The persistent threat landscape facing high-security environments has been drastically complicated by the emergence of a sophisticated new campaign attributed to the state-sponsored hacking collective known widely as APT37 (also identified by aliases such as ScarCruft, Ricochet Chollima, and InkySquid). This advanced persistent threat actor has deployed a novel arsenal, dubbed "Ruby Jumper," specifically engineered to bridge the chasm between internet-connected networks and completely isolated, air-gapped systems. This development marks a significant escalation in cyber warfare capabilities, as air-gaps—long considered the ultimate defense for critical data—are now demonstrably vulnerable to physical, removable-media-based infiltration.
Air-gapped networks, the bedrock of security for classified military installations, core national infrastructure (such as nuclear facilities and power grids), and highly sensitive research and development laboratories, operate on the principle of absolute physical disconnection. This isolation is enforced both at the hardware level—by the complete absence of network interface cards, Wi-Fi adapters, or Bluetooth modules—and often through stringent logical segmentation controls like specialized VLAN configurations and hardened firewalls on any adjacent systems. The traditional method for transferring data into or out of such environments relies exclusively on vetted, physical transfer mechanisms, predominantly removable storage drives like USB flash drives or external hard disks. It is precisely this mandated physical vector that Ruby Jumper weaponizes.
Security researchers at Zscaler, who meticulously dissected the components of the Ruby Jumper operation, have unveiled a meticulously crafted suite of five interconnected malicious tools: RESTLEAF, SNAKEDROPPER, THUMBSBD, VIRUSTASK, and FOOTWINE. The complexity of this multi-stage operation suggests significant investment and planning by the sponsoring state actor, focusing on stealth, persistence, and multifaceted espionage capabilities once inside the most secure perimeters.
The Infiltration Vector: LNK Files and Deceptive Context
The initial compromise within the targeted ecosystem begins with a deceptively simple action: the victim interacting with a malicious Windows shortcut file, identifiable by the .LNK extension. This initial lure is engineered to be compelling enough to elicit a click from an unsuspecting insider or contractor accessing data on a system connected to the perimeter network, perhaps one that bridges to the air-gapped environment via controlled data transfer procedures.
Upon execution of the LNK file, a complex PowerShell script is immediately unleashed. This script performs the dual function of extracting concealed payloads directly embedded within the shortcut file itself—a classic technique for evading simple signature-based detection—while simultaneously launching a decoy document to occupy the user’s attention and mask the background malicious activity. Although the specific targets remain obscured, researchers noted the decoy document’s content: an Arabic translation of a North Korean newspaper article pertaining to the ongoing dynamics of the Palestine-Israel conflict. This contextual detail strongly supports the attribution to APT37, whose targeting patterns often align with geopolitical interests favored by Pyongyang.
The PowerShell script’s primary objective is the initial deployment of the first malware component, RESTLEAF. RESTLEAF functions as a persistent implant, establishing clandestine communication channels with APT37’s command-and-control (C2) infrastructure. Intriguingly, the malware appears to be utilizing Zoho WorkDrive for C2 communications, potentially exploiting legitimate cloud service traffic to camouflage its beaconing activities within routine enterprise data flow, a method that makes network monitoring significantly more challenging.

The Ruby Interpreter: A Novel Persistence Mechanism
RESTLEAF does not linger; its role is to secure the next-stage payload. It communicates with the C2 to retrieve encrypted shellcode, which then facilitates the download and installation of SNAKEDROPPER. This is where the Ruby Jumper toolkit reveals its most novel characteristic: a profound reliance on the Ruby programming language runtime environment.
SNAKEDROPPER executes a highly unusual maneuver: it installs the complete Ruby 3.3.0 runtime environment, including its interpreter, standard libraries, and the RubyGems infrastructure. This legitimate, necessary software stack is disguised under the guise of a benign, USB-related utility named usbspeed.exe. By embedding the malware within a fully functional, necessary software ecosystem, APT37 ensures its malicious code has the necessary execution environment readily available without needing to smuggle a complete interpreter through traditional means or rely on potentially locked-down system binaries.
