurations. Excessive failed login attempts often flood security logs, causing critical, high-fidelity telemetry regarding successful breaches or subsequent malicious activity to be overwritten or discarded prematurely. Furthermore, legitimate administrative tools, inventory scanners, or vulnerability assessment platforms frequently generate high volumes of failed authentications, creating significant noise that masks true threats.
In this specific case, the crucial telemetry remained intact, confirming a single successful compromise following the barrage of attempts. While the brute-force campaign targeted numerous user accounts, only one account achieved successful authentication.
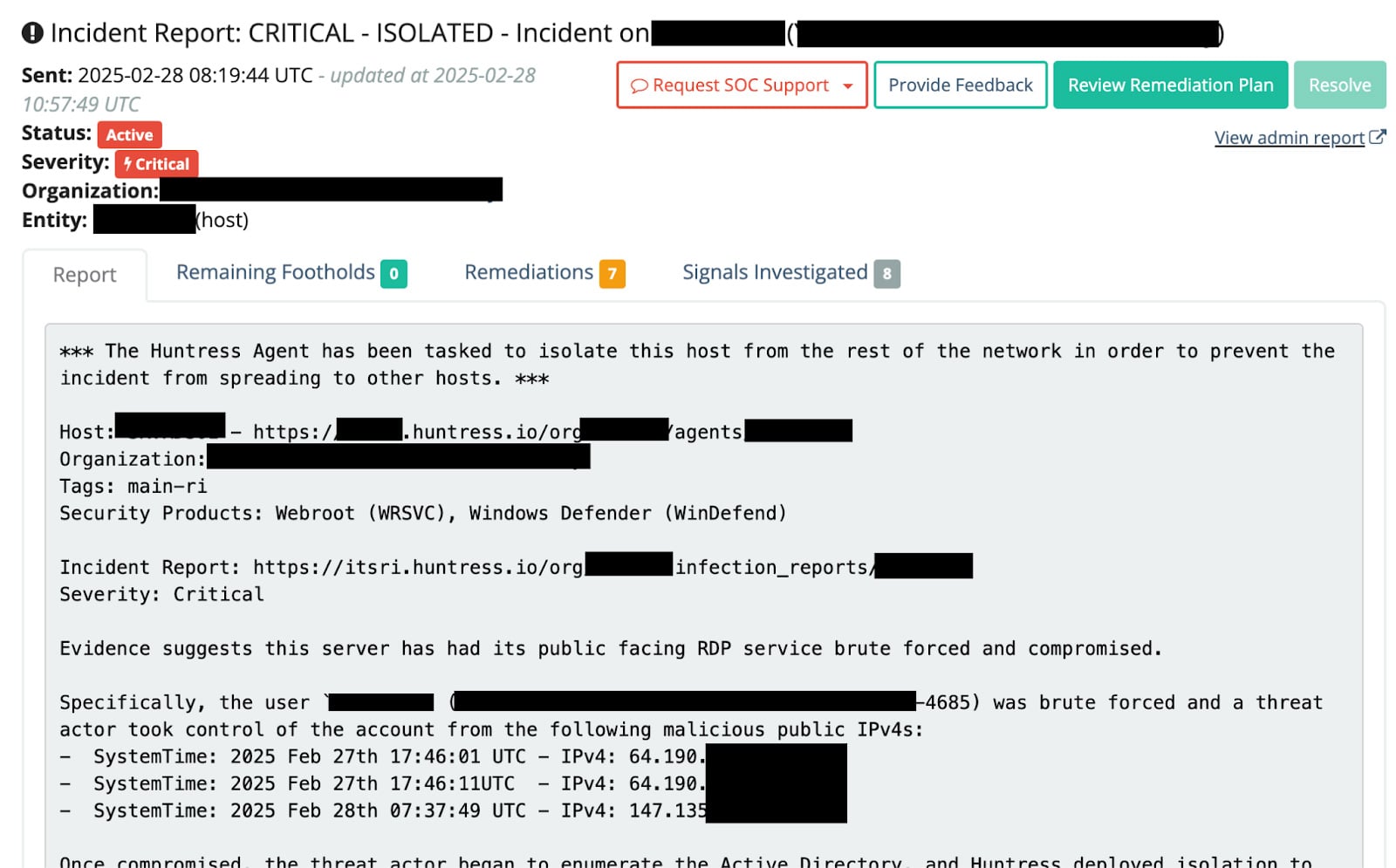
This initial foothold immediately became the primary pivot point for the investigation. A peculiar pattern emerged immediately: the successful logins for this single compromised account originated from a surprisingly diverse array of external IP addresses over a concentrated timeframe. Standard intrusions typically originate from a single or a small cluster of related IPs. This multiplicity strongly suggested the threat actor was not operating from a fixed location but leveraging a rotating pool of intermediary servers. A deeper chronological analysis of the login timestamps supported the theory that a single operator was utilizing distributed infrastructure rather than a coordinated effort by multiple independent threat actors.
