The clandestine digital marketplaces are witnessing a significant shift in product valuation, moving away from bespoke exploit kits toward the large-scale monetization of initial access infrastructure. At the forefront of this lucrative trade are compromised credentials for widely used web hosting control panels, most notably cPanel. These access tokens are no longer niche items; they are being aggressively marketed across illicit forums and encrypted chat services—often via Telegram—at near-commodity pricing, functioning as pre-built launching pads for widespread malicious activities, including sophisticated phishing campaigns and large-scale scams.
Recent forensic analysis conducted by cybersecurity researchers over a concentrated seven-day observation window underscores the structured, industrialized nature of this market. The study monitored vast volumes of chatter within these adversarial channels, specifically cataloging over 200,000 discrete posts referencing cPanel access. This deep dive illuminated precisely why cPanel, due to its pervasive deployment and administrative depth, has become such a prized asset in the contemporary threat landscape.
The Ubiquity and Power of cPanel: A Centralized Target
cPanel stands as one of the dominant management interfaces for Linux-based web hosting globally. It abstracts complex server administration tasks—managing DNS zones, configuring mail servers, administering databases, provisioning SSL certificates, and manipulating file systems—into a cohesive graphical interface. This centralization of power is precisely what makes it so valuable to malicious actors.
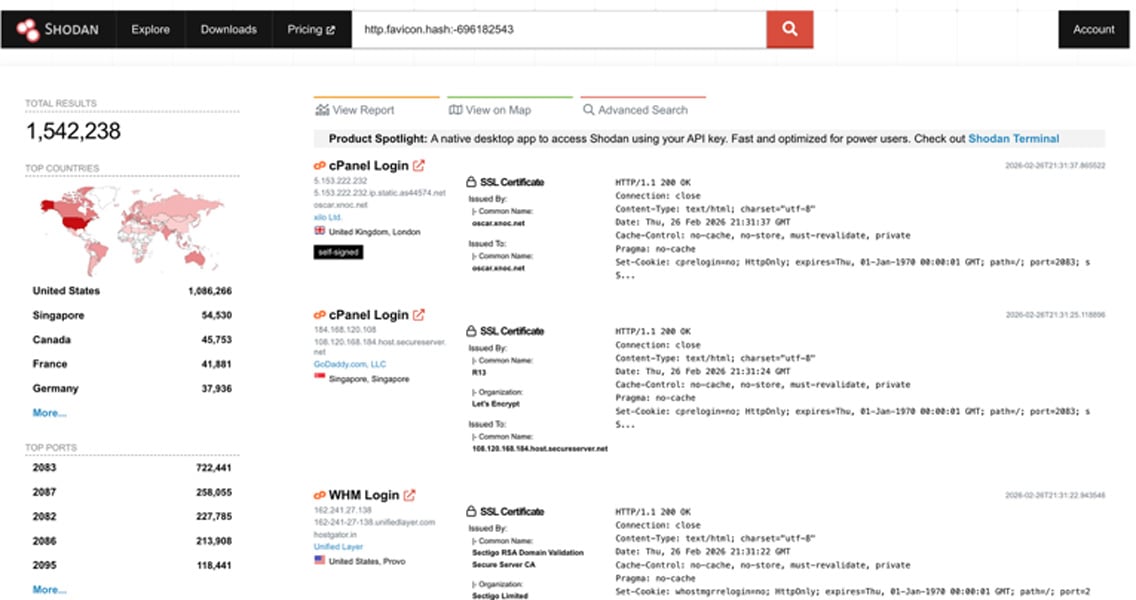
The sheer scale of deployment confirms its status as a prime target. Internet-facing scanning services, such as Shodan, consistently reveal well over 1.5 million servers actively broadcasting cPanel services. A geographic heatmap of these installations reveals a heavy concentration in specific regions, notably the United States, where the count frequently surpasses one million instances. This high density translates directly into a large potential inventory for cybercriminals harvesting credentials.

The Gateway Effect: One Key, Dozens of Doors
For any entity operating a web presence—be it a small e-commerce site, a corporate subsidiary, or an extensive enterprise web portfolio—a single compromised cPanel credential grants an attacker an alarming level of control. This access transcends merely defacing a single webpage. It unlocks the entire hosting account infrastructure, enabling a spectrum of disruptive and harmful actions:
- Unrestricted File System Access: The ability to upload, modify, or delete any file associated with the account, facilitating the deployment of persistent backdoors, web shells, or malware distribution points.
- Email Infrastructure Hijacking: Threat actors can commandeer the account’s Simple Mail Transfer Protocol (SMTP) services, turning legitimate, trusted domains into high-volume senders for phishing, spam, and malware delivery, bypassing initial spam filters due to the domain’s established reputation.
