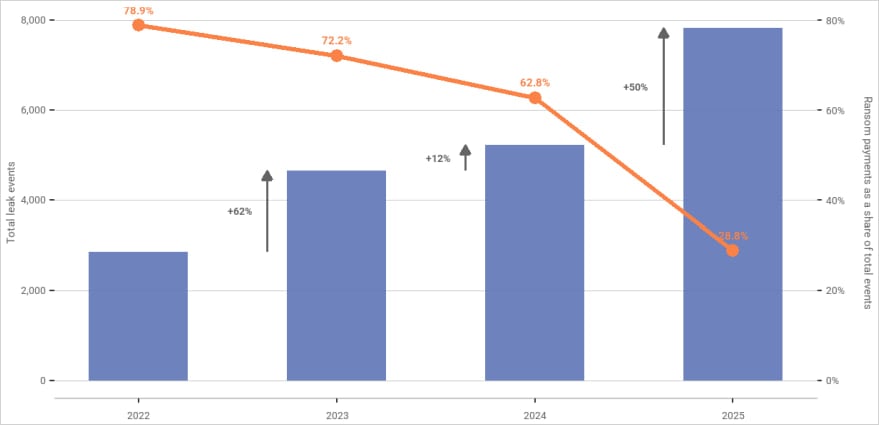
The landscape of cyber extortion is presenting a complex, seemingly contradictory picture as data reveals a significant dip in the rate at which victims are capitulating to ransom demands, even as the sheer volume of reported attacks continues its upward trajectory. Analysis from the blockchain intelligence firm Chainalysis indicates that only 28% of ransomware victims opted to pay threat actors last year, establishing a historical low point for financial concessions in the cybercrime ecosystem. This figure marks a stark contrast to previous years, signaling a fundamental shift in organizational resilience or risk tolerance against these debilitating attacks.
This downward trend in payment rates is not an anomaly but the culmination of four consecutive years of diminishing returns for cybercriminals. This sustained decline suggests that defensive measures, coupled with changing geopolitical and enforcement landscapes, are beginning to erode the traditional ransomware business model. Despite this reduced willingness to pay, the overall financial scale of the ecosystem remains substantial. Preliminary on-chain transaction data for the preceding year pegs total ransomware payments at approximately $820 million, though Chainalysis analysts project this figure will ultimately surpass $900 million once all attributed events and transactions are finalized.
To fully appreciate the current environment, it is crucial to contextualize these figures against the backdrop of attack frequency. Chainalysis reports a staggering 50% year-over-year increase in claimed ransomware incidents. This simultaneous surge in malicious activity and drop in successful payouts illustrates a critical divergence: threat actors are casting a wider net, but fewer entities are choosing to settle disputes financially. For perspective, the payment rate in the previous year stood at 62.8%, a figure that itself represented a notable drop from 78.9% recorded in 2022. The visual representation of this data—showing rising incident bars against a falling payment rate line—underscores the maturation of cyber defense strategies across various sectors.

This data corroborates findings from other industry observers, including prior reports from Coveware, which similarly documented a steady erosion of victim payment percentages throughout the previous year. The confluence of these independent data points lends significant weight to the conclusion that the ransomware economy is undergoing structural stress.
Drivers Behind the Resistance: A Multi-Faceted Deterrent
The reasons behind this increasing reluctance to pay are multifaceted, stemming from improvements in both proactive defense and reactive measures. According to Chainalysis’s detailed assessment, several key factors are reshaping the calculus for potential victims.
Foremost among these is improved incident response maturity. Organizations are becoming more adept at isolating breaches quickly, restoring operations via robust backup strategies (often air-gapped or immutable), and minimizing the operational downtime that criminals leverage for coercion. The ability to recover without paying the ransom significantly devalues the core product offered by the attackers: encryption or data exfiltration.
Secondly, heightened regulatory scrutiny plays an increasingly punitive role. Governments globally are tightening data protection laws, often imposing severe penalties for non-compliance following a breach. The calculus now includes not just the cost of the ransom, but the potentially catastrophic fines associated with regulatory non-adherence, making internal restoration a financially preferable route.