The immediate consequence of the successful RDP compromise was the establishment of initial access into the victim network. Following standard procedure, the threat actor commenced internal reconnaissance, specifically targeting domain enumeration—mapping out organizational structure, user groups, and Active Directory configurations. Once these enumeration signals were flagged as malicious by the SOC, swift action was taken: a network-wide isolation order was immediately issued to sever command-and-control (C2) paths and halt any nascent lateral propagation.
On the surface, the incident appeared resolved: a typical RDP breach, internal scanning, swift containment. However, the subsequent forensic deep-dive, conducted after isolation, revealed anomalies that deviated sharply from established ransomware tradecraft, prompting a comprehensive re-evaluation.
Uncharacteristic Tradecraft: The Manual Search for Stored Secrets
In typical post-compromise activity following RDP or VPN exploitation, threat actors adhere to highly optimized, automated playbooks for credential harvesting. This usually involves memory scraping tools like Mimikatz or Procdump to extract credentials from the Windows Local Security Authority Subsystem Service (LSASS) process, or leveraging tools like Secretsdump for registry hive extraction. In some instances, session data from web browsers might be targeted.

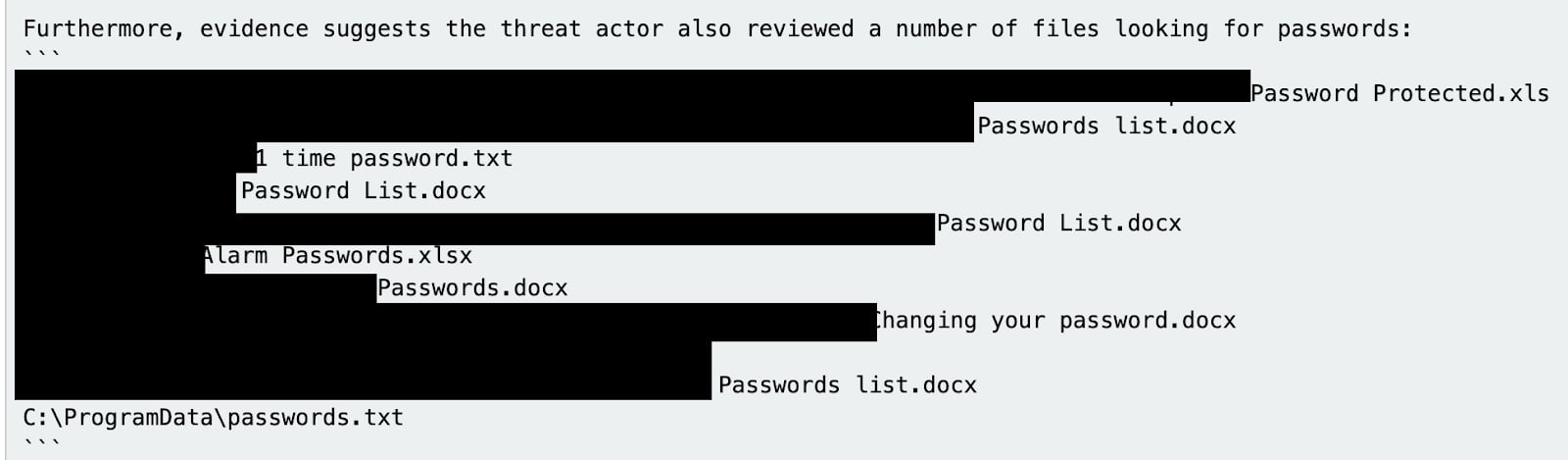
What was observed in this environment, however, represented a significant departure: the actor was actively navigating file systems and file shares, specifically searching for plain-text credential material stored within accessible files. This behavior is generally inefficient and atypical for sophisticated ransomware groups who rely on high-yield, automated extraction from memory or protected system areas.