- Database Exfiltration and Manipulation: Access to underlying databases allows for the theft of sensitive customer information, proprietary business data, or the injection of malicious content directly into live web applications.
- SSL and DNS Tampering: The potential to alter Domain Name System (DNS) records can redirect traffic intended for legitimate sites to attacker-controlled infrastructure, or compromise SSL certificate management, enabling man-in-the-middle attacks.
- Lateral Movement and Privilege Escalation: In shared hosting scenarios, a single compromised cPanel account often provides the pathway to pivot to other accounts hosted on the same physical or virtual server, exponentially increasing the scope of the breach. On an organizational level, this can lead to the complete compromise of a company’s public-facing digital presence.
Crucially, because these compromised access methods utilize valid, legitimate user credentials, they often bypass conventional perimeter security defenses that rely heavily on flagging anomalous external connection attempts. The initial malicious activity—such as quiet outbound email campaigns or the subtle uploading of obfuscated scripts—can persist undetected for extended periods before visible exploitation manifests.
Historical Vectors: How the Keys are Forged
The infiltration of cPanel environments is rarely attributed to a single exploit; rather, it stems from a confluence of predictable security failures and automated exploitation.
The most common initial access method remains credential compromise. This is frequently achieved through:
- Credential Stuffing: Automated attempts to log in using credentials harvested from prior, unrelated data breaches across the web.
- Phishing: Targeted social engineering campaigns aimed at tricking administrators or hosting account holders into surrendering their login details.
- Brute-Forcing: Automated scanning and rapid guessing of credentials against exposed cPanel login portals, often targeting weak or default passwords.
Beyond direct credential theft, configuration weaknesses serve as open invitations. Leaving configuration files like .env or config.yaml publicly accessible, failing to implement Multi-Factor Authentication (MFA), or using easily guessable passwords creates low-hanging fruit for automated scanning tools.
A second major pathway involves web application exploitation. Servers hosting Content Management Systems (CMS) like WordPress, Joomla, or Drupal are often the weak link. If these platforms—or their associated plugins and themes—are not rigorously patched, they provide attackers with a route to upload web shells. Once a shell is established within a website’s directory, the attacker can often leverage that foothold to enumerate server configuration files (like wp-config.php) to harvest database credentials, which can then be used to escalate privileges or gain broader access to the hosting environment, eventually leading to the cPanel interface itself.
The advent of sophisticated botnets has accelerated this process. These automated networks continuously probe the internet for known CVEs, exposed management ports, and misconfigurations, effectively turning the entire cPanel ecosystem into a constant source of exploitable inventory ripe for monetization.
The Cybercrime Economy: Commoditization and Market Structure
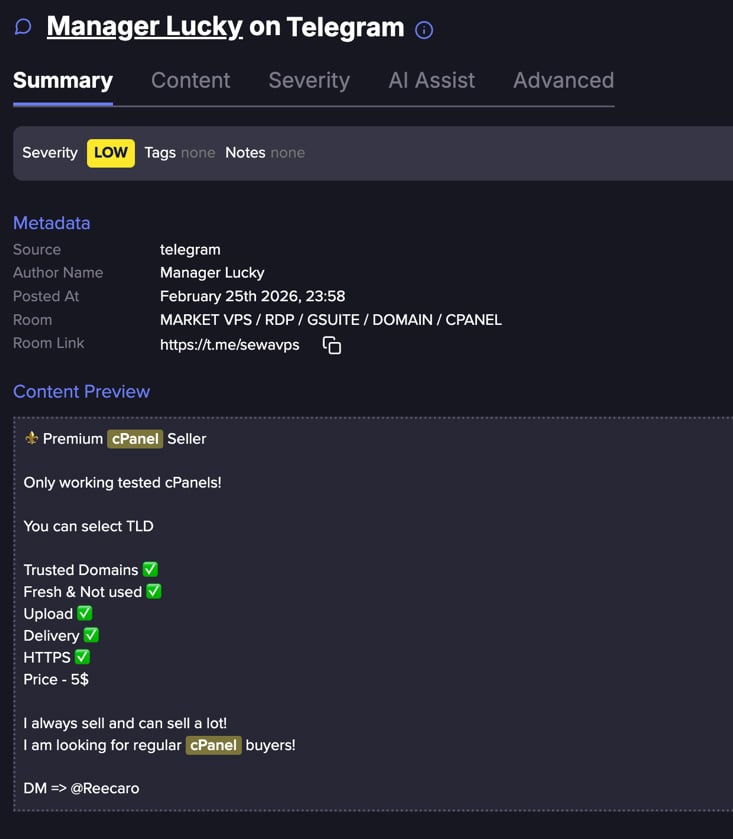
The research tracking underground communications reveals a highly professionalized market dedicated to the resale of these compromised access points. The analysis of over 200,000 posts over seven days showed that approximately 90% of the listings were duplicates. This high redundancy suggests an efficient system of amplification, where a smaller set of unique, confirmed access credentials are advertised across numerous channels simultaneously using templated advertising, indicating automated reposting tools are standard practice.