Coordinated international law enforcement actions also contribute substantially. High-profile takedowns of major Ransomware-as-a-Service (RaaS) operations and arrests of key infrastructure operators inject uncertainty into the criminal market. When the reliability of the criminal pipeline is questioned, the perceived value of paying a ransom diminishes.
Finally, market fragmentation within the cybercriminal sphere itself is a factor. As the number of active extortion groups swells—Chainalysis identified 85 distinct groups in the last year, up from periods dominated by just a handful of major players—the marketplace for stolen data becomes saturated, potentially reducing the leverage of individual actors.
The Paradox of the Payout: Higher Stakes, Higher Costs
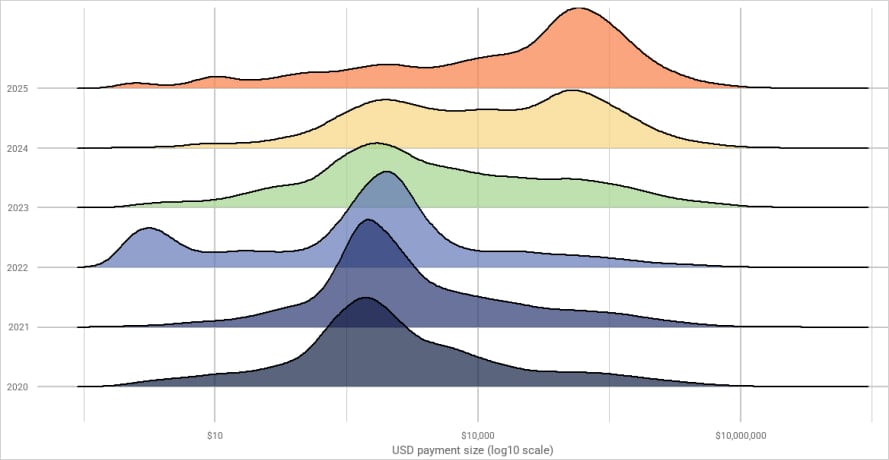
While fewer victims are paying, those who do decide to remit funds are paying significantly more. This presents the most telling indicator of evolving criminal strategy. The median ransom demand skyrocketed by an astonishing 368%, soaring from an average of $12,738 in the preceding year to $59,556 in the latest reporting period.
This dramatic increase in the median payment suggests a critical shift in victim psychology. It implies that organizations are not paying smaller, tactical ransoms, but rather larger, strategic ones motivated by the desire to mitigate secondary risk—specifically, the risk associated with data exposure. When a victim pays a substantial sum, the implicit contract is that the threat actors will not only decrypt the systems but, crucially, permanently delete the exfiltrated data and refrain from selling it on dark web marketplaces or using it for subsequent double or triple extortion schemes. The rising median payment reflects an organization’s desperate attempt to buy the complete eradication of their data liability, rather than just operational recovery.
This phenomenon demonstrates that ransomware is evolving from a pure availability attack (encryption) into a more sophisticated information governance and reputation crisis management tool for the attackers.
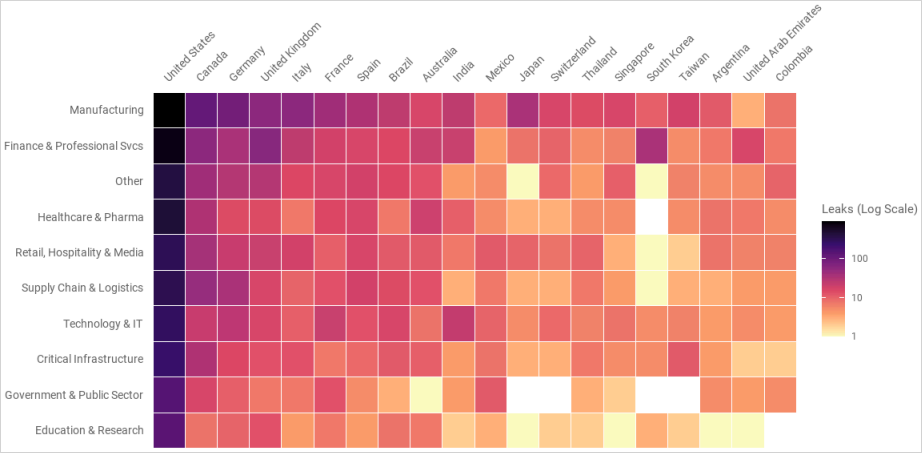
Industry Impact and Geographic Concentration
The threat actors are demonstrating a clear, sustained preference for targeting organizations within highly developed economies, likely due to the perceived higher likelihood of large payouts and the severity of regulatory impact. For the latest reporting cycle, the United States remained the primary target, followed sequentially by Canada, Germany, and the United Kingdom.