The analytical team hypothesized that this manual search indicated a tradecraft deviation, possibly suggesting the actor was either less experienced, operating under specific constraints, or perhaps executing a specialized, secondary objective. While extracting credentials from LSASS is procedural and repeatable across different client environments, locating and validating passwords within arbitrary text files scattered across a file share requires manual intervention and verification—a less scalable approach. This suggested the actor was attempting to maximize credential acquisition beyond the standard playbook’s output.
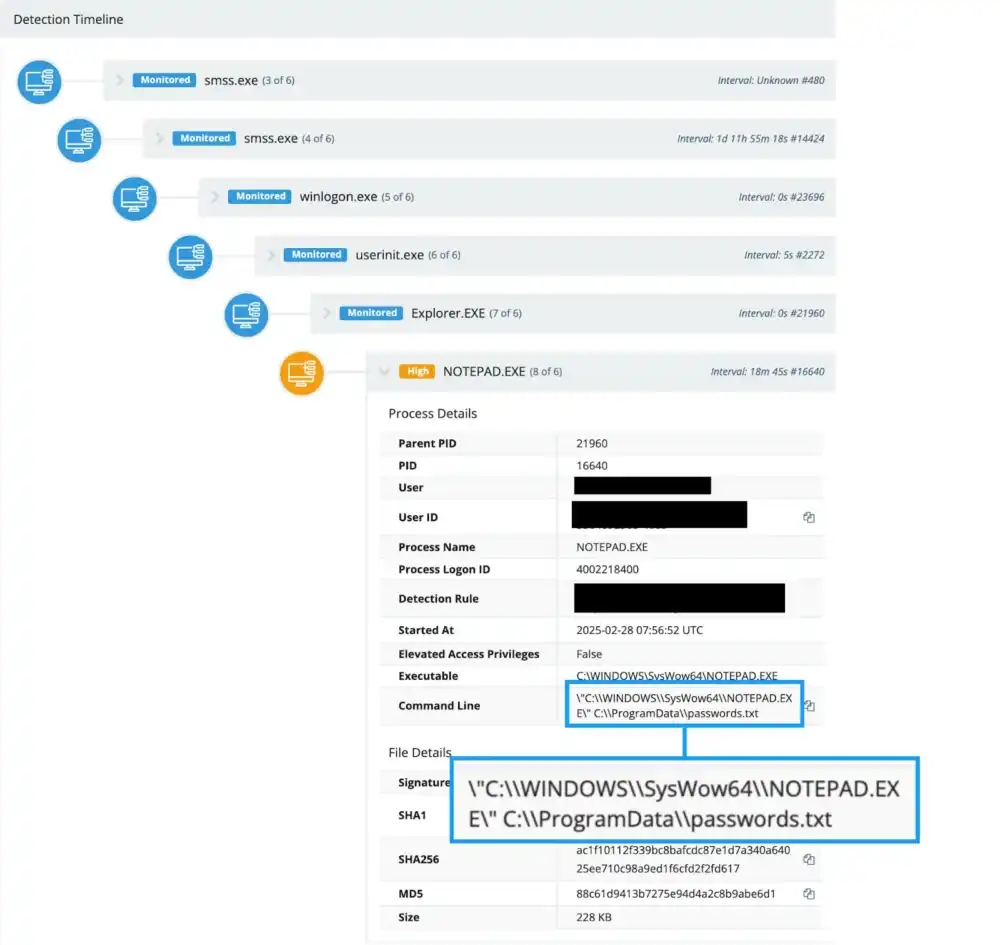
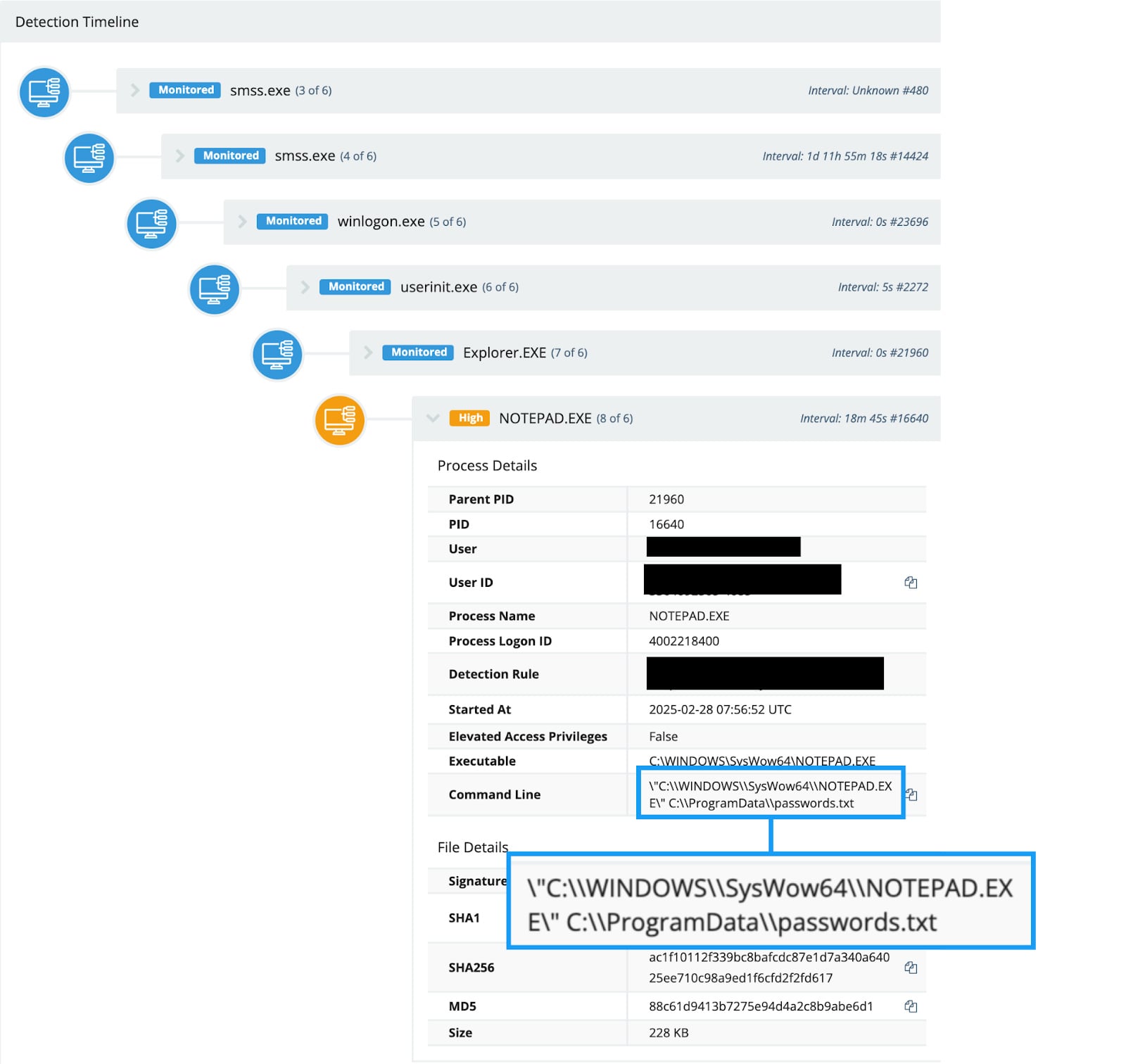
Forensic artifacts from the affected host provided concrete evidence of this manual activity. Process monitoring logs captured instances of the standard Windows notepad.exe opening various text files. Further examination of jump-list artifacts—metadata detailing recently accessed files—revealed a pronounced pattern of the threat actor repeatedly interacting with files containing keywords such as "password," "creds," or "keys" in their naming convention. This consistent, hands-on interaction strongly suggested the actor was prioritizing files containing potentially overlooked or legacy credentials that automated tools might miss or deem too risky to target directly.