This market operates with the precision of any legitimate commerce platform. Listings often feature marketing terminology familiar from commercial sales—terms like "fresh," "high quality," "spam clean," or "ready for mailing"—to establish perceived value and trust among illicit buyers.
The pricing structures are tiered, demonstrating a sophisticated understanding of risk versus reward:

| Quality Tier | Quantity (Units) | Approximate Price (USD) |
|---|---|---|
| Premium | 100 | $75 |
| Premium | 500 | $289 |
| Premium | 1,000 | $645 |
| Regular | 1,000 | $23 |
| Regular | 3,000 | $42 |
| Regular | 5,000 | $58 |
This data clearly shows a steep volume discount model. "Premium" access, likely verified as active, unrevoked, and possessing clean SMTP reputation, commands a significantly higher per-unit price. Conversely, "Regular" access, which may have inherent risks such as being flagged or partially restricted, is sold in massive quantities at a fraction of the cost, signaling that the buyers are often looking for volume to use as phishing infrastructure where a few successful sends are enough to recoup the low initial investment.
The practice of selling in bulk suggests that the initial compromise mechanism (e.g., a specific stealer log source or a known vulnerability scanner run) often yields a high volume of credentials, many of which might be dead ends or have already been discovered by the original victim. The sellers offload this inventory rapidly, trading speed of sale for slightly lower per-unit revenue.
Industry Implications: The Shift to Access Brokerage
This phenomenon marks a critical evolution in the cybercrime supply chain. The focus is increasingly shifting away from the complex, resource-intensive development of zero-day exploits toward the far more efficient business model of Initial Access Brokerage (IAB). Why spend months developing a complex ransomware strain when access to a verified, reputable domain infrastructure can be purchased instantly?
For organizations, this commodification of hosting access transforms a technical security failure into a critical business continuity risk. When a cPanel account is compromised and sold, the damage is multifaceted:
- Reputational Collapse: The domain and associated IP addresses are quickly blacklisted by major email providers and security vendors due to the spam or phishing traffic originating from them. Reversing this blacklisting is time-consuming and costly.
- Operational Paralysis: If proprietary data or critical website assets are held for ransom, or if the site is defaced during the initial exploitation phase, core business functions cease.
- Supply Chain Risk: If the compromised hosting account services other downstream clients or partners, the breach cascades, turning a local security incident into a widespread ecosystem failure.
The ability of threat actors to package, grade, and distribute these credentials using established commercial pricing models lowers the barrier to entry for less technically sophisticated cybercriminals. A novice scammer no longer needs to worry about how to breach a server; they simply need capital to purchase a reliable mailing platform already integrated into a trusted web host.
Future Impact and Proactive Defense Strategies
The trajectory suggests that the industrialization of compromised hosting access will only intensify. As automated harvesting tools become more refined, the supply of these "digital real estate" assets will likely increase, further driving down the unit price for lower-quality access while premium, verified access maintains high value.
To effectively combat this threat, organizations must pivot their defensive posture beyond traditional perimeter monitoring:
- Mandatory and Enforced MFA: Multi-Factor Authentication must be enforced universally across all control panel interfaces (cPanel, Plesk, etc.). This single measure neutralizes the vast majority of credential stuffing and brute-force attacks.
- Strict IP Whitelisting: Wherever feasible, restrict access to administrative panels to known, static administrative IP addresses. This severely limits the utility of stolen credentials obtained remotely.
- Continuous SMTP Monitoring: Implement robust monitoring of outbound mail traffic from all hosting accounts. Anomalous spikes in volume, unusual recipient domains, or failures in standard mail authentication protocols (like SPF/DKIM) are critical, often leading indicators of compromise.
- File Integrity Monitoring (FIM): Deploy FIM solutions to alert on unauthorized modifications to critical application files (like CMS configuration files) or the appearance of unexpected executable scripts or web shells.
- Proactive Threat Intelligence Consumption: Security teams must actively monitor underground intelligence feeds, specifically tracking when their domains, subdomains, or specific hosting credentials appear in bulk sales data or stealer logs. Detecting the sale of access is often the final warning before the use of that access.
- Principle of Least Privilege: Ensure that hosting accounts are segregated based on need. If an account only hosts a static informational page, it should not have unnecessary access to database management or advanced mail server configurations.
In the evolving landscape where digital infrastructure is treated as tradable inventory, safeguarding hosting credentials moves from being a routine IT maintenance task to a frontline strategic defense against being co-opted as an unwitting platform for global fraud operations. The integrity of the digital surface area is now directly tied to the health of the entire cybercrime ecosystem’s operating capacity.