The persistence mechanism is equally ingenious. SNAKEDROPPER modifies the core functionality of the RubyGems library by replacing a default file, operating_system.rb, with a maliciously crafted version. This modified file is programmed to execute automatically whenever the Ruby interpreter starts. To ensure regular execution, a scheduled task, cryptically named rubyupdatecheck, is established to trigger the interpreter—and thus the malicious Ruby code—every five minutes.
Once the Ruby environment is established and persistent, SNAKEDROPPER proceeds to fetch the subsequent stages of the attack toolkit, installing them as Ruby files. The THUMBSBD backdoor is delivered as ascii.rb, while the VIRUSTASK malware is hidden as bundler_index_client.rb. This strategy of utilizing file extensions common to software development environments further aids in blending the malicious execution with legitimate system processes, especially on developer workstations or systems involved in software testing that might reside near the air-gapped network.
THUMBSBD: Weaponizing Removable Media
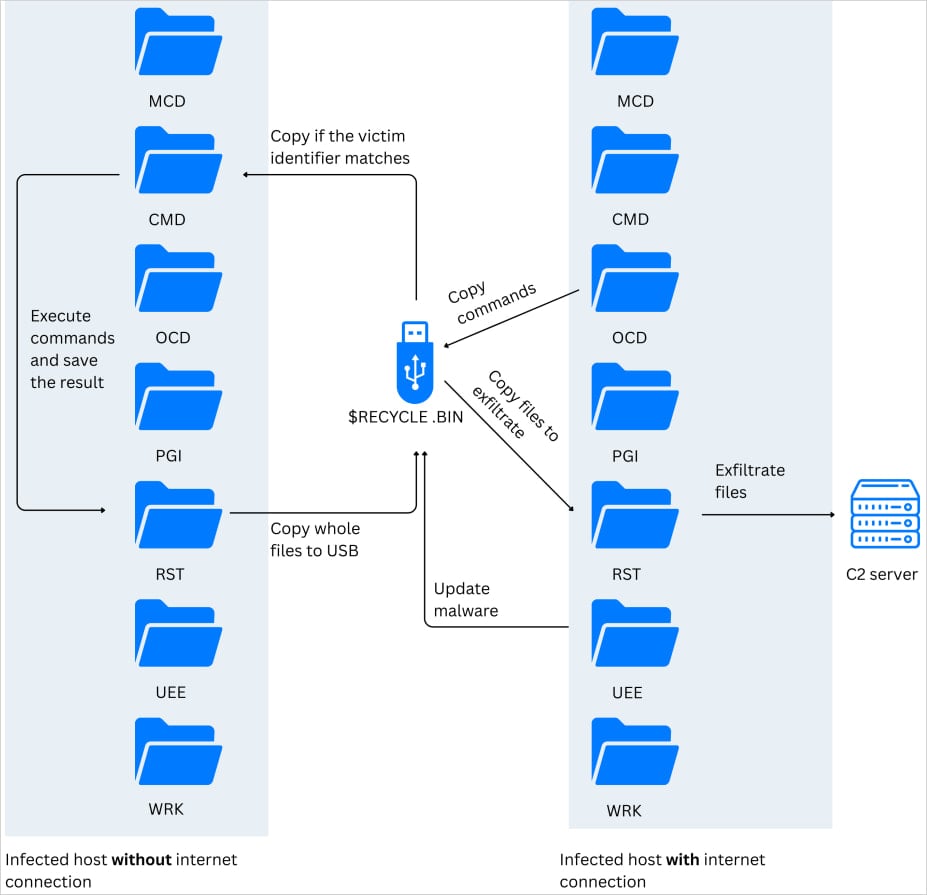
The THUMBSBD backdoor assumes the critical role of reconnaissance, staging, and, most importantly, bridging the physical isolation gap. Its functions include gathering detailed system information, queuing up commands received from the C2, and preparing collected data for exfiltration.