This uncharacteristic methodology served as the critical secondary signal. It indicated that the source of the brute-force attack might be associated with a specific, perhaps niche, segment of the cybercrime ecosystem, prompting an intensive pivot back to the initial source IPs.
Infrastructure Mapping: Following the Digital Breadcrumbs
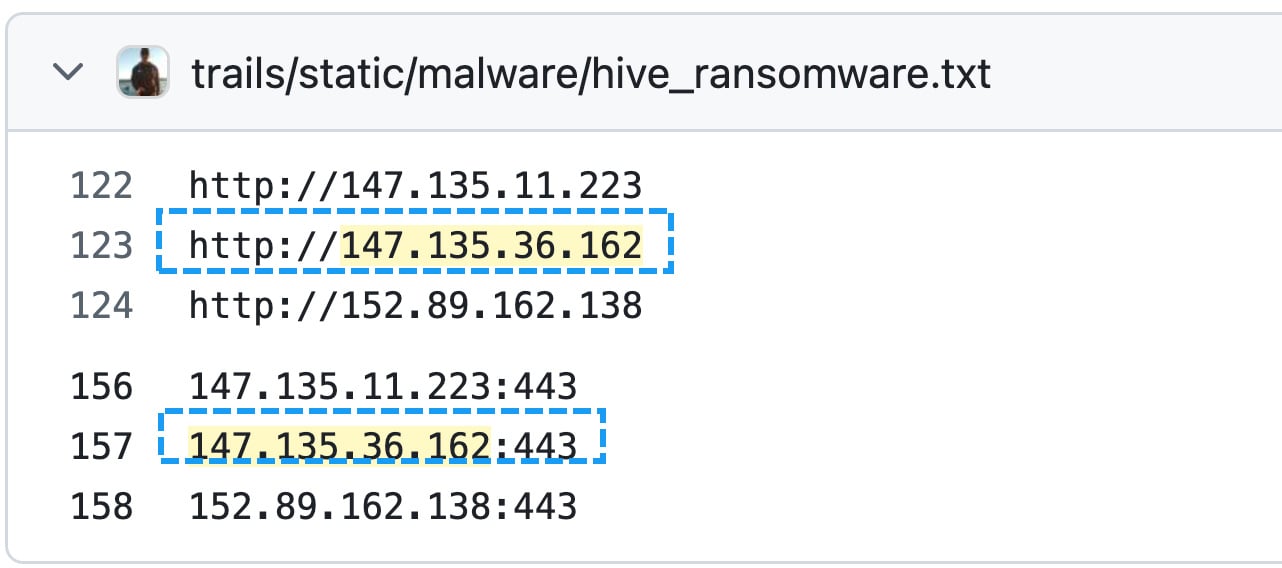
The initial set of brute-forcing IP addresses, once cross-referenced against threat intelligence platforms such as Maltrail, yielded immediate associations with established ransomware families. Specifically, one of the attacking IPs was correlated with activities linked to the Hive ransomware operation. Further verification via government advisories, such as those published by CISA, also connected this specific IP address to the BlackSuite threat group. This established a preliminary link between the initial access vector and known, high-impact ransomware affiliates.