The impact on targeted organizations can be severe, even when the payment rate is low. Chainalysis highlighted several incidents that underscore the potential scale of damage: the attack against Jaguar Land Rover, estimated to have caused $2.5 billion in damages; the breach of Marks & Spencer attributed to the Scattered Spider group; and the DaVita Inc. incident, which compromised records belonging to 2.7 million patients. These high-profile cases serve as cautionary tales, regardless of whether the ransom was ultimately paid.
The Initial Access Economy: Leading Indicators of Threat
An essential, yet often underappreciated, component of the ransomware supply chain is the role of Initial Access Brokers (IABs). These are specialized threat actors who breach networks and then sell vetted, authenticated access credentials or remote desktop protocol (RDP) access to the final-stage ransomware operators.
The financial activity within the IAB market remained relatively stable, with reported earnings hovering around $14 million for the last year, a figure comparable to the previous period. While this constitutes a mere 1.7% of the total estimated ransomware revenue, IAB activity acts as a crucial barometer for future attacks. Chainalysis researchers have established a temporal correlation: spikes in IAB payment inflows are typically followed by a discernible increase in ransomware payment demands and subsequent victim data leak posts approximately 30 days later. This suggests that IAB revenue flow is a valuable, albeit short-term, leading indicator for predicting upcoming waves of major ransomware campaigns.
However, the economics of initial access itself are being disrupted. The average cost for a single network access point has plummeted dramatically, falling from around $1,427 in the first quarter of 2023 to a mere $439 in the first quarter of 2026. This deflationary pressure is attributable to several factors: the increased automation and efficiency afforded by AI-assisted tooling in the reconnaissance phase, and a potential oversupply of compromised access logs originating from less sophisticated malware strains, such as info-stealers. When access becomes cheaper and more plentiful, ransomware groups can afford to be more selective about which targets they pursue with full-scale, costly encryption operations, prioritizing those with higher potential yield.
Expert Analysis: Adaptation Over Attrition
The prevailing narrative within cybersecurity circles must pivot away from viewing the drop in payment rates as a sign of ransomware’s imminent demise. Instead, analysts must recognize this as a period of intense adaptation within the cybercrime industry.
The research strongly suggests that ransomware is not losing the fight; rather, it is optimizing its methods to extract maximum value from a smaller pool of willing payers. The strategy is shifting from volume-based extortion (hoping a large percentage of many victims will pay small amounts) to high-stakes, high-value extortion aimed at the most lucrative, risk-averse targets.
This adaptation manifests in several ways:
- Increased Focus on Data Exfiltration: The higher median payment validates the success of double and triple extortion models. Attackers know that the regulatory and reputational damage from data leakage often outweighs the immediate operational impact of encryption, forcing larger payments to secure data destruction guarantees.
- Diversification of Extortion Methods: As direct ransom payments become harder to secure, criminal groups are likely exploring alternative monetization streams, such as selling access directly to other criminal factions, demanding ransoms in non-fungible crypto assets, or shifting focus toward supply chain compromise where the collateral damage is exponentially higher.
- Automation and Efficiency: The reduced cost of initial access, driven by new tooling, allows ransomware affiliates to run leaner operations. They can invest more resources into specialized attack vectors or intelligence gathering on specific high-value targets, rather than spending time manually breaching entry points.
The future trajectory of this threat will be defined by the continuous arms race between defenders who are improving their resilience (backups, zero-trust architecture, mandatory MFA) and attackers who are becoming more surgical, sophisticated, and adept at exploiting the data risk rather than solely the availability risk. The record-low payment rate is not a victory lap; it is a warning that the nature of the threat is morphing into something potentially more insidious and harder to negotiate away. Organizations must prepare not just for encryption, but for the guaranteed leak of their most sensitive assets, necessitating a comprehensive, data-centric approach to cybersecurity governance moving forward.