However, its paramount function centers on removable storage. THUMBSBD actively scans for connected USB drives. Upon detection, it covertly creates hidden directories within the file system of these drives and systematically copies sensitive files into these concealed locations. This process effectively transforms the external storage device into a covert data mule.
As Zscaler researchers meticulously documented, this capability effectively turns the removable media into a "bidirectional covert C2 relay." This is the key breakthrough for APT37: the infected USB drive now serves not only to ferry stolen data out of the air-gapped zone to an attacker-controlled machine (the "exfiltration" path) but also to carry new commands into the isolated network segment (the "command and control" path). An operator physically inserts an infected drive into an air-gapped machine, unknowingly uploading commands, and later removes the drive, which is then inserted into a machine connected to the internet, allowing the exfiltration of staged data.

This "stitching" of isolated networks via removable media circumvents decades of network security architecture designed to stop network-borne threats. It exploits the necessary human element of physical data transfer, a vector that is notoriously difficult to secure comprehensively.
VIRUSTASK: Spreading the Contagion Across Segments
While THUMBSBD focuses on data movement and command reception, VIRUSTASK is the infection propagation mechanism designed to spread the Ruby Jumper malware to new air-gapped machines once the initial breach vector has been established.
VIRUSTASK actively weaponizes any removable drive it encounters. It achieves this by modifying the file system on the USB media. It hides existing legitimate files and replaces them with malicious LNK shortcut files. When an unsuspecting user plugs this compromised drive into another isolated workstation, the operating system presents the malicious shortcut as if it were the original file. Clicking this shortcut triggers the execution of the embedded Ruby interpreter, initiating the entire infection chain anew on the fresh host.
Crucially, the propagation mechanism includes a safeguard: the VIRUSTASK module will only proceed with infecting a new host if the inserted removable media possesses at least 2GB of free space. This threshold likely serves as a heuristic to avoid smaller, potentially non-storage-capacity devices or to ensure sufficient room for staging and executing the multi-stage payloads.
The Payload Suite: Comprehensive Espionage
The final components of the Ruby Jumper operation confirm APT37’s intent is deep, long-term intelligence gathering, rather than simple denial-of-service or ransomware deployment.
The THUMBSBD backdoor is also responsible for deploying FOOTWINE, a sophisticated Windows spyware backdoor. FOOTWINE is disguised as an Android Package Kit (APK) file, adding another layer of obfuscation, suggesting potential crossover targeting or simply leveraging a familiar file structure to avoid suspicion. This spyware possesses a robust capability set: keylogging to capture credentials and sensitive inputs, continuous screenshot capture, audio and video recording, extensive file manipulation rights, registry access for deep system modification, and the ability to execute arbitrary remote shell commands. This provides APT37 with near-total situational awareness and control over the compromised air-gapped host.
Furthermore, the campaign has been observed utilizing BLUELIGHT, a full-fledged backdoor previously linked directly to APT37 operations. The inclusion of BLUELIGHT, combined with the specific LNK file initial vector, the two-stage shellcode delivery mechanism, and the characteristic C2 infrastructure utilizing Zoho WorkDrive, provides Zscaler researchers with high confidence in attributing the Ruby Jumper campaign specifically to APT37.
The context provided by the decoy document—interest in North Korean media narratives—further reinforces the attribution, aligning with APT37’s historical focus on defense, foreign policy, and political entities relevant to South Korea and its allies.
Industry Implications: The Erosion of Physical Security Assumptions
The successful deployment of Ruby Jumper against air-gapped networks represents a paradigm shift in cybersecurity threat modeling. For decades, security architects have relied on the air-gap as the final, insurmountable barrier against cyber espionage, particularly for nation-state actors who might struggle with persistent remote access to highly segmented networks.