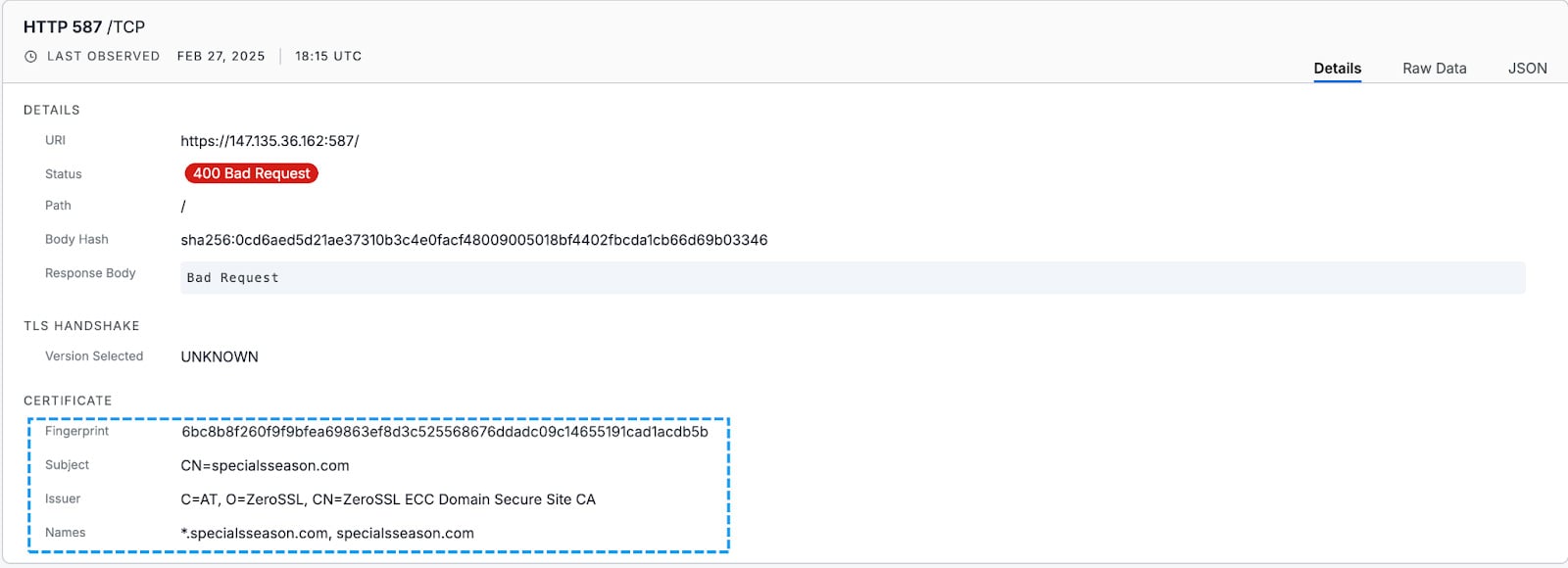
The investigation shifted focus from the IP addresses themselves to the digital artifacts they presented—namely, associated network certificates. Examination of the Transport Layer Security (TLS) certificates tied to the brute-forcing IP address uncovered a highly revealing domain name: specialsseason[.]com.
This domain name provided a crucial anchor point. The team utilized the cryptographic fingerprint (SHA256 hash) of this certificate to perform broad network reconnaissance, searching for other associated IP addresses and domain names sharing the identical TLS signature. This technique, often overlooked in routine triage, is highly effective for mapping infrastructure that is deliberately obfuscated or rotated.
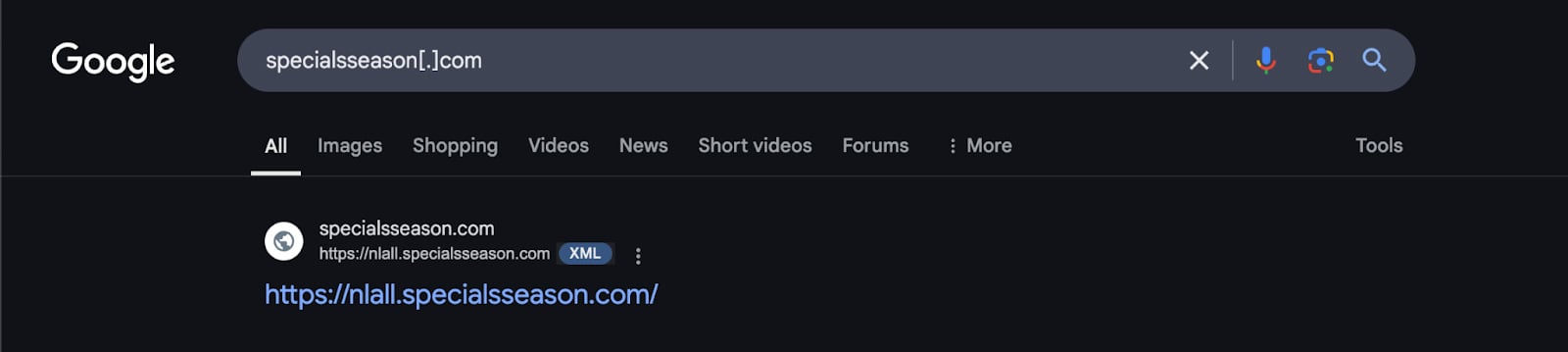
The results were significant: the certificate fingerprint linked the initial IP to a vast network of related infrastructure. A distinct naming convention emerged across the associated IP addresses: they were subdomains structured as NL-<countrycode>.specialsseason[.]com. This structure suggested a globally distributed, highly organized network utilizing a common certificate authority or provisioning system. The country codes observed spanned numerous jurisdictions, including significant clusters in Russian-speaking regions (NL-RU, NL-RU2, etc.) alongside multiple US and European codes. This geographical dispersal strongly suggested a professionalized infrastructure designed for resilience and C2 obfuscation, typical of sophisticated RaaS or IAB operations.
The VPN Nexus: Initial Access Brokers Exposed
The next layer of discovery involved pivoting from the newly identified IP set. Many of these distributed servers hosted various listening services across different ports. Analyzing the TLS certificates presented by these new IPs—all sharing the fingerprint of the original—revealed a second, deeply embedded malicious domain: 1vpns[.]com.
This domain name immediately raised suspicion due to its close typographical resemblance to legitimate Virtual Private Network (VPN) services, indicating an attempt at brand mimicry or association with common anonymity tools. The subtle difference—the inclusion of the ‘s’ following ‘1vpn’—is a classic domain squatting technique.
Further intelligence gathering confirmed that this specific VPN service was allegedly advertised by Initial Access Brokers (IABs). The terminology itself, "Special Season," often used in threat actor parlance to denote "big game hunting"—targeting high-value enterprises for massive ransomware payouts—strongly indicated that this infrastructure was a commercial offering specifically tailored for financially motivated threat groups.
The analysis revealed reports linking the 1vpns service to multiple, distinct ransomware gangs, solidifying its role as a shared utility within the cybercrime ecosystem. An adjacent service, advertised via related infrastructure, surfaced the domain 1jabber[.]com, featuring a list of other "funny" or obfuscated domains.
Crucially, one of the associated domains mentioned, nologs[.]club, provided context to the operational philosophy. The FAQ section for this VPN service explicitly boasted a "zero logs" retention policy. For IABs and ransomware affiliates whose operations rely on maintaining anonymity and evading attribution, a provider promising zero logging is the ultimate procurement target.
Industry Implications and Expert Analysis
This case study transcends the resolution of a single network incident. It provides an unprecedented, infrastructure-centric view into the mechanics of the RaaS supply chain. We often discuss ransomware through the abstract lens of TTPs (Techniques, Tactics, and Procedures) or static Indicators of Compromise (IOCs). This analysis, however, peels back the layers to reveal the actual service providers that facilitate initial access.