This attack proves that the air-gap is only as secure as the human processes surrounding data transfer. The reliance on physical media—the very mechanism intended to maintain isolation—has been transformed into the primary conduit for compromise.
For Critical Infrastructure (CI) and Defense: Sectors managing operational technology (OT) environments—power generation, manufacturing control systems, and military command systems—must immediately reassess their data handling protocols. Traditional endpoint detection and response (EDR) solutions are irrelevant here. The defense must shift to rigorous procedural controls, including:
- Strict Media Vetting: Implementing dedicated, non-internet-connected scanning stations that thoroughly vet all removable media for suspicious scripts, file types, and size anomalies before any transfer is authorized.
- Hardware Whitelisting: Where possible, using hardware security modules or write-once media for data ingestion into critical zones.
- Behavioral Anomaly Detection: Focusing on unusual process execution chains (like a Word document spawning PowerShell, which then installs a full programming runtime environment).
The Rise of Supply Chain Exploitation: The infection chain, starting potentially on an internet-connected machine and ending on an air-gapped one, highlights a significant supply chain risk. If a vendor or contractor servicing the secure facility uses a compromised laptop to prepare data for transfer, that compromise can leap across the digital divide.
The Novelty of Language Choice: The use of the Ruby runtime environment is noteworthy. While malware often relies on ubiquitous languages like C++ or Python (which is frequently pre-installed), relying on Ruby suggests a deliberate choice to leverage a less commonly monitored or sandboxed execution environment in specialized, high-security settings. Attackers exploit the "blind spots" in defensive toolsets, and Ruby interpreter execution is often overlooked in environments hardened against traditional Windows malware.
Expert Analysis and Future Trajectories
The sophistication exhibited by the Ruby Jumper toolset suggests a maturation in APT37’s operational planning. Previous sophisticated attacks often relied on simpler methods to bridge the gap, such as exploiting vulnerabilities in firmware or utilizing specialized hardware implants. Ruby Jumper demonstrates a preference for a purely software-based, cross-platform (via the interpreter) methodology that leverages seemingly benign administrative tasks (like USB utility installation and scheduled updates) for persistence.
.jpg)
The employment of Zoho WorkDrive for C2 is another area demanding attention. As organizations increasingly adopt Software-as-a-Service (SaaS) platforms for legitimate business functions, these platforms become attractive camouflage for threat actors. Future defensive strategies must incorporate deep inspection of traffic patterns, even to ostensibly trusted cloud services, looking for anomalous command structures or data exfiltration volumes disguised as legitimate cloud synchronization activity.
Looking forward, the trajectory indicated by Ruby Jumper suggests a relentless focus by state actors on overcoming physical segmentation. We can anticipate further evolution in malware designed to exploit:
- Firmware and BIOS Attacks: Moving beyond application-layer malware to implant code directly into the system firmware, making eradication much harder, even across drive wipes.
- Electromagnetic and Acoustic Side-Channels: While not explicitly used in Ruby Jumper, the development of malware capable of manipulating system components (like CPU caches or cooling fans) to transmit data via electromagnetic emissions or sound waves represents the next frontier in overcoming air-gaps without physical media insertion.
- Supply Chain Poisoning of Installers: Targeting the creation and distribution of legitimate software installers that organizations might use to patch or maintain air-gapped systems, embedding toolkits like Ruby Jumper within updates for network monitoring tools or antivirus signatures.
The Ruby Jumper campaign is a stark reminder that cybersecurity is an arms race where the objective is not merely to block known threats but to anticipate the adversary’s next creative leap over established security boundaries. For organizations relying on the integrity of an air-gap, the analysis of this Ruby-based intrusion mandates an urgent, holistic re-evaluation of every physical data transfer point and the assumption of inherent trust in any removable media. The gap is bridged; the defense must now adapt to a world where physical isolation no longer guarantees digital security.