The observed behavior—the manual search for credentials in files—combined with the sophisticated, geographically distributed infrastructure points toward a specialized Initial Access Broker. These brokers specialize in gaining initial footholds (often via compromised RDP, phishing, or vulnerable VPNs) and then selling that access to various ransomware groups. Their infrastructure, as mapped via certificate fingerprinting, is designed not just for attack execution but for enduring operational security, utilizing globally distributed hosting and domain spoofing to obscure their true location and client base.
The failure to detect this broader network would have resulted in treating the incident as an isolated RDP compromise. By "zooming out" and following the non-standard tradecraft (the manual file searches) back to the originating IP addresses, the SOC team was able to transition from tactical remediation to strategic threat intelligence gathering, effectively mapping a significant portion of a criminal ecosystem’s support structure.
Future Impact and Defensive Posture
The persistence of exposed RDP remains a significant vector, but this incident highlights the evolving sophistication of the actors exploiting it. Organizations must recognize that successful brute-force attempts are often the entry ticket for highly organized IABs who then monetize that access.
For future defense, this scenario underscores several key requirements:
- Beyond Brute Force Alerts: SOCs must be trained to treat anomalous post-compromise behavior (like the manual file searching) as a higher-fidelity indicator than the initial access attempt itself. Automated credential harvesting often leaves a cleaner signature than manual exploration.
- Certificate Visibility: Leveraging threat intelligence tools capable of pivoting on shared TLS certificate fingerprints across vast IP ranges is essential for mapping interconnected infrastructure that attackers use to rotate their command and control points.
- Supply Chain Awareness: Security teams must understand that IABs are distinct entities from the final ransomware operators. Disrupting the IABs’ infrastructure, as demonstrated here, can starve multiple ransomware gangs of their crucial initial access points.
This incident, born from a routine alert, proves that diligent, curiosity-driven investigation—pulling on every discernible thread—can lead to the dismantling of sophisticated, multi-national cybercriminal operations. The digital thread was thin, but the resulting tapestry revealed a robust, commercially available ecosystem dedicated to fueling the global ransomware epidemic.
Conclusion
Ransomware remains an existential threat to enterprises across all sectors. To many practitioners, the brute-force attack on RDP is a known quantity, a threat so common it risks complacency. At Huntress, the methodology employed is to "SOC and Awe"—to maintain relentless investigative curiosity.

In this instance, the investigation evolved from a seemingly straightforward, resolved brute-force event into the unmasking of an extensive, geographically dispersed Ransomware-as-a-Service infrastructure. This infrastructure appears explicitly designed and operated by Initial Access Brokers to facilitate illicit access for numerous ransomware affiliates, emphasizing the monetization and service-oriented nature of modern cybercrime.
Tradecraft Tuesday: No Products. No Pitches. Just Hacks.
Tradecraft Tuesday provides cybersecurity professionals with an in-depth analysis of the latest threat actors, attack vectors, and mitigation strategies. Each weekly session features technical walkthroughs of recent incidents, comprehensive breakdowns of malware trends, and up-to-date indicators of compromise (IOCs).
Participants gain:
- Real-time technical breakdowns of emerging threats.
- Actionable intelligence derived from frontline incident response.
- Deeper insight into threat actor methodologies beyond simple IOC lists.
Register for Tradecraft Tuesday – Advance your defensive posture with real-time intelligence and technical education specifically designed for those responsible for safeguarding their organization’s environment.
Indicators of Compromise
| IOC Type | IOC |
| IP Address | 64.190.113[.]159 |
| IP Address | 147.135.36[.]162 |
| Domain | specialsseason[.]com |
| Domain | 1vpns[.]com |
| Certificate Fingerprint (SHA256) | 6bc8b8f260f9f9bfea69863ef8d3c525568676ddadc09c14655191cad1acdb5b |
| Certificate Fingerprint (SHA-1) | 65899cd65dd753d2eef5463f120ae023e873e1bd |
| Certificate Fingerprint (SHA-246) | b884cce828f06fb936fd5809d5945d861401c606c4ebe894464c99e6473e9570 |
Sponsored and written by Huntress Labs.